A weekly aggregation of important cybersecurity and privacy news.
Table of Contents
- Stan’s Top-3: My pick of the 3 most important stories of the week.
- The Front Page: Other front page cybersecurity and privacy stories.
- Section 2 – Personal Security and Privacy: Important stories for protecting yourself and your family. Includes Cyber Humor because laughter is the best medicine.
- Section 3 – General Cyber Security and Privacy: Cybersecurity and privacy stories for those wanting a deeper look.
- Section 4 – Securing the Organization: Stories to support executives and top management in securing their organizations.
Stan’s Top-3
Our Lead Story: Brian Krebs excellent analysis of how tougher sanctions on Russia will likely trigger a Russian retaliation against America and its allies, which could escalate into cyber attacks on Western financial institutions and energy infrastructure. Russia Sanctions May Spark Escalating Cyber Conflict, KrebsOnSecurity, February 25, 2022
CISA Shields Up.The Cybersecurity and Infrastructure Security Agency (CISA) has published important guidance to small and medium-size businesses (along with governments and nonprofits) so they can better protect themselves from cyber attack. This is vital information for anyone tasked with their organization’s cybersecurity. If IT reports to you, make sure IT is doing these things. And if you work in an organization, make sure your executives know to make sure IT is doing these things. Don’t assume. Don’t trust. Verify.
On the privacy side, the IRS has decided to back away completely from requiring users to provide facial scans, even saying any biometric data shared with ID.me would be permanently deleted over the next few weeks. IRS: Selfies Now Optional, Biometric Data to Be Deleted: KrebsOnSecurity, February 22, 2022
The Front Page
Ukraine Impact – How ready are we for sanctions blow-back?
One of the things I’ve learned in 40 years of cybersecurity is we are never as secure as we think we are. This is particularly true for mid-size and smaller organizations. We would be wise to be concerned. I can only hope the American Electric Power CEO isn’t being naïve.
US officials tell businesses to watch for potential ransomware attacks after Biden announces Russia sanctions: (CNN)Minutes after President Joe Biden announced new sanctions on Russian banks and elites on Tuesday, a senior FBI cyber official asked US businesses and local governments to be mindful of the potential for ransomware attacks as the crisis between the Kremlin and Ukraine deepens. CNN, February 22, 2022
US banks are worried about the possibility of a massive Russian cyberattack, says cybersecurity CEO: CrowdStrike CEO George Kurtz said that bank executives in the United States are concerned about the possibility of devastating Russian cyberattacks. Insider, February 25, 2022
‘We’re ready’ — American Electric Power CEO says it’s focused on cybersecurity defense for years: American Electric Power CEO Nick Akins told CNBC’s Jim Cramer on Thursday that the utility provider feels confident in its cybersecurity defenses. CNBC February 24, 2022
The Biden administration continues to strengthen our cyber enforcement capabilities.
The US Department of Justice forms new task force to combat criminal use of cryptocurrencies: The US Justice Department this week announced the launch of the National Cryptocurrency Enforcement Team to combat the criminal use of digital assets. … Deputy Attorney General Lisa Monaco made the announcement at the Munich Cyber Security Conference, and appointed veteran prosecutor Eun Young Choi to serve as the inaugural director of the force. Yahoo News, February 18, 2022
The tax man takes on ransomware: Sanctions, indictments and potential cyber counter-attacks aren’t President Joe Biden’s only options for denting the scourge of ransomware attacks plaguing schools, hospitals and government offices. … He also has the Internal Revenue Service. Politico, February 20, 2022
Nonprofit Cyber — A new coalition of cybersecurity nonprofits.
Of special interest to SecureTheVillage is the announcement of Nonprofit Cyber, a coalition of global nonprofit organizations to enhance joint action to improve cybersecurity. SecureTheVillage congratulates the initial 22 members and looks forward to joining the coalition. Cybersecurity Nonprofits Form “Nonprofit Cyber” Coalition:, Cyber Readiness Institute, February 23, 2022
We need knowledgeable cybersecurity leadership not grandstanding politicians.
This story illustrates the magnitude of the political leadership challenge we face in securing our freedoms from cyber attack. You may recall last year Missouri Governor Mike Parson ludicrously vowed to criminally prosecute a journalist for reporting a misconfigured state website that exposed personal information of more than 100,000 teachers. It turns out that Parson’s own Office of Administration has had responsibility for securing the state’s IT systems since before the system was misconfigured in 2011. Missouri Governor’s Office Responsible for Teacher Data Leak: KrebsOnSecurity, February 22, 2022
Section 2 – Personal Security and Privacy
Be careful out there.
