This week’s essential cybersecurity and privacy news for the cyber-aware and the cyber-concerned. Designed to educate, support, and advocate.
Stan’s Top of the News
This week’s Top of the News celebrates the organizations in SecureTheVillage’s LA Cybersecure Program. Kudos to our first business / nonprofit cohort for completing the customized information security assessment. And great thanks to Sightline Security and their founder / President Kelley Misata for their work to get our first cohort off to such a great start. Cohort members are now completing the Cyber Readiness Program of the Cyber Readiness Institute. The village securing the village.
- First Cohort of LA Business and Nonprofit Participants in SecureTheVillage Program Receive Customized Cybersecurity Roadmaps from Sightline Security. SecureTheVillage’s innovative LA Cybersecure Program Provides Education, Tools, Coaching, and Community to Empower Small Businesses and Nonprofits to Defend Themselves in a way that, until now, only Big Businesses have Been Able to Achieve.
Small and Midsize Organizations. Take your security to the next level. Apply Now! If you’re a small business, nonprofit, or IT / MSP in the greater Los Angeles area, apply NOW for LA Cybersecure, a program with coaching and guidance that costs less than two cups of coffee a week. https://securethevillage.org/la-cybersecure-pilot/ The LA Cybersecure Program is funded in part by a grant from the Center for Internet Security (CIS) Alan Paller Laureate Program.
Family Protection Newsletter: Did you know we created the Family Protection Newsletter for non-cyber experts? For your parents, friends, those who need to protect themselves in a digital world. Sign up or share with a friend! Click here to learn more and quickly add to your free subscription!
How Hackable Are You? Take our test. Find out how hackable you are and download our free updated 13-step guide.
- How Hackable Are You? Think your defenses are strong. Find out as SecureTheVillage tests you on five basics. Please take our short test as your answers will help you and guide us to improve community safety.
Cybersecurity Nonprofit of the Week … Cyber Readiness Institute
Our kudos this week to the Cyber Readiness Institute (CRI) and the great work they do helping our medium-size and smaller organizations manage their information security challenges. CRI’s Cyber Readiness Program helps organizations protect their data, employees, vendors, and customers. This free, online program is designed to help small and medium-sized enterprises become more secure against today’s most common cyber vulnerabilities. Their free Cyber Leader Certification Program is a personal professional credential for those who have completed the Cyber Readiness Program. Both are highly recommended. The Cyber Readiness Institute plays a major role in LA Cybersecure. Like SecureTheVillage, the Cyber Readiness Institute is a fellow-member of Nonprofit Cyber. Dr. Stahl is a proud member of CRI’s Small Business Advisory Council.
Please Support SecureTheVillage.
- We need your help if we’re to build a world of CyberGuardians TM. Please donate to SecureTheVillage. Thank you. It takes a village to secure the village. TM.
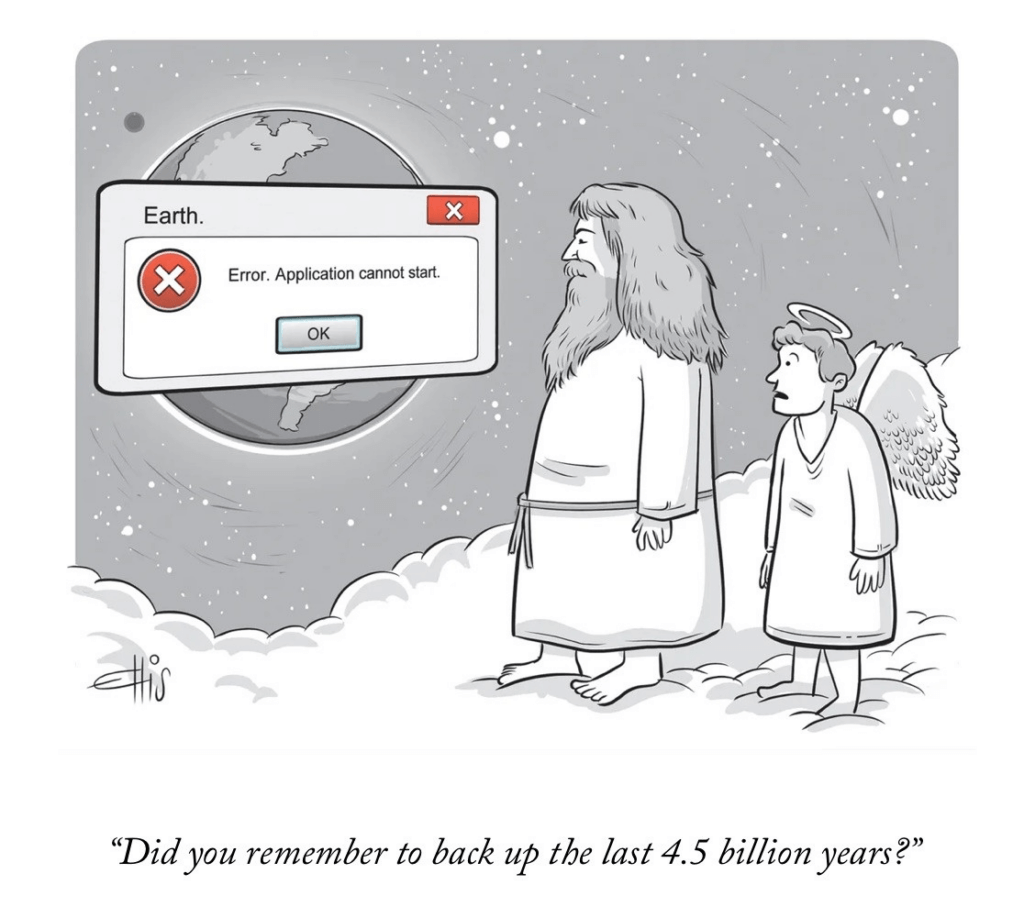
Cyber Humor
Section 2 – Let’s Be Careful Out There. And Let’s Help Others Who Aren’t Yet Cyber-Aware.
