This week’s essential cybersecurity and privacy news for the cyber-aware and the cyber-concerned. Designed to educate, support, and advocate.
Stan’s Top of the News
West clashes with China, Russia over UN Cybercrime Convention: The United Nations Cybercrime Convention is becoming a battleground between the EU and other Western countries on the one hand, China, Russia and other authoritarian regimes on the other. https://www.euractiv.com/section/law-enforcement/news/west-clashes-with-china-russia-over-un-cybercrime-convention/
What it will look like if China launches cyberattacks in the U.S.: Chinese hackers are likely to target U.S. military networks and other critical infrastructure in the event of an invasion of Taiwan. While much of the cybersecurity world’s attention is on fending off Russian hacks against Ukraine, American officials are increasingly worried about another growing threat: attacks by China on U.S. soil. If China invades Taiwan, they say, it is likely to unleash a volley of digital strikes against the United States at the same time. … Top lawmakers, the U.S. intelligence community and cybersecurity officials have warned in recent weeks that if an invasion happens, China would likely try to hobble critical U.S. systems with cyberattacks on military transport systems like ports and railroads, or against key civilian services like water and electricity. https://www.politico.com/news/2023/04/16/chinese-hackers-military-taiwan-invasion-00092189
An Iranian hacking group went on the offensive against U.S. targets, Microsoft says: An Iranian hacking group could be looking to launch destructive cyberattacks on U.S. targets, Microsoft said Tuesday. An Iranian government-linked hacking group previously known for its focus on reconnaissance has shifted to targeting U.S. critical infrastructure, potentially with the goal of launching destructive cyberattacks, Microsoft said in a report today. https://wapo.st/43XRA
From Secure The Village
New. Family Protection Newsletter: Did you know we created the Family Protection Newsletter, for non-cyber experts? For your parents, friends, those who need to protect themselves in a digital world. We feature info on how to freeze your credit and what ‘marriage scams’ are in Edition 1. Sign up or share with a friend! Click here to learn more and quickly add to your free subscription!
How Hackable Are You? Take our test. Find out how hackable you are and download our free 8-step guide.
- How Hackable Are You? Think your defenses are strong. Find out as SecureTheVillage tests you on five basics. Please take our short quiz as your answers will help you and guide us to improve community safety.
Upcoming events. Please join us.
- Los Angeles Cybersecurity Workforce Coalition: The monthly meeting of the workforce coalition, Tue, May 2, 1:00 pm – 2:00 pm PT.
- Invasion of the Body & Mind (Data) Snatchers: What you need to know. What you need to do. May 25, 11:00 am – 12:30 pm PT.
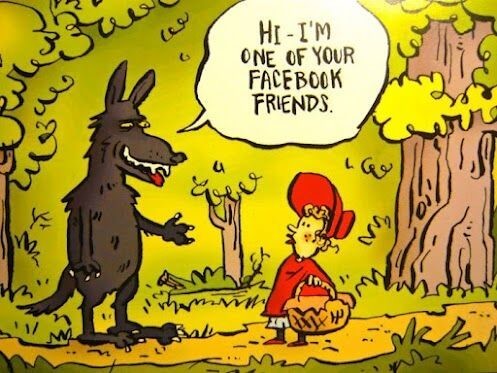
Cyber Humor
Cybersecurity Nonprofit of the Week … The Global Anti-Scam Alliance
Our kudos this week to the Global Anti-Scam Alliance. Their mission is to create a world where people worldwide are safe from the financial and emotional trauma caused by online scams. To protect consumers worldwide from scams. GASA realizes its mission by raising awareness, enabling hand-on tools for consumers and law enforcement, facilitating knowledge sharing, organizing research, supporting the development of (legal) best practices, and offering training and education. At the 4th Global Anti Scam Summit this week, GASA outlined Ten Recommendations to Turn the Tide on Scams. Like SecureTheVillage, the Global Anti-Scam Alliance is a fellow-member of Nonprofit Cyber.
Live on Cyber with Dr. Stan Stahl – Live on LinkedIn and Your Favorite Podcast Platform

What’s in your cyber-control: (Video) (Podcast): This week, Stan Stahl, PhD and Julie Michelle Morris riff on the cybersecurity and privacy things individuals can control. … Application developers can issue an update but it’s of no value unless the user installs it. … The update – and the vulnerability it protects against – is OUTSIDE the user’s control. Updating that program is WITHIN the user’s control. Stan and Julie discuss this and other ways users can make themselves less hackable, by taking control of the things that they are in control of … Keeping software up to date … Freezing your credit … Being careful on email … Backing up files … Using strong unique passwords, etc. … As always, Stan and Julie provide actionable tips and thoughtful wisdom in an engaging conversation on the complexities of cybersecurity and privacy.
Section 2 – Let’s Be Careful Out There. And Let’s Help Others Who Aren’t Yet Cyber-Aware.
