This week’s essential cybersecurity and privacy news for the cyber-aware and the cyber-concerned. Designed to educate, support, and advocate.
Stan’s Top of the News
This week’s Top of the News is an in-depth cybercrime analysis by The Wall Street Journal.
- Hackers Extort Less Money, Are Laid Off as New Tactics Thwart More Ransomware Attacks: Cybercriminals face drop in payments, as U.S. companies are better at bouncing back from attacks. … Law-enforcement officials including Attorney General Merrick Garland, speaking, and Deputy Attorney General Lisa Monaco have been dedicating resources to thwarting cyberattacks. … “It reflects, I think, the pivot that we have made to a posture where we’re on our front foot,” Deputy Attorney General Lisa Monaco said in an interview. “We’re focusing on making sure we’re doing everything to prevent the attacks in the first place.” … Ms. Monaco and other law-enforcement officials have pushed over the past two years to rely less on solely charging foreign hackers, who may never see a courtroom. Instead, they dedicate resources to thwarting cyberattacks before they can do more damage, an approach they have likened to efforts to combat terrorism following the Sept. 11, 2001, attacks. … “We needed to change our orientation…to one where we are putting prevention first, disruption first, and putting victims at the center of our approach,” Ms. Monaco said, speaking Friday at the Munich Cyber Security Conference. “That means we are trying to break the business model of ransomware actors. … Companies have also stepped up their cybersecurity practices, driven by demands from insurance underwriters and a better understanding of the risks of ransomware following high-profile attacks. Companies are spending more money on business continuity and backup software that allow computer systems to restart after they have been infected. … With improved backups, U.S. companies are better at bouncing back from ransomware attacks than they were four years ago, according to Coveware Inc., which helps victims respond to ransomware intrusions and has handled thousands of cases. … Four years ago, 85% of ransomware victims wound up paying their attackers. Today that number is 37%, according to Coveware Inc. Chief Executive Bill Siegel. As more victims resist paying, hackers have looked for more lucrative targets. The average ransomware payout in the final quarter of 2022 was just over $400,000—up from around $300,000 during the last quarter of 2021, Mr. Siegel said. … “For financially motivated cybercriminals, they will go where the opportunities are profitable,” he said. … Experts said that in some cases financially motivated hackers are migrating away from ransomware toward other methods of attacks, such as scams to obtain payment-card data. … “Just because traditional ransomware has slowed down doesn’t mean threat actors have,” said Adam Meyers, senior vice president of intelligence at CrowdStrike. The Wall Street Journal, February 22, 2023
How Hackable Are You? Take our test. Find out how hackable you are and download our free 8-step guide.
- How Hackable Are You? Think your defenses are strong. Find out as SecureTheVillage tests you on five basics. Please take our short quiz as your answers will help you and guide us to improve community safety.
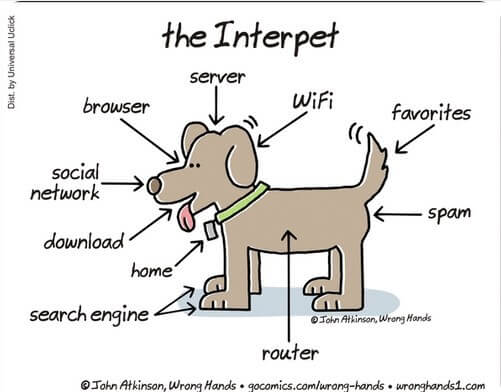
Cyber Humor
Cybersecurity Nonprofit of the Week … Nonprofit Cyber
Kudos to Nonprofit Cyber, the coalition of nonprofit organizations that focus on raising the bar in cybersecurity, as it celebrates its first anniversary. In a year, Nonprofit Cyber has grown to thirty-seven members strong, with six new organizations joining: BBB Institute for Marketplace Trust, Black Girls Hack, Building Cyber Security, Internet Safety Lab, the Global Anti Scam Alliance, and the Maritime Safety and Security Alliance. SecureTheVillage is a proud member of Nonprofit Cyber.
