A weekly aggregation of important cybersecurity and privacy news designed to educate, support, and advocate; helping you meet your data care challenges and responsibilities.
Stan’s Top of the News
This week’s Top of the News has stories on the great work being done by cybersecurity nonprofits.
SecureTheVillage has launched what we believe to be the first ever survey of actual user cybersecurity practices.
- Our short 5-question survey “How Hackable Are You” is designed to help everyone make sure they’re doing the basics. It will also provide SecureTheVillage insights to help us support the cybersecurity readiness of our families. People taking the survey can download our new Guide to Personal Cybersecurity and sign up for our Cybersecurity News of the Week and Weekend Vulnerability & Patch Report. We encourage all of our readers to take the survey and to invite their friends and neighbors to do the same.
Nonprofit Cyber, the first coalition of cybersecurity nonprofits, has released its index of 120 cybersecurity solutions offered by members. SecureTheVillage is a proud member of Nonprofit Cyber and our solutions that support mid-size and smaller organizations and individuals are included in the index.
- Nonprofit Cyber Releases Index of 120 Cybersecurity Solutions: Nonprofit Cyber announced that it had published an index of cybersecurity solutions offered by its members: the Nonprofit Cyber Solutions Index. This is the first comprehensive index of actual cybersecurity capabilities provided by the NGO community. In particular, the index identifies a large selection of free or low-cost cybersecurity capabilities for individuals, small businesses, and others left behind in the current environment. Other solutions, such as information sharing platforms for enterprises, cybersecurity companies, and governments are also included. … The Solutions Index includes 120 solutions from 23 Nonprofit Cyber members. It can be found here: https://nonprofitcyber.org/nonprofit-cyber-solutions-index/. The Index can be used as a “finding aid” to find, for example, the solutions provided that are intended for law enforcement or cybersecurity personnel. Nonprofit Cyber, November 3, 2022
Several nonprofits (many of them members of Nonprofit Cyber) have come together to develop the Cyber Incident Reporting Framework.
- The framework is designed to achieve the recommendations of the international Ransomware Task Force announced this week by the White House (see story below). The effort was led by the Cyber Threat Alliance and the Institute for Security and Technology and includes CREST, CipherTrace, Coveware, Cybera, Cybercrime Support Network, Cyber Peace Institute, Open Cybersecurity Alliance, and SolarWinds.
Michael Daniel, CEO of the Cyber Threat Alliance, and Megan Stifel, chief strategy officer for the Institute for Security and Technology, wrote the following opinion piece that puts the framework in the context of our Nation’s need to develop effective cybersecurity and privacy regulations.
- Cyber incident reporting isn’t the problem — ignorance is: For over 20 years, the federal government has urged industry — particularly those operating critical infrastructure systems like water systems and electric grids — to voluntarily secure their digital assets, share relevant threat information within their sectors, and report incidents to the government. This purely voluntary approach initially made sound legal and policy sense. The alternative, such as government monitoring private networks for signs of potential breaches, seemed both extreme and impractical. … Unfortunately, we have reached the limits of what purely voluntary approaches to cybersecurity can achieve. Without sufficient information, as a nation we remain ignorant of and overwhelmingly exposed to the full scope of our cyber risk. Our experience over the last 20 years indicates that we need the federal government to impose certain requirements if we want to reduce our level of cyber risk. The Hill, November 2, 2022
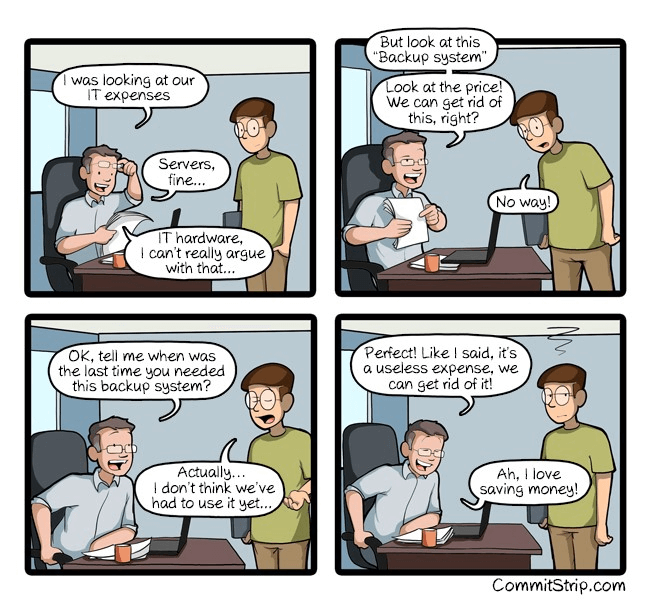
Cyber Humor
Security Nonprofits of the Week … Nonprofit Cyber and the Institute for Security and Technology
- Kudos this week to Nonprofit Cyber for its work compiling the Nonprofit Cyber Solutions Index. Nonprofit Cyber is a coalition of implementation-focused cybersecurity nonprofits who collaborate, work together on projects, voluntarily align activities to minimize duplication, increase mutual support, and link the community to key stakeholders with a shared communication channel. SecureTheVillage is a proud member of Nonprofit Cyber.