Gone in seconds: rising text message scams are draining US bank accounts: Sophisticated robotexts are bombarding Americans’ phones, costing unsuspecting people millions of dollars. … The text message created an instant surge of panic. … “Freemsg: Chase, Did you attempt wire transfer amount of $7500. Reply Y if recognized, Or NO to stop fraud.” … For Ohio resident Kelli Hinton, this was the beginning of a hard-to-detect scam in which a man posing as a Chase Bank fraud investigator ended up clearing two of her bank accounts of $15,000. https://www.theguardian.com/money/2023/apr/22/robo-texts-scams-bank-accounts
Chatbots and Voice-Cloning Fuel Rise in AI-Powered Scams: Cybercrime experts warn that new tech offers scammers frighteningly effective tools … A Houston-area couple received a call last month from their adult son — or at least they thought it was him: The voice sounded exactly like him. He said he’d been in a car accident where he hit a woman who was six-months pregnant, had just been released from the hospital, and now was in the county jail about to be charged with DWI, according to a KHOU 11 News report. He needed $5,000 to get himself out of this mess. … Absolutely convinced that the caller was their child, they handed over the cash to an intermediary who came to their home pick it up. https://www.aarp.org/money/scams-fraud/info-2023/ai-chatbots-voice-cloning.html>
Facebook users can apply for their portion of a $725 million lawsuit settlement: Facebook users in the U.S. can now apply for their share of a $725 million privacy lawsuit settlement if they had accounts from May 2007 to December 2022. … Facebook’s parent company, Meta, is doling out the payments to settle a lawsuit alleging it allowed Cambridge Analytica, a former British political consulting firm used by the 2016 Donald Trump presidential campaign, to access about 87 million users’ personal information. To apply for the funds, people can apply online or by mailing their forms by Aug. 25. https://www.npr.org/2023/04/20/1170987739/facebook-settlement-lawsuit-privacy
Section 3 – Cybersecurity and Privacy News for the Cyber-Concerned.
EU proposes $1.2 billion plan to counter growing cybersecurity threats: BRUSSELS, April 18 (Reuters) – The European Commission on Tuesday announced a 1.1-billion-euro ($1.2 billion) plan to counter growing cybersecurity threats, underscoring mounting concerns about a series of high-profile hacking incidents. https://www.reuters.com/technology/eu-proposes-12-bln-plan-counter-growing-cybersecurity-threats-2023-04-18/>
In letter to EU, open source bodies say Cyber Resilience Act could have ‘chilling effect’ on software development: The proposed legislation also poses ‘an unnecessary economic and technological risk to the EU. … More than a dozen open source industry bodies have published an open letter asking the European Commission (EC) to reconsider aspects of its proposed Cyber Resilience Act (CRA), saying it will have a “chilling effect” on open source software development if implemented in its current form. https://techcrunch.com/2023/04/18/in-letter-to-european-commission-open-source-bodies-say-cyber-resilience-act-could-have-chilling-effect-on-software-development/>
The New Risks ChatGPT Poses to Cybersecurity: The FBI’s 2021 Internet Crime Report found that phishing is the most common IT threat in America. From a hacker’s perspective, ChatGPT is a game changer, affording hackers from all over the globe a near fluency in English to bolster their phishing campaigns. Bad actors may also be able to trick the AI into generating hacking code. And, of course, there’s the potential for ChatGPT itself to be hacked, disseminating dangerous misinformation and political propaganda. This article examines these new risks, explores the needed training and tools for cybersecurity professionals to respond, and calls for government oversight to ensure that AI usage doesn’t become detrimental to cybersecurity efforts. https://hbr.org/2023/04/the-new-risks-chatgpt-poses-to-cybersecurity
From ChatGPT to HackGPT: Meeting the Cybersecurity Threat of Generative AI: It’s time to replace traditional, rule-based approaches to cybersecurity with “smarter” technology and training. … For the past several years, cybercriminals have been using artificial intelligence to hack into corporate systems and disrupt business operations. But powerful new generative AI tools such as ChatGPT present business leaders with a new set of challenges. … Consider these entirely plausible scenarios … https://sloanreview.mit.edu/article/from-chatgpt-to-hackgpt-meeting-the-cybersecurity-threat-of-generative-ai/
Shut it off immediately’: The health industry responds to data privacy crackdown: Biden administration enforcement actions have chilled advertising spending and cut into bottom lines. … A series of federal data privacy crackdowns is complicating how health care companies market their services online. The Federal Trade Commission has led the way in the new enforcement push, fining telehealth companies for violating their customers’ privacy and barring them from doing so in the future. The director of HHS’ Office for Civil Rights said her staff has launched its own investigation, calling online health data collection “problematic” and “widespread.” The agency also recently sought to update health data privacy protections to bar providers and insurers from releasing information about a patient seeking or obtaining a legal abortion. https://www.politico.com/news/2023/04/17/health-industry-data-privacy-00092447
Addressing the cybersecurity staff shortage: As cyber threats continue to rapidly evolve, the need for skilled cybersecurity professionals becomes increasingly urgent. Organizations are realizing the gaps in internal cyber risk management teams are interfering with their ability to effectively address emerging cyber threats. According to The International Information System Security Certification Consortium (ISC), “The cybersecurity workforce gap has increased from 2.7 million in 2021 to 3.4 million in 2022.” Cyber Seek currently reports a whopping 755,743 across the U.S., and the shortage is predicted to be a growing problem well into 2025. With companies investing in technology more than ever to streamline services and enhance their daily business functions, vulnerabilities are exploited by cybercriminals and the demand for cybersecurity professionals will only become more critical. https://www.securitymagazine.com/articles/99237-addressing-the-cybersecurity-staff-shortage
U.S., U.K., Australia, Canada and New Zealand Release Cybersecurity Best Practices for Smart Cities. Cybersecurity officials provide recommendations and resources to help communities balance efficiency and innovation with cybersecurity, privacy protections, and national security. https://www.cisa.gov/news-events/news/us-uk-australia-canada-and-new-zealand-release-cybersecurity-best-practices-smart-cities
How Mexico Became the Biggest User of the World’s Most Notorious Spy Tool: A New York Times investigation reveals the story behind how Mexico became the first and most prolific user of Pegasus. It’s still using it, despite promising to stop.