Live on Cyber with Dr. Stan Stahl – Live on LinkedIn and Your Favorite Podcast Platform

Live on Cyber with Dr. Stan Stahl: (Video) (Podcast): Describing cybersecurity can look a lot like the story of the blind men and the elephant. One grabs the trunk and says “This is a snake.” Another reaches to the elephant’s ear and says it’s a fan. One feels the tusk and says it’s a spear. And so on, each believing that they – and only they – know the elephant. … To many, cybersecurity is IT managing the network. To others, it’s complying with laws and legal obligations. Others see it as a risk management matter to be managed with insurance. Others see it as an operational risk-reduction challenge. Yet to others, cybersecurity is a workforce challenge or the challenge of protecting seniors from romance and other scams. Truth be told, cybersecurity is all of these things along with matters of war and peace … as the cyberwar playing out in Ukraine demonstrates. … Join Stan and Julie as they riff on the opportunities to improve our collective cybersecurity – get our arms around the whole cyber-elephant so to speak – by breaking down the silos, listening to each other, and co-creating opportunities to collaborate … to make 1 + 1 = 1,000 as we say at SecureTheVillage. … As always, Stan and Julie provide actionable tips and thoughtful wisdom in a fun conversation on the complexities of cybersecurity and privacy. For a 90-second introduction to the Cyber-Elephant please watch our SecureTheVillage video.
Section 2 – Let’s Be Careful Out There. And Let’s Help Others Who Aren’t Yet Cyber-Aware.
An in-depth story of victims who lost everything when their iPhones were stolen. The story reminds me of Jessica Roy’s series in the Los Angeles Times that we posted in the November 20 News when she described her own experiences as a victim of identity theft after her wallet was stolen.
- A Basic iPhone Feature Helps Criminals Steal Your Entire Digital Life: The passcode that unlocks your phone can give thieves access to your money and data; ‘it’s like a treasure box’. … In the early hours of Thanksgiving weekend, Reyhan Ayas was leaving a bar in Midtown Manhattan when a man she had just met snatched her iPhone 13 Pro Max. … Within a few minutes, the 31-year-old, a senior economist at a workforce intelligence startup, could no longer get into her Apple account and all the stuff attached to it, including photos, contacts and notes. Over the next 24 hours, she said, about $10,000 vanished from her bank account. … Similar stories are piling up in police stations around the country. Using a remarkably low-tech trick, thieves watch iPhone owners tap their passcodes, then steal their targets’ phones—and their digital lives. The Wall Street Journal, February 24, 2023
- How to Protect Your iPhone Data From Thieves: Strengthen your passcode and use Screen Time controls to keep a predator you meet in real life from hijacking your digital life. … Our phones are a portal to everything that’s important to us—our most sensitive communications, our life savings, our photos. You’d think all that would be protected by something more complex than a four- or six-digit passcode. … “The most important thing is awareness,” says Sgt. Robert Illetschko, lead investigator on iPhone theft cases in Minneapolis. “People forget that what they’re holding in their hand is their entire life.” He adds, “If someone has access to it, they can do a lot of damage.”
Beware. The mouse may not be the Mouse.
- Beware Fake Disney Plus Emails That Steal Your Bank Information: Scammers are using fake Disney Plus emails to access users’ personal data — especially their banking information. According to our colleagues at The Money Edit, scammers send emails that tell victims they need to act immediately to prevent their accounts from being disabled. It’s a close cousin of the banking scams, where seemingly-official email messages impersonate Bank of America and others which can easily lead to empty customer bank accounts. … Learn some of the things to watch out for, to avoid becoming the next Disney Plus scam victim. Kiplinger, February 18, 2023
Another story of misleading apps. Why am I not surprised? And neither should you be.
