This week’s essential cybersecurity and privacy news for the cyber-aware and the cyber-concerned. Designed to educate, support, and advocate.
Stan’s Top of the News
As somewhere in the neighborhood of 35% of us trust the news we get from social media platforms, our Top of the News is an in-depth analysis from The Washington Post showing how social media companies are receding from their role as watchdogs.
Russia, China, North Korea, Iran, along with other enemies of America, both foreign and domestic, can be expected to increase the amount of disinformation they generate. Making matters more challenging, they will use AI to make their disinformation seem more believable.
The result will be a significant increase in disinformation at the same time as social media sites are doing less to help their readers recognize it.
This puts the burden on we the people to be extra-vigilant at the same time as our psychological biases — particularly confirmation bias — push us to believe the disinformation that aligns with our other beliefs.
The net result: Expect the 2024 elections to be a wild ride. Our Republic will be tested as never before.
- Following Elon Musk’s lead, Big Tech is surrendering to disinformation: Facebook and YouTube are receding from their role as watchdogs against conspiracy theories ahead of the 2024 presidential election. … Social media companies are receding from their role as watchdogs against political misinformation, abandoning their most aggressive efforts to police online falsehoods in a trend expected to profoundly affect the 2024 presidential election.
New. Family Protection Newsletter: Did you know we created the Family Protection Newsletter, for non-cyber experts? For your parents, friends, those who need to protect themselves in a digital world. We feature info on how to freeze your credit and what ‘marriage scams’ are in Edition 1. Sign up or share with a friend! Click here to learn more and quickly add to your free subscription!
How Hackable Are You? Take our quiz. Find out how hackable you are and download our free 8-step guide.
- How Hackable Are You? Think your defenses are strong. Find out as SecureTheVillage tests you on five basics. Please take our short quiz as your answers will help you and guide us to improve community safety.
Upcoming events. Please join us.
- Los Angeles Cybersecurity Workforce Coalition: The monthly meeting of the workforce coalition, Tue, September 5, 1:00 pm – 2:00 pm PT.
Cyber Humor
Cybersecurity Nonprofit of the Week … US Valor
Kudos this week to US Valor, a nonprofit with two intertwined objectives: (1) helping veterans transition back into civilian life and (2) helping America meet our cybersecurity workforce challenge. US Valor does this through an innovative Department of Labor approved Apprenticeship Program. The US Valor Cybersecurity Apprenticeship Program (CAP) is all about helping transitioning military personnel and U.S. Veterans experience a smooth transition from military life to the civilian world through its Department of Labor Registered Apprenticeship Program (RAP). I’m a proud member of US Valor’s Advisory Board and I encourage you to support them.
Live on Cyber with Dr. Stan Stahl – Live on LinkedIn and Your Favorite Podcast Platform

The Silent War on Small Organizations: From Stealthy Ransomware to AI Threats: (Video) (Podcast): Today’s #cyber landscape is evolving, and so is the threat to small organizations. The balance of power has shifted, and the bad actors are increasingly sophisticated. From the ‘Play’ Ransomware Group targeting Managed Service Providers (#MSPs) and thereby endangering midsized and smaller organizations across the globe, to hackers seamlessly integrating into platforms like Slack and Trello—small organizations find themselves at the frontline of an escalating digital battle. And if that wasn’t enough, the rise of generative AI technologies now poses newer, unpredictable threats. But with knowledge, comes power. Join Stan and Julie in this episode of #LiveonCyber as we dive deep into the escalating cyber threats facing small organizations and discuss ways to reinforce digital defenses. #Smallbusinesses, it’s time to ramp up – use these insights to help safeguard your business and keep your doors open. In cybersecurity, unity is strength. It takes a village to secure the Village™.
Section 2 – Let’s Be Careful Out There. And Let’s Help Others Who Aren’t Yet Cyber-Aware.
A Best Buy scam alert and two scam stories. Let’s be careful out there.
- Best Buy scam alert! People are pretending to be members of the Geek Squad. How to spot it: Best Buy customers beware. Scammers are pretending to be from Geek Squad, the company’s tech-support arm, and tricking people into handing over their personal information.
- Scam victim tricked into stealing $200,000 for scammers, police say: DES MOINES, Iowa (KCCI) – Police say an Iowa man who once lost thousands to a phone scam thought he was being vigilant, but he was tricked again, this time into working for the scammers. … Loren Esse is facing charges for his alleged participation in a money laundering scheme. Police say he was tricked into working for scammers, who convinced him they were a government agency investigating cybercrime. … “He started out in this case as a victim. But as he continued on, moving this money through these accounts and putting the cash into bitcoin and sending it on, what we realized was that he’s actually helping them facilitate this crime unknowingly,” said Des Moines Police Department Sgt. Paul Parizek.
