A weekly aggregation of important cybersecurity and privacy news helping you meet your data care challenges and responsibilities.
Stan’s Top-3
Our lead story this week is a in-depth story of government cyber-surveillance by noted journalist Ronan Farrow . Cyber-surveillance is a technology that can be used for good and bad. We want our government to use surveillance technology to track cybercriminals but we don’t want them to track journalists and others who might oppose the government. Farrow’s story details the work of the NSO Group and their advanced Pegasus spyware and how it continues to be used to spy on journalists. … I’ll be talking to Nicole Perlroth about Pegasus at our May 4 webinar. Ms. Perlroth wrote about Pegasus in her book This is how they tell me the world ends.
- How Democracies Spy on Their Citizens: The inside story of the world’s most notorious commercial spyware and the big tech companies waging war against it. The New Yorker, April 18, 2022
Our next story from 60 minutes is an overview of the Cybersecurity & Infrastructure Security Agency’s (CISA) Shields Up program. As Agency Director Jen Easterly tells Bill Whitaker “We are seeing evolving intelligence about Russian planning for potential attacks. … It’s all about preparation not panic.” And as SecureTheVillage regularly points out: Everyone from the Board Room to the Living Room must do their part.
- Launching Shields Up to help organizations prepare for malicious cyberattacks: “We are seeing evolving intelligence about Russian planning for potential attacks, and we have to assume that there’s going to be a breach,” Cybersecurity and Infrastructure Security Agency Director Jen Easterly tells Bill Whitaker. … CISA has launched a program called Shields Up to help organizations prepare for malicious cyberattacks, and encourage U.S. industry to share information with the government regarding suspected intrusions in their systems. 60 Minutes, April18, 2022
A still too common information security misconception is that it is a technology problem for IT to manage. Like so many other dangerous ideas, this one is of course partly true; IT does have a role to play. But the more important role is leadership and tone at the top. With this as backdrop, our next story from our friend Bob Zukis of the Digital Directors Network discusses the SEC’s proposed rules to require disclosure of cybersecurity expertise on Boards.
- SEC proposes transformational cyber changes to the boardroom: The SEC recently proposed new rules that would require U.S. public company boardroom disclosure of corporate directors with cybersecurity expertise. This is currently a relatively rare skillset within the ranks of most corporate boards, not just in the U.S. but worldwide. Forbes, April 18, 2022
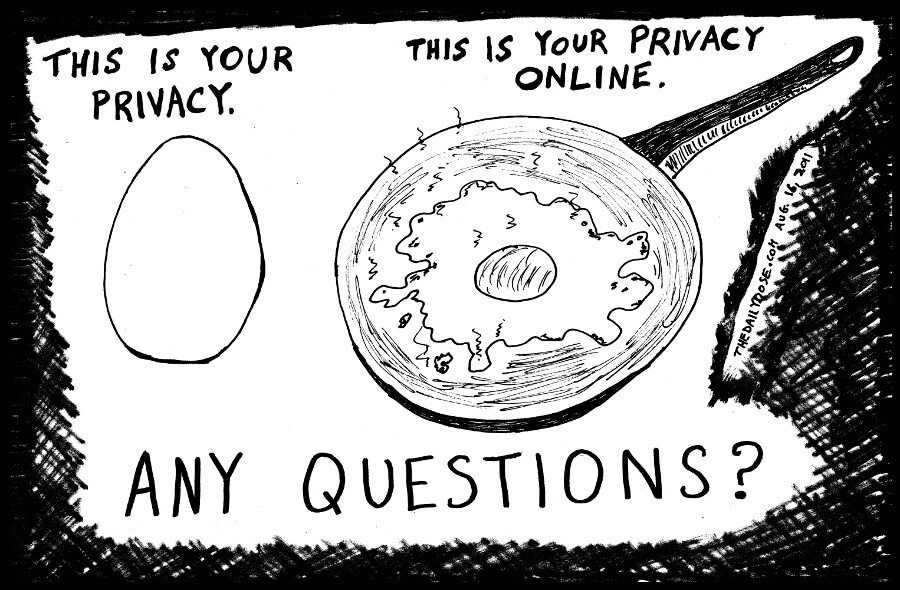
Cyber Humor
The Front Page
Other front page cybersecurity and privacy stories.
Our other front page stories all reflect the same theme. Cyberspace is dangerous so be careful out there. All of these stories have one thing in common – they illustrate the range of challenges we face in securing our data against attack. As CISA Director Jen Easterly said in the 60 Minutes piece, it’s about preparation, not panic. And as Sun Tzu said, if you don’t know your enemy you will be imperiled in every battle.
