SecureTheVillage Calendar
Technology & Security Management HappyHour: Introduction to the ME-ISAC with Founder Chris Taylor. August 4 @ 4:30 pm – 5:30 pm PDT
Information Security Management Webinar: NIST Cyberprivacy Frameworks. August 13 @ 10:00 am – 11:00 am PDT
Dealing With Cyber Bullies: A Personal Account August 13 @ 2:00 pm – 3:00 pm PDT
Financial Services Cybersecurity Roundtable – August 2020. August 21 @ 8:00 am – 10:00 am PDT
CyberFreedomWebinar: Taming The Tiger: How to Detect, Deter, & Defeat Disinformation with Marc Ambinder. September 8 @ 10:00 am – 11:00 am PDT
Information Security Management Webinar: The Great Reboot: Succeeding in a World of Catastrophic Risk and Opportunity with Bob Zukis & Others. September 10 @ 10:00 am – 11:00 am PDT
Individuals at Risk
Cyber Privacy
IndieFlix streaming service leaves thousands of confidential agreements, filmmaker SSNs, videos exposed on public server: The CyberNews research team discovered an unsecured data bucket on a publicly accessible Amazon Simple Storage (S3) server containing confidential data belonging to IndieFlix. Cybernews, July 30, 2020
Identity Theft
Is Your Chip Card Secure? Much Depends on Where You Bank: Chip-based credit and debit cards are designed to make it infeasible for skimming devices or malware to clone your card when you pay for something by dipping the chip instead of swiping the stripe. But a recent series of malware attacks on U.S.-based merchants suggest thieves are exploiting weaknesses in how certain financial institutions have implemented the technology to sidestep key chip card security features and effectively create usable, counterfeit cards. KrebsOnSecurity, July 30, 2020
Here’s Why Credit Card Fraud is Still a Thing: Most of the civilized world years ago shifted to requiring computer chips in payment cards that make it far more expensive and difficult for thieves to clone and use them for fraud. One notable exception is the United States, which is still lurching toward this goal. Here’s a look at the havoc that lag has wrought, as seen through the purchasing patterns at one of the underground’s biggest stolen card shops that was hacked last year. KrebsOnSecurity, July 29, 2020
Cyber Warning
Android malware posing as Covid-19 contact tracing apps: You might want to think twice before downloading a contact tracing app from a link. TechRadarPro, July 31, 2020
That job offer in your inbox might be part of a North Korean cyberattack: Professionals in the aerospace and defense industries should watch out; a wave of fake job offers containing malicious documents have been spotted in the wild by McAfee researchers. TechRepublic, July 31, 2020
Cyber Update
Nearly 80 Netgear routers have a major security flaw and half won’t be patched … Update if you can. Replace if you can’t: Netgear has decided not to issue a firmware update to 45 of its nearly 80 router and gateway models affected by a remote code execution vulnerability that was disclosed at the end of June. Left unpatched, a hacker could effectively bypass the login credentials and take control of the router. PC Gamer, July 30, 2020
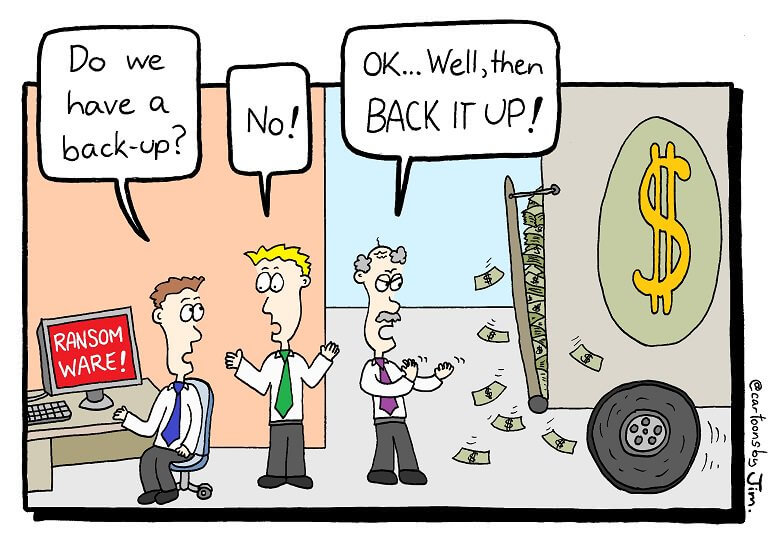
Cyber Humor
Information Security Management for the Organization
Cybersecurity in the C-Suite
What’s New in the 2020 Cost of a Data Breach Report: In a world of uncertainty and change, it’s a comfort that some things are consistent year after year. Now in its 15th year, the annual Cost of a Data Breach Report, with research by the Ponemon Institute and published by IBM Security, continues to provide a detailed view of the financial impacts security incidents can have on organizations, with historical data revealing trends in data breach causes and consequences. SecurityIntelligence, July 28, 2020
Business ID Theft Soars Amid COVID Closures: Identity thieves who specialize in running up unauthorized lines of credit in the names of small businesses are having a field day with all of the closures and economic uncertainty wrought by the COVID-19 pandemic, KrebsOnSecurity has learned. This story is about the victims of a particularly aggressive business ID theft ring that’s spent years targeting small businesses across the country and is now pivoting toward using that access for pandemic assistance loans and unemployment benefits. KrebsOnSecurity, July 27, 2020
