A weekly aggregation of important cybersecurity and privacy news helping you navigate the new world of cybersecurity and privacy.
Stan’s Top-3
This week’s Top-3 all reflect cybersecurity at the national level.
Our first story features award-winning author Nicole Perlroth discussing a serious federal cybersecurity alert that malware has been discovered with the potential to shut down our electrical grid and other critical infrastructure. (SecureTheVillage is hosting an event with Ms. Perlroth on May 4. See details below.)
- Threat of cyberattack on U.S. infrastructure takes more serious turn: Nicole Perlroth, cybersecurity advisor to CISA, talks with Rachel Maddow about a new federal alert about the discovery of malware, likely from Russia, that could grant hackers access to infrastructure systems like the electricity grid. MSNBC, April 13, 2022
Our second story is another illustration of the national cyber threat. It tells the story of how DHS blocked a cyber attack that could have cut telecommunications service to all of Hawaii.
- DHS investigators say they foiled cyberattack on undersea internet cable in Hawaii: Federal agents in Honolulu last week “disrupted” an apparent cyberattack on an unnamed telecommunication company’s servers associated with an underwater cable responsible for internet, cable service and cell connections in Hawaii and the region, the agency said in a statement Tuesday. Cyberscoop, April 13, 2022
The following story is important as it illustrates the value of cyber crime to the North Korean economy. You might remember our story 2 weeks ago about hackers stealing $600 million from video game Axie Infinity’s Ronin network. The Treasury Department reports the crime was likely committed by the notorious state-backed North Korean cybercrime gang, Lazarus. When you consider that North Korea’s estimated GDP is only $27 billion, this theft adds 2% to North Korea’s economy.
- U.S. officials link North Korean hackers to $615 million cryptocurrency heist: North Korean state-backed hacking collective Lazarus Group is linked to a massive cryptocurrency hack that led to the theft of $615 million in digital assets, U.S. officials allege. CNBC, April 15, 2022
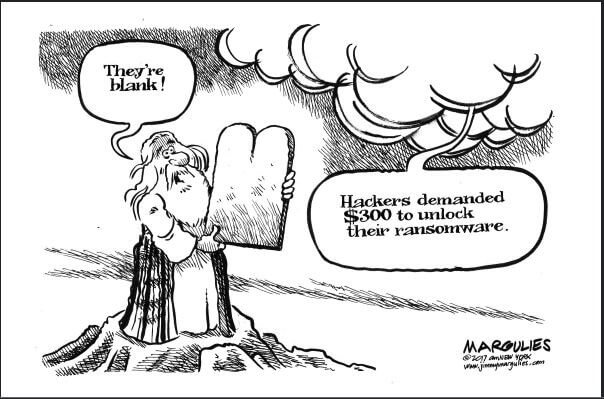
Cyber Humor
The Front Page
Other front page cybersecurity and privacy stories.
These next two stories are about Ukrainian cyber-defense. In the first, Ukraine claims to have stopped a Russian cyberattack on its electrical grid. The second tells the story of a team of Ukrainians that has been tracking Russian attackers for years, learning their moves, and finding ways to defend.
- Ukraine says it stopped a Russian cyberattack on its power grid: Hackers have revamped a rare piece of malware specifically made to target power infrastructure … An attack on Ukraine’s power grid was foiled by cybersecurity analysts and officials, as reported by Reuters. After investigating the methods and software used by the attackers, cybersecurity firm ESET says that it was likely carried out by a hacking group called Sandworm, which The Record reports allegedly has ties to the Russian government. The Verge, April 13, 2022
- Preparing for Armageddon: How Ukraine battles Russian hackers: One long-running rivalry shows how Kyiv has withstood major cyberattacks. … For years, a small and disparate Ukrainian team including IT experts, intelligence officers, and a criminal prosecutor has kept a wary eye on a group of hackers nicknamed Armageddon. Ars technica, April 14, 2022
With so much ransomware coming out of Russia, it feels good to read a story of Russian companies and government agencies being targeted in ransomware attacks. But it also raises serious questions of who is doing it. Stay tuned.
- Ransomware groups go after a new target: Russian organizations: In many ransomware incidents, Russia-linked actors often play the role of attacker rather than the victim. … But in recent weeks, cyberattacks have crippled Russian companies and disrupted government agencies. The Record, April 15, 2022
Augmenting our Top-3 story about North Korea, the following stories tell of a North Korean hacking campaign targeting the chemical sector and of a new $5 million Department of State rewards program targeted against North Korea hackers.