Let’s be careful out there. And let’s help others.
- Financial Institutions Report $27 Billion in Elder Financial Exploitation Suspicious Activity in One-Year Period: The U.S. Department of the Treasury’s Financial Crimes Enforcement Network (FinCEN) issued a Financial Trend Analysis today focusing on patterns and trends identified in Bank Secrecy Act (BSA) data linked to Elder Financial Exploitation (EFE), or the illegal or improper use of an older adult’s funds, property, or assets. FinCEN examined BSA reports filed between June 15, 2022 and June 15, 2023 that either used the key term referenced in FinCEN’s June 2022 EFE Advisory or checked “Elder Financial Exploitation” as a suspicious activity type. This amounted to 155,415 filings over this period indicating roughly $27 billion in EFE-related suspicious activity.
- New Brokewell malware takes over Android devices, steals data: Security researchers have discovered a new Android banking trojan they named Brokewell that can capture every event on the device, from touches and information displayed to text input and the applications the user launches. … The malware is delivered through a fake Google Chrome update that is shown while using the web browser. Brokewell is under active development and features a mix of extensive device takeover and remote control capabilities. … To protect yourself from Android malware infections, avoid downloading apps or app updates from outside Google Play and ensure that Play Protect is active on your device at all times. … Google has confirmed to BleepingComputer that Google Play Protect automatically protects users against known versions of this malware
Section 3 – Cybersecurity and Privacy News for the Cyber-Concerned.
I doubt that the sky is falling. But with geopolitics heating up, these could be harbingers of some serious cracks.
- DHS asked to consider potentially ‘devastating’ impact of hacks on rural water systems: A bipartisan pair of House lawmakers is pressing for more details about the breach of a water facility in Texas that was carried out by a group with suspected ties to the Russian government. … In an April 23 letter, Reps. Pat Fallon (R-TX) and Ruben Gallego (D-AZ) asked Homeland Security Secretary Alejandro Mayorkas for a briefing on the January incident, which caused a tank at a water facility in Muleshoe, Texas, to overflow. The Google-owned security firm Mandiant later issued a report that said the group purportedly behind the attack, the Cyber Army of Russia, is linked to a Russian state actor, Sandworm — which has gained global notoriety for its past, and present, digital assaults on Ukraine. … The group has since claimed credit for a cyberattack on an Indiana water plant.
- China Infiltrates US Critical Infrastructure in Ramp-up to Conflict: Threat actors linked to the People’s Republic of China, such as Volt Typhoon, continue to “pre-position” themselves in the critical infrastructure of the United States, according to military and law enforcement officials. … The People’s Republic of China is accelerating the development of its military capabilities — including cyber operations — because it believes it will need to deter and confront the United States, US officials said yesterday. … since last May it has been recognized as a threat to critical infrastructure and military bases. In fact, it’s seen as such a clear threat that it was recently disrupted by the US government and private sector companies, officials said this week.
- Chinese, Russian espionage campaigns increasingly targeting edge devices: Chinese and Russian hackers have turned their focus to edge devices — like VPN appliances, firewalls, routers and Internet of Things (IoT) tools — amid a startling increase in espionage attacks, according to Google security firm Mandiant. … The company published the findings as part of its annual report on cyber investigations Mandiant was involved in last year. … Charles Carmakal, chief technology officer at Mandiant, told Recorded Future News that there has been a significant shift in the tactics used by espionage hackers based in China and Russia. For years, incident responders saw the same playbook — employees would be targeted with malicious phishing emails containing malware that would give hackers a foothold into the system. … But last year, Carmakal said the most common way into companies was by finding a zero-day vulnerability in frequently deployed devices. … “I think there is a very deliberate focus by the Chinese government to start to identify zero day vulnerabilities and develop malware for edge devices. And something that might surprise people is that we see Chinese espionage operators using less and less malware today on Windows computers than ever before,” he said. … “The reason for that is because [Endpoint Detection and Response] solutions are getting really good now. If you deploy malware on a Windows computer, the chances of you getting caught are much higher than if you deployed the same malware on a VPN appliance.”
