A weekly aggregation of important cybersecurity and privacy news designed to educate, support, and advocate; helping you meet your data care challenges and responsibilities.
Stan’s Top of the News
If you read only one story in depth this week, make it Jessica Roy’s courageous telling of the identity theft nightmare that befell her when her wallet was stolen. It’s a compelling story of pain and determination as she struggled to clean up her stolen identity. It’s also peppered with things we can all do to better protect ourselves — starting with freezing our credit — and what we need to insist government do to help. If you’re an LA Times subscribers, there are three other stories in the series that I also recommend you read.
- My wallet was stolen at a bar. Then my identity theft nightmare began: 2019 was a pretty exciting year for me. … I stole a Tesla. I got into a car accident — a BMW, that time. I got a new iPhone. I opened two new checking accounts and went on a bad-check-writing spree for as much as $13,000 at a time. I attempted to open dozens of new credit cards. I wrote a check for someone’s bail, which they skipped. … On paper, Jessica Roy had a wild year. In reality, that year, and what followed, has been a nightmare. … I am the victim of identity theft. And it could happen to you. I also have some bad news: It will be entirely your problem, and no one — not the police, not the government, not the financial institutions — really cares or will help you much. But with determination, you can fight back. I did. … My troubles started in a bar in San Francisco the day after Thanksgiving 2018. When I went to close my tab, I discovered my wallet was gone. By the time I got my bank on the phone the next morning, my debit card had been used at a gas station for $48.15 and with a Square card reader for $30. I disputed both transactions and canceled all my cards. I went to a San Francisco police station to report the stolen wallet. … When I got home to L.A., I had to get a new driver’s license, had to update my autopay bills and had to buy a new wallet. I thought that was the end of it. … Then the letters started arriving. … Jessica Roy Assistant Editor, Utility Journalism, Los Angeles Times, 10/26/22
SecureTheVillage launches a campaign to identify and strengthen user basic cybersecurity practices.
- How Hackable Are You? Think your defenses are strong. Find out as SecureTheVillage tests you on five basics. Please take our short quiz as your answers will help you and guide us to improve community safety.
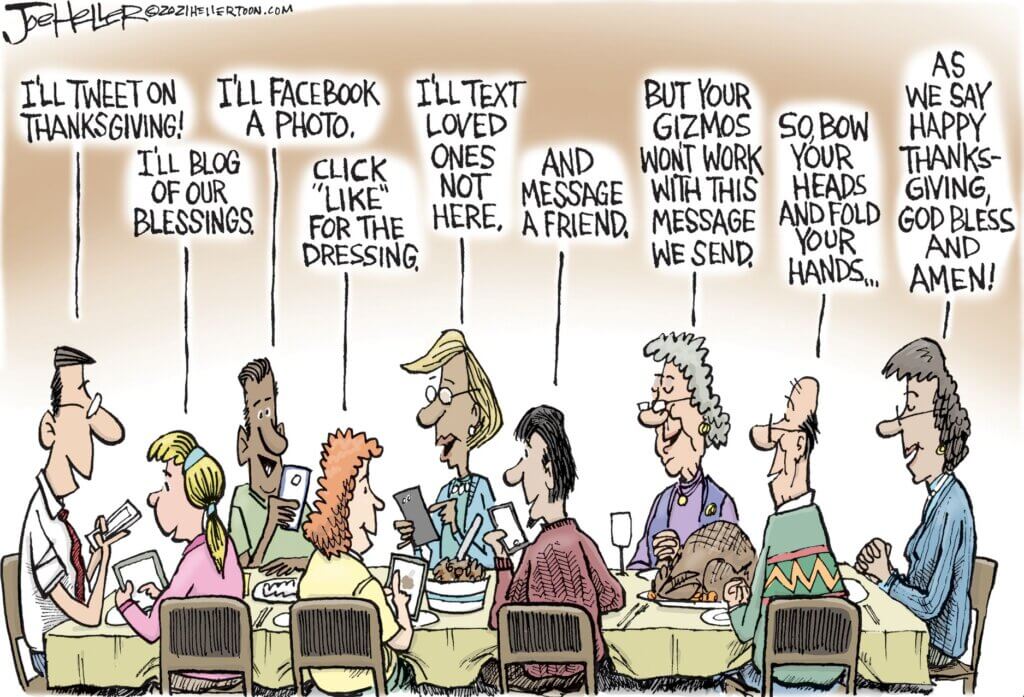
Cyber Humor
Cybersecurity Nonprofit of the Week … US Valor
Kudos this week to US Valor, a nonprofit with two intertwined objectives: (1) helping veterans transition back into civilian life and (2) helping America meet our cybersecurity workforce challenge. US Valor does this through an innovative Department of Labor approved Apprenticeship Program. The US Valor Cybersecurity Apprenticeship Program (CAP) is all about helping transitioning military personnel and U.S. Veterans experience a smooth transition from military life to the civilian world through its Department of Labor Registered Apprenticeship Program (RAP). I’m a proud member of US Valor’s Advisory Board and I encourage you to support them.