- Lazarus Targets Chemical Sector With ‘Dream Jobs,’ Then Trojans: Chemical companies are the latest to be targeted by the well-known North Korean group, which has targeted financial firms, security researchers, and technology companies in the past. … The North Korean-linked Lazarus group sent fake job offers to targets in the chemical sector and information technology firms, which — when opened — install Trojan horse programs to collect information and send it back to the attackers, technology provider Broadcom’s security arm Symantec stated in an advisory on April 14. DARK Reading, April, 15, 2022
- U.S. offers $5 million for info on North Korean cyber operators: The State Department announced Friday that it is offering a reward of up to $5 million for information about North Korean digital operations that help keep the regime afloat and fund its weapons programs. The Record, April 15, 2022
In further government action, the Justice Department announced that it has seized the website and user database of a very popular underground cybercrime forum, and has arrested the alleged administrator. One hopes that its database will provide evidence to shut down more of these cyber crime gangs.
- RaidForums Gets Raided, Alleged Admin Arrested: The U.S. Department of Justice (DOJ) said today it seized the website and user database for RaidForums, an extremely popular English-language cybercrime forum that sold access to more than 10 billion consumer records stolen in some of the world’s largest data breaches since 2015. The DOJ also charged the alleged administrator of RaidForums — 21-year-old Diogo Santos Coelho, of Portugal — with six criminal counts, including conspiracy, access device fraud and aggravated identity theft. KrebsOnSecurity, April 12, 2022
Security Nonprofit of the Week
Our kudos this week to the Cyber Readiness Institute (CRI) and the great work they do helping our medium-size and smaller organizations manage their information security challenges. CRI’s Cyber Readiness Program helps organizations protect their data, employees, vendors, and customers. This free, online program is designed to help small and medium-sized enterprises become more secure against today’s most common cyber vulnerabilities. Their free Cyber Leader Certification Program is a personal professional credential for those who have completed the Cyber Readiness Program. Both are highly recommended.
Live on Cyber with Dr. Stan Stahl – Live on LinkedIn
Live on Cyber with Dr. Stan Stahl: Join Julie Morris and me as we discuss the latest in cybersecurity. This week we talk about basic online security tactics everyone needs to implement; the FBI’s latest cyber crime statistics; and the sad story of a Business Email Compromise (BEC) fraud that cost a nonprofit $650,000. SecureTheVillage, April 14, 2022
Register Now. Invitation to Sponsor.
SecureTheVillage presents Nicole Perlroth, Award-winning Cybersecurity Journalist, New York Times Bestselling Author, and CISA advisor. A Virtual Learning Opportunity By & For Leaders in Cybersecurity. May 4, 11:00AM Pacific. Registration now open. Sponsorships still available.

Section 2 – Personal Security and Privacy
Important stories for protecting yourself and your family.
It’s update time again. Make sure Windows has updated itself and check your other programs for updates as well.
- Microsoft Patch Tuesday, April 2022 Edition: Microsoft on Tuesday released updates to fix roughly 120 security vulnerabilities in its Windows operating systems and other software. Two of the flaws have been publicly detailed prior to this week, and one is already seeing active exploitation, according to a report from the U.S. National Security Agency (NSA). KrebsOnSecurity, April 13, 2022
This next story is important if you use a D-Link router. Several older D-Link models have reached “end-of-life” and are no longer being provided with updates. These routers need to be replaced as soon as possible as the Cybersecurity & Infrastructure Agency (CISA) says they are now defenseless against attack.
- PSA: Replace vulnerable D-Link routers as soon as possible, says CISA: These EOL models won’t receive security patches. … Network routers are a type of device that users tend to hold on to for far longer than they should. So long as they can still get connected to the internet, many users see no harm in keeping their old devices plugged in. However, the Cybersecurity & Infrastructure Agency (CISA) is reminding D-Link customers why that’s not such a good idea: five more D-Link models have recently been added to the agency’s list of vulnerable devices. Techspot, April 11, 2022
Section 3 – General Cybersecurity and Privacy Stories
Cybersecurity and privacy stories for those wanting a deeper look.
These next several stories continue to illustrate the magnitude of what security professionals call the “threat landscape.” The first augments our lead story on the newly discovered malware that threatens our electrical grid and other critical infrastructure. The fourth story is an illustration of the impact the recent breach of identity management platform Okta is having on cybersecurity.
