SecureTheVillage Calendar
TownHallWebinar: Power Hour: Get the Facts with the Cyber Security Summit. May 20 @ 10:30 am – 12:00 pm PDT
TownHallWebinar: Online Event: Doing it…. Online with Dr. Steve Krantz. June 3 @ 1:00 pm – 2:30 pm PDT
Financial Services Cybersecurity Roundtable: Current Financial Services Threat Landscape. June 19 @ 8:00 am – 10:00 am
TownHallWebinar: Up On Cyber 2020. June 25 @ 8:00 am – 12:30 pm PDT
TownHallWebinar: Personal Cyber Security with Dr. Steve Krantz. July 21 @ 1:00 pm – 2:30 pm PDT
Donna Woods – Educator and SecureTheVillage Friend – Receives Presidential Cybersecurity Education Award
California Teacher Honored as Inaugural Presidential Cybersecurity Education Award Recipient. … Donna Woods recognized for instilling in her students the skills, knowledge, and passion for cybersecurity: MORENO VALLEY, Calif., May 14, 2020 /PRNewswire/ — U.S. Secretary of Education Betsy DeVos announced this week that Donna Woods, the Career Technical Education Cyber Pathway Instructor, at Moreno Valley Unified School District, has been selected as one of two national inaugural Presidential Cybersecurity Education Award recipients. This award recognizes Ms. Woods, of Canyon Springs High School, for instilling in her students the skills, knowledge, and passion for cybersecurity. Ms. Woods was nominated for the honor by synED, a non-profit organization that identifies emerging best practices for effective articulation between employers, jobseekers and education providers. PR Newswire, May 14, 2020
Individuals at Risk
Cyber Privacy
Email Data Leak Found to Be Feeding Information to Advertising and Analytics Companies: A widespread email data leak is forwarding addresses in plain text to a variety of advertising and analytics companies, without end users being aware of what is happening. This leak occurs when users sign up for, unsubscribe from, or click on marketing emails from popular online services: MailChimp, Quibi, Wish, JetBlue and the Washington Post among the bigger names. The user’s email address winds up being forwarded to marketing programs run by Google, Facebook, Microsoft and Twitter among others. CPO, May 14, 2020
Cyber Danger
This powerful Android malware stayed hidden for years, infecting tens of thousands of smartphones: Mandrake spyware hoovers up information raging from account credentials, screen records, GPS and more — and has been for years. All while those behind it carefully cover their tracks. ZDNet, May 14, 2020
Cyber Update
Microsoft Patch Tuesday, May 2020 Edition: Microsoft today issued software updates to plug at least 111 security holes in Windows and Windows-based programs. None of the vulnerabilities were labeled as being publicly exploited or detailed prior to today, but as always if you’re running Windows on any of your machines it’s time once again to prepare to get your patches on. KrebsOnSecurity, May 12, 2020
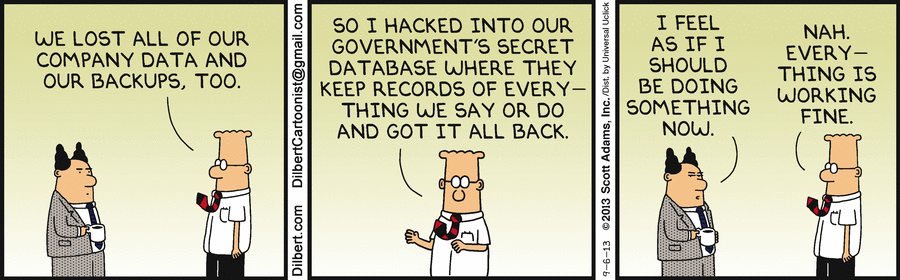
CyberHumor
Information Security Management for the Organization
Information Security Management and Governance
The Definitive Cyber Security Statistics Guide for 2020: Cyber attacks continue to grow in both numbers and ferocity — 2019 was just a sign of the things to come. Here’s your list of 122 of the most current cybersecurity industry, cyber attack, and data breach statistics for 2020 and beyond. The SSL Store, May 14, 2020
“Thinking About Thinking” is Critical to Cybersecurity … Most cybersecurity vulnerabilities are created by often unconscious human decisions. Understanding mental shortcuts we use in decision-making can help strengthen cybersecurity: Humans make a lot of decisions each day, whether we are aware of them or not. Research shows that people make approximately 200 decisions about food every single day1. And, depending on how we define the word “decision,” the daily number can creep into the tens of thousands. Although we may believe our decisions are rational, cognitive scientists argue that we are far less objective than we think. Cognitive biases shape our cybersecurity decisions from the keyboard to the boardroom, and these decisions ultimately determine the effectiveness of our cybersecurity solutions. CSO, May 14, 2020
