This week’s essential cybersecurity and privacy news for the cyber-aware and the cyber-concerned. Designed to educate, support, and advocate.
Stan’s Top of the News
Top of the News this week. Big kudos to the National Institute of Standards and Technology (NIST) with their release of the Cyber Security Framework 2.0 (DRAFT). Of great importance is the creation of a new 6th function: Governance that includes risk management strategy; cybersecurity supply chain risk management; roles, responsibilities, and authorities; policies, processes, and procedures; and oversight. There is also a new emphasis on cybersecurity supply chain risk management. New guidance has been provided with Implementation Examples to provide notional examples of action-oriented processes to achieve CSF Subcategories. Continuous improvement has been emphasized through a new Improvement Category in the Identify Function, as well as improvements in guidance on developing and updating Profiles and action plans. All in all, it’s an excellent draft and we look forward to the final 2.0 Framework early in 2024. In the meantime, organizations should begin to use the draft framework to strengthen their cybersecurity posture.
- NIST Cyber Security Framework 2.0 (DRAFT): This is the public draft of the NIST Cybersecurity Framework (CSF or Framework) 2.0. The Framework has been used widely to reduce cybersecurity risks since its initial publication in 2014. Many organizations have told NIST that CSF 1.1 remains an effective framework for addressing cybersecurity risks. There is also widespread agreement that changes are warranted to address current and future cybersecurity challenges and to make it easier for organizations to use the Framework. NIST is working with the community to ensure that CSF 2.0 is effective for the future while fulfilling the CSF’s original goals and objectives. Comments are open until November 5, 2023.
New. Family Protection Newsletter: Did you know we created the Family Protection Newsletter, for non-cyber experts? For your parents, friends, those who need to protect themselves in a digital world. We feature info on how to freeze your credit and what ‘marriage scams’ are in Edition 1. Sign up or share with a friend! Click here to learn more and quickly add to your free subscription!
How Hackable Are You? Take our quiz. Find out how hackable you are and download our free 8-step guide.
- How Hackable Are You? Think your defenses are strong. Find out as SecureTheVillage tests you on five basics. Please take our short quiz as your answers will help you and guide us to improve community safety.
Upcoming events. Please join us.
- Cybersecurity Threat Briefing – Meeting Today’s Cyber Crime Challenges, with Special Guest Speaker SSA Michael Sohn, FBI. Co-hosted with Department Financial Protection & Innovation. Friday, August 18, 8:30 am – 10:00 am PT
- Los Angeles Cybersecurity Workforce Coalition: The monthly meeting of the workforce coalition, Tue, September 5, 1:00 pm – 2:00 pm PT.
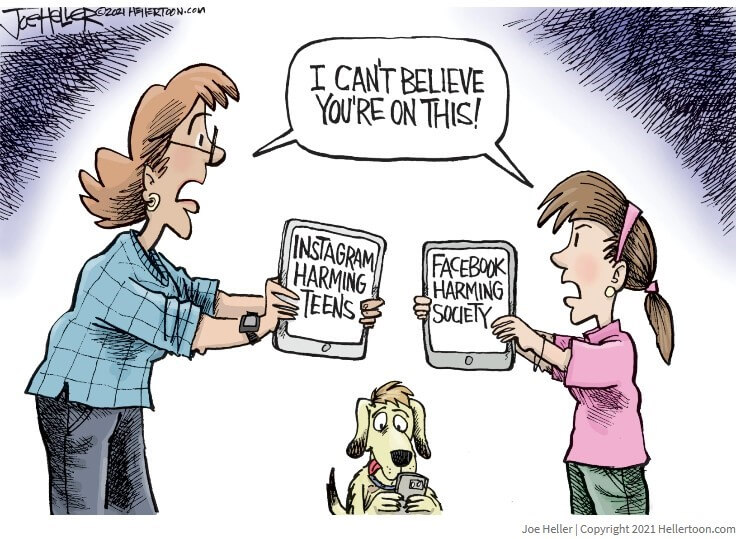
Cyber Humor
Cybersecurity Nonprofit of the Week … The Institute for Security and Technology.
- Kudos this week to The Institute for Security and Technology and their Ransomware Task Force (RTF). The Task Force aims to equip businesses, organizations, and governments of all sizes to prepare for ransomware attacks, effectively respond, and quickly recover. The Task Force has published the Cyber Incident Reporting Framework and the Blueprint for Ransomware Defenserepresenting a set of foundational and actionable safeguards derived from the Center for Internet Security’s Critical Security Controls. Like SecureTheVillage, the Institute is a member of Nonprofit Cyber, a coalition of implementation-focused cybersecurity nonprofits.