Information Security Management
Top 6 cybersecurity trends to watch for at Black Hat USA 2020: Experts weigh in to share their thoughts on the hottest topics to expect at this year’s all-digital Black Hat conference. TechRepublic, July 31, 2020
Is “Dumpster Fire” too strong a word to describe CMMC compliance concerns with many MSPs?: For a lot of companies, it is not what they think it is and the reason is primarily based on misplaced assumptions. Too many people and companies view Cybersecurity Maturity Model Certification (CMMC), including compliance with it, as strictly an IT issue. To compound this issue, for most SMBs within the Defense Industrial Base (DIB), IT is rarely staffed in-house and is usually outsourced to a local/regional Managed Service Providers (MSP) or Managed Security Service Providers (MSSP). The assumption is that these “IT experts” will handle all manners of IT and cybersecurity for them. LinkedIn, July 29, 2020
Is your company safe from this cybersecurity flaw?: 2019 was one of the worst years on record for attacks and breaches. Over the course of 2019 there was a massive 54% increase in data breaches – many with dire consequences. HRD, July 29, 2020
How and Why to Take a Holistic Approach to Threat Modeling: By taking a broader, more expansive view of threat modeling, organizations can consider the whole picture of their security strategy and improve efficiency. Threat modeling is a systematic approach to finding, prioritizing and fixing security threats, but it can be much more. It invites an exercise in systematic collaborative thinking, and as such its benefits go beyond tangible security fixes. SecurityIntelligence, July 29, 2020
Cyber Warning
DDoS Attacks Increase in Size, Frequency and Duration: Distributed denial of service (DDoS) attacks are increasing in size, frequency and duration. SecurityIntelligence, July 30, 2020
North Korea’s Lazarus brings state-sponsored hacking approach to ransomware: In search of funds for country’s weapons program, Lazarus goes hunting for big game. ars technica, July 29, 2020
Kaspersky: New hacker-for-hire mercenary group is targeting European law firms: The Deceptikons group is the second major hacker-for-hire mercenary group exposed this year after Dark Basin. ZDNet, July 29, 2020
Cyber Talent
Cybersecurity skills crisis worsens for fourth year in a row, impacting 70% of organizations: Fourth annual global study from ESG and ISSA finds 45 percent state cybersecurity skills shortage has only gotten worse over the past few years. Why has nothing changed? SecurityMagazine, July 30, 2020
Cybersecurity in Society
Cyber Crime
The Garmin Hack Was a Warning: As ransomware groups turn their attention to bigger game, expect more high-profile targets to fall. Wired, August 1, 2020
Labour Party is latest victim of Blackbaud ransomware attack … Widening Blackbaud data breach ensnares the Labour Party as the cloud software firm continues to duck questions about its behaviour: The widening Blackbaud data breach has spread into the world of politics, with the Labour Party becoming the latest organisation to step forward as a victim of the US firm’s ransomware incident. Reports suggest that data on Labour’s donors, including information on their political opinions and views, may have been put at risk. ComputerWeekly, July 31, 2020
Questions Persist About Ransomware Attack on Blackbaud … CRM Firm Admits Paying Ransom; Waited Weeks to Notify Victims Despite GDPR Rules: Numerous unanswered questions persist concerning a ransomware outbreak at Blackbaud, which provides cloud-based marketing, fundraising and customer relationship management software used by thousands of charities, universities, healthcare organizations and others. BankInfoSecurity, July 30, 2020
Travel company CWT avoids ransomware derailment by paying $4.5m blackmail demand: According to reports, Minnesota-based business travel company CWT is the latest victim of the latest trend in ransomware. NakedSecurity, July 30, 2020
Hackers Demand Hefty Ransom After Successful Ransomware Attack on Telecom Giant: Telecom Argentina, the largest telecommunications company in the country, was hit by a ransomware attack involving the Sodinokibi ransomware group. The attack disrupted internal systems of the telecom company. The ransomware gang are demanding $7.5 million in Monero (XMR) crypto exchanges, but the amount would double if the company fails to pay within 48 hours. CPO, July 30, 2020