- FBI warns agricultural sector of heightened risk of ransomware attacks: The FBI on Wednesday alerted food and agriculture companies to be prepared for ransomware operatives to potentially attack agricultural entities during planting and harvest seasons — a time frame the feds warned is more likely to draw the attention of ransomware actors bent on leveraging the sector at its most vulnerable, including now as the spring planting season gets underway. Cyberscoop, April 20, 2022
- North Korean hackers are targeting blockchain companies with malicious crypto-stealing apps: In a joint advisory issued on Monday, the FBI, CISA and the U.S. Treasury said they had observed the North Korean-backed threat actors targeting a variety of organizations in the blockchain and cryptocurrency industries, including crypto exchanges, cryptocurrency trading companies, venture capital funds that have invested in cryptocurrency and individuals known to hold large amounts of cryptocurrency or valuable non-fungible tokens (NFTs) and play-to-earn video games. Tech Crunch, April 19, 2022
- Ransomware: This gang is getting a lot quicker at encrypting networks: A highly successful and aggressive ransomware gang is getting even faster at encrypting networks as they look to extort ransom payments from as many victims as possible. ZD Net, April 20, 2022
- Cybercrime Is Escalating From Bank Heists to Market Manipulation: For the fifth year in a row, I interviewed 130 chief information security officers and security leaders at top financial institutions around the world about how they’re being targeted by cybercriminals and what their biggest concerns are regarding the security of the financial sector. From ransomware attacks to market manipulation, it’s evident that today’s cybercrime cartels are more organized and destructive than ever before. Tom Kellermann, Barron’s, April 20, 2022
- Zero-Day Exploit Use Exploded in 2021: Ransomware and other financially motivated threat actors joined nation-state-backed groups in leveraging unpatched flaws in attack campaigns, new data shows. … Threat actors exploited more zero-day vulnerabilities in 2021 than any prior year and mostly in software from Microsoft, Google, and Apple. DARK Reading, April 21, 2022
- Hackers Sneak ‘More_Eggs’ Malware Into Resumes Sent to Corporate Hiring Managers: A new set of phishing attacks delivering the more_eggs malware has been observed striking corporate hiring managers with bogus resumes as an infection vector, a year after potential candidates looking for work on LinkedIn were lured with weaponized job offers. The Hacker News, April 21, 2022
- “Smishing” Scam Texts Are Getting More Common (and More Annoying): Attempts to steal your data from text messages are reportedly on the rise. Smishing scams averaged a $900 loss per report filed by the FTC in 2021. … You’ve probably gotten one already: a text from a strange number (maybe even your own) advertising CBD gummies, confirming a package delivery, or letting you know a bill has been paid, complete with a seemingly unsuspecting link. These texts are scams called “smishing,” and apparently they are on the rise. Gizmodo, April 20, 2022
- T-Mobile customers warned of unblockable SMS phishing attacks: An ongoing phishing campaign targets T-Mobile customers with malicious links using unblockable texts sent via SMS (Short Message Service) group messages. Bleeping Computer, April 15, 2022
- Here’s why your digital footprints are more than a privacy risk: They can actually help hackers infiltrate computer networks. … Phishing attacks have doubled since early 2020. The success of phishing attacks depends on how authentic the contents of messages appear to the recipient. All phishing attacks require certain information about the targeted people, and this information can be obtained from their digital footprints. Interesting Engineering, April 16, 2022
Picking up on the above Sun Tzu quote, he also said those that know neither themselves nor their enemy are defeated in every battle. In cybersecurity as in any win-lose endeavor: it’s what you don’t know that you don’t know that gets you into the biggest trouble. it’s about preparation, not panic.
- Beanstalk founders dismissed concerns about governance attacks before losing $182 million: In Discord chats, community members asked about vulnerability to flash loans but were largely ignored … On April 17th, the decentralized finance (DeFi) project Beanstalk Farms was exploited for $182 million after an attacker mounted a lightning-fast hostile takeover, buying a controlling stake of tokens and immediately voting to send themself all of the funds. The Verge, April 22, 2022
- Terra Users Lose $4.3M in Crypto to Phishing Scam Over 10 Days: SlowMist – a blockchain security firm – has identified dozens of crypto addresses that have appeared to fall victim to a phishing scam on the Terra network since April 12th. The scammer’s address has reportedly reeled in $4.31M in assets up until the time of writing. Crypto Potato, April 21, 2022
Security Nonprofit of the Week
Our kudos this week to the Center for Internet Security (CIS®) and the great work they do to make the connected world a safer place for people, businesses, and governments. Strong proponents of collaboration and innovation, CIS® is a community-driven nonprofit responsible for the CIS Controls®, CIS Benchmarks™, and CIS Hardened Images®. CIS is also home to the Multi-State Information Sharing and Analysis Center® (MS-ISAC®) and the Elections Infrastructure Information Sharing and Analysis Center® (EI-ISAC®).
