A weekly aggregation of important cybersecurity and privacy news designed to educate, support, and advocate; helping you meet your data care challenges and responsibilities.
Stan’s Top of the News
As the cost of cybercrime continues to rise and the FBI warns of sophisticated cyberattacks, CISA wants to help ordinary people understand the vital role we all play in prevention. Cybersecurity is not something just for the experts. All of us have a responsibility to care for the data we have in our computers and online.
- Average Data Breach Costs Hit a Record $4.4 Million, Report Says: The average cost of a data breach rose to an all-time high of $4.4 million this year, according to the IBM Security report released Wednesday. That marked a 2.6% increase from a year ago and a 13% jump since 2020. … More than half of the organizations surveyed acknowledged they had passed on those costs to their customers in the form of higher prices for their products and services, IBM said. CNET, July 27, 2022
- The growth in targeted, sophisticated cyberattacks troubles top FBI cyber official: The FBI is deeply worried that cybercriminals and nation-state adversaries are developing more precision in their attacks and taking advantage of innovations in artificial intelligence that will compound the digital threat in the years to come, FBI Assistant Director for Cyber Bryan Vorndran said Wednesday. CyberScoop, July 20, 2022
- Jen Easterly wants to cut the nerdspeak: To the average person, cybersecurity can be a subject overflowing with technologically dense, often impenetrable terms and concepts. … The head of the federal government’s cyber agency, Jen Easterly, says that in her one-year tenure she has spent the most time establishing her organization as one that people want to come work at, and she also wants to convince everyone else to take better care of their own computers and phones — which means cutting out the “nerdspeak.” The Washington Post, July 26, 2022
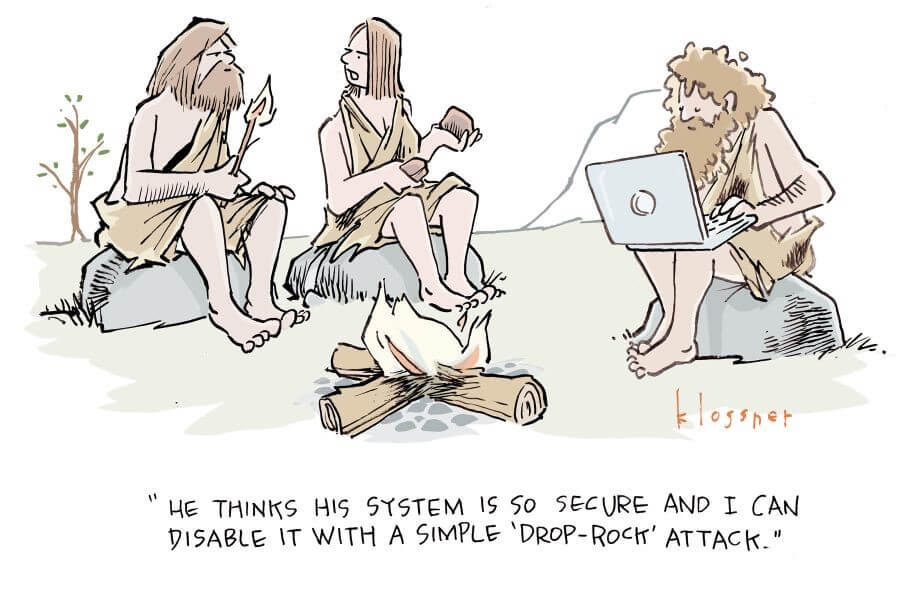
Cyber Humor
Security Nonprofit of the Week
Kudos this week to US Valor, a nonprofit with two intertwined objectives: (1) providing opportunities to U.S. veterans and (2) helping America meet our cybersecurity workforce challenge. US Valor does this through an innovative Department of Labor approved Apprenticeship Program. The US Valor Cybersecurity Apprenticeship Program (CAP) is all about helping transitioning military personnel and U.S. Veterans experience a smooth transition from military life to the civilian world through its Department of Labor Registered Apprenticeship Program (RAP). I’m a proud member of US Valor’s Advisory Board.