- Kudos this week also to The Institute for Security and Technology and their Ransomware Task Force (RTF). The Task Force aims to equip businesses, organizations, and governments of all sizes to prepare for ransomware attacks, effectively respond, and quickly recover. This week the Task Force published the Cyber Incident Reporting Framework. This follows the earlier release of its ‘Blueprint for Ransomware Defense’ representing a set of foundational and actionable safeguards derived from the Center for Internet Security’s Critical Security Controls. The Institute is a fellow-member of Nonprofit Cyber, the first-of-its-kind coalition of global nonprofit organizations to enhance joint action to improve cybersecurity.
Section 2 – Personal Data Care – Security and Privacy
Important data care stories for protecting yourself and your family.
- How Phone Scammers Tricked Americans Out of Nearly $40 Billion In 2022: 44,750 views Nov 4, 2022 Despite the rise of sophisticated crypto frauds and ransomware plots, phone scams continue to trick Americans out of tens of billions of dollars each year. CNBC, November 4, 2022
- These Android apps can steal your banking info by recording your screen — delete them now: Five malicious Android apps that appear innocent-looking at first glance have been discovered on the Google Play Store and are being used to steal banking information from unsuspecting users. … According to a report from ThreatFabric, these malicious apps pose as finance trackers and other utilities like file managers to trick potential victims into downloading them in the first place. However, this appears to be working as the five malicious apps discovered by the firm’s researchers have been downloaded over 100,000 times combined. Tom’s Guide, November 4, 2022
- Security Cameras Make Us Feel Safe, but Are They Worth the Invasion?: Internet cameras like Amazon’s Ring come at a high cost to our privacy. … San Francisco, long a capital of progressivism and a haven for techies, is about to embark on a citywide surveillance experiment that privacy experts warn could set a dangerous precedent. It signifies an important moment in which anyone who owns a security camera, including popular devices like Amazon’s Ring and Google’s Nest Cam, should pause to reflect on some critical questions: What are we actually getting from these cameras? What are we giving away? Are the trade-offs worth it? The New York Times, November 2, 2022
- The Prying Eyes of Social Media: The lack of regulation of online platforms puts our private lives up for sale. … When the Finnish prime minister, Sanna Marin, was recently captured on video dancing at a party with friends, a great deal of ink was spilled evaluating her behavior. She was criticized for conduct unbecoming a prime minister and for an exuberance that some on the far right gleefully—and falsely—claimed must have been excited by illicit drug use. This framing put the onus on Marin to closely monitor herself even in closed rooms, and it does the same for us all. It compels us to perpetually distrust weddings, birthday parties—anywhere there are others who have cell phones. … Marin was in a supposedly private space at a supposedly private party. Technology being what it is, the leak didn’t have to be an overtly intentional exposure. Yes, it could have been an undercover Russian spy or a stalker paid off to share dirt. But it is just as possible that a friend posted it—for supposedly “personal” use—on Facebook or WhatsApp or TikTok. It is too easy to forget that nothing posted on these platforms is ever really personal—even in the European Union, which has somewhat stronger protections than the United States. This kind of inadvertent surveillance is always a problem when posting content on social media. It can be extracted and exploited for both legal and illegal ends: to threaten political careers, to defame and embarrass, or, as we see in red states, to threaten those who are thinking about—or who are thought to be thinking about—abortion, contraception, or other “disobedience” in our brave new world. The Nation, September 20, 2022
Section 3 – A Deeper Look for the Cyber-Concerned Citizen
Data Care, cybersecurity, and privacy stories to keep you informed.
