A weekly aggregation of important cybersecurity and privacy news helping you navigate the new world of cybersecurity and privacy.
Stan’s Top-3
The emerging Russian cyber war.
Are We Ready for Putin’s Cyber War? I Asked One of Biden’s Top Cybersecurity Officials.: Anne Neuberger, the deputy national security adviser for cyber and emerging technology, discusses how the battle in cyberspace is shaping up on this episode of “Sway.” New York Times, March 10, 2022
Breaking Russia’s internet backbone: Lumen joins Cogent in cutting off Russia’s main internet connections. … The internet’s governing bodies dismissed Ukraine’s requests to cut Russia off from the internet. But now, two of the main backbone internet providers, Lumen Technologies and Cogent, have severed Russia’s ties to the internet. ZD Net, March 10, 2022
Let’s be careful out there.
Fraud Is Flourishing on Zelle. The Banks Say It’s Not Their Problem: Zelle, the payments platform used by millions of customers, is a popular target of scammers. But banks have been reluctant to make fraud victims whole — despite owning the system. New York Times, March 6, 2022
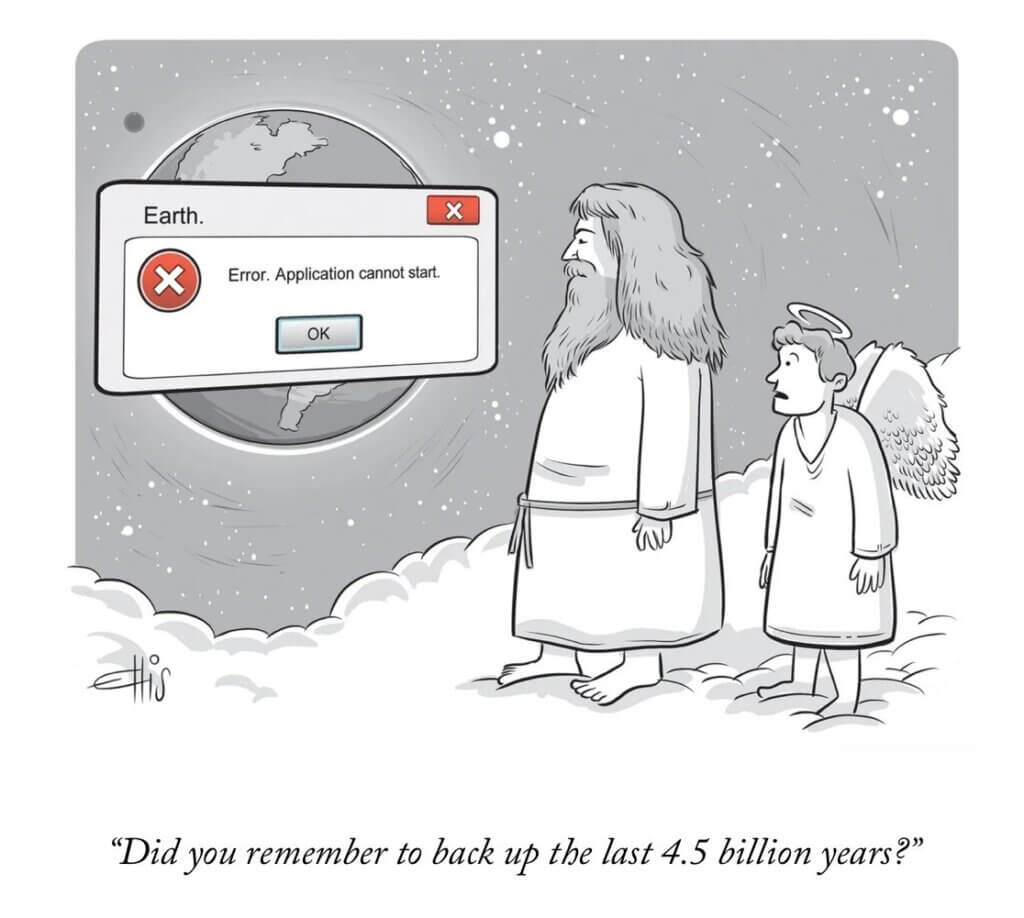
Cyber Humor
The Front Page
Other front page cybersecurity and privacy stories.