Your Android phone could have stalkerware, here’s how to remove it: A security vulnerability in one of the biggest consumer-grade spyware operations today is putting at risk the private phone data of about 400,000 people, a number that’s growing daily. The operation, identified by TechCrunch, is run by a small crew of developers in Vietnam but has yet to fix the security issue. Yahoo!finance, February 22, 2022
FBI warning: Watch out for email fraudsters using fake video meetings to steal your money: Business email compromise (BEC), a multi-billion dollar subset of phishing threats, might need a new name because the scams are no longer just about email. The FBI warns that scammers have ramped up video meetings as a tool to trick unsuspecting victims into handing over their money. ZD Net, February 21, 2022
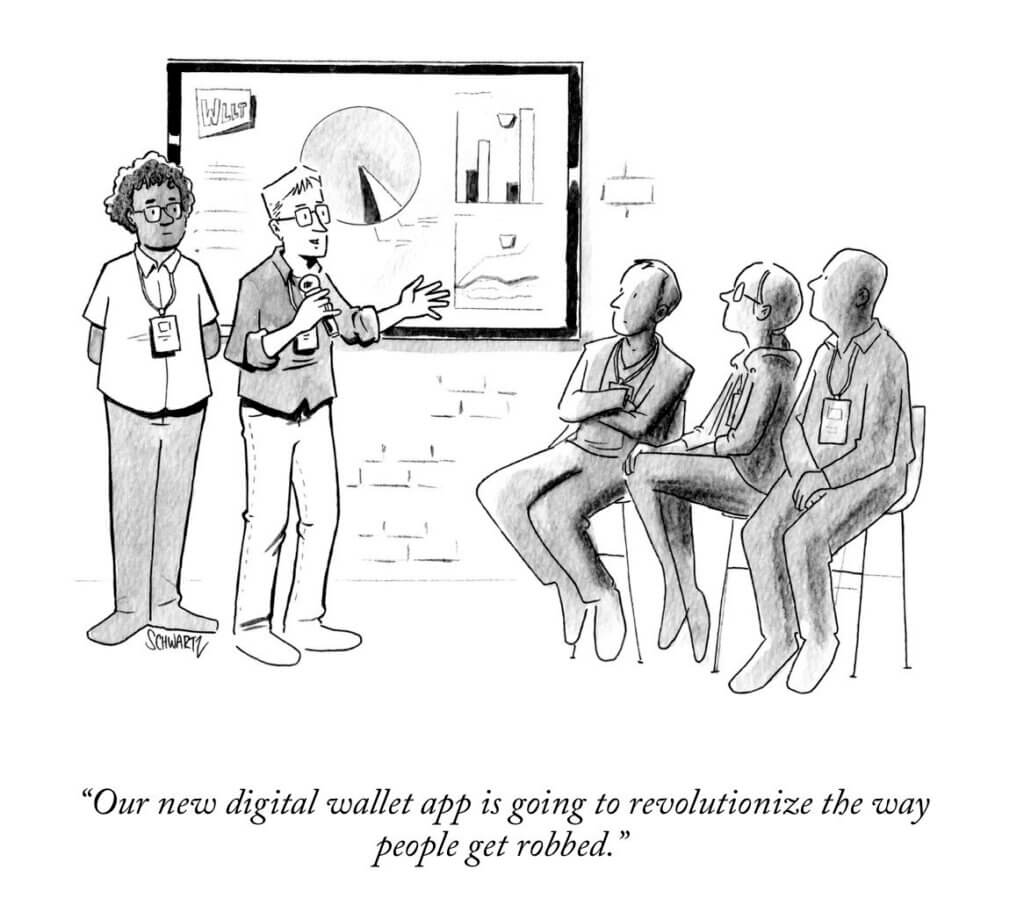
Cyber Humor
Section 3 – General Cyber Security and Privacy Stories
A deeper dive on the cyber war in Ukraine.
IBM Security X-Force Research Advisory: New Destructive Malware Used In Cyber Attacks on Ukraine: On February 23, 2022, open-source intelligence sources began reporting detections of a wiper malware — a destructive family of malware designed to permanently destroy data from the target — executing on systems belonging to Ukrainian organizations. Security Intelligence, February 25, 2022
Russia or Ukraine: Hacking groups take sides: Russia’s invasion of Ukraine has taken place both on and offline, blending physical devastation with escalating digital warfare. Ransomware gangs and other hacking groups have taken to social media to announce where their allegiances lie. … The Record will be tracking who these groups align with, as well as any attacks they launch related to the conflict. The Record, February 25, 2022
Cyber Crime.
