SecureTheVillage Calendar
Leadership Council Meeting, July 8: Special Guest Dr. Vinton Cerf, Father of the Internet. July 8 @ 12:00 pm – 1:30 pm PDT
TownHallWebinar: Personal Cyber Security with Dr. Steve Krantz. July 21 @ 1:00 pm – 2:30 pm PDT Calabasas Senior Center Calabasas, CA
STVHappyHour – July 2020. July 23 @ 4:30 pm – 5:30 pm PDT
TownHallWebinar: NIST Cyberprivacy Frameworks. August 13 @ 10:00 am – 11:00 am PDT
Financial Services Cybersecurity Roundtable – August 2020. August 21 @ 8:00 am – 10:00 am PDT
TownHallWebinar: The Great Reboot: Succeeding in a World of Catastrophic Risk and Opportunity with Bob Zukis & Others. September 10 @ 10:00 am – 11:00 am PDT
Individuals at Risk
Cyber Privacy
Sixteen Facebook apps caught secretly sharing data with third-parties: Academic study used unique “honeytoken” emails to install Facebook apps and see which inboxes received emails from unrecognized senders. ZDNet, July 2, 2020
Cyber Defense
Brave New World: Nine Steps to Greater Cybersecurity That You’ve Been Putting Off: As streets worldwide are filling up with people, though, in face masks and disposable gloves, the suggestion that we’re entering our new reality is increasingly being heard. This new reality will possibly change our approach toward many things that we deemed normal like trips to other countries or even such minor events as commuting to work. But has this COVID-19 turbulence taught us anything? First of all, it has taught us to be cautious — in our movements and face-to-face contacts. But what about cyberspace, which recently came under great pressure, with people transferring not only their work but also daily habits into online? CPO, July 1, 2020
Cyber Danger
Pirated Security Apps Are Being Used To Spread New Mac Ransomware: A new strain of malware targeting Mac users has been spotted. The malware, called ThiefQuest, is being delivered pushed to would-be victims as part of an infected torrent download. Forbes, July 2, 2020
Phishing links hidden inside calendar invite attachments: Cybercriminals have found a new way to reach users’ inboxes. TechRadarPro, July 1, 2020
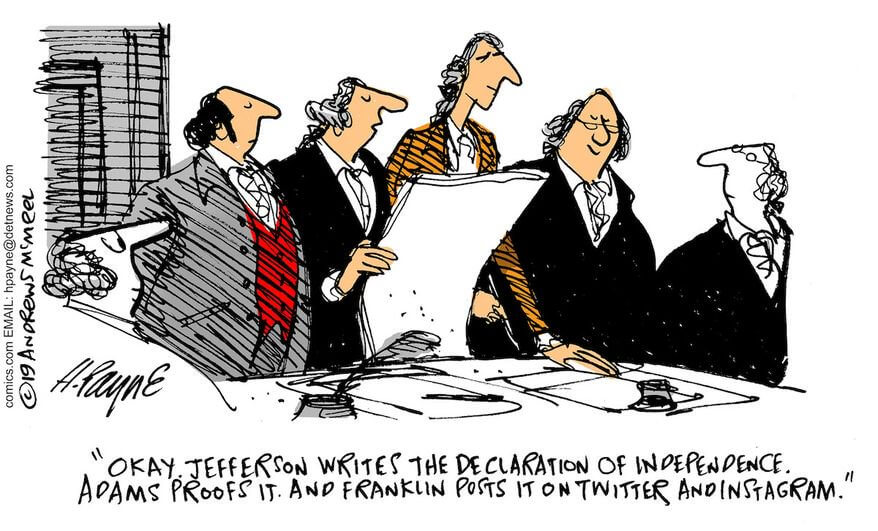
Cyber Humor
Information Security Management for the Organization
Information Security Management
Be prepared: Why you need an incident response policy … Smart security teams have updated incident response plans in place before a security breach happens: Companies that don’t take the time to develop a security incident response plan pay a high price when the inevitable breach happens. TechRepublic, July 2, 2020
Cyber Defense
NSA releases guidance on securing IPsec Virtual Private Networks: The US National Security Agency (NSA) has published guidance on how to properly secure IP Security (IPsec) Virtual Private Networks (VPNs) against potential attacks. BleepingComputer, July 2, 2020
Why Zero-Click Cyberthreats Should Be on Your Radar: For years, the statistics have told us that human error is the greatest contributor to cyberattacks. We’ve stressed the importance of training, training and more training to prevent the almost inevitable from happening. We’ve been convinced that the key to defending against cyberthreats is to keep the unsuspecting from clicking on phishing emails and infecting devices and systems with malware. SecurityIntelligence, July 2, 2020
Secure The Human
Remote Workers Becoming More Security Conscious Although Bad Habits Persist says TrendMicro: Remote workers have become significantly more cybersecurity conscious since the COVID-19 lockdown began, according to a new study from Trend Micro. It found that nearly three-quarters (72%) of remote workers are more aware of their organization’s cybersecurity policies, and 85% now take instructions from their IT team seriously. InfoSecurity, July 1, 2020
Cyber Talent