The emerging Russian cyber war.
‘Not the time to go poking around’: How former U.S. hackers view dealing with Russia: People with experience in U.S. hacking operations say they expect both Washington and Moscow to show caution in how they wield their digital weapons. … The CIA and NSA have spent years burrowing into Russia’s critical computer networks to collect intelligence — and acquire access that President Joe Biden could seize on to order destructive cyberattacks on Vladimir Putin’s regime. Politico, March 12, 2022
China says U.S. addresses used its computers to launch cyberattacks on Russia, Ukraine: SHANGHAI, March 11 (Reuters) – China has experienced continuous cyberattacks since February in which internet addresses in the United States have been used to seize control of Chinese computers to target Belarus, Russia and Ukraine, state news agency Xinhua said on Friday. Reuters, March 11, 2022
EXCLUSIVE BNP Paribas bars Russia-based staff from computer systems as cyber attack fears grow: LONDON/FRANKFURT, March 9 (Reuters) – France’s largest bank BNP Paribas has cut off its Russia-based workforce from its internal computer systems as it seeks to bolster its defences against any potential cyber attack, a source with direct knowledge of the matter told Reuters. Reuters, March 9, 2022
Russia to attempt to use ransomware funds to support economy.
Russia May Use Ransomware Payouts to Avoid Sanctions’ Financial Harm: FinCEN warns financial institutions to be wary of unusual cryptocurrency payments or illegal transactions Russia may use to ease financial hurt from Ukraine-linked sanctions. Threatpost, March 10, 2022
Two alleged cybercriminals extradited to US.
REvil ransomware member extradited to U.S. to stand trial for Kaseya attack: The U.S. Department of Justice announced that alleged REvil ransomware affiliate, Yaroslav Vasinskyi, was extradited to the United States last week to stand trial for the Kaseya cyberattack. Bleeping Computer, March 10, 2022
Canadian Ransomware Suspect Extradited to US After Officials Seize $28M in Cryptocurrency: A former Canadian government employee was turned over to the US to face charges of using ransomware to scam millions of dollars from victims. c|net, March 10, 2022
Section 2 – Personal Security and Privacy
Important stories for protecting yourself and your family.
Let’s be careful out there.
Watch out for this phishing attack that hijacks your email chats to spread malware: Hackers know you are more likely to trust messages that look like they’re part of an ongoing conversation. … A prolific botnet used to deliver malware, ransomware and other malicious payloads is spreading itself by hijacking email conversations in order to trick PC users into downloading it in what’s described as an “extremely active” phishing campaign. ZD Net, March, 10, 2022
Social media phishing attacks are at an all time high: Phishing campaigns continue to focus on social media, ramping up efforts to target users for the third consecutive year as the medium becomes increasingly used worldwide for communication, news, and entertainment. Bleeping Computer, March 4, 2022
Managing your security.
A Practical Guide to Securing Your Windows PC: There’s no one-size-fits-all solution to computer security, and locking down and securing your computer might feel like an impossible task, but that doesn’t have to be the case. There is such a thing as “good enough” security for most people. And securing your Windows PC doesn’t have to cost money, consume a lot of time, or require technical know-how—it just takes enough patience to navigate a series of Windows settings. Wirecutter, March 4, 2022
Locked-Out Account Users Wrestle With Two-Factor Authentication: Two-factor authentication aims to keep hackers out of online accounts. It sometimes keeps their rightful owners out too. … Consumers who use two-factor authentication are finding that changing a phone number or neglecting to write down recovery codes can leave them inadvertently locked out of online accounts. … Companies are increasingly pushing account holders to embrace two-factor authentication, a login method that typically makes users supplement their passwords with codes sent by apps or texts. Wall Street Journal, March 9, 2022
Synthetic Identity Fraud: One more reason to freeze your credit.