- IST needs our help to help them help us. They have submitted a panel to #SXSW2024 “Crypto’s Still King for Ransomware. What Can We Do About It?” #RansomwareTaskForce researcher Zoë Brammer will present her work on mapping the ransomware payment ecosystem and conducting a mini-pilot on threat actor behavior. A panel featuring IST’s Megan Stifel, Jason Kikta, and Steven M. Kelly, CISSP will follow, where IST experts will discuss how we can best disrupt ransomware’s profitability. Panel selection is by vote. To vote, visit panelpicker.sxsw.com/vote to sign in or create an account. Find their panel and click “vote up!”
Live on Cyber with Dr. Stan Stahl – Live on LinkedIn and Your Favorite Podcast Platform

Closing the Cybersecurity Workforce Gap: (Video) (Podcast): With 300,000+ cybersecurity roles unfilled nationwide, we’re fighting a losing battle against well-funded, highly skilled cybercrime operations. The Biden-Harris Administration’s ground-breaking National Cyber Workforce and Education Strategy (NCWES) aims to combat the onslaught. And more than filling roles; it’s about empowering every American in our digital realm. On Episode 30, “The Top 3 in America’s Battle Plan Against Cybercrime,” Stan and Julie break down the NCWES, its game-changing implications, and the pressing call for cyber-vigilance among organizations and individuals alike.
Section 2 – Let’s Be Careful Out There. And Let’s Help Others Who Aren’t Yet Cyber-Aware.
Let’s be careful out there. Vultures are everywhere.
- Are you smarter than a scammer? Play this game: In 2022, 2.4 million Americans reported to the Federal Trade Commission that they were victims of a scam, losing nearly $8.8 billion, a 30 percent increase from 2021. Most reported scam attempts come via email, followed by phone calls and text messages, and the most popular types of scams are people impersonating businesses or government agencies. … Learn more about how to keep yourself safe by testing your instincts below and guessing whether each instance is a scam, using real-life examples. We’ll also give some helpful advice on how to keep yourself and loved ones safe.
- New scam targeting Venmo users steals log-in information: It’s never been easier to make or take a payment. With a few taps on a phone screen, money can move through peer-to-peer payment apps like Cash App, Zelle and Venmo. … Unfortunately, these easy exchanges make it easier for fraudsters and hackers to carry out their own money-making schemes. … The victims report receiving a text message that appears to come from Venmo, saying a sign-in to the user’s account was detected in a different city. The message goes on to say, “Not you? Tap the link to sign in now.” But that link leads to a fake website, made to look like Venmo’s, and asks the user to log into their Venmo account. If they do, the scammer then steals their login information, and has full access to their account. … Any time you receive a message or email claiming to come from a bank or payment app, don’t click on the link or call the phone number they provide. Go directly to the source, instead.
The App Danger Project: Support to parents concerned about the safety of their children’s apps.
- Amid Sextortion’s Rise, Computer Scientists Tap A.I. to Identify Risky Apps: Researchers who found that a fifth of social networking apps have received multiple user complaints about sexual exploitation have launched a website to help parents vet apps. … Almost weekly, Brian Levine, a computer scientist at the University of Massachusetts Amherst, is asked the same question by his 14-year-old daughter: Can I download this app? … Mr. Levine responds by scanning hundreds of customer reviews in the App Store for allegations of harassment or child sexual abuse. The manual and arbitrary process has made him wonder why more resources aren’t available to help parents make quick decisions about apps. … Over the past two years, Mr. Levine has sought to help parents by designing a computational model that assesses customers’ reviews of social apps. Using artificial intelligence to evaluate the context of reviews with words such as “child porn” or “pedo,” he and a team of researchers have built a searchable website called the App Danger Project, which provides clear guidance on the safety of social networking apps.
Self-defense: Plan to update Chrome weekly. As we’ve discussed repeatedly, one of the most Important things you can do to stay cyber-safe is to keep your computers, smartphones, and other devices patched and updated. To help our readers keep up with this, we’ve been publishing our Weekend Patch Report every Sunday since 2008.
- Chrome Will Now Have Weekly Security Updates for You: Google will start releasing weekly security updates for its Chrome browser, the company said in a blog post Tuesday. Previously, Google released security fixes as part of updates that went out every two weeks. The more-frequent patches will start with Chrome 116, which began rolling out this week.
Section 3 – Cybersecurity and Privacy News for the Cyber-Concerned.
The Biden-Harris Administration continues its strong defensive work. While critical and necessary, the challenge will be implementation at ground-level. Top-down needs to meet bottom-up.