Live on Cyber with Dr. Stan Stahl – Live on LinkedIn

Live on Cyber with Dr. Stan Stahl: Where’s Julie, you ask!! While she’s taking a well-deserved break, I asked my friend and colleague Kelly Kendall to join me on Live on Cyber. Kelly’s the founder / CEO of US Valor, this week’s Cybersecurity Nonprofit. Join Kelly and me as we discuss US Valor’s innovative program to meet the twin challenges of (i) helping veterans transition back into civilian life and (ii) meeting our cybersecurity workforce challenge.
Section 2 – Personal Data Care – Security and Privacy
Important data care stories for protecting yourself and your family.
It’s the holidays. Time for deals. And time for steals as the scammers ramp up their activities. Be careful out there!!! Never Trust. Always verify.
- Black Friday and Cyber Monday Shoppers: Expect More Fraud Than Ever: This year will see record holiday spending—along with a surge in scam websites and products, according to a recent study. These tips can help keep you and your loved ones safe. … Here’s a scene you might be familiar with: It’s the weekend after Thanksgiving, and you find a minute to check out some online deals. An item comes on the screen with way more features than you expected, at a much lower price than you thought possible. It might be sold by an unfamiliar website or one you’ve used time and time again. … You press Add to Cart, enter your credit card details, and pull the trigger. Satisfied with your deal-hunting, it’s time to celebrate with a fresh plate of leftovers. … But then a few days go by, and things get weird. PC Magazine, November 18, 2022
- Phishing kit impersonates well-known brands to target US shoppers: A sophisticated phishing kit has been targeting North Americans since mid-September, using lures focused on holidays like Labor Day and Halloween. … The campaign spotted by Akamai started in September 2022 and continued throughout October, preying on online shoppers looking for “holiday specials.” … The central theme of the phishing emails sent to prospective victims is a chance to win a prize from a reputable brand. … Everyone visiting the phishing site wins the promised prize after completing a short survey. In addition, a five-minute timer ensures those taking the survey are infused with a feeling of urgency. … Some impersonated brands include sporting goods firm Dick’s, high-end luggage maker Tumi, Delta Airlines, and the wholesale clubs, Sam’s Club and Costco. Bleeping Computer, November 17, 2022
- BofA managers hear Zelle scammer as victim puts them on speakerphone, fraud claim still denied: A woman runs into Bank of America with a Zelle scammer still on the phone, hoping the bank could stop him from receiving her money. Bank managers heard the scammer claiming to be from PG&E and trying to get more money. In the end, Bank of America said it wasn’t fraud and denied her claim for a refund. ABC7, KGO, November 16, 2022
Section 3 – A Deeper Look for the Cyber-Concerned Citizen
Data Care, cybersecurity, and privacy stories to keep you informed.
As Twitter continues to seemingly implode, here are two articles describing the potential for more disinformation and the impact of lessened cybersecurity.