What Is Synthetic Identity Fraud?: Cybercriminals don’t need to know everything about you to commit fraud. Here’s how to prevent and report synthetic fraud. … Identity theft has always been an issue, but, as the internet has taken over more aspects of daily life, the threat has never been greater. It’s become easier to steal people’s personal information, and a new problem has emerged: synthetic identity fraud. MUO, March 6, 2022
Section 3 – General Cyber Security and Privacy Stories
Cybersecurity and privacy stories for those wanting a deeper look.
Cyber attacks increasing in frequency and severity.
LockBit ransomware gang claims attack on Bridgestone Americas: A cyberattack on Bridgestone Americas, one of the largest manufacturers of tires in the world, has been claimed by the LockBit ransomware gang. Bleeping Computer, March 11, 2022
Ubisoft says it experienced a ‘cyber security incident’, and the purported Nvidia hackers are taking credit: Ubisoft believes no personal player information was exposed … Ubisoft experienced a “cyber security incident” last week that temporarily disrupted some games, systems, and services, the company reported Thursday. Ubisoft hasn’t said who might be responsible, but on Friday evening, the group who purportedly hacked Nvidia took credit. The Verge, March 11, 2022
Dunno about you, but we’re seeing an 800% increase in cyberattacks, says one MSP: Cyberwarfare escalates for some as Russia continues to invade Ukraine … Revenge and inflation are key drivers behind an 800 percent increase in cyberattacks seen by a managed services provider since the days before the onset of Russia’s invasion of Ukraine last month, according to the company’s top executive. The Register, Mar 11, 2022
FBI Alert: Ransomware Attacks Hit Critical Infrastructure Organizations: Bureau releases indicators of compromise for the RagnarLocker ransomware that has hit 10 different critical infrastructure sectors. … The FBI issued a warning this week that the RagnarLocker ransomware has infected some 52 organizations in manufacturing, energy, financial services, government, and information technology so far this year. DARKReading, March 9, 2022
Emotet Botnet’s Latest Resurgence Spreads to Over 100,000 Computers: The insidious Emotet botnet, which staged a return in November 2021 after a 10-month-long hiatus, is once again exhibiting signs of steady growth, amassing a swarm of over 100,000 infected hosts for perpetrating its malicious activities. The Hacker News, March 9, 2022
Cyber firm: At least 6 US state governments hacked by China: Hackers working on behalf of the Chinese government broke into the computer networks of at least six state governments in the United States in the last year. That’s according to a report released Tuesday by a private cybersecurity firm. The report from Mandiant does not identify the hacked agencies or offer a motive for the intrusions, which began last May and continued through the last month. Yahoo!News, March 8, 2022
Google: Chinese hackers target Gmail users affiliated with US govt: Google’s Threat Analysis Group has warned multiple Gmail users that they were targeted in phishing attacks conducted by a Chinese-backed hacking group tracked as APT31. Bleeping Computer, March 8, 2022
Russia, China May Be Coordinating Cyber Attacks: SaaS Security Firm: A SaaS security company says a spike in cyber attacks from Russia and China in recent weeks suggests the two countries may be coordinating their cyber efforts. eSecurity Planet, March 8, 2022
Filling the cyber talent pipeline.
Microsoft: There’s a critical shortage of women in cybersecurity, and we need to do something about it: There are more than 2.5 million open cybersecurity jobs worldwide, says Microsoft – meaning it’s never been more important to get women into the industry. … Encouraging more women to pursue cybersecurity careers is “mission-critical” to filling some of the 2.5 million open jobs worldwide and tackling a global shortage of tech skills, Microsoft has said. ZD Net, March 10, 2022
SEC to vote on stronger security disclosure rules.