- Most popular apps mislead consumers about the data they collect, study claims: When was the last time you looked at what personal information and approvals you give the apps that you use on a regular basis? If free apps like Twitter, Facebook, Facebook Lite, and Snapchat – or paid apps like Minecraft or Grand Theft Auto: San Andreas – are in your app collection, you may want to take a second look. … Why? Because in those apps’ privacy policies, you might find that you’ve given them the okay to share user information with advertisers, internet service providers, platforms, and numerous other types of companies. In short, it may be your information, but it could easily find its way elsewhere. … In a new study – “See No Evil: How Loopholes in the Google Play Store’s Data Safety Labels Leave Companies in the Clear and Consumers in the Dark,” – Mozilla Foundation researchers pulled off their blinders to look at whether Google Play Store’s new data safety labels provide consumers with accurate information about apps that collect, use, and share personal data. … In an astonishing 80% of the apps reviewed, Mozilla found that what those app companies self-reported on Google’s Data Safety Form and what their policies actually say are two different things.
Here’s a great guide for home users from the NSA. It goes far deeper than the 8 basic things SecureTheVillage covers in our How Hackable Are You? Guide; but it also fails to alert people to freeze their credit.
- NSA Releases Best Practices For Securing Your Home Network: The National Security Agency (NSA) released the “Best Practices for Securing Your Home Network” Cybersecurity Information Sheet (CSI) today to help teleworkers protect their home networks from malicious cyber actors. … “In the age of telework, your home network can be used as an access point for nation-state actors and cybercriminals to steal sensitive information,” said Neal Ziring, NSA Cybersecurity Technical Director. “We can minimize this risk by securing our devices and networks, and through safe online behavior.” … The guide includes recommendations for securing routing devices, implementing wireless network segmentation, ensuring confidentiality during telework, and more. … Spearphishing, malicious ads, email attachments, and untrusted applications can present concerns for home internet users. NSA not only shows teleworkers how to secure their home networks, but also provides tips for staying safe online. National Security Agency, February 22, 2023
Section 3 – Cybersecurity News for the Cyber-Concerned.
Unintended consequences can also happen to our enemies. Russia thought they would own the cyber-battlefield in Ukraine. Instead Ukraine, the EU, the United States and our allies have come together to improve our collective cyber-defenses. Necessity as we see once again is the mother of invention.
- Impact of Ukraine-Russia war: Cybersecurity has improved for all: Money flowing to major ransomware hackers is down while international cooperation is up. … Russia’s cyberspace attacks on Ukraine during the past year have erased data, degraded communication and stolen information, but they have fallen far short of the destruction that many predicted after the invasion a year ago. … In fact, the campaign may have helped inoculate Ukraine against more devastating attacks, experts say, by revealing Russian tactics when the stakes were highest, proving the value of faster collaboration and other defensive measures, and destroying the myth of Russia as an unstoppable cyber superpower. The Washington Post, February 25, 2023
Insider has an excellent in-depth story of election interference by Putin’s Wagner Group.
- How Putin’s Russian goon squad used Mexican gig workers to troll an American election: The Wagner Group is a private company in name only. A trove of leaked documents demonstrate that it is best understood as an arm of the Russian state. … In March 2020, a freelance writer in Mexico City was browsing the internet at home when he saw an ad for a self-described “social media” company that was looking for writers to post messages online. The company didn’t appear to have a name. Instead, there was a WhatsApp number and an address for an account on an encrypted email service. “Fluent English is a must,” the ad emphasized. … The freelancer — I’ll call him Carlos — thought the whole thing seemed sketchy. But he was a recent college graduate navigating the job market during the first weeks of the COVID-19 pandemic. He needed the money. Posting to social media sounded like an easy work-from-home gig, so he applied. Insider, February 18, 2022
TikTok continues under siege as its days appear numbered.