Hacker leaks 386 million user records from 18 companies for free: A threat actor is flooding a hacker forum with databases exposing expose over 386 million user records that they claim were stolen from eighteen companies during data breaches. BleepingComputer, July 28, 2020
Garmin Confirms Ransomware Attack As Services Come Back Online: Just a few days ago, Garmin GRMN -1.4% chalked up a worldwide service outage to a maintenance issue. Today, the company cleared the air. A ransomware attack was the real culprit. Forbes, July 27, 2020
Cyber Attack
Twitter: Epic Account Hack Caused by Mobile Spearphishing: Hackers “mislead certain employees” to gain access to internal tools to take over high-profile accounts and push out a Bitcoin scam. ThreatPost, July 31, 2020
Russia’s GRU Hackers Hit US Government and Energy Targets … A previously unreported Fancy Bear campaign persisted for well over a year—and indicates that the notorious group has broadened its focus: RUSSIA’S GRU MILITARY intelligence agency has carried out many of the most aggressive acts of hacking in history: destructive worms, blackouts, and—closest to home for Americans—a broad hacking-and-leaking operation designed to influence the outcome of the 2016 US presidential election. Now it appears the GRU has been hitting US networks again, in a series of previously unreported intrusions that targeted organizations ranging from government agencies to critical infrastructure. Wired, July 24, 2020
Cyber Espionage
Exclusive: China-backed hackers ‘targeted COVID-19 vaccine firm Moderna’: WASHINGTON (Reuters) – Chinese government-linked hackers targeted biotech company Moderna Inc, a U.S.-based coronavirus vaccine research developer, this year in a bid to steal data, according to a U.S. security official tracking Chinese hacking. Reuters, July 30, 2020
Know Your Enemy
The Cold War Bunker That Became Home to a Dark-Web Empire: An eccentric Dutchman began living in a giant underground facility built by the German military—and ran a server farm beloved by cybercriminals. The New Yorker, July 27, 2020
National Cybersecurity
Leaders Seek a Grand Strategy for Cybersecurity … The Cyberspace Solarium Commission’s proposed strategy of layered deterrence: Geopolitics in an online world are defined by what’s changed and what hasn’t. AFCEA, August 1, 2020
Cyber Freedom
New Initiative Links Cybersecurity Pros to Election Officials … A University of Chicago Harris School of Public Policy initiative is building a database of cybersecurity volunteers: The Election Cyber Surge program opens a line of communication between U.S. State and Local election officials and a network of volunteer cybersecurity technologists for direct communication about cybersecurity matters leading up to November 2020. Harris Public Policy, University of Chicago
Cyber Lawsuit
Epiq Systems Faces California Privacy Suit From Cyber Attack: Epiq Systems Inc., a legal services provider, is facing a federal lawsuit in California alleging it is at fault for malware and ransomware attacks that exposed data in violation of the state’s landmark privacy law. Bloomberg, July 30, 2020
Cyber Enforcement
Three people have been charged for Twitter’s huge hack, and a Florida teen is in jail … Update: The Tampa teen allegedly pretended to work for Twitter’s IT department: Early on July 31st, the FBI, IRS, US Secret Service, and Florida law enforcement placed 17-year-old Graham Clark of Tampa, Florida, under arrest. He’s accused of being the “mastermind” behind the biggest security and privacy breach in Twitter’s history, one that took over the accounts of President Barack Obama, Democratic presidential candidate Joe Biden, Bill Gates, Elon Musk, Kanye West, Apple, and more to perpetrate a huge bitcoin scam on July 15th. The Verge, July 31, 2020
Disinformation
Anti-NATO Disinformation Campaign Leveraged CMS Compromises: Researchers uncovered a disinformation campaign aiming to discredit NATO via fake news content on compromised news websites. ThreatPost, July 31, 2020
Cyber Research
IBM completes successful field trials on Fully Homomorphic Encryption: FHE allows computation of still-encrypted data, without sharing the secrets. ars technica, July 31, 2020