Live on Cyber with Dr. Stan Stahl – Live on LinkedIn

Live on Cyber with Dr. Stan Stahl: Join Julie Morris and me as we discuss data care in the context of Benjamin Franklin’s quote: Distrust and caution are the parents of security.” Distrust and caution … when we open an email … when we get a text asking for a donation … when we connect to wi-fi at Starbucks or a hotel … when we wire funds. #NeverTrust.AlwaysVerify.
Section 2 – Personal Data Care – Security and Privacy
Important data care stories for protecting yourself and your family.
As if to illustrate the responsibility we all have to protect our data, we have several stories this week about locking down the data in our computers and online lives. Data care means correctly configuring Facebook, Apple, Google, and LinkedIn. It means understanding what private browsing is – and what it is not. It means keeping malicious programs off our devices. And it means protecting our passwords and other ‘keys to the kingdom.’ Just as health care puts basic responsibility for my health on me, data care puts basic responsibility for protecting data on users.
- The Default Tech Settings You Should Turn Off Right Away: These controls, which are buried inside products from Apple, Google, Meta and others, make us share more data than we need to. … There’s a catchy saying going around with a valuable lesson about our personal technology: The devil is in the defaults. … The saying refers to the default settings that tech companies embed deep in the devices, apps and websites we use. These settings typically make us share data about our activities and location. We can usually opt out of this data collection, but the companies make the menus and buttons hard to notice, likely in the hope that we don’t immediately tweak them. The New York Times, July 29, 2022
- You should change these LinkedIn privacy settings now: The professional network can be an over-sharer. Here’s how to limit the personal information it exposes. … You might not think of LinkedIn as a privacy risk, especially compared to the social networks that make lots of headlines for being naughty. LinkedIn, owned by Microsoft, is where you share your resume with the world — information many members want to be visible, especially if they’re hunting for a job. … But using LinkedIn comes with some exposure that may not be so obvious. For one: salespeople, crooks or stalkers could try to use the details you reveal on LinkedIn to target you with aggressive pitches, trick you into targeted phishing attacks or otherwise gain your confidence. You could also inadvertently leave breadcrumbs that suggest to your current employer that you’re on the hunt for a new job. The Washington Post, July 26, 2022
- What a digital law expert wants you to know about post-Roe data privacy: Following the U.S. Supreme Court’s decision to abolish federal abortion rights by overturning Roe v. Wade, experts have raised concerns about the type of personal data that’s collected within certain reproductive health apps, such as trackers of menstrual cycles or fertility. The fear is that this type of information could be used against someone seeking an abortion in a state that has made it illegal, or has severe restrictions in place. … “The world has changed in many ways since Roe [v. Wade]. But one of the ways that it’s changed is we have a digital surveillance infrastructure now that did not exist before,” Corynne McSherry, legal director for the Electronic Frontier Foundation, a nonprofit defending digital privacy, told Yahoo News. Yahoo!news, July 27, 2022
- Incognito Mode Isn’t As Incognito As You Might Think: You’ve seen the prompt: If you’re using a shared or public computer, use incognito mode. It gives you a sense of security knowing that whatever sites you visit or passwords you type won’t be saved to the device—like skulking around in an invisibility cloak. But of course, nothing you do online is invisible. Private browsing (aka incognito mode) is a great way to prevent your web browser from saving what you do. But to call it privacy-focused is a stretch, and while your browser or device doesn’t log your movements in its history and cookies, that doesn’t mean the sites you visit don’t clock your behavior. Despite its name, you’re not really incognito, and you may want to dial back your confidence in what these modes really do. Wirecutter, July 21, 2022
- Malware hits millions of Android users — delete these apps right now: Malware and adware continue to be a major problem on the Play Store. … Another batch of malicious apps filled with adware and malware has managed to slip past Google’s defenses and end up on the Play Store. … In order to trick unsuspecting users into downloading them, these 36 malicious apps pose as image-editing tools, virtual keyboards, system optimizers, wallpaper changers and other useful tools. Tom’s Guide, July 29, 2022
- What to Do if Your Password Is Exposed in a Data Breach: Don’t panic: We’ll tell you how to minimize the damage. … These days, if your passwords and login credentials have appeared in a public data breach, you’re most likely going to know about it: Apple, Google, password managers, web browsers and more will all warn you if the details that they’re storing have been spotted in a breach. The next question is: what should you do about it? Gizmodo, July, 27, 2022
Section 3 – A Deeper Look for the Cyber-Concerned Citizen
Data Care, cybersecurity and privacy stories to keep you informed.