- Momentum builds in Congress to crack down on TikTok: Lawmakers from both parties have increased their scrutiny of the app, with some backing a national ban to counter China as others probe its effects on young people. … There’s no consensus yet, but bipartisan momentum is building for Congress to do something, anything, to crack down on TikTok. NBC News, February 18, 2023
- TikTok banned from EU Commission phones over cybersecurity: The European Union’s executive branch said Thursday that it has temporarily banned TikTok from phones used by employees as a cybersecurity measure, reflecting widening worries from Western officials over the Chinese-owned video sharing app. … TikTok faces intensifying scrutiny from Europe and the U.S. over security and data privacy amid worries that the hugely popular app could be used to promote pro-Beijing views or sweep up users’ information. It comes as China and the West are locked in a wider tug of war over technology ranging from spy balloons to computer chips. … The EU’s action follows similar moves in the U.S., where more than half of the states and Congress have banned TikTok from official government devices. AP News, February 23, 2023
In a clear error illustrating just how complex it can be to securely configure web servers, a DoD server was left exposed on the Internet without a password. It’s an illustration of the need for “Security by Design” that CISA Director Jen Easterly described several weeks ago in a story in Foreign Affairs we covered. Stop Passing the Buck on Cybersecurity:
- Sensitive US military emails spill online: A government cloud email server was connected to the internet without a password. … The U.S. Department of Defense secured an exposed server on Monday that was spilling internal U.S. military emails to the open internet for the past two weeks. … A misconfiguration left the server without a password, allowing anyone on the internet access to the sensitive mailbox data inside using only a web browser, just by knowing its IP address. TechCrunch, February 21, 2023
The NIST Cyber Security Framework has become the de facto US framework for information security management. NIST has announced plans to update the Framework with a draft planned for Summer. NIST has now published a concept paper that is available for review.
- NIST plans biggest ever reform of Cybersecurity Framework: CSF 2.0 blueprint offered up for public review. … The US National Institute of Standards and Technology (NIST) is planning significant changes to its Cybersecurity Framework (CSF) – the first in five years, and the biggest reform yet. … First published in 2014 and updated to version 1.1 in 2018, the CSF provides a set of guidelines and best practices for managing cybersecurity risks. The framework is designed to be flexible and adaptable rather than prescriptive, and is widely used by organizations and government agencies, both within and outside the US, to create cybersecurity programs and measure their maturity. … Following a long consultation, NIST has published a concept paper for CSF 2.0 and opened it up to further review. The resulting feedback will be used to develop a final draft of the revised framework, due out sometime this summer. Port Swigger, February 23, 2023
The National Security Telecommunications Advisory Committee (NSTAC) voted this week to send President Biden recommendations on improved cybersecurity management, including an office to work collaboratively to harmonize cyber regulations. The story brought back memories of my own work in the late 1980s when I served on an NSTAC Working Group making recommendations on protecting sensitive unclassified information.
- Federal panel says agencies need to focus on harmonizing cyber regulations: An advisory committee recommended the creation of an office to deconflict cyber rules … The report now goes to the White House for President Biden’s consideration. … The Biden administration needs to take numerous steps to deconflict and organize the proliferation of cybersecurity regulations, according to a report that a presidential advisory committee approved Tuesday. … That includes things like creating an office within the Cybersecurity and Infrastructure Security Agency to harmonize cybersecurity rules across the federal government, or directing a trio of federal agencies to coordinate with foreign governments to develop consensus cybersecurity standards. … The recommendations arrive as the U.S. cyber scene awaits publication of the Biden administration’s national cybersecurity strategy, the White House pushes for mandates on numerous industries, and CISA writes a rule to require critical infrastructure owners and operators to report major cyber incidents to the agency. … The advisory panel, named the National Security Telecommunications Advisory Committee (NSTAC), voted Tuesday to send the report to Biden for his consideration. The Washington Post, February 22, 2023
In cybercrime this week.