- Feds Uncover a ‘Swiss Army Knife’ for Hacking Industrial Control Systems: The malware toolkit, known as Pipedream, is perhaps the most versatile tool ever made to target critical infrastructure like power grids and oil refineries. … Malware designed to target industrial control systems like power grids, factories, water utilities, and oil refineries represents a rare species of digital badness. So when the United States government warns of a piece of code built to target not just one of those industries, but potentially all of them, critical infrastructure owners worldwide should take notice. Wired, April 13, 2022
- Microsoft Exposes Evasive Chinese Tarrask Malware Attacking Windows Computers: The Chinese-backed Hafnium hacking group has been linked to a piece of a new malware that’s used to maintain persistence on compromised Windows environments. The Hacker News, April 13, 2022
- Hospital robot system gets five critical security holes patched: Researchers at healthcare cybersecurity company Cynerio just published a report about five cybersecurity holes they found in a hospital robot system called TUG. Naked security, April 12, 2022
- GitHub: Attacker breached dozens of orgs using stolen OAuth tokens: GitHub revealed today that an attacker is using stolen OAuth user tokens (issued to Heroku and Travis-CI) to download data from private repositories. Bleeping Computer, April 15, 2022
Privacy is in the news with two stories this week, one from the FTC and the other from Apple.
- FTC Chair Pushes Privacy Rules, Calls for Limits on Data Collection: Lina Khan is gearing up to establish federal privacy regulation for the digital age. … Federal Trade Commission Chair Lina Khan said it is time that the agency, which is tasked with enforcing consumer privacy protections, “reassess” rules around what data companies can collect about consumers and how they secure that data. C|net, April 11, 2022
- Apple drops out of industry trade group over ‘weak privacy laws’: Apple is dropping out of a privacy trade group that has shifted towards more “industry-friendly data privacy laws.” The news was first reported by Politico and Apple confirmed the decision through a spokesperson. The change comes ahead of Apple CEO Tim Cook headlining a global privacy summit next week. 9TO5Mac, April 7, 2022
I confess to not being sure what to make of this next story. If my customers’ sensitive information had been stolen, wouldn’t my customers want me to buy it back? Don’t I have an ethical responsibility to attempt to do so? But then, wouldn’t I be incredibly naïve if I actually believed the cyber criminals who stole this information would actually remove it from their servers?
- T-Mobile may have secretly attempted to buy customer data leaked in 2021 hack: Court documents suggest a third-party firm possibly hired by the carrier tried to purchase the information. engadget, April 12, 2022
Section 4 – Securing the Organization
Stories to support executives and top management in securing their organizations.
Every organization needs to train staff to be mindful of cybersecurity. As the following two stories illustrate, there are good ways to do this and not-so-good ways.
- OHSU apologizes after phishing test draws complaints: PORTLAND, Ore. (AP) — Officials at Oregon Health & Science University have apologized to employees after a fake phishing test drew complaints about raising false hopes. The News-Review, April 15, 2022
- Creating a Security Culture Where People Can Admit Mistakes: In cybersecurity, user error is the symptom, not the disease. A healthy culture acknowledges and addresses the underlying causes of lapses. … Andy Ellis, advisory CISO for Orca Security and a longtime Akamai veteran, likes to tell a story about a potentially serious security incident. One of his team members was testing the email integration of a new incident tracking system. Unfortunately, the test email, titled “[TEST] Meteor strike destroys the headquarters,” went to everyone in the company and created a loop that crashed the mail servers. DARK Reading, April 11, 2022
I remember several years ago when the rush to the cloud began. Whenever I heard an acolyte say something like “Your information is secure in the cloud,” I would smile, knowing better. Well, here we are several years later and we’re still struggling to secure our cloud applications. Don’t trust. Verify.
- Terrible cloud security is leaving the door open for hackers. Here’s what you’re doing wrong: A rise in hybrid work and a shift to cloud platforms has changed how businesses operate – but it’s also leaving them vulnerable to cyberattacks. … Cloud applications and services are a prime target for hackers because poor cybersecurity management and misconfigured services are leaving them exposed to the internet and vulnerable to simple cyberattacks. ZD Net, April 12, 2022
And this next story is a reminder to IT Departments and MSPs everywhere to always be on the alert for bad stuff going on in the network. There’s a reason why “detect” is the third critical information security function in the NIST Cyber Security Framework. If you only know your enemy is in your system when your enemy wants you to know, you will lose every time.
- Clueless hackers spent months inside a network and nobody noticed. But then a ransomware gang turned up: Novice hackers who didn’t know what they were doing spent months inside a government agency network without being detected – before higher-skilled attackers came in after them and launched a ransomware attack. ZD Net, April 13, 2022