Security leadership: Women on the frontline … Meet 13 female executives who are succeeding in security leadership roles: Editor’s note: First, we believe it’s important that all public servants should be commended and recognized for their contributions, particularly during the COVID-19 pandemic. So many enterprise security professionals are on the frontlines, in harm’s way without much recognition, and some are risking their lives to provide help, services and expertise. Thank you to all security leaders and first responders! SecurityMagazine, July 1, 2020
Cybersecurity in Society
Cyber Privacy
Europeans Talk the Talk, but Do They Walk the Walk on Data Protection? – CPO Magazine … Results of 35,000 survey by European Agency for Fundamental Rights, FRA: It is an accepted truth that Europeans care more about their privacy than most. We take it for granted that because the European Union has created the General Data Protection Regulation (GDPR) – an admittedly world-leading piece of privacy legislation – that citizens in the EU must care more about their data protection rights. CPO, July 2, 2020
Florida becomes first state to enact DNA privacy law, blocking insurers from genetic data: Florida on Wednesday became the nation’s first state to enact a DNA privacy law, prohibiting life, disability and long-term care insurance companies from using genetic tests for coverage purposes. WashingtonExaminer, July 2, 2020
Cyber Crime
Ransomware attackers pressure Knoxville by posting city data online: Cybercriminals have published city of Knoxville files online, including employees’ personal information, as part of an ongoing effort to pressure city leaders to pay up in a ransomware attack. Knox News, July 2, 2020
University of California SF pays ransomware hackers $1.14 million to salvage research … The malware infected crucial research stored in the UCSF medical school’s network: The University of California at San Francisco (UCSF) has admitted to paying a partial ransom demand of $1.14 million to recover files locked down by a ransomware infection. ZDNet, June 30, 2020
COVID-19 ‘Breach Bubble’ Waiting to Pop?: The COVID-19 pandemic has made it harder for banks to trace the source of payment card data stolen from smaller, hacked online merchants. On the plus side, months of quarantine have massively decreased demand for account information that thieves buy and use to create physical counterfeit credit cards. But fraud experts say recent developments suggest both trends are about to change — and likely for the worse. KrebsOnSecurity, June 30, 2020
Cyber Attack
State-Sponsored Cyber Attacks Threaten Australian Critical Infrastructure: The discussion around state-sponsored cyber attacks on Australia has once again launched to the fore in the country following comments by the Prime Minister Scott Morrison on June 19. According to the new remarks, Australian institutions of all kinds have fallen victim to cyber attacks from a sophisticated state based cyber-actor over at least the course of the last several months, raising alarm about the vulnerability of the country’s critical infrastructure. CPO, July 2, 2020
WastedLocker Ransomware Targets Dozens of Newspaper Websites Operated by a U.S. Media Company in Phishing Attack: The cybercriminal gang behind the WastedLocker ransomware strain recently targeted dozens of newspaper websites operated by a U.S. media company, according to the security firm Symantec. BankInfoSecurity, July 2, 2020
Cyber Strike By Foreign Force Caused Iran Explosion say Israeli Experts … Iranian officials confirmed damage to building near the Natanz nuclear power plant, saying an “accident” occurred. Israel denies connection: TEL AVIV: A mysterious attack using a “kinetic cyber” weapon has caused extensive damage to one of Iran’s most important nuclear facilities, experts here say. BreakingDefense, July 2, 2020
Cyber Defense
