This week’s essential cybersecurity and privacy news for the cyber-aware and the cyber-concerned. Designed to educate, support, and advocate.
Stan’s Top of the News
The Top of the News this week is personal. It’s personal in part because I’m interviewed. It’s also personal because the victim is a long-time colleague. … The story is important beyond the purely personal. It illustrates our deepest cybersecurity challenge: How the security of our technology – and how we use it – has more holes than Swiss cheese. … Hole 1: Because of lax controls by Spectrum in changing phones, cybercriminals were able to execute a SIM-swap attack and take over Jeff’s phone. … Hole 2: Now, armed with the phone, the cybercriminals were able to steal money from his bank because of a hole in the MFA / 2FA procedures Bank of America uses to authenticate customers. … Bank of America uses SMS-texting as its MFA when it authenticates customers. Readers of this Newsletter know that SMS-texting is a weak form of MFA. Stronger alternatives exist, including Authenticators from Google and Microsoft. … An easy way to close hole 2 is to make a bank responsible for any losses unless it offers its customers strong MFA. … And we can go a long way to closing Hole 1 if the carriers would make it harder for cyber criminals to execute SIM-swap attacks. In a perfect world, the carriers would recognize the problem and take the initiative to provide their customers a PIN to be used when changing phones. In our less-than-perfect world, I suspect it will take regulations to close this hole. Great thanks to NBC Universal and producer Christine Roher for covering this story.
- Man lost $21,000 in SIM swap scam. Crooks hijacked his cellphone number and then stole money from his bank account using two-factor authentication in a scam the FBI says is taking millions from people. Here’s how to protect yourself.
Small and Midsize Organizations. Take your security to the next level. Apply Now! If you’re a small business, nonprofit, or IT / MSP in the greater Los Angeles area, apply NOW for LA Cybersecure, a pilot program with coaching and guidance that costs less than two cups of coffee a week. https://securethevillage.org/la-cybersecure-pilot/ The LA Cybersecure Pilot Program is funded by a grant from the Center for Internet Security (CIS) Alan Paller Laureate Program.
Family Protection Newsletter: Did you know we created the Family Protection Newsletter for non-cyber experts? For your parents, friends, those who need to protect themselves in a digital world. Sign up or share with a friend! Click here to learn more and quickly add to your free subscription!
How Hackable Are You? Take our test. Find out how hackable you are and download our free updated 13-step guide.
- How Hackable Are You? Think your defenses are strong. Find out as SecureTheVillage tests you on five basics. Please take our short test as your answers will help you and guide us to improve community safety.
Please Support SecureTheVillage.
- We need your help if we’re to build a world of CyberGuardians TM. Please donate to SecureTheVillage. Thank you. It takes a village to secure the village. TM.
Cybersecurity Nonprofit of the Week … Sightline Security
Our kudos this week to Sightline Security, a nonprofit that helps nonprofits secure and protect their critical information. Sightline’s mission is to equip, empower, and support nonprofits to navigate and embed cybersecurity into their organizations with confidence. Kudos to Sightline Security for their cyber support to the vital under-served nonprofit community. Sightline Security is playing a major role in our LA Cybersecurity Pilot Program. Like SecureTheVillage, Sightline Security is a fellow-member of Nonprofit Cyber.
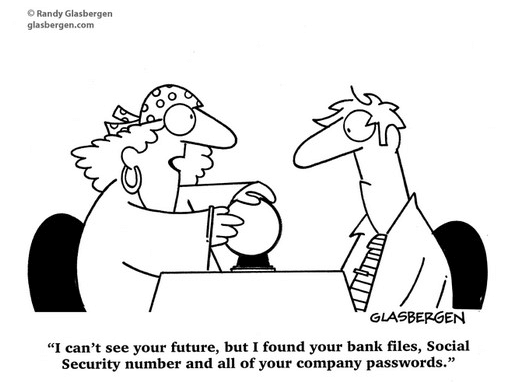
Cyber Humor
Section 2 – Let’s Be Careful Out There. And Let’s Help Others Who Aren’t Yet Cyber-Aware.