- The White House’s ‘AI Cyber Challenge’ aims to crowdsource national security solutions: The winning systems will be able to analyze and correct vulnerable code in critical infrastructure. … At the Black Hat USA Conference in Las Vegas on Wednesday, the Biden Administration revealed its plans to better defend the nation’s critical digital infrastructure: It’s launching a DARPA-led challenge competition to build AI systems capable of proactively identifying and fixing software vulnerabilities. … The “AI Cyber Challenge” (AIxCC) is a two-year development program open to competitors throughout the US. It’s being hosted by DARPA in collaboration with Anthropic, Google, Microsoft and OpenAI. Those companies are providing both their expertise in the field and access to their AI technologies.
- White House rolls out array of cyber initiatives to bolster K-12 defenses: The Biden-Harris administration on Monday announced a host of federal and private industry initiatives to strengthen the digital defenses of K-12 schools as educators across the country scramble for resources to fight a rising tide of cyberattacks. … The White House hosted the “Cybersecurity Summit for K-12 Schools,” featuring an array of education technology providers and superintendents. It comes after the most recent school year saw eight significant digital attacks, including four that forced schools to cancel classes. … The administration is “committed to taking real meaningful steps to ease the minds of parents” by securing digital infrastructure to “make it harder for bad actors” to steal the sensitive information of students and educators or security details that could endanger a school, Anne Neuberger, the deputy national security adviser for cyber and emerging technology, told reporters during a call on Sunday.
Kudos to Polish Central Cybercrime Bureau, Europol, and the US Federal Bureau of Investigation for their take-down of a hosting service for cybercriminals.
- 5 arrested in Poland for running bulletproof hosting service for cybercrime gang: This week, the Polish Central Cybercrime Bureau (Centralne Biuro Zwalczania Cyberprzestępczości) under the supervision of the Regional Prosecutor’s Office in Katowice (Prokuratura Regionalna w Katowicach) took action against LolekHosted.net, a bulletproof hosting service used by criminals to launch cyber-attacks across the world. … Five of its administrators were arrested, and all of its servers seized, rendering LolekHosted.net no longer available. … This latest success in the fight against cybercrime follows a complex investigation supported by Europol and the US Federal Bureau of Investigation (FBI).
Japan and Britain both revealed breaches this week.
- China hacked Japan’s sensitive defense networks, officials say: In the fall of 2020, the National Security Agency made an alarming discovery: Chinese military hackers had compromised classified defense networks of the United States’ most important strategic ally in East Asia. Cyberspies from the People’s Liberation Army had wormed their way into Japan’s most sensitive computer systems. … Tokyo has strengthened its defenses, but gaps remain that could slow information-sharing with the Pentagon
- ‘Hostile actors’ hacked British voter registry, electoral agency says: Britain’s Electoral Commission announced Tuesday that it had identified a cyberattack, which went unnoticed for at least 14 months, that gave “hostile actors” access to its systems. … The still-unidentified hackers would have had access to emails and voter information, mostly names and addresses, much of which was already in the public domain, the commission said in a statement posted to the social media platform X, formerly called Twitter. The August 2021 breach, which was discovered in October 2022, “has no impact” on voters’ “ability to take part in the democratic process” and will not affect “current registration status or eligibility,” according to an FAQ about the breach posted to the commission website.
We continue to make it way too easy for cybercriminals.
- Homeland Security report details how teen hackers exploited security weaknesses in some of the world’s biggest companies: A group of teenage hackers managed to breach some of the world’s biggest tech firms last year by exploiting systemic security weaknesses in US telecom carriers and the business supply chain, a US government review of the incidents has found, in what is a cautionary tale for America’s critical infrastructure. … The Department of Homeland Security-led review of the hacks, which was shared exclusively with CNN, determined US regulators should penalize telecom firms with lax security practices and Congress should consider funding programs to steer American youth away from cybercrime.
- Has Microsoft cut security corners once too often?: As Microsoft revealed tidbits of its post-mortem investigation into a Chinese attack against US government agencies via Microsoft, two details stand out: the company violated its own policy and did not store security keys within a Hardware Security Module (HSM) — and the keys were successfully used by attackers even though they had expired years earlier. … This is simply the latest example of Microsoft quietly cutting corners on cybersecurity and then only telling anyone when it gets caught. … Tenable CEO Amit Yoran wrote a powerful post on LinkedIn last week and described “a repeated pattern of negligent cybersecurity practices…. Microsoft’s lack of transparency applies to breaches, irresponsible security practices and to vulnerabilities, all of which expose their customers to risks they are deliberately kept in the dark about.”
Lessons Learned from the MOVEit supply chain debacle.