Chipmaker Nvidia investigates potential cyberattack: Feb 25 (Reuters) – U.S chipmaker Nvidia Corp (NVDA.O) said on Friday it was investigating a potential cyberattack, following a news report that said the attack may have had taken parts of its business offline for two days. Reuters, February 25, 2022
Know the enemy.
Network hackers focus on selling high-value targets in the U.S.: A Crowdstrike report looking into access brokers’ advertisements since 2019 has identified a preference in academic, government, and technology entities based in the United States. … Initial access brokers are a vital link in the cybercrime chain, as these threat actors are devoted to breaching corporate networks for future attacks. … These brokers then sell access to these networks to other cybercriminals who will do the “dirty” and more risky work of deploying malware, ransomware, move laterally, conduct espionage, etc. Bleeping Computer, February 23, 2022
North Korean Hackers Launder Crypto Using Sophisticated Techniques: Report: According to a recent analysis, the Pyongyang-led cybercrime organization – the Lazarus Group – employs advanced techniques to steal and launder cryptocurrencies. The gang has shown “remarkable adaptation to evolving regulation,” the report warned. CryptoPotato, February 20, 2022
How new privacy rules are impacting the commercial use of personal data.
The New Rules of Data Privacy: The data harvested from our personal devices, along with our trail of electronic transactions and data from other sources, now provides the foundation for some of the world’s largest companies. Personal data also the wellspring for millions of small businesses and countless startups, which turn it into customer insights, market predictions, and personalized digital services. For the past two decades, the commercial use of personal data has grown in wild-west fashion. But now, because of consumer mistrust, government action, and competition for customers, those days are quickly coming to an end. Harvard Business Review, February 25, 2022
Quantum security achieves secrecy holy grail.
Cryptographers Achieve Perfect Secrecy With Imperfect Devices: For the first time, experiments demonstrate the possibility of sharing secrets with perfect privacy — even when the devices used to share them cannot be trusted. Quanta Magazine, February 25, 2022
Section 4 – Securing the Organization
Government ramps up cybersecurity support to organizations.
NIST Video Series: Protecting Your Small Business: To help small businesses develop cybersecurity awareness and training programs, NIST recently produced videos and related resources on three of the highest-interest cybersecurity topics: Ransomware, Phishing, and Multi-Factor Authentication. … These short, animated videos are posted online at the NIST Small Business Cybersecurity Corner, where each topic is given a resource page that can be shared as a standalone article.
CISA Free Cybersecurity Services and Tools: As part of its continuing mission to reduce cybersecurity risk, CISA has compiled a list of free cybersecurity tools and services to help organizations further advance their security capabilities. This living repository includes cybersecurity services provided by CISA, widely used open source tools, and free tools and services offered by private and public sector organizations across the cybersecurity community. CISA, February 2022
CISA Insights: Preparing for and Mitigating Foreign Influence Operations Targeting Critical Infrastructure: CISA has released CISA Insights which provides proactive steps organizations can take to assess and mitigate risks from information manipulation. Malicious actors may use tactics—such as misinformation, disinformation, and malinformation—to shape public opinion, undermine trust, and amplify division, which can lead to impacts to critical functions and services across multiple sectors. CISA, February 18, 2022
CISA Adds Four Known Exploited Vulnerabilities to Catalog: CISA has added four new vulnerabilities to its Known Exploited Vulnerabilities Catalog, based on evidence that threat actors are actively exploiting the vulnerabilities listed in the table below. These types of vulnerabilities are a frequent attack vector for malicious cyber actors of all types and pose significant risk to the federal enterprise. CISA, February 25, 2022
Shields Up Technical Guidance: CISA has created a new Shields Up Technical Guidance webpage that details malicious cyber activity affecting Ukraine. The webpage includes technical resources from public and private sector partners to assist organizations against these threats. CISA, February 2022
Another story that ransomware now includes extortion.
Backups ‘no longer effective’ for stopping ransomware attacks: Traditional methods of mitigating ransomware are less efficacious thanks to the rise in double and triple extortion techniques. Computer Weekly, February 23, 2022
Cyber talent in crisis.
Cybersecurity burnout is real. And it’s going to be a problem for all of us: Burnout might be the most critical cybersecurity risk facing organizations in 2022. So, how do we tackle it? … With the number of data breaches in 2021 soaring past that of 2020, there is even more pressure on security teams to keep businesses secure in 2022. But at a time when strength and resilience have never been more important, burnout, low staff morale and high employee turnover could put businesses on the backfoot when attempting to manage the mounting cybersecurity threat. ZD Net, February 25, 2022