- I Was the Head of Trust and Safety at Twitter. This Is What Could Become of It: This month, I chose to leave my position leading trust and safety at Elon Musk’s Twitter. … My teams were responsible for drafting Twitter’s rules and figuring out how to apply them consistently to hundreds of millions of tweets per day. In my more than seven years at the company, we exposed government-backed troll farms meddling in elections, introduced tools for contextualizing dangerous misinformation and, yes, banned President Donald Trump from the service. The Cornell professor Tarleton Gillespie called teams like mine the “custodians of the internet.” The work of online sanitation is unrelenting and contentious. … Enter Mr. Musk. Yoel Roth, The New York Times, November 18,m 2022
- Here’s How Bad a Twitter Mega-Breach Would Be: Elon Musk laid off half the staff, and mass resignations seem likely. If nobody’s there to protect the fort, what’s the worst that could happen? … The possibility of a Twitter breach is particularly worrying given a whistleblower report and congressional testimony this summer from Twitter’s former chief security officer, Peiter Zatko, that alleged an already dire state of the company’s internal defenses and access controls. In other words, the company already seemingly had security issues before Musk took over—and the situation may have gotten worse since. Wired, November 17, 2022
We’re posting four ransomware stories this week to illustrate the national security implications of these attacks.
- Michigan school districts reopen after three-day closure due to ransomware attack: Public schools in two Michigan counties are reopening on Thursday after a ransomware attack crippled their ability to function and closed doors to students for three days. … All of the public schools in Jackson and Hillsdale counties announced their reopening on Thursday in letters to parents, assuring them that cybersecurity experts, tech officials and law enforcement worked around the clock to restore the systems following outages that began on Monday. … Jackson County Intermediate School District Superintendent Kevin Oxley said the ransomware attack was detected last weekend, and they proactively took their systems offline in order to contain the damage. … During the attack he urged students and teachers not to use school-issued devices. By Wednesday, he they were able to bring essential systems back online. … “However, students will continue to have limited access to several technology resources when they return tomorrow, as our teams continue to work on restoring additional systems,” he said. The Record, November 17, 2022
- Hive ransomware actors have extorted over $100M from victims, says FBI: The U.S. government has warned of ongoing malicious activity by the notorious Hive ransomware gang, which has extorted more than $100 million from its growing list of victims. … A joint advisory released by the FBI, the U.S. Cybersecurity and Infrastructure Security Agency, and the Department of Health and Human Services on Thursday revealed that the Hive ransomware gang has received upwards of $100 million in ransom payments from more than 1,300 victims since the gang was first observed in June 2021. TechCrunch, November 18, 2022
- Ransomware incidents now make up majority of British government’s crisis management COBRA meetings: Ransomware incidents in the United Kingdom are now so impactful that the majority of the British government’s recent crisis management COBRA meetings have been convened in response to them rather than other emergencies. The Record, November 18, 2022
- Ransomware is a global problem that needs a global solution: This time last year, we were optimistic. It seemed like the tide was turning on ransomware after the U.S. government scored a handful of wins against the cybercriminals carrying out these increasingly damaging attacks: the Justice Department successfully seized $2.3 million in bitcoin that Colonial Pipeline paid to the DarkSide ransomware gang to reclaim its data, and months later it played a part in bringing down the notorious REvil ransomware gang. Tech Crunch, November 18, 2022
This story is worrisome. A Russian business passing itself off as an American company has its code installed in thousands of smartphone applications, the Army, and the CDC. Something nefarious is going on. Stay tuned.
- Russian Code Found in Thousands of American Apps, Including the CDC’s: Why is a Russian company that supplied code to thousands of apps on both Google Play and the Apple App Store pretending to be American? … A software company whose code is used in thousands of widely downloaded apps has been pretending to be based in the U.S. when, in reality, it operates out of Russia, new reporting from Reuters shows. The company, Pushwoosh, used fake street addresses and even fake employee profiles on LinkedIn to create the illusion that it was headquartered in the U.S., according to the recent investigation, but the firm is actually located in a city in Siberia. … Pushwoosh’s code is used in at least eight thousand different apps currently available on the Google Play and Apple store. The company’s clients have even included the Army and Center for Disease Control and Prevention (CDC), which, until recently, used its code in at least seven different public-facing apps. Gizmodo, November 14, 2022
This week we have two privacy / surveillance stories. The Commonwealth of Massachusetts is being sued for allegedly installing a contact tracing application on residents’ smartphones without users permission or knowledge. And the European Union is in the midst of a spyware scandal that links back to the Pegasus spyware from NSO Group.