A sad cybercrime story. An 81 year old scam victim is in jail. An innocent Uber driver is dead.
- What we know about the shooting of an Uber driver in Ohio and the scam surrounding it: It was a common scam that ended with an uncommon outcome, tragically in an Ohio driveway. … William J. Brock fatally shot an Uber driver because he wrongly assumed she was part of a scheme to extract $12,000 in supposed bond money for a relative, authorities said this week. Lo-Letha Hall was a victim of the same con, summoned by the grifters to Brock’s house to retrieve a purported package for delivery. … Brock later told investigators he believed Hall arrived to get the money the scammers wanted. … He is now facing murder charges, to which he’s pleaded not guilty. Hall’s family is grieving. And Uber is helping investigators to try to catch whoever was behind the attempted swindle.
From AARP comes a scam quiz. Will you pass?
- How Much Do You Know About P2P Payment and Cryptocurrency Scams: Take this quiz to see if you are savvy about tools like Zelle and Venmo, and why criminals Love them
Section 3 – Cybersecurity and Privacy News for the Cyber-Concerned.
Things are getting hot in national cybersecurity. Russia and China pose continued threat to our critical infrastructure. One of the Nation’s leading information security defenders, the MITRE Corporation announces they’ve suffered an incident.
- Chinese Government Poses ‘Broad and Unrelenting’ Threat to U.S. Critical Infrastructure, FBI Director Says: Partnerships, joint operations, and private sector vigilance can help us fight back. … FBI Director Christopher Wray on April 18 warned national security and intelligence experts, as well as students, that risks the government of China poses to U.S. national and economic security are “upon us now”—and that U.S. critical infrastructure is a prime target. … “The PRC [People’s Republic of China] has made it clear that it considers every sector that makes our society run as fair game in its bid to dominate on the world stage, and that its plan is to land low blows against civilian infrastructure to try to induce panic and break America’s will to resist,” he said in remarks at the Vanderbilt Summit on Modern Conflict and Emerging Threats in Nashville. … But he suggested that partnerships with both the private sector and academia can be powerful tools in the quest to neutralize this threat.
- Russia-linked hacking group suspected of carrying out cyberattack on Texas water facility, cybersecurity firm says: A hacking group with ties to the Russian government is suspected of carrying out a cyberattack in January that caused a tank at a Texas water facility to overflow, experts from US cybersecurity firm Mandiant said Wednesday. … The hack in the small town of Muleshoe, in north Texas, coincided with at least two other towns in north Texas taking precautionary defensive measures after detecting suspicious cyber activity on their networks, town officials told CNN. The FBI has been investigating the hacking activity, one of the officials said. … The attack was a rare example of hackers using access to sensitive industrial equipment to disrupt regular operations at a US water facility, following a separate cyberattack last November on a Pennsylvania water plant that US officials blamed on Iran. … The cyber incidents in Texas also help explain a rare public appeal that US national security adviser Jake Sullivan made last month to state officials and water authorities to shore up their cyber defenses. Cyberattacks are hitting water and wastewater systems “throughout the United States” and state governments and water facilities must improve their defenses against the threat, Sullivan said in a joint letter with the Environmental Protection Agency chief to state officials.
- Biden admin, U.S. ports prep for cyberattacks as nationwide infrastructure is targeted: U.S. physical infrastructure is increasingly the target of hacks, with Google’s cybersecurity firm Mandiant releasing a report Wednesday teasing out links between Russian hackers and a January attack on a water filtration plant in a small Texas town. … The nation’s largest ports are also at risk, and Biden administration cybersecurity officers and key port executives held a call on Wednesday to discuss security issues, including the Chinese-made cranes that have received government scrutiny this year. … “More needs to be done across the ports, and supply chain,” said Gene Seroka, executive director for the Port of Los Angeles, who noted that in 2023 the port stopped 750 million hacking attempts.