An in-depth look by The New York Times on “Scam World.”
- Welcome to Scam World: You open your eyes and grope for your phone. You check your inbox and discover dozens of spam emails that made it past the filter. … Tapping over to Instagram, you find a request for a supposed brand collaboration in your DMs. Your WhatsApp notifications, meanwhile, consist solely of strangers asking you to invest in a cryptocurrency exchange. … While scrolling social media on your lunch break, you see Tom Hanks promoting a dental plan and Taylor Swift peddling a cookware giveaway. (Or at least that’s what seems to be going on.) … On the way home from work, you receive a text alert from FedEx, with a tracking number and a link to update your delivery preferences — except you don’t remember any pending shipments to your home. … Should you click the link? Pick up that call? Pursue that job opportunity? Is the person who texted you “hey” just now from a number you don’t recognize someone you actually know? … Welcome to Scam World, the seedy layer just beneath the world we live in every day. It’s cluttered with these bogus text messages, spam calls and phishing attempts. … In Scam World, any engagement with a stranger is a risk. Thanks to spoofing, for example, which cloaks the identity and location of the computer or phone being used, a call could be from a helpful customer service representative or a cyber criminal pretending to be one.
Privacy Victory: Students fight back and win against overly aggressive school district.
- ‘Unapologetically loud’: How student journalists fought a Kansas district over spyware and won: LAWRENCE — When Lawrence Public Schools deployed spyware last fall, district officials said it would help them respond to a growing mental health crisis by monitoring students’ correspondence, photos, classwork and files. … But student journalists were alarmed by the First Amendment problems inherent with the district’s implementation of the surveillance program, made by Gaggle. … As district officials dismissed the students’ concerns, they gathered evidence
More privacy work to do. Much more!!!
- How G.M. Tricked Millions of Drivers Into Being Spied On (Including Me): Automakers have been selling data about the driving behavior of millions of people to the insurance industry. In the case of General Motors, affected drivers weren’t informed, and the tracking led insurance companies to charge some of them more for premiums. I’m the reporter who broke the story. I recently discovered that I’m among the drivers who was spied on.
- Health insurance giant Kaiser will notify millions of a data breach after sharing patients’ data with advertisers: U.S. health conglomerate Kaiser is notifying millions of current and former members of a data breach after confirming it shared patients’ information with third-party advertisers, including Google, Microsoft and X (formerly Twitter).
- Dating apps are collecting more of your information than you think: Research from the Mozilla Foundation says these apps are getting ‘thirstier’ for our data: For people in search of lasting relationships on dating apps, there’s nothing quite like matching with someone who wants to know the real you. … That kind of curiosity could signal keen interest, or at the very least, a certain social grace. But those potential partners aren’t the only curious ones in the mix: The apps you may have used to meet them might be just as hungry for your personal information. … So say researchers at the Mozilla Foundation’s Privacy Not Included project, who updated reviews of 25 of the most popular dating apps out there based on their user privacy practices, data breach track records and more. The result? 22 of those apps — including popular options like Tinder, Grindr, OkCupid, Hinge and Bumble — received the team’s “Privacy Not Included” warning label.
Congressional factions and the White House pass legislation. CISA and the FBI work together on alerting system. Government working together protecting people. This is the way the system should work. Kudos and let’s see more of it.
- More than 800 vulnerabilities resolved through CISA ransomware notification pilot: A pilot program to proactively notify organizations their devices may be vulnerable to ransomware attacks is already bearing fruit, the Cybersecurity and Infrastructure Security Agency said Thursday. … The Ransomware Vulnerability Warning Pilot was unveiled in January 2023 as a program designed to “identify organizations with internet-accessible vulnerabilities commonly associated with known ransomware actors.” … The program was mandated under the cyber incident reporting legislation President Joe Biden signed into law in 2022. It is run by the Joint Ransomware Task Force, co-led by CISA and the FBI. … CISA said it made 1,754 notifications last year to organizations with internet-exposed devices vulnerable to attack. Of those, 852 were “patched, implemented a compensating control, or taken offline after notification from CISA.”
Coalition’s 2024 Cyber Claims Report shows claims rising in frequency and severity. Phishing and remote access weaknesses highlighted.