Live on Cyber with Dr. Stan Stahl – Live on LinkedIn

Live on Cyber with Dr. Stan Stahl: Join Julie Morris and me as we discuss the latest in cybersecurity. This week we talk about the “swiss army knife of hacking tools” discovered attacking our industrial control systems; the attempted breach of an undersea cable providing phone, Internet and other communication services to Hawaii; and how North Korea uses cybercrime to support their economy. SecureTheVillage, April 20, 2022
Nicole Perlroth. Register Now. Invitation to Sponsor.
SecureTheVillage presents Nicole Perlroth, Award-winning Cybersecurity Journalist, New York Times Bestselling Author, and CISA advisor. A Virtual Learning Opportunity By & For Leaders in Cybersecurity. May 4, 11:00AM Pacific. Registration now open. Sponsorships still available.

Section 2 – Personal Data Care – Security and Privacy
Important data care stories for protecting yourself and your family.
In addition to our Smishing stories on the Front-Page, here’s a story for Lenovo laptop users, please check to see if you’re vulnerable to these attacks. If you are, you will need to update your BIOS.
- Millions of Lenovo Laptops Contain Firmware-Level Vulnerabilities: Three flaws present in consumer laptops can give attackers a way to drop highly persistent malware capable of evading methods to remove it, security vendor says. … More than 100 different Lenovo consumer laptop computers, used by millions of people worldwide, contain firmware-level vulnerabilities that give attackers a way to drop malware that can persist on a system even after a hard-drive replacement or operating system re-install. DARK Reading, Updated April 20, 2022
Section 3 – General Data Care Stories – Cybersecurity and Privacy
Cybersecurity and privacy stories for those wanting a deeper look.
Let’s start off the rest of this week’s news with a couple of positive stories. If you remember our story last week of how North Korea stole over $600m. Well now Binance has been able to freeze almost 6% of the stolen funds. It’s not much but it suggests we’re getting better at tracking crypto payments. And Visa’s new initiatives to fight cybercrime will only keep up the pressure on the cybercriminals … now if we can only get everyone involved in data care.
- Binance freezes stolen Axie Infinity crypto after North Korean hackers move funds: Binance CEO Changpeng Zhao said the cryptocurrency platform has frozen $5.8 million in funds that were stolen from popular DeFi platform Ronin Network by cybercriminals connected to the North Korean government. … The US Treasury also expanded its sanctions against the group to include new addresses being used to launder the money. The Record, April 22, 2022
- Visa Says It Will Take New Actions to Fight Cybercrime: Visa wrote in a blog that digital payments have become more important, with a level of reliability and speed, so the company has taken more of a responsibility to fight fraud and keep transactions secure. PYMNTS, April 20, 2022
On the war front, the New York Times had an interesting article this week on hackers claiming to have penetrated some major Russian institutions.
- Hackers Claim to Target Russian Institutions in Barrage of Cyberattacks and Leaks: Hackers claim to have broken into dozens of Russian institutions over the past two months, including the Kremlin’s internet censor and one of its primary intelligence services, leaking emails and internal documents to the public in an apparent hack-and-leak campaign that is remarkable in its scope. New York Times, April 22, 2022
The Russian Conti ransomware group is in the news again this week with two stories. The first story is of particular interest as it claims that Conti launched a ransomware attack in Costa Rica with the intent of destabilizing a government transition.
- Conti ransomware attack was aimed at destabilizing government transition, Costa Rican president says: Several systems operated by the government of Costa Rica were hit with a ransomware attack this week, according to the country’s president Carlos Alvarado Quesada. … The Conti ransomware group added systems connected to several government agencies to its list of victims on Tuesday and Wednesday. Government officials confirmed Conti’s involvement. The Record, April 22, 2022
- Conti’s Ransomware Toll on the Healthcare Industry: Conti — one of the most ruthless and successful Russian ransomware groups — publicly declared during the height of the COVID-19 pandemic that it would refrain from targeting healthcare providers. But new information confirms this pledge was always a lie, and that Conti has launched more than 200 attacks against hospitals and other healthcare facilities since first surfacing in 2018 under its earlier name, “Ryuk.” KrebsOnSecurity, April 18, 2022
And LAPSUS$ — the cybercrime group that hacked NVIDIA, OKTA, and others—is now alleged to have also stolen T-Mobile source code in an attack.