- Emergency services a likely target for cyberattacks, warns DHS: Ransomware attacks in particular threaten to disrupt services. … Calling 911 is meant to save lives. But the emergency service, and others like it, are also viewed as ripe targets for criminally minded cyber-attackers, according to a new federal assessment – and any vulnerability in those critical networks can expose victims to a multitude of dangerous ripple effects. … The analysis, compiled by the Department of Homeland Security (DHS) and obtained by ABC News, outlines concerns that the Emergency Service Sector can be exploited and mined for sensitive data, in turn hampering medical and law enforcement services and posing an ongoing threat to personal information and public safety.
- MITRE Response to Cyber Attack in One of Its R&D Networks: McLean, Va., April 19, 2024 – MITRE today disclosed that despite its fervent commitment to safeguarding its digital assets, it experienced a breach that underscores the nature of modern cyber threats. After detecting suspicious activity on its Networked Experimentation, Research, and Virtualization Environment (NERVE), a collaborative network used for research, development, and prototyping, compromise by a foreign nation-state threat actor was confirmed. … To offer learnings from its experience, MITRE has published initial details about the incident via the Center for Threat-Informed Defense, found here
Kudos to law enforcement for their take-down of a major phishing service.
- LabHost phishing service with 40,000 domains disrupted, 37 arrested: The LabHost phishing-as-a-service (PhaaS) platform has been disrupted in a year-long global law enforcement operation that compromised the infrastructure and arrested 37 suspects, among them the original developer. … The phishing platform launched in 2021 and enabled cybercriminals paying a monthly subscription fee to launch effective attacks using a variety of phishing kits for banks and services in North America. … The recent international law enforcement operation coordinated by Europol started roughly a year ago and involved police forces and special investigators in 19 countries, as well as partners from the private sector like Microsoft, Trend Micro, Chainalysis, Intel 471, and The Shadowserver Foundation. … “The investigation uncovered at least 40 000 phishing domains linked to LabHost, which had some 10 000 users worldwide,” reads Europol’s announcement.
Two FTC stories this make the cybersecurity news this week.
- FTC Fines Mental Health Startup Cerebral $7 Million for Major Privacy Violations: The U.S. Federal Trade Commission (FTC) has ordered mental telehealth company Cerebral from using or disclosing personal medical data for advertising purposes. … It has also been fined more than $7 million over charges that it revealed users’ sensitive personal health information and other data to third-parties for advertising purposes and failed to honor its easy cancellation policies. … “Cerebral and its former CEO, Kyle Robertson, repeatedly broke their privacy promises to consumers and misled them about the company’s cancellation policies,” the FTC said in a press statement. … While claiming to offer “safe, secure, and discreet” services in order to get consumers to sign up and provide their data, the company, FTC alleged, did not clearly disclose that the information would be shared with third-parties for advertising.
- MGM Resorts sues to halt probe that began after a massive hack prompted a front-desk clerk to ask the FTC chair for her credit card number: MGM Resorts International sued the Federal Trade Commission to stop an investigation into how it dealt with a cybersecurity attack last year. … The company said the investigation deprives it of its fundamental due process rights and that FTC Chair Lina Khan should recuse herself from the case, according to the lawsuit filed in Washington federal court Monday.
Colorado passes a first-of-its-kind privacy law.
- Your Brain Waves Are Up for Sale. A New Law Wants to Change That: In a first, a Colorado law extends privacy rights to the neural data increasingly coveted by technology companies. … The law takes aim at consumer-level brain technologies. Unlike sensitive patient data obtained from medical devices in clinical settings, which are protected by federal health law, the data surrounding consumer neurotechnologies go largely unregulated, Mr. Genser said. That loophole means that companies can harvest vast troves of highly sensitive brain data, sometimes for an unspecified number of years, and share or sell the information to third parties.
The ongoing UnitedHealth / Change Healthcare debacle continues to play out.
- UnitedHealth to take up to $1.6 billion hit this year from Change hack: The hack at Change, a provider of health care billing and data systems and a key node in the U.S. health care system, disrupted payments to doctors and health care facilities nationwide for a month.
