A weekly aggregation of important cybersecurity and privacy news designed to educate, support, and advocate; helping you meet your data care challenges and responsibilities.
Stan’s Top of the News
The nation’s Emergency Alert System allows the federal government, the president or state-level officials to send out emergency warnings about potential weather issues and AMBER alerts for missing children. Imagine if it stopped working or terrorists took it over to issue false alerts. That’s what could happen if TV stations, radio stations, and cable networks fail to update their equipment to fix vulnerabilities that have been discovered in the software. Like oil pipelines and meat processing, we are all connected by technology that – in some cases – is hanging by a thread. That’s why there’s such a national push towards improved cybersecurity.
- FEMA issues warning to emergency alert system managers that devices could be hacked: The Federal Emergency Management Agency (FEMA) issued a warning this week to participants in the emergency alert system (EAS) that vulnerabilities can be used to allow threat actors to issue alerts over TV, radio, and cable networks. The Record, August 5, 2022
As if things in cyber aren’t bad enough already, things will soon be a lot more challenging when fake videos become so good that they are indistinguishable from real ones.
- The impact of deepfakes: How do you know when a video is real?: In a world where seeing is increasingly no longer believing, experts are warning that society must take a multi-pronged approach to combat the potential harms of computer-generated media. … As Bill Whitaker reports this week on 60 Minutes, artificial intelligence can manipulate faces and voices to make it look like someone said something they never said. The result is videos of things that never happened, called “deepfakes.” Often, they look so real, people watching can’t tell. Even Justin Bieber has been tricked by a series of deepfake videos on the social media video platform TikTok that appeared to be of Tom Cruise. 60 Minutes, July 31, 2022
After the above two somewhat dystopian stories, let’s end the Top of the News with a happy-ending story. Imagine setting off for dinner at a nice quiet restaurant you’ve been looking forward to for a month. Now imagine that hackers had taken over Waze, Google Maps, and Apple Maps, and directed everybody to that restaurant. As you get close, you’d be caught in a traffic jam of monumental proportion. There goes your beautiful dinner. On the Internet, that’s called a “distributed denial of service” attack (DDoS). In the following feel-good story, Akamai blocked the largest-ever distributed denial of service attack Europe has ever seen.
- Akamai: We stopped record DDoS attack in Europe: A ‘sophisticated, global botnet’ held an Eastern European biz under siege over 30 days. … Akamai Technologies squelched the largest-ever distributed denial-of-service (DDoS) attack in Europe earlier this month against a company that was being consistently hammered over a 30-day period. The Register, August 1, 2022
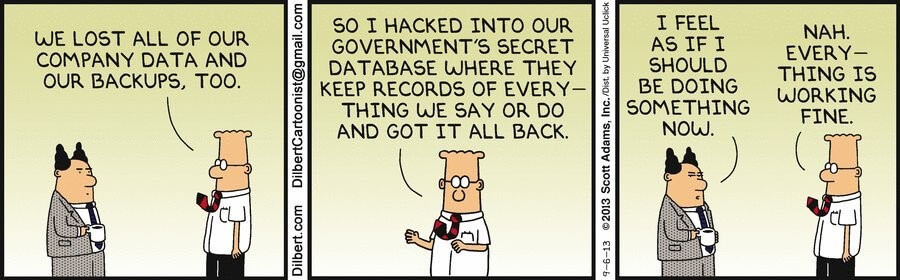
Cyber Humor
Security Nonprofit of the Week
Kudos this week to Nonprofit Cyber. Nonprofit Cyber is a coalition of implementation-focused cybersecurity nonprofits to collaborate, work together on projects, voluntarily align activities to minimize duplication and increase mutual support, and link the community to key stakeholders with a shared communication channel. SecureTheVillage is a proud member of Nonprofit Cyber.