- 56% of cyber insurance claims originate in the email inbox: 56% of all 2023 claims were a result of funds transfer fraud (FTF) or business email compromise (BEC), highlighting the importance of email security as a critical aspect of cyber risk management, according to Coalition. … “We also found that policyholders using internet-exposed remote desktop protocol were 2.5 times more likely to experience a claim,” said Shelley Ma, Incident Response Lead at Coalition’s affiliate, Coalition Incident Response. … Overall claims frequency increased 13% year-over-year (YoY), and overall claims severity increased 10% YoY, resulting in an average loss of $100,000. Claims frequency increased across all revenue bands, with businesses between $25 million and $100 million in revenue seeing the sharpest spike (a 32% YoY increase).
Ransomware means destroyed businesses and broken lives. Kudos to the Ransomware Task Force, a program of the Institute for Security and Technology (IST) for their work on ransomware. The Institute was our Cybersecurity Nonprofit of the Week in February. They are a fellow member of Nonprofit Cyber.
- Ransomware payments surpass $1 billion in 2023, report finds: The rate and scale of ransomware attacks have increased significantly over the past few years, with ransom payments surpassing $1 billion for the first time ever in 2023, according to a new report released Wednesday by the Ransomware Task Force (RTF). … The 36-page April 2024 progress report “Doubling Down” highlights the ongoing threat of ransomware despite concerted efforts by government agencies, civil society, the technical community, and the private sector to combat it. … The Institute for Security and Technology (IST), a California-based think tank behind the Ransomware Task Force report, reviews the recommendations it made in a 2021 RTF report “Combating Ransomware: A Comprehensive Framework for Action,” noting that while some progress has been made, major challenges remain.
This Week in Cybercrime, including the latest updates on UnitedHealth breach.
- UnitedHealth says ‘substantial proportion’ of Americans’ information hit by cyberattack, confirms ransom payment: The cyberattack on Change Healthcare in February targeted the data of “a substantial proportion of people in America,” UnitedHealth Group (UHG) said this week, with the company confirming it paid a ransom in an effort to protect patient information. … “Based on initial targeted data sampling to date, the company has found files containing protected health information (PHI) or personally identifiable information (PII), which could cover a substantial proportion of people in America,” UHG said in an update on Monday regarding the attack on its subsidiary. … Due to the scope of attack, UHG said it will likely take “several months” to identify and notify customers who were impacted. The company has launched a website where customers can get information and has set up call centers to offer “offer free credit monitoring and identity theft protections for two years” to affected individuals.
- Sweden’s liquor shelves to run empty this week due to ransomware attack: A ransomware attack on a Swedish logistics company has prompted warnings from the country’s sole liquor retailer that its top shelves in stores around the country may be empty by the end of the week.
- Anti-Trump PAC Lincoln Project scammed for $35,000 after vendor email hack: The anti-Donald Trump super PAC Lincoln Project lost $35,000 to a business email compromise (BEC) scam in February. … Spokesman Greg Minchak confirmed the incident to the news site RawStory. … Minchak described a classic BEC incident: “A vendor’s email was hacked, with the hackers producing authentic-looking invoices that were sent from our vendor’s legitimate email account,” he said. “The hack affected multiple clients of the vendor, including Lincoln Project.”
- Plasma donation company Octapharma slowly reopening as BlackSuit gang claims attack: The plasma donation company Octapharma has begun to reopen some of its 180 centers around the world following a ransomware attack that forced it to shut down operations for nearly a week.
Section 4 – Securing the Corporate Technology Infrastructure.
Patch now!!!
- CISA Warns of Windows Print Spooler Flaw After Microsoft Sees Russian Exploitation: The US cybersecurity agency CISA on Tuesday added a two-year-old Windows Print Spooler flaw to its Known Exploited Vulnerabilities (KEV) catalog. … Tracked as CVE-2022-38028 (CVSS score of 7.8) and addressed as part of Microsoft’s October 2022 Patch Tuesday updates, the issue can be exploited to gain System privileges on a vulnerable machine.
- Cisco Releases Security Updates Addressing ArcaneDoor, Vulnerabilities in Cisco Firewall Platforms: Today, Cisco released security updates to address ArcaneDoor—exploitation of Cisco Adaptive Security Appliances (ASA) devices and Cisco Firepower Threat Defense (FTD) software. A cyber threat actor could exploit vulnerabilities (CVE-2024-20353, CVE-2024-20359, CVE-2024-20358) to take control of an affected system. … Cisco has reported active exploitation of CVE 2024-20353 and CVE-2024-20359 and CISA has added these vulnerabilities to its Known Exploited Vulnerabilities Catalog.
Act now to block Okta attacks.
- Okta warns of “unprecedented” credential stuffing attacks on customers: Okta warns of an “unprecedented” spike in credential stuffing attacks targeting its identity and access management solutions, with some customer accounts breached in the attacks. … In an advisory today, Okta says the attacks seem to originate from the same infrastructure used in the brute-force and password-spraying attacks previously reported by Cisco Talos [1, 2].