National security is again in the cyber news. Stories this week focus on Iran and China.
- US bolsters cyber alliance to counter rising Iran threat: President Biden vowed to expand cyber cooperation with Israel and Saudi Arabia on his trip to the Middle East last week, a move experts see as a direct response to the rising digital threat from Iran. … The U.S. and Saudi Arabia signed bilateral agreements to strengthen their cybersecurity partnership and share information related to cyber threats and malicious actors, while Israel and the U.S. pledged to ramp up collaboration to combat cyber crime. The Hill, July 24, 2022
- China Targeted Fed to Build Informant Network and Access Data, Probe Finds: The investigation by Senate Republicans found that the decade long effort included detaining a Fed economist in China. … China tried to build a network of informants inside the Federal Reserve system, at one point threatening to imprison a Fed economist during a trip to Shanghai unless he agreed to provide nonpublic economic data, a congressional investigation found. … The investigation by Republican staff members of the Senate’s Committee on Homeland Security and Governmental Affairs found that Fed employees were offered contracts with Chinese talent-recruitment programs, which often include cash payments, and asked to provide information on the U.S. economy, interest-rate changes and policies, according to a report of the findings released Tuesday. The Wall Street Journal, July 26, 2022
- Leaked Audio From 80 Internal TikTok Meetings Shows That US User Data Has Been Repeatedly Accessed From China: “I feel like with these tools, there’s some backdoor to access user data in almost all of them,” said an external auditor hired to help TikTok close off Chinese access to sensitive information, like Americans’ birthdays and phone numbers. … For years, TikTok has responded to data privacy concerns by promising that information gathered about users in the United States is stored in the United States, rather than China, where ByteDance, the video platform’s parent company, is located. But according to leaked audio from more than 80 internal TikTok meetings, China-based employees of ByteDance have repeatedly accessed nonpublic data about US TikTok users — exactly the type of behavior that inspired former president Donald Trump to threaten to ban the app in the United States. Buzzfeed News, June 17, 2022
This week’s cybercrime victims include a small town in Ontario that has been hit with ransomware.
- A small Canadian town is being extorted by a global ransomware gang: Internal IT systems are locked, but staff say essential services like transit and water treatment are operational. … The Canadian town of St. Marys, Ontario, has been hit by a ransomware attack that has locked staff out of internal systems and encrypted data. … The small town of around 7,500 residents seems to be the latest target of the notorious LockBit ransomware group. On July 22nd, a post on LockBit’s dark web site listed townofstmarys.com as a victim of the ransomware and previewed files that had been stolen and encrypted. The Verge, July 22, 2022
- U.S. Justice Department probing cyber breach of federal court records system: The U.S. Justice Department is investigating a cyber breach involving the federal court records management system, the department’s top national security attorney told lawmakers on Thursday. … Matt Olsen, head of the Justice Department’s National Security Division, alluded to the threat of cyber attacks by foreign nations as he told the U.S. House of Representative Judiciary Committee that the incident was a “significant concern.” Reuters, July 29, 2022
- Attackers stole $6 million from Audius by exploiting a bug in the contract: Blockchain data of the attacker’s wallet shows that the stolen funds were exchanged for 704.17 Ether, worth around $1.09 million, on Uniswap. … Decentralized music streaming platform Audius was exploited on July 23 when an attacker exploited a vulnerability in its governance smart contract code. According to Audius’ analysis of the hack, the attacker stole over 18.5 million AUDIO tokens, the platform’s native cryptocurrency, worth around $6.05 million at the time. Cryptoslate, July 26, 2022
More evidence of the value of multi-factor authentication (2FA/MFA) in blocking cyber attacks. If you’re not using 2FA on your critical accounts, you should implement it immediately.