Live on Cyber with Dr. Stan Stahl – Live on LinkedIn

Live on Cyber with Dr. Stan Stahl: Julie and I riff this week on a profound quote of Nobel Prize winner Thomas Schelling: “One thing a person cannot do, no matter how rigorous his analysis or heroic his imagination, is to draw up a list of things that would never occur to him.” Julie and I talk about drawing up a list of data care, cybersecurity, and privacy things “that would never occur to him,” getting rid of the “nerd speak,” as CISA Director Jen Easterly calls it, while doing our best to avoid all too human “failures of imagination.”
Webinar Available: Roe v Wade: Critical Implications for Our Personal Privacy
Our recent community webinar on the privacy implications of Roe V Wade is now available for viewing on the SecureTheVillage website.
Section 2 – Personal Data Care – Security and Privacy
Important data care stories for protecting yourself and your family.
Another reminder of just how creative these cyber-criminals are. Please be careful out there.
- Scammers Sent Uber to Take Elderly Lady to the Bank: Email scammers sent an Uber to the home of an 80-year-old woman who responded to a well-timed email scam, in a bid to make sure she went to the bank and wired money to the fraudsters. In this case, the woman figured out she was being scammed before embarking for the bank, but her story is a chilling reminder of how far crooks will go these days to rip people off. KrebsOnSecurity, August 4, 2022
Let’s say you’ve got MFA on your gmail account and you aggressively keep your browser patched and updated. Secure? Pretty much so. But 100%? Absolutely not as the following story about a malicious browser extension shows.
- North Korea-backed hackers have a clever way to read your Gmail: Researchers have unearthed never-before-seen malware that hackers from North Korea have been using to surreptitiously read and download email and attachments from infected users’ Gmail and AOL accounts. … The malware, dubbed SHARPEXT by researchers from security firm Volexity, uses clever means to install a browser extension for the Chrome and Edge browsers, Volexity reported in a blog post. The extension can’t be detected by the email services, and since the browser has already been authenticated using any multifactor authentication protections in place, this increasingly popular security measure plays no role in reining in the account compromise. The extension isn’t available in Google’s Chrome Web Store, Microsoft’s add-ons page, or any other known third-party source and doesn’t rely on flaws in Gmail or AOL Mail to get installed. Ars Technica, August 3, 2022
Data care begins with you!! This next story provides instructions for managing the privacy settings of your cell carrier. It took all of a couple of minutes to set up my ATT account with minimal information sharing. No “Relevant Advertising.” No “Enhanced Relevant Advertising.” No “Third Party Services.” No thank you, ATT.
- Cell carrier privacy settings to change now: Your carrier can use your web history, app use and sometimes even location to help advertisers target you. … Apps and devices aren’t the only tech in your life due for a privacy check. Your cellphone carrier is likely peeking into your personal information, too. … In response to a reader question in April, we examined the privacy policies of the three major carriers in the United States — AT&T, T-Mobile and Verizon — and found that all of them can use data such as your web history for targeted advertising. The Washington Post, August 1, 2022
When I first saw this story, I thought “Here’s another of those so-what privacy stories. This is 2022. Of course my car is tracking me.” But in reading the story, I also discovered that I might be able to get a discount on my car insurance if I give my insurance company access to my driving information Hmmm?
- Who Is Collecting Data from Your Car?: A firehose of sensitive data from your vehicle is flowing to a group of companies you’ve probably never heard of. … Welcome to the world of connected vehicle data, an ecosystem of dozens of businesses you never knew existed. … Today’s cars are akin to smartphones, with apps connected to the internet that collect huge amounts of data, some of which is highly personal. … Most drivers have no idea what data is being transmitted from their vehicles, let alone who exactly is collecting, analyzing, and sharing that data, and with whom. … The Markup has identified 37 companies that are part of the rapidly growing connected vehicle data industry that seeks to monetize such data in an environment with few regulations governing its sale or use. The Markup, July 27, 2022
Here’s an important privacy story about our children’s personal information being put at risk by the security weaknesses of the companies collecting the information. The story quotes Hector Balderas, the attorney general of New Mexico, whose office has sued tech companies for violating the privacy of children and students, “There has really been an epic failure.”