Three Years After WannaCry, Ransomware Accelerating While Patching Still Problematic … The WannaCry ransomware worm remains a study in preventable catastrophes. Yet many companies continue to ignore its lessons: Three years ago, the WannaCry ransomware worm quickly compromised hundreds of thousands of out-of-date, unpatched computers and servers, encrypting data on the systems and often shutting down operations at affected organizations. Dark Reading, May 13, 2020
Paying Ransom Doubles the Cost of Ransomware Attack: Research: Cybersecurity firm Sophos recently announced the findings of its global survey “The State of Ransomware 2020,” which revealed that paying ransom for data decryption post a ransomware attack is far more expensive. The research said that the total cost of recovery from a ransomware attack almost doubles when organizations pay ransom to cybercriminals. CISOMag, May 13, 2020
The state of ransomware 2020: Results of an independent study of
5,000 IT managers across 26 countries. Sophos, May 2020
Cyber Defense
What is the Zero Trust Framework in cybersecurity and 5 considerations for building a Zero Trust IT environment: Zero Trust isn’t a product or service, and it’s certainly not just a buzzword. Rather, it’s a particular approach to cybersecurity. It means exactly what it says – not ‘verify, then trust’ but ‘never trust and always verify.’ SCMedia, May 15, 2020
Top 10 most exploited vulnerabilities list released by FBI, DHS CISA: When work-from-home became a sudden, urgent need in March, many organizations slapped together cloud-collaboration services such as Microsoft Office 365 for their newly locked-down staff. Naked Security, May 14, 2020
Cyber Talent
The lack of women in cybersecurity leaves the online world at greater risk: Women are highly underrepresented in the field of cybersecurity. In 2017, women’s share in the U.S. cybersecurity field was 14%, compared to 48% in the general workforce. The Conversation, May 13, 2020
Secure The Human
Biases in Perceptions of Information Security Threats: As of March 2020, everyone in the UK was asked to work from home where possible. This current shift in situation presents not only technological but also human factor challenges for information security. Organizations will have to tailor their awareness campaigns and training to target issues specific to working from home, confronting new security-based obstacles that their employees and clients might be facing. InfoSecurity, May 15, 2020
Cybersecurity in Society
Cyber Crime
‘REvil’ Hackers Double Their Allen Grubman Ransom Demand To $42m, Threaten To Dump Donald Trump Dirt: The cyberattackers who broke into a top celebrity law firm have increased their demands and dropped a new name in their campaign of intimidation: Donald Trump. The Daily Beast, May 15, 2020
Healthcare Giant Magellan Struck with Ransomware, Data Breach: Logins, personal information and tax info were all exfiltrated ahead of the ransomware attack, thanks to a phishing email. ThreatPost, May 14, 2020
COVID-19 blamed for 238% surge in cyberattacks against banks. Disarray caused by the pandemic has become a breeding ground for financially-motivated attacks: The coronavirus pandemic has been connected to a 238% surge in cyberattacks against banks, new research claims. ZDNet, May 14, 2020
Texas courts slammed by ransomware attack Officials say they will not bow to any blackmail or ransom demands: Texas has revealed a ransomware attack launched against its court system but insists no ransom will be paid. ZDNet, May 12, 2020
Pitney Bowes hit with second ransomware attack: For the second time in a seven-month span, Pitney Bowes has been hit by a ransomware attack, but cyber experts and financial analysts cautioned against rashly judging the company’s security practices – or assuming fiscal doom – with some suggesting that lessons learned from the first attack may have limited the damage of the most recent one. SCMedia, May 12, 2020
Ransomware Hit ATM Giant Diebold Nixdorf: Diebold Nixdorf, a major provider of automatic teller machines (ATMs) and payment technology to banks and retailers, recently suffered a ransomware attack that disrupted some operations. The company says the hackers never touched its ATMs or customer networks, and that the intrusion only affected its corporate network. KrebsOnSecurity, May 11, 2020
Cyber Attack