- These ransomware hackers gave up when they hit multi-factor authentication: More evidence that multi-factor authentication works. Police explain how they have seen ransomware gangs abandon attacks when they hit MFA security. … A ransomware attack was prevented just because the intended victim was using multi-factor authentication (MFA) and the attackers decided it wasn’t worth the effort to attempt to bypass it. … It’s often said that using MFA, also known as two-factor authentication (2FA), is one of the best things you can do to help protect your accounts and computer networks from cyberattacks because it creates an effective barrier – and now Europol has seen this in action while investigating ransomware gangs. ZD Net, July 27, 2022
As the next stories illustrate, the government continues to take action to protect us against cybercrime and fraud.
- A Rogues’ Gallery of Robocallers: The FTC and the FCC regularly bring actions against robocallers and Do Not Call violators in civil court, often with help from state authorities. Consumer Reports highlights some catches by the agencies. Consumer Reports, July 25, 2022
- Uber admits covering up 2016 hacking, avoids prosecution in U.S. settlement: Uber Technologies Inc (UBER.N) on Friday accepted responsibility for covering up a 2016 data breach that affected 57 million passengers and drivers, as part of a settlement with U.S. prosecutors to avoid criminal charges. Reuters, July 22, 2022
Section 4 – Information Security and Privacy Management in the Organization
Stories to support executives and top management in securing their organizations and protecting privacy.
Insanity is often defined as doing the same thing over and over while expecting different results. When it comes to cybercrime, it’s déjà vu all over again.
- Data Vu: Why Breaches Involve the Same Stories Again and Again: Data breaches involve the same old mistakes; we must break the cycle. … In the classic comedy Groundhog Day, protagonist Phil, played by Bill Murray, asks “What would you do if you were stuck in one place and every day was exactly the same, and nothing that you did mattered?” In this movie, Phil is stuck reliving the same day over and over, where the events repeat in a continual loop, and nothing he does can stop them. Phil’s predicament sounds a lot like our cruel cycle with data breaches. … Every year, organizations suffer more data spills and attacks, with personal information being exposed and abused at alarming rates. While Phil eventually figured out how to break the loop, we’re still stuck: the same types of data breaches keep occurring with the same plot elements virtually unchanged. Scientific American, July 26, 2022
If you’re a ransomware victim, No More Ransom may be able to help.
- Ransomware: 1.5 million people have got their files back without paying the gangs. Here’s how: No More Ransom project now offers free tools for decrypting 165 families of ransomware as the fight against extortion groups continues. … The battle against ransomware is challenging because not only are ransomware attacks extremely disruptive, but in many cases, victims opt to pay the ransom demand for a decryption key – fueling additional ransomware attacks because criminals know they can make easy money. … However, one scheme continues to take the fight to ransomware gangs and has now helped over 1.5 million victims successfully decrypt their machines without giving into ransom demands, preventing an estimated $1.5 billion from ending up in the hands of cyber criminals. ZD Net, July 26, 2022
And, if you’re hiring, watch out for deepfakes.
- FBI issues warning about ‘deepfakes’ being used to secure jobs: The Federal Bureau of Investigation is now issuing a warning about the dark side of deepfake videos, telling job recruiters to watch out for fake applicants as people are reportedly using those false videos to apply for remote work. TND, July 28, 2022