- A Cyberattack Illuminates the Shaky State of Student Privacy: At a moment when education technology firms are stockpiling sensitive information on millions of school children, safeguards for student data have broken down. … The software that many school districts use to track students’ progress can record extremely confidential information on children: “Intellectual disability.” “Emotional Disturbance.” “Homeless.” “Disruptive.” “Defiance.” “Perpetrator.” “Excessive Talking.” “Should attend tutoring.” … Now these systems are coming under heightened scrutiny after a recent cyberattack on Illuminate Education, a leading provider of student-tracking software, which affected the personal information of more than a million current and former students across dozens of districts — including in New York City and Los Angeles, the nation’s largest public school systems. The New York Times, July 31, 2022
I always like being able to cover a story in Scientific American. This one is on the challenges of fighting robocalls.
- The Robocalls Problem Is So Bad That the FCC Actually Did Something: “Hello, we’ve been trying to reach you about your car’s extended warranty.” After years of seemingly unstoppable scam robocalls, this phrase is embedded into the minds of many of us. Last month the Federal Communications Commission (FCC) announced it was ordering phone providers to block any calls coming from a known car warranty robocall scam, offering hope that U.S. phone users may hear that all-too-familiar automated voice a little less often. … But there is more work required to crack down on these calls. After all, car warranty warnings are only one type of scam. To understand how robocallers reach us, and why it’s so hard to stop them, Scientific American spoke with Adam Doupé, a cybersecurity expert at Arizona State University. Scientific American, August 5, 2022
Here’s Wirecutter’s analysis of Two-Factor Authentication apps. I find a combination of Google and Microsoft authenticators works fine for me but if you’re looking for something else, this story may be helpful.
- The Best Two-Factor Authentication App: The most important thing you can do to increase your online security, alongside using a password manager, is to enable two-factor authentication. After interviewing three experts and testing seven authenticator apps, we think Authy has the best combination of compatibility, usability, security, and reliability. Wirecutter, July 27, 2022
Section 3 – A Deeper Look for the Cyber-Concerned Citizen
Data Care, cybersecurity and privacy stories to keep you informed.
National cybersecurity leads the general news this week.
- Stolen money from cyberattacks makes up a third of the funds for North Korea’s missile program, US official says … A US official said cyberattacks are a “core driver” of North Korea’s revenue and have become a major concern. … A 2022 UN report says that North Korean hackers walked away with more than $400 million in cryptocurrency during cyberattacks in 2021. Insider, July 29, 2022
- Cyberattack on Albanian government suggests new Iranian aggression: Tehran-linked hack of a NATO member is a significant escalation. … In mid-July, a cyberattack on the Albanian government knocked out state websites and public services for hours. With Russia’s war raging in Ukraine, the Kremlin might seem like the likeliest suspect. But research published on Thursday by the threat intelligence firm Mandiant attributes the attack to Iran. And while Tehran’s espionage operations and digital meddling have shown up all over the world, Mandiant researchers say that a disruptive attack from Iran on a NATO member is a noteworthy escalation. Ars technica, August 5, 2022
- Hacktivist group Anonymous is using six top techniques to ‘embarrass’ Russia: Anonymous has claimed to have hacked over 2,500 Russian and Belarusian sites. … In some instances, stolen data was leaked online in amounts so large it will take years to review.. … The hacks have also exposed Russia’s cybersecurity defenses to be far weaker than previously believed, say cybersecurity researchers. CNBC, July 28, 2022
With Europe experiencing energy challenges wrought by the Russian invasion of Ukraine, this next story lives in the intersection of cybercrime and national security.