- Leaked Chats Show LAPSUS$ Stole T-Mobile Source Code: KrebsOnSecurity recently reviewed a copy of the private chat messages between members of the LAPSUS$ cybercrime group in the week leading up to the arrest of its most active members last month. The logs show LAPSUS$ breached T-Mobile multiple times in March, stealing source code for a range of company projects. T-Mobile says no customer or government information was stolen in the intrusion. KrebsOnSecurity, April 22, 2022
Our “cyber-law” story this week tells of another contribution to the evolving body of cybersecurity law focused on what counts as “reasonable security.” In this story, defendants agreed to pay $11 million to settle a class action lawsuit alleging that one of the defendants, Zywave, failed to implement “reasonable” security practices.
- Zywave, Insurance Technologies Corp. Data Breach $11M Class Action Lawsuit Settlement: Insurance Technologies Corp. (ITC) and Zywave Inc. agreed to pay a combined $11 million as part of a class action lawsuit settlement to resolve claims surrounding a 2021 data breach that compromised sensitive consumer information. Top Class Actions, April 19, 2022
Our final article is an essay on privacy and security suggesting that we can better control the loss of our private information by limiting the amount of information that companies are legally allowed to collect about us.
- Companies lose your data and then nothing happens: Data breaches are everywhere and consequences are ??? … At this point, it’s hard not to imagine that at least some of your personal information isn’t for sale in some dark corner of the internet. After all, data breaches are happening constantly. Companies suck up customers’ details and then, try as they might — and let’s assume they really try — declare that it’s been leaked or hacked. You know the drill; the subsequent breach announcement goes a little something like this: “Oops!! We were the victims of a cyberattack, and by extension, so were you! It affected ??? people and we think ??? information was involved, but we’re still kind of guessing here at what happened. Hopefully you have some sort of identity theft protection, which maybe we’re offering and maybe not. But regardless, love you! We’re family! Please come back soon!” Vox, April 21, 2022
Section 4 – Data Care in the Organization
Stories to support executives and top management in securing their organizations.
This next story reflects the reality that too many mid-size and smaller organizations lack the information security management expertise to effectively protect the data entrusted to them. It was written by my friend and colleague, David Lam. David’s the Partner-in-Charge of our information security management team at SecureTheVillage’s Platinum Sponsor, Miller Kaplan.
- Are Your And Your Vendors’ Information Security Practices Backed By Experts?: When evaluating vendors, you may often hear them make claims or assertions as to the existence of their information security practices; however, many of these claims, upon scrutiny/questioning, turn out to be empirically false. Forbes, April 13, 2022
HP’s CISO, Joanna Burkey, is the author of an excellent piece on improving the practice of information security management.
- 3 Ways We Can Improve Cybersecurity: To better manage risks, companies can concentrate on resilience, sharing information to protect from cyber threats, and making the cybersecurity tent bigger by looking at workers with nontraditional skill sets. DARK Reading, April 22, 2022
The Pentagon continues to explore ways to assist its 300,000 contractors quickly come up to speed in basic information security management. This is a basic challenge with no easy answers. From the perspective of the information at risk and protecting the supply chain, CMMC is a reasonable requirement on defense contractors. From the perspective of the heavy lift required for too many of these contractors coupled with the shortage of qualified information security subject matter experts, it’s not realistic to expect these contractors to be able to reasonably achieve CMMC. Locked between the proverbial rock and hard place, the Pentagon is properly looking for creative ways to quickly raise the bar.
- Pentagon eyeing the cloud to help firms meet CMMC cybersecurity requirements: The Pentagon is assessing whether to develop cloud service offerings to help contractors meet requirements for its cyber certification program, according to the Defense Department’s deputy chief information officer. Breaking Defense, April 22, 2022
Kudos this week to CISA, NIST, and several other federal agencies for providing our organizations with vital information and guidance directly relevant to effectively managing information security. Every organization needs to take advantage of the guidance they provide.
- CISA, FBI, NSA, and International Partners Issue Advisory on Demonstrated Threats and Capabilities of Russian State-Sponsored and Cyber Criminal Actors: The Cybersecurity and Infrastructure Security Agency (CISA), along with the Federal Bureau of Investigation (FBI), National Security Agency (NSA), Australian Cyber Security Centre (ACSC), Canadian Centre for Cyber Security (CCCS), National Cyber Security Centre New Zealand (NZ NCSC), and the United Kingdom’s National Cyber Security Centre (NCSC-UK) and National Crime Agency (NCA), with contributions from industry members of the Joint Cyber Defense Collaborative, issued a joint Cybersecurity Advisory on Russian state-sponsored and criminal cyber threats to critical infrastructure that could impact organizations both within and beyond Ukraine. CISA, April 20, 2022
- NIST revamps aging enterprise patch management guidance: The US National Institute of Standards and Technology (NIST) has overhauled its enterprise patch management guidance for the first time in nearly a decade. Portswigger, April 21, 2022