How Have I Been Pwned became the keeper of the internet’s biggest data breaches: When Troy Hunt launched Have I Been Pwned in late 2013, he wanted it to answer a simple question: Have you fallen victim to a data breach? TechCrunch, July 3, 2020
Cyber Danger
Anatomy of a Long-Con Phish … A fraudster on LinkedIn used my online profile in an apparent attempt to pull off a wide-ranging scam business venture: Phishing is one of the oldest fraud techniques online. Phishers often utilize a spray-and-pray method to hit as many potential victims as possible. The aim of such an attack is quick profit via the harvesting of user login or banking credentials. Once the victim surrenders his/her valuable information, the phisher moves on, either to the next victim or a different campaign altogether. DarkReading, July 2, 2020
Cyber Law
The Cybersecurity 202: Get ready for encryption fireworks in Congress today: Encryption advocates and tech firms are sounding alarms about a bill seeking to combat child pornography set to be debated by the Senate Judiciary Committee this morning. The Washington Post, July 2, 2020
Bombora Sues ZoomInfo For Allegedly Gaining An Unfair Advantage By Breaching CCPA: Can companies use violations of the California Consumer Privacy Act (CCPA) to nail a rival for noncompetitive behavior? Ad Exchanger, June 11, 2020
Cyber Survaillence
Anonymous Hackers Warn TikTok Users — ‘Delete This Chinese Spyware Now’ … TikTok has attracted scrutiny recently for accessing smartphone keyboards. Now Anonymous hackers show just how much data TikTok collects about you: A few weeks ago, we reported that a new version of iOS exposed that TikTok was accessing mobile clipboards every few keystrokes. A TikTok representative said the action was intended as an anti-spam measure, but there are far more effective ways to block spam. DigitalMusicNews, July 2, 2020
Report accuses China of extensive mobile spyware use to track ethnic minority group: A new blog post and research report from the Lookout Threat Intelligence Team has exposed the lengths to which a reputed Chinese government-sponsored APT operation has allegedly gone to track the country’s Uyghur minority population, including the trojanization of mobile apps with surveillanceware. SC Media, July 2, 2020
Cyber Enforcement
Nigerian National Brought to U.S. to Face Charges of Conspiring to Launder Hundreds of Millions of Dollars from Cybercrime Schemes: LOS ANGELES – A Dubai resident who flaunted his extravagant lifestyle on social media has arrived in the United States to face criminal charges alleging he conspired to launder hundreds of millions of dollars from business email compromise (BEC) frauds and other scams, including schemes targeting a U.S. law firm, a foreign bank and an English Premier League soccer club. US Dept. of Justice, July 3, 2020
European Police Hack Encrypted Communication System … Cracking of EncroChat’s Network Leads to Hundreds of Arrests in Organized Crime Crackdown: European police gained access to messages sent via an encrypted cellular network, leading to the arrest of hundreds of alleged organized crime members, according to Europol, the EU law enforcement agency. BankInfoSecurity, July 2, 2020
Russian Cybercrime Boss Burkov Gets 9 Years: A well-connected Russian hacker once described as “an asset of supreme importance” to Moscow was sentenced on Friday to nine years in a U.S. prison after pleading guilty to running a site that sold stolen payment card data, and to administering a highly secretive crime forum that counted among its members some of the most elite Russian cybercrooks. KrebsOnSecurity, June 27, 2020
Cyber Miscellany
Bruce Schneier says we need to embrace inefficiency to save our economy: It took a global pandemic and stay-at-home orders for 1.5 billion people worldwide, but something is finally occurring to us: The future we thought we expected may not be the one we get. Schneier On Securiy, June 30, 2020