- Change Healthcare stolen patient data leaked by ransomware gang: An extortion group has published a portion of what it says are the private and sensitive patient records on millions of Americans stolen during the ransomware attack on Change Healthcare in February. … On Monday, a new ransomware and extortion gang that calls itself RansomHub published several files on its dark web leak site containing personal information about patients across different documents, including billing files, insurance records and medical information. … Some of the files, which TechCrunch has seen, also contain contracts and agreements between Change Healthcare and its partners. … RansomHub threatened to sell the data to the highest bidder unless Change Healthcare pays a ransom. … This is the second group to demand a ransom payment to prevent the release of stolen patient data in as many months.
Two new cyber-warnings. Last Pass warns of a phishing campaign targeting their users. And researchers find dozens of fake E-ZPass sending smishing (SMS text) messages to unsuspecting travelers.
- Cybercriminals pose as LastPass staff to hack password vaults: LastPass is warning of a malicious campaign targeting its users with the CryptoChameleon phishing kit that is associated with cryptocurrency theft. … According to researchers at mobile security company Lookout, campaigns using this phishing kit also targeted cryptocurrency platforms Binance, Coinbase, Kraken, and Gemini, using pages that impersonated Okta, Gmail, iCloud, Outlook, Twitter, Yahoo, and AOL.
- Researchers find dozens of fake E-ZPass toll websites after FBI warning: Cybersecurity researchers have found almost 30 phishing websites spoofing the electronic toll collection service E-ZPass following an FBI warning last week. … The FBI said in an alert that since early March the Internet Crime Complaint Center (IC3) has received over 2,000 complaints reporting smishing texts impersonating road toll collection services from at least three states.
This week in cybercrime.
- Omni Hotels Says Personal Information Stolen in Ransomware Attack: Omni Hotels says customer information was compromised in a cyberattack claimed by the Daixin Team ransomware group. … The incident, which occurred on March 29, prompted Omni to shut down systems, which led to disruptions across the company’s hotels and resorts. By April 8, Omni had restored systems across all properties. … While Omni did not provide details on the type of cyberattack it fell victim to, the Daixin Team ransomware group has added the hotel chain to its leak site, claiming the theft of all records pertaining to Omni’s visitors from 2017 onwards.
- Hackers are threatening to leak World-Check, a huge sanctions and financial crimes watchlist:A financially motivated criminal hacking group says it has stolen a confidential database containing millions of records that companies use for screening potential customers for links to sanctions and financial crime. ….The hackers, which call themselves GhostR, said they stole 5.3 million records from the World-Check screening database in March and are threatening to publish the data online.
- Frontier Communications Shuts Down Systems Following Cyberattack: Telecommunications giant Frontier Communications on Thursday informed the Securities and Exchange Commission (SEC) that certain systems were shut down following a cyberattack. … The incident, the company said in a regulatory filing with the SEC, was identified on April 14, when a third-party “gained unauthorized access to portions of its information technology environment”.
- United Nations agency investigates ransomware attack, data theft: The United Nations Development Programme (UNDP) is investigating a cyberattack after threat actors breached its IT systems to steal human resources data. … UNDP, the UN’s global development network, works in over 170 countries and territories and relies on donations from UN member states and private sector/multilateral organizations to help eradicate poverty and fight inequality and exclusion.
Section 4 – Securing the Corporate Technology Infrastructure.
If you have Palo Alto equipment, patch now.
- Palo Alto Networks releases fixes for zero-day as attackers swarm VPN vulnerability: Palo Alto Networks has released fixes for a zero-day vulnerability affecting its GlobalProtect VPN product that is being targeted following its disclosure last week. … Hotfixes for the vulnerability — labeled CVE-2024-3400 — were published on Sunday, as promised in an urgent notice about the bug on Friday morning. The zero-day carries the highest severity score possible of 10. … Security company Volexity, which Palo Alto credited with discovering the bug, said it “is highly likely” the attacker behind the exploitation is a state-backed threat actor and that the first attacks date back to at least March 26.