This week in cybercrime.
- US Treasury: Financial institutions reported $1.2 billion in ransomware losses in 2021: United States financial institutions reported a record year for ransomware attacks and payments in 2021 – driven by malware variants believed to be linked to Russia. In all, the cost of incidents reported last year under the Bank Secrecy Act jumped to $1.2 billion, from $416 million the year before. The Record, November 1, 2022
- Cybercrime reports jump as criminal gangs target families and businesses, cybersecurity agency says: Cybercrime is continuing to surge in Australia as gangs use increasingly sophisticated techniques to defraud and blackmail households, governments and businesses across the nation. … The Australian Cyber Security Centre (ACSC) has launched its third annual threat report, revealing that it received over 76,000 cybercrime reports last financial year – a 13 per cent increase from the year before. … The release comes in the wake of a string of high-profile data breaches — including cyber attacks on both Optus and Medibank — which have compromised the private data of millions of Australians. … And the figures in the threat report still only provide a partial picture because a large proportion of attacks go unreported. ABC News Australia, November 3, 2022
- Record $760M Stolen in Exploits During ‘Hacktober’: Bad Month for DeFi Security Highlights Pitfalls of Freewheeling Practices. … Call it Hacktober.The crypto market suffered a record $760M in exploits in October, according to PeckShield, a blockchain security company which lists MakerDAO, DeFi’s largest protocol, as a customer. … Despite an exploiter’s move to return $50M to users last month, the total value of stolen funds in 2022 surged to almost $3B. That’s nearly double the $1.5B hackers took in 2021 and nearly 12 times the 2020 total. The Defiant, November 1, 2022
- World’s second largest copper producer recovering from cyberattack: The second largest copper producer in the world said it is recovering from a cyberattack that forced it to shut off several IT systems. … German firm Aurubis did not respond to requests for comment but released a statement on Friday saying that overnight, the company faced a cyberattack that “was apparently part of a larger attack on the metals and mining industry.” … “As a result, numerous systems at Aurubis sites had to be shut down and disconnected from the internet as a preventive measure. Production could largely be maintained,” the company said. “The extent of the impact in the Group is currently being assessed. In addition, Aurubis is working closely with the investigating authorities.” The Record, October 31, 2022
- Crime group hijacks hundreds of US news websites to push malware: A cybercriminal group has compromised a media content provider to deploy malware on the websites of hundreds of news outlets in the U.S., according to cybersecurity company Proofpoint. TechCrunch, November 3, 3022
- $28 million stolen from cryptocurrency platform Deribit: Cryptocurrency derivatives platform Deribit on Tuesday said a hacker stole $28 million from the company, forcing it to halt withdrawals as it investigates the incident. The Record, November 2, 2022
- ALMA observatory in Chile targeted by cyberattack: The ALMA space telescope in the Chilean Andes suffered a cyberattack over the weekend that has downed its website and suspended its work, the observatory announced Wednesday. … ALMA, the world’s most powerful telescope for observing molecular gas and dust, studies the building blocks of stars, planetary systems, galaxies and life itself, according to the European Southern Observatory (ESO), its co-operator. … The attack Saturday on ALMA’s computer systems did not compromise its powerful antennas or any scientific data, it said on Twitter. … The cyberattack forced the suspension of astronomical observations, left the observatory with limited email services, and its website still offline four days later. France 24, November 2, 2022
- Dropbox discloses breach after hacker stole 130 GitHub repositories: Dropbox disclosed a security breach after threat actors stole 130 code repositories after gaining access to one of its GitHub accounts using employee credentials stolen in a phishing attack. … The company discovered the attackers breached the account on October 14 when GitHub notified it of suspicious activity that started one day before the alert was sent. … The successful breach resulted from a phishing attack that targeted multiple Dropbox employees using emails impersonating the CircleCI continuous integration and delivery platform and redirecting them to a phishing landing page where they were asked to enter their GitHub username and password. … On the same phishing page, the employees were also asked to “use their hardware authentication key to pass a One Time Password (OTP).” Bleeping Computer, November 1, 2022
The White House continues its international cybersecurity leadership while the United Kingdom has begun scanning the private sector to help get its arms around the cybersecurity challenge.