- The MOVEit mass hacks hold a valuable lesson for the software industry: The MOVEit mass hacks will likely go down in history as one of the largest and most successful cyberattacks of all time. … By exploiting a vulnerability in Progress Software’s MOVEit managed file transfer service, used by thousands of organizations to securely transfer large amounts of often-sensitive files, hackers were able to inject SQL commands and access customers’ sensitive data. The attack exploited a zero-day vulnerability, which meant Progress was unaware of the flaw and did not have time to patch it in time, leaving its customers largely defenseless. … The Russia-linked Clop ransomware group, which claimed responsibility for the hacks, has been publicly listing alleged victims since June 14. This growing list includes banks, hospitals, hotels, energy giants and more, and is part of an attempt to pressure victims into paying a ransom demand to stop their data from spilling online. In a post this week, Clop said that on August 15, it would leak the “secrets and data” of all MOVEit victims that refused to negotiate. … According to Emsisoft’s latest statistics, the MOVEit hack has affected at least 620 known corporates and more than 40 million individuals. Those figures have increased almost daily since the hacks began.
Watching cybercriminals at work gives researchers new insights into their objectives and behaviors. Different strokes for different folks.
- Researchers watched 100 hours of hackers hacking honeypot computers: Imagine being able to sit behind a hacker and observe them take control of a computer and play around with it. … That’s pretty much what two security researchers did thanks to a large network of computers set up as a honeypot for hackers. … The researchers deployed several Windows servers deliberately exposed on the internet, set up with Remote Desktop Protocol, or RDP, meaning that hackers could remotely control the compromised servers as if they were regular users, being able to type and click around. … Thanks to these honeypots, the researchers were able to record 190 million events and 100 hours of video footage of hackers taking control of the servers and performing a series of actions on them, including reconnaissance, installing malware that mines cryptocurrencies, using Android emulators to conduct click fraud, brute-forcing passwords for other computers, hiding the hackers’ identities by using the honeypot as a starting point for another attack, and even watching porn.
This week in Cybercrime. Two more MOVEit victims. Attacks on our cities and copper miner Freeport-McMoRan.
- EY breach exposes Bank of America customer credit card numbers: Ernst & Young (EY) said over 30,000 Bank of America customers were exposed via the MOVEit Transfer attacks, with threat actors accessing financial account information and credit card numbers.
- Missouri says some Medicaid health information was compromised in MOVEit breach: Missouri’s Department of Social Services (DSS) this week became the latest state agency to confirm it had data stolen through a vulnerability affecting the MOVEit file transfer tool. … A DSS spokesperson would not say how many people were affected but said they will be sending notices to “all Missouri Medicaid participants and providers that were enrolled in May of 2023.” … In a statement released Tuesday, officials said they were notified by IBM on June 13 that Medicaid participants’ protected health information was accessed by hackers.
- Hackers stole $6 million from city of New Haven in cyberattacks: Hackers stole more than $6 million from the city of New Haven through a series of cyberattacks, and the FBI and New Haven police are investigating, Mayor Justin Elicker announced Thursday. … It appears that hackers got access to the email account of the chief operating officer of New Haven’s public schools in late May. … The mayor said the thefts happened through what the FBI calls “business email compromise.”
- California city investigating data theft after ransomware group’s claims: The California city of El Cerrito is investigating the potential theft of data after a ransomware group added the city’s government to its list of victims on Wednesday.
Number affected in Dallas ransomware attack expected to grow, city says: A week after Dallas revealed 26,212 people have been impacted by the city’s ransomware attack, officials say it’s likely an ongoing review will reveal more people had their personal information exposed. They also believe it could take at least several months to determine the full scope and cost to taxpayers. - Copper miner Freeport-McMoRan reports cybersecurity incident: Freeport-McMoRan said on Friday it was investigating a cybersecurity incident affecting the copper miner’s information systems.
Section 4 – Managing Information Security and Privacy in Your Organization.
Cybersecurity Infrastructure Security Agency (CISA) and the National Security Agency (NSA) recently collaborated on a new best-practices guide for administrators on identity and access management.
- What CISA and NSA Guidance Means for Critical Infrastructure Security: Strategically investing in solutions that meet you where you are makes all the difference in staying secure from cyber threats. … The Cybersecurity Infrastructure Security Agency (CISA) and the National Security Agency (NSA) recently collaborated to produce an important new document, “Identity and Access Management: Recommended Best Practices for Administrators.” Part of the Enduring Security Framework (ESF), it presents a distillation of identity access management (AIM) and cybersecurity guidance put forth by CISA to date, based on NIST standards. It is specifically packaged for the information security and risk management (ISRM) admin and targeted at the private sector.