- City of Oakland still struggling from two week old ransomware attack, calls in CA Gov and National Guard: The City of Oakland, California is still struggling from the aftereffects of a two week old ransomware attack that crippled city services. … City officials have now called in IT specialist teams from both the California State National Guard and the California Governor’s Office of Emergency Services (CalOES) to help with recovery efforts. Cybernews, February 24, 2023
- L.A. Unified data breach last year includes at least 2,000 student records, officials say: The Los Angeles Unified School District disclosed Wednesday that “approximately 2,000 student assessment records” were posted on the dark web as a result of a recent cyberattack, including those for 60 who are currently enrolled. … The posted records also included an unspecified number of driver’s license numbers and Social Security numbers. The district statement did not say to whom those numbers belonged, but the school system does not routinely collect Social Security numbers from students. … Separately, the Long Beach school system, one of the state’s largest, notified families Wednesday of a data breach that, so far, appears to contain the email addresses of students and student ID numbers. Los Angeles Times, February 22, 2023
- News Corp says state hackers were on its network for two years: Mass media and publishing giant News Corporation says that attackers – believed to be from China – behind a breach disclosed in 2022 first gained access to its systems two years before, in February 2020. … This was revealed in data breach notification letters sent to employees affected by the data breach, who had some of their personal and health information accessed, while the threat actors had access to an email and document storage system used by several News Corp businesses. … The incident affected multiple news arms of the publishing conglomerate, including The Wall Street Journal, the New York Post, and its U.K. news operations. Bleeping Computer, February 24, 2023
- Cyberattack on food giant Dole temporarily shuts down North America production, company memo says: A cyberattack earlier this month forced produce giant Dole to temporarily shut down production plants in North America and halt food shipments to grocery stores, according to a company memo about the incident obtained by CNN. … The previously unreported hack — which a source familiar with the incident said was ransomware — led some grocery shoppers to complain on Facebook in recent days that store shelves were missing Dole-made salad kits. … “Dole Food Company is in the midst of a Cyber Attack and have subsequently shut down our systems throughout North America,” Emanuel Lazopoulos, senior vice president at Dole’s Fresh Vegetables division, said in a February 10 memo to retailers. CNN, February 22, 2023
Kudos to Britain’s Royal Mail back in operations six weeks after a ransomware attack … while refusing to pay the $80 million ransom demand.
- Royal Mail resumes overseas deliveries via post offices after cyber-attack: Royal Mail has restarted international parcel and letter deliveries through Post Office branches almost six weeks after it revealed it had been affected by a ransomware cyber-attack that left it battling to get its international services back up and running. … It refused to pay an $80m (£67m) ransom sought by hackers linked to Russia after the “cyber incident”, which resulted in 11,500 Post Office branches across the UK being unable to handle international mail or parcels. The Guardian, February 21, 2023
And finally, I offer the following story to illustrate the power of human creativity in the search for easy money.
- Teacher Charged After Crypto Mining Operation Discovered in School Crawl Space: A Massachusetts teacher is facing charges after authorities say he carried out an elaborate cryptocurrency mining operation out of the school where he worked. Nadeam Nahas, 39, was teaching at Cohasset High School when a town facilities inspector visited the school and found an unusual electrical setup in one room. Yahoo, February24, 2023
Section 4 – Managing Information Security and Privacy in Your Organization.
The information security profession continues in crisis.
- 1 in 4 CISOs Wants to Say Sayonara to Security: Thanks to burnout and stress, Gartner predicts churn and even departure from profession among half of today’s security leaders by 2025. … Enterprises can expect to see some pretty dramatic churn in their cybersecurity departments in the next two years if they’re not proactive about countering security burnout. A prediction out today by Gartner estimates that almost half of cybersecurity leaders will change jobs by 2025. More startling, the analyst firm predicts that one in four leaders will exit the security stage completely. … According to Deepti Gopal, director analyst for Gartner, cybersecurity professionals are generally facing “unsustainable levels of stress.” For CISOs and other security managers, the mental and emotional fallout from occupying the scapegoat role is not only spurring many them to look outside of their current jobs or their professions, it’s also impacting their effectiveness when they stay. … “CISOs are on the defense, with the only possible outcomes that they don’t get hacked or they do,” Gopal says. “The psychological impact of this directly affects decision quality and the performance of cybersecurity leaders and their teams.” … For a long time now, the need for cybersecurity expertise has gone unfilled across the entire industry. Per last year’s (ISC)2 estimates, there is a current shortfall of 3.4 million cybersecurity experts. Even as other jobs in the tech industry begin to evaporate in the face of tech sector layoffs, cybersecurity appears to be immune to this. A report earlier this month from (ISC)2 showed that only 10% of corporate executives expect to lay off members of their cybersecurity teams this year. DARK Reading, February 22, 2023