Report names connected medical devices with the biggest cybersecurity risks: Nurse call systems, infusion pumps and medication dispensing technologies are the riskiest medical devices with Internet connectivity, according to security company Armis. … The conclusion is based on an analysis of common vulnerabilities and exposures (CVEs). Armis’ assessment found 39% of nurse call systems and 27% of infusion pumps have unpatched critical severity CVEs. … The report comes as the U.S. Food and Drug Administration prepares to start requiring medical device makers to provide cybersecurity information as part of their pre-market submissions. https://www.medtechdive.com/news/medical-device-cybersecurity-risk/648270/
Lawmakers Reintroduce Bill to Bolster Cybersecurity of K-12 Schools: The bipartisan, bicameral legislation directs CISA to provide primary and secondary schools with more targeted cyber information and resources to combat a rise in ransomware attacks. https://www.nextgov.com/cybersecurity/2023/04/lawmakers-reintroduce-bill-bolster-cybersecurity-k-12-schools/385366/
How Investigators Cracked a $3.4 Billion Crypto Heist: Jimmy Zhong appeared to have pulled off the perfect crime. In December 2012, he stumbled upon a software bug that allowed him to steal 50,000 bitcoins from a site on the dark web called the Silk Road. WSJ’s Robert McMillan explains how Zhong’s stolen crypto stayed hidden until investigators developed better ways to track down crypto criminals. https://www.wsj.com/podcasts/the-journal/how-investigators-cracked-a-34-billion-crypto-heist/1D51D374-253D-4829-A4FB-883BDA2B96F4
Capita confirms hackers stole data in recent cyberattack: Outsourcing giant Capita has published an update on the cyber-incident that impacted it at the start of the month, now admitting that hackers exfiltrated data from its systems. https://www.bleepingcomputer.com/news/security/capita-confirms-hackers-stole-data-in-recent-cyberattack/
3CX Breach Was a Double Supply Chain Compromise: We learned some remarkable new details this week about the recent supply-chain attack on VoIP software provider 3CX. The lengthy, complex intrusion has all the makings of a cyberpunk spy novel: North Korean hackers using legions of fake executive accounts on LinkedIn to lure people into opening malware disguised as a job offer; malware targeting Mac and Linux users working at defense and cryptocurrency firms; and software supply-chain attacks nested within earlier supply chain attacks. https://krebsonsecurity.com/2023/04/3cx-breach-was-a-double-supply-chain-compromise/
Manatee County falls victim to cybercrime that could cost taxpayers $1.4 million: Cyber criminals pulled a fast one on Manatee County, and it could cost taxpayers $1.4 million. All it took was an email and a fake invoice. https://www.fox13news.com/news/manatee-county-falls-victim-to-cybercrime-that-could-cost-taxpayers-1-5-million
Section 4 – Managing Information Security and Privacy in Your Organization.
5 steps to help achieve a cybersecurity mindset: Throughout this week on SiliconRepublic.com, we’ve heard from several professionals working across the cybersecurity industry, from cyber risk analysts all the way up to security leaders. … One unifying message that has come through from all of these experts is that having a strong cybersecurity mindset within any business is key to ensuring your organisation is as prepared as it can be as the threat landscape continues to grow. It’s all well and good knowing that you need a strong security mindset, but what does that actually look like and how can you ensure both you as a leader and the rest of your team start thinking with cybersecurity baked into your plans? https://www.siliconrepublic.com/business/cybersecurity-mindset-leaders-bt-michael-mcnamara
7 cybersecurity mindsets that undermine practitioners and how to avoid them: CISOs and other security practitioners can sometimes see things from a negative perspective, which is understandable given the nature of the job. But correcting how we see the role of cybersecurity can lead to much more positive outcomes. https://www.csoonline.com/article/3693255/7-cybersecurity-mindsets-that-undermine-practitioners-and-how-to-avoid-them.html