- Ransomware Hit on European Pipeline & Energy Supplier Encevo Linked to BlackCat: Customers across several European countries are urged to update credentials in the wake of the attack that affected a gas-pipeline operator and power company. … Following a July 25 announcement that its subsidiaries had been breached in a ransomware attack, Encevo, an energy supplier based in Luxembourg, followed up a few days later with an update that teams were currently investigating the extent of the damage done. DarkReading, August 1, 2022
This was another terrible week for the crypto-currency crowd. I don’t work in the crypto space nor am I a crypto-speculator but, with years of experience in secure software engineering, I’m blown away at how poorly written their software algorithms and their “operational security” must be.
- Hackers drain nearly $200 million from crypto startup in ‘free-for-all’ attack: Hackers yanked almost $200 million in crypto from Nomad, a so-called blockchain bridge. … Blockchain bridges allow users to transfer tokens from one network to another. … They’ve become a prime target for hackers seeking to swindle investors out of millions. CNBC, August 2, 2022
- Thousands of Solana wallets drained in multimillion-dollar exploit: Solana, an increasingly popular blockchain known for its speedy transactions, has become the target of the crypto sphere’s latest hack after users reported that funds have been drained from internet-connected “hot” wallets. … An unknown actor drained funds from approximately 8,000 wallets on the Solana network, Solana’s Status Twitter account said. It’s estimated the loss so far is around $8 million. TechCrunch, August 3, 3022
- ZB Exchange Loses Nearly $5M in Suspected Hack, Pauses Withdrawals: The self-titled “world’s most secure” exchange may be the third crypto company to suffer a multimillion-dollar exploit this week. … Crypto exchange ZB Exchange has paused user withdrawals, likely in response to a suspected hack that appears to have drained nearly $5 million in tokens from the firm’s hot wallet on Tuesday. CoinDesk, August, 4, 2022
Security solutions provider Check Point Software released a report this week showing continued growth in ransomware, particularly in attacks on IT vendors and other technology service providers.
- Ransomware now strikes one in 40 organisations per week, Check Point finds: VARs, systems integrators, and distributors saw a 143% year-on-year increase in attacks during Q2. … Incidents have risen 59% year-on-year from one in 64 organisations being affected in Q2 2021, due to a combination of higher geopolitical tensions, an increase in remote working, as well as a willingness of organisations to pay the cost of the ransom. … Across the wider landscape, the second quarter of 2022 saw cyber-attacks hit an all-time high, increasing by 32% when compared to Q2 2021. … “Ransomware attacks are showing no signs of slowing down,” commented Omer Dembinsky, Data Group Manager at Check Point Software. IT Pro, July 27, 2022
Several stories on the legal front made the news this week. This includes a class action suit against Experian, an agreement by state Attorney Generals to launch a full-court press against the telecoms who make money by allowing robo-callers on their networks, and actions by law-enforcement in Australia and the United States to arrest and hold cyber-criminals responsible for their crimes.