- Massachusetts Secretly Installed COVID Spyware App on Smart Phones: Lawsuit: The Massachusetts Health Department secretly installed surveillance software on New Englanders’ smart phones without their consent, a lawsuit filed Monday in U.S. District Court of Massachusetts alleges. … The lawsuit alleges that the Commonwealth of Massachusetts worked with Google to develop a contact tracing application for residents’ smartphones near the end of the COVID-19 epidemic. … But when few residents voluntarily downloaded the app, Massachusetts’ caused the surveillance app to be downloaded on the smart phones of Mass. residents — and even New Hampshire residents who worked in the state — without users permission or knowledge. Maine Wire, November 18, 2022
- Europe’s Spyware Scandal Is a Global Wakeup Call: Multiple European governments are using advanced surveillance tools to spy on their own people, according to a damning new European Parliament report. “EU Member States have been using spyware on their citizens for political purposes and to cover up corruption and criminal activity,” the report reads. “Some went even further and embedded spyware in a system deliberately designed for authoritarian rule.” Slate, November 15, 2022
We’re covering four national cybersecurity stories this week.
- Biden set to approve expansive authorities for Pentagon to carry out cyber operations: The Defense Department has largely won out in a long-running bureaucratic battle with the State Department over retaining its broad powers to launch cyber operations, according to two sources familiar with the matter. … While the exact details of which authorities the Pentagon retains to carry out cyber operations are classified, sources familiar with the matter said it succeeded in holding onto key parts of broad authorities the Trump administration granted DOD in 2018. Cyber Scoop, November 17, 2022
- The FBI alleges TikTok poses national security concerns: The head of the FBI says the bureau has “national security concerns” about the U.S. operations of TikTok, warning that the Chinese government could potentially use the popular video-sharing app to influence American users or control their devices. Npr, November 17, 2022
- Two enormous cyberattacks convince Australia to ‘hack the hackers’: Australia’s Cybersecurity Minister Clare O’Neil vowed this weekend to “hack the hackers” after two monumental, back-to-back cyberattacks against Australian telecommunications giant Optus and insurance titan Medibank affected swaths of people. … The fallout has included the public exposure of sensitive health data and the theft of information about millions of customers. The Cybersecurity 202, The Washington Post, November 15, 2022
- Russia’s cyber forces ‘underperformed expectations’ in Ukraine: senior US official: A senior cyber official at the Department of Defense said on Wednesday that Russian forces “underperformed expectations” in both the cyber and military space, as the West fears the Kremlin would unleash destructive cyberattacks against Ukraine as part of its invasion. The Hill, November 16, 2022
Section 4 – Information Security and Privacy Management in the Organization
Stories to support executives and top management in securing their organizations and protecting privacy.
Information security teams continue being challenged as the costs of cybercrime continue to climb, the technology challenges increase, and the nation’s cybersecurity workforce continues to be anemic.
- Zero-Trust Initiatives Stall, as Cyberattack Costs Rocket to $1M per Incident: Researchers find current data protections strategies are failing to get the job done, and IT leaders are concerned, while a lack of qualified IT security talent hampers cyber-defense initiatives. … Organizations are struggling with mounting data losses, increased downtime, and rising recovery costs due to cyberattacks — to the tune of $1.06 million in costs per incident. Meanwhile, IT security staffs are stalled on getting defenses up to speed. … That’s according to the 2022 Dell Global Data Protection Index (GDPI) survey of 1,000 IT decision-makers across 15 countries and 14 industries, which found that organizations that experienced disruption have also suffered an average of 2TB data loss and 19 hours of downtime. DARK Reading, November 17, 2022
- Not patched Log4j yet? Assume attackers are in your network, say CISA and FBI: Almost a year on from Log4j’s disclosure, a joint alert by CISA and the FBI warns organizations that if they haven’t protected their systems against it yet, they really need to now. … A joint security alert by CISA and the FBI has warned organizations that haven’t applied much-needed Log4j security patches and mitigations to VMware Horizon server instances to assume their network has been compromised and act accordingly. ZD Net, November 17, 2022