- White House Ransomware Confab Ends With Data Sharing Pledge: Three Dozen Countries Vow Cooperation and Get Tough Measures. … The United States, European Union and three dozen countries vowed a crackdown on ransomware after meeting for two days in the White House. … A voluntary International Counter Ransomware Task Force led by Australia will swap early warning signs of ransomware attacks “as well as consolidate policy and best practice frameworks,” the declaration states. … A Regional Cyber Defense Centre in Lithuania will test out the task force concept by implementing a scaled-down version of operationalized ransomware threat information sharing. Bank Info Security, November 1, 2022
- British govt is scanning all Internet devices hosted in UK: The United Kingdom’s National Cyber Security Centre (NCSC), the government agency that leads the country’s cyber security mission, is now scanning all Internet-exposed devices hosted in the UK for vulnerabilities. … The goal is to assess UK’s vulnerability to cyber-attacks and to help the owners of Internet-connected systems understand their security posture. … “These activities cover any internet-accessible system that is hosted within the UK and vulnerabilities that are common or particularly important due to their high impact,” the agency said. Bleeping Computer, November 4, 2022
Meanwhile, the cyber-insurance market continues its struggles responding to cyber risk.
- Insurance giant settles NotPetya lawsuit, signaling cyber insurance shakeup: The settlement last week in a $100 million lawsuit over whether insurance giant Zurich should cover losses Mondelez International suffered from NotPetya may very well reshape the entire cyber insurance marketplace. … In September, the Treasury Department asked for industry input on whether it should provide any “support for the cyber insurance market,” FedScoop reported. It is exploring policy measures such as “the creation of a backstop program for cyber insurance risk akin to the Terrorism Risk Insurance Program, which was created after 9/11 to allow Wall Street to continue to offer property insurance policies that include coverage for damage caused by acts of terrorism.” … FedScoop also noted the rising cost of cyber insurance and that the total cost of premiums increased 75% to $4.8 billion in 2021 compared to the previous year, according to data from the ratings agency A.M. Best. “In a June report, the agency noted that the number of reported claims in the U.S. cyber market had swelled to nearly 26,000 during 2021, up from 22,000 in the prior year, and about 6,000 in 2016.” CyberScoop, November 4, 2022
With the election just a couple of days away, we offer the following election security stories.