- Class Action Targets Experian Over Account Security: A class action lawsuit has been filed against big-three consumer credit bureau Experian over reports that the company did little to prevent identity thieves from hijacking consumer accounts. The legal filing cites liberally from an investigation KrebsOnSecurity published in July, which found that identity thieves were able to assume control over existing Experian accounts simply by signing up for new accounts using the victim’s personal information and a different email address. KrebsOnSecurity, August 5, 2022
- US Attorneys General will take legal action against telecom providers enabling robocalls: They’re joining forces to form the Anti-Robocall Litigation Task Force…. The Attorneys General of all 50 states have joined forces in hopes of giving teeth to the seemingly never-ending fight against robocalls. … North Carolina AG Josh Stein, Indiana AG Todd Rokita and Ohio AG Dave Yost are leading the formation of the new Anti-Robocall Litigation Task Force. In Stein’s announcement, he said the group will focus on taking legal action against telecoms, particularly gateway providers, allowing or turning a blind eye to foreign robocalls made to US numbers. Engadget, August 4, 2022
- Alleged Russian Cryptocurrency Money Launderer Extradited to United States: Defendant Extradited from Greece to Face Charges Stemming from the Operation of BTC-e, an Illicit Bitcoin Exchange Alleged to Have Received Deposits Valued at Over $4 Billion. … Alexander Vinnik, 42, a Russian citizen, was charged in a 21-count superseding indictment in January 2017. Vinnik was taken into custody in Greece in July 2017 at the request of the United States. He made his initial appearance earlier today in federal court in San Francisco before U.S. Magistrate Judge Sallie Kim. … “After more than five years of litigation, Russian national Alexander Vinnik was extradited to the United States yesterday to be held accountable for operating BTC-e, a criminal cryptocurrency exchange, which laundered more than $4 billion of criminal proceeds,” said Assistant Attorney General Kenneth A. Polite, Jr. of the Justice Department’s Criminal Division. “This extradition demonstrates the Department’s commitment to investigating and dismantling illicit cyber activity and would not have been possible without the relentless work of the Justice Department’s Office of International Affairs. The Justice Department thanks the Government of Greece, particularly the Ministry of Justice, for all their efforts in securing the defendant’s transfer to the United States.” United States Department of Justice, August 5, 2022
- Australian police charge man with developing spyware used by more than 14,500 people: An Australian man faces up to 20 years in prison for allegedly creating and distributing spyware that became the subject of a global law enforcement operation. … The 24-year-old man, who has not been named by authorities, was arrested by Australian Federal Police (AFP) and appeared in a Brisbane court Friday where he was charged with six counts related to computer offenses. He is accused of creating the Imminent Monitor remote access Trojan (RAT) when he was 15, which authorities say was sold to more than 14,500 individuals across 128 countries. The Record, August, 1, 2022
Section 4 – Information Security and Privacy Management in the Organization
Stories to support executives and top management in securing their organizations and protecting privacy.
If you haven’t done so recently, take a look at your privacy policies. Are they still a fit for the kinds of data you collect and what you do with it.
- Privacy Policies – Some Simple Lessons: Online privacy policies are ubiquitous. Sometimes they are mandated by law – that’s been the case in California for years – and a variety of other states and federal agencies (like the Securities and Exchange Commission) require them as well. As a practical matter, almost every firm that has an online presence has a privacy policy. But it’s not enough to have a privacy policy – the policy has to be “right,” and failing to do that can open a company to liability. At the same time, done correctly, a privacy policy is an important asset. Robert E. Braun, Jeffer Mangels Butler Mitchell, SecureTheVillage Leadership Team, July 6, 2022
This story is not only a warning to always be on guard against phishing attacks, it’s also a reminder that nothing – not Multi-Factor Authentication (MFA) and not anything else either – is a panacea. There are no silver-bullets to ward off the enemy.
- Large-Scale Phishing Attacks Targeting Microsoft Enterprise Email Services Bypass MFA: Security researchers from ThreatLabz have uncovered a new strain of a large-scale phishing campaign using adversary-in-the-middle (AiTM) techniques along with several evasion tactics. … According to an advisory published by the company on Tuesday, similar AiTM phishing techniques were used in a separate phishing campaign described by Microsoft last month. … Now, ThreatLabz revealed that using intelligence gathered from the Zscaler cloud, it observed an increase in the use of advanced phishing kits in a large-scale campaign in June.
If you’re IT, here’s a story for you. Please, please, please make sure you’ve patched these vulnerabilities and they’re not on your network. If you’re not IT, please forward the story to them.
- U.S. and Australian security agencies release list of 2021’s ‘top’ malware strains: The most commonly seen malware strains in 2021 include Agent Tesla, Qakbot, TrickBot, GootLoader and several others, according to a new list released by the Cybersecurity and Infrastructure Security Agency (CISA) and the Australian Cyber Security Centre (ACSC). The Record, August 4, 2022