SEC to vote on new cybersecurity disclosure rules as Ukraine crisis gives them ‘special relevance’: The Securities and Exchange Commission is voting on Wednesday to propose new cybersecurity rules for public companies. … There are two components to the proposal: Mandatory cybersecurity incident reporting and required disclosures on company policies to manage cybersecurity risks. CNBC, March 9, 2022
Countering Putin’s ongoing disinformation campaign.
Russia’s Information War Is Being Waged on Social Media Platforms: Days after Russia invaded Ukraine, multiple social media platforms—including Facebook, Twitter and YouTube—announced they had dismantled coordinated networks of accounts spreading disinformation. These networks, which were comprised of fabricated accounts disguised with fake names and AI-generated profile images or hacked accounts, were sharing suspiciously similar anti-Ukraine talking points, suggesting they were being controlled by centralized sources linked to Russia and Belarus. Scientific American, March 8, 2022
Brian Krebs continues his expose of the notorious Conti ransomware gang.
Conti Ransomware Group Diaries, Part IV: Cryptocrime: Three stories here last week pored over several years’ worth of internal chat records stolen from the Conti ransomware group, the most profitable ransomware gang in operation today. The candid messages revealed how Conti evaded law enforcement and intelligence agencies, what it was like on a typical day at the Conti office, and how Conti secured the digital weaponry used in their attacks. This final post on the Conti conversations explores different schemes that Conti pursued to invest in and steal cryptocurrencies. KrebsOnSecurity, March 7, 2022
Section 4 – Securing the Organization
Stories to support executives and top management in securing their organizations.
Let’s be careful out there.
Malware now using NVIDIA’s stolen code signing certificates: Threat actors are using stolen NVIDIA code signing certificates to sign malware to appear trustworthy and allow malicious drivers to be loaded in Windows. Bleeping Computer, March 5, 2022
Over 40% of Log4j Downloads Are Vulnerable Versions of the Software: The data point is a reminder of why fixing the widespread vulnerability will take a long time. … Three months after the Apache Foundation disclosed the infamous Lo4j vulnerability [CVE-2021-44228] and issued a fix for it, more than 4 in 10 downloads of the logging tool from the Maven Central Java package repository continue to be known vulnerable versions. DARKReading, March 10, 2022
Update now as CISA adds 11 new vulnerabilities that are being actively exploited.
CISA has added 11 new vulnerabilities to its Known Exploited Vulnerabilities Catalog: CISA Adds 11 Known Exploited Vulnerabilities to Catalog, based on evidence that threat actors are actively exploiting the vulnerabilities listed in the table below. These types of vulnerabilities are a frequent attack vector for malicious cyber actors of all types and pose significant risk to the federal enterprise. Cybersecurity& Infrastructure Security Agency, March 7, 2022
Why You Should Be Using CISA’s Catalog of Exploited Vulnerabilities: It’s a great starting point for organizations that want to ride the wave of risk-based vulnerability management rather than drowning beneath it. … The Cybersecurity and Infrastructure Security Agency (CISA) recently issued Binding Operations Directive 22-01 aimed at reducing risk associated with actively exploited vulnerabilities. The directive was accompanied by a catalog of known exploited vulnerabilities maintained by CISA that includes mandatory remediation deadlines. Essentially, it means “fix these fast or else” for applicable agencies and organizations. DARKReading, March 10, 2022
Cyber surveillance: Is this really how we want to ensure worker productivity?
The IT department says it was asked to spy on co-workers. It didn’t go well: Is this really the best way to manage employees? Is it even a good way to manage the IT department? ZD Net, March 6, 2022
Industry alliance to provide support for zero-trust.
For those with zero trust in zero-trust networks, this industry alliance may help: The Cloud Security Alliance is trying to cut through the myriad zero-trust approaches and solutions out there and attempt to offer some practical info for corporate network admins. The Register, March 11, 2022