- China, Russia, and Iran Working To Undermine Midterm Elections, Cybersecurity Group Says: China is using a network of social media accounts and altered news articles to “sow division both between the U.S. and its allies and within the U.S. political system itself,” according to a threat assessment by Mandiant, a cybersecurity and intelligence organization that works with governments and the public sector. China’s latest efforts to undermine the American democratic process come amid parallel attempts by Russia and Iran to interfere with the upcoming elections. Washington Free Beacon, October 31, 2022
- Nearly 2,000 fake Twitter accounts were trying to churn up U.S. voters even more: At first glance, the Twitter accounts belonging to “Ultra MAGA BELLA Hot Babe” and “Salome Cliff” don’t seem to have much in common. With the former alleging voter fraud and criticizing transgender people, and the latter praising President Biden, the two accounts racked up thousands of followers on Twitter. … But the accounts were actually part of a newly disclosed China-based operation seeking to influence U.S. politics in the run-up to the midterms by amplifying polarizing topics. The Washington Post, November 1, 2022
- National Guard to offer midterm elections cybersecurity help: The move is part of a wider effort to ensure the midterms are secure from cybersecurity threats. … National Guard cybersecurity experts will be ready to offer assistance around the midterm elections in 14 states next week, National Guard officials said Friday. Politico, November 4, 2022
- CISA chief sees no “specific or credible threats” to election infrastructure: Jen Easterly, head of the Cybersecurity and Infrastructure Security Agency (CISA), said Sunday on Face The Nation that her agency has not seen “specific or credible threats” to compromise election infrastructure before Election Day, now just over a week away. … Even as there are no “specific or credible threats,” the federal government issued a general warning that domestic violence extremists across the ideological spectrum pose a “heightened threat” to the midterm contests. … The bulletin from a group of federal agencies and distributed to law enforcement partners across the country stated potential targets of violence by domestic violent extremists include candidates seeking public office, election officials and workers, political rallies and party representatives, among others. … While Easterly said she is confident the November elections will be “safe and secure,” and believes Americans should feel the same way about the integrity of elections in their states, the CISA chief acknowledged there is still concern about voter intimidation and threats to election workers. … “It is a very complex threat environment,” she said. “You have cyber threats, you have insider threats, you have rampant disinformation. And yes, very worryingly, you have threats of harassment, intimidation and violence against election officials, polling places and voters.” CBS News, October 30, 2022
The following story explores the cybersecurity risks resulting from Musk’s purchase of Twitter.
- How Elon Musk’s Twitter Buy Raises Cybersecurity Risks For The Rest Of Us: The problem is not just more misinformation, but five new threats to the network. … For all the worries that Elon Musk’s purchase of Twitter will roll back limits on hate speech and misinformation, the acquisition also presents major cybersecurity concerns. Now that a critical public communications network has become private property, there are five major cyber risks that have to be accounted for, both within the network and beyond. Defense One, November 1, 2022
LinkedIn continues to respond to the plethora of fake accounts that impact the trustworthiness and reliability of its platform.
- LinkedIn Adds Verified Emails, Profile Creation Dates: Responding to a recent surge in AI-generated bot accounts, LinkedIn is rolling out new features that it hopes will help users make more informed decisions about with whom they choose to connect. Many LinkedIn profiles now display a creation date, and the company is expanding its domain validation offering, which allows users to publicly confirm that they can reply to emails at the domain of their stated current employer. KrebsOnSecurity, November 4, 2022
Cybersecurity action by governments is again in the news.
- Chegg sued by FTC after suffering four data breaches within 3 years: The U.S. Federal Trade Commission (FTC) has sued education technology company Chegg after exposing the sensitive information of tens of millions of customers and employees in four data breaches suffered since 2017. Bleeping Computer, October 31, 2022
- Hacker Charged With Extorting Online Psychotherapy Service: A 25-year-old Finnish man has been charged with extorting a once popular and now-bankrupt online psychotherapy company and its patients. Finnish authorities rarely name suspects in an investigation, but they were willing to make an exception for Julius “Zeekill” Kivimaki, a notorious hacker who — at the tender age of 17 — had been convicted of more than 50,000 cybercrimes, including data breaches, payment fraud, operating botnets, and calling in bomb threats. KrebsOnSecurity, November 3, 2022
Section 4 – Information Security and Privacy Management in the Organization
Stories to support executives and top management in securing their organizations and protecting privacy.
- CISA Releases Guidance on Phishing-Resistant and Numbers Matching Multifactor Authentication: CISA has released two fact sheets to highlight threats against accounts and systems using certain forms of multifactor authentication (MFA). CISA strongly urges all organizations to implement phishing-resistant MFA to protect against phishing and other known cyber threats. If an organization using mobile push-notification-based MFA is unable to implement phishing-resistant MFA, CISA recommends using number matching to mitigate MFA fatigue. Although number matching is not as strong as phishing-resistant MFA, it is one of best interim mitigation for organizations who may not immediately be able to implement phishing-resistant MFA. … CISA recommends users and organizations see CISA fact sheets Implementing Phishing-Resistant MFA and Implementing Number Matching in MFA Applications. Visit CISA.gov/MFA for more information on MFA, including an infographic of the hierarchy of MFA options. CISA, October 31, 2022