Cyber Attack On U.K. Electricity Market Confirmed: National Grid Investigates: The company that facilitates payments on the U.K. electricity market, tracking the trade between those who produce electricity and those who supply it and resolving the differences, has fallen victim to a cyber-attack. Elexon is at the center of the balancing and settlement system, working with Great Britain’s National Grid Electricity System Operator (ESO) to keep the lights on. The lights didn’t go off across the U.K. as a result of this cyber-attack, but internal IT systems and laptops at Elexon went dark. Forbes, May 15, 2020
Know Your Enemy
Crypto-Lock and Tell: Ransomware Gangs Double Down on Leaks. Dedicated Leak Sites Are Likely Driving More Victims to Pay, Security Experts Warn: Ransomware continues to pummel organizations, as many attackers don’t just bring crypto-locking malware to bear, but also steal and threaten to leak data. BankInfoSecurity, May 15, 2020
A cybercrime store is selling access to more than 43,000 hacked servers: The MagBo portal provides access to hacked servers, with some belonging to local and state government, hospitals, and financial organizations. ZDNet, May 14, 2020
National Cybersecurity
Internet Lessons from COVID19 — by “Father of the Internet” Vint Cerf: The novel SARS-COV-2 virus that leads to COVID-19 disease is teaching us a great many lessons about infrastructure writ large. We are discovering weaknesses in socio-economic safety nets, in our healthcare systems, public transportation system, our education systems and many others. Societies around the world are organized around a presumption that people can work, play and interact with each other in close proximity. Our dependence on this assumption has been upended by a virus that propagates through proximity and through the air and on commonly touched surfaces. Among the responses, social distancing has become a strong recommendation around the globe. But our physical infrastructure is operationally dependent on people being able to work together in proximity. That includes traveling together. One has only to look at the airline industry to see how quickly that mode of travel has evaporated. Schools have been closed in favor of remote education and “work from home” has become a guideline for those whose jobs permit it. For many, of course, work requires proximity, from haircuts to grocery stores, people need to be present. If that isn’t safe, many people cannot work and the economic impact is catastrophic. Medianama, May 14, 2020
The Cybersecurity 202: Commission that pushed a cybersecurity overhaul hopes coronavirus boosts the effort: The lawmakers behind an ominous report about America’s lack of preparedness for a major cyberattack are hoping the coronavirus pandemic will boost their calls to overhaul the nation’s digital defenses. The Washington Post, May 15, 2020
Cyber History
The Confessions of Marcus Hutchins, the Hacker Who Saved the Internet: At 22, he single-handedly put a stop to the worst cyberattack the world had ever seen. Then he was arrested by the FBI. This is his untold story. Wired, May 12, 202
Secrets, Surveillance and Snowden … After receiving top-secret documents from the NSA whistleblower, reporter Barton Gellman broke the news that the National Security Agency was spying on Americans. Here’s how it happened: The inbox logged a message as I slept. Many hours passed before I checked. Probably should have kept away, but habit tugged. We had taken the channel dark last night. Not because we knew it was blown, but because we could not know. These email accounts were anonymous, encrypted, isolated from our everyday Internet lives. Best I could tell, there was no way to lock them down tighter. That thought had reassured me once. The Washington Post, May 11, 2020
Cyber Freedom
The Cybersecurity 202: New Jersey lawsuit tries to block Internet voting in the state: Human rights activists and New Jersey law students are suing to block the state from using Internet-based voting systems, which security experts say are fundamentally insecure against hacking. The Washington Post, May 14, 2020
Fake News
Project Aims to Unmask Disinformation Bots … BotSight, a machine learning project, rates Twitter users based on the likelihood that there is a human behind the keyboard. Could such technology blunt the impact of disinformation campaigns?: Aiming to combat disinformation on social media, a research team published plug-ins for major Web browsers on Thursday that give users a score as to the likelihood that a Twitter handle is a bot or a human. DarkReading, May 14, 2020