- Scammers impersonate bank employees to steal nearly $2M from Pennsylvania customers, officials say: A theft ring stole nearly $2 million from bank customers in central Pennsylvania in an elaborate scheme in which the scammers, posing as bank employees, tricked people into giving up their account information, the attorney general’s office said Friday. … The suspects disguised their phone numbers to make it seem as if the calls were coming from the banks’ phone numbers, and asked victims to provide their online banking login, debit card number and other information. Victims then got locked out of their accounts.
And scamming is only going to get worse with AI.
- Deepfake Imposter Scams Are Driving a New Wave of Fraud: Computer-generated children’s voices so realistic they fool their own parents. Masks created with photos from social media that can penetrate a system protected by face ID. They sound like the stuff of science fiction, but these techniques are already available to criminals preying on everyday consumers. … The proliferation of scam tech has alarmed regulators, police and people at the highest levels of the financial industry. Artificial intelligence in particular is being used to “turbocharge” fraud, US Federal Trade Commission Chair Lina Khan warned in June, calling for increased vigilance from law enforcement.
Meanwhile, Christie’s, the world’s best known art auction house, failed to protect the privacy of people submitting art photos for evaluation.
- How a Christie’s website revealed where people kept their art: The British auction house inadvertently published location data on its website for hundreds of images of items owners were seeking to sell. … On a recent Wednesday evening, a university professor in a large town in western Germany was preparing several paintings to be sold through the British auction house Christie’s. Using his iPhone, he took pictures of the inherited works at his home to upload to the company’s website. Within a few weeks, the site promised, Christie’s would give him an estimate of their value and tell him if it was interested in auctioning them. … But by uploading the images, he not only sent pictures of the pieces to Christie’s, he also revealed their exact location for anyone to see online, according to two German cybersecurity researchers. Hundreds of other would-be Christie’s clients, including Americans, were exposed to the same vulnerability, the two researchers, Martin Tschirsich and André Zilch, told The Washington Post. … The findings show how cybersecurity vulnerabilities aren’t just an issue for Big Tech companies, but for almost everyone as more and more business is transacted over the internet.
Section 3 – Cybersecurity and Privacy News for the Cyber-Concerned.
How hard is it to get basic information about us from the credit bureaus? Not very, as the following story demonstrates. The story is another illustration of the need for Congress to act to protect the American people.
- The Secret Weapon Hackers Can Use to Dox Nearly Anyone in America for $15: Most Americans have very little choice but to provide their personal information to credit bureaus. Hackers have found a way into that data supply chain, and are advertising access in group chats used by violent criminals who rob, assault, and shoot targets.
Here’s an excellent analysis from Scientific American on what it will take to put guard rails on AI.
- Safeguarding AI Is Up to Everyone: The use of artificial intelligence is so varied and industry-specific, no one federal agency can manage it alone. … Artificial intelligence is everywhere, and it poses a monumental problem for those who should monitor and regulate it. At what point in development and deployment should government agencies step in? Can the abundant industries that use AI control themselves? Will these companies allow us to peer under the hood of their applications? Can we develop artificial intelligence sustainably, test it ethically and deploy it responsibly? … Such questions cannot fall to a single agency or type of oversight. AI is used one way to create a chatbot, it is used another way to mine the human body for possible drug targets, and it is used yet another way to control a self-driving car. And each has as much potential to harm as it does to help. We recommend that all U.S. agencies come together quickly to finalize cross-agency rules to ensure the safety of these applications; at the same time, they must carve out specific recommendations that apply to the industries that fall under their purview. … Without sufficient oversight, artificial intelligence will continue to be biased, give wrong information, miss medical diagnoses, and cause traffic accidents and fatalities.
As we regularly report, North Korea appears to get upwards of 50% of their GDP from cybercrime.
- FBI says North Korean hackers preparing to cash out after high-profile crypto hacks: The U.S. government said it believes North Korean hackers are preparing to cash out millions of dollars stolen during a spate of high-profile crypto hacks. … On Tuesday, the FBI warned cryptocurrency companies about recent blockchain activity connected to the theft of hundreds of millions of dollars in cryptocurrency by malicious actors affiliated with the North Korea-backed Lazarus Group, also known as APT38 and “TraderTraitor.”
While it may be another 15 years until quantum computers are big enough and powerful enough to break current encryption algorithms, NIST has been hard at work since 2016 to develop cryptographic algorithms strong enough to survive a quantum attack. This week, NIST published draft post-quantum standards.
- NIST Publishes First Draft Standards for Post-Quantum Cryptography: The first draft standards for quantum-resistant public key cryptography based on algorithms chosen by the National Institute for Standards and Technology (NIST) are now available for public comment. … The publication of NIST’s first post-quantum cryptographic (PQC) draft standards marks an important milestone in its effort launched in 2016 to address the potential for quantum computers to break existing RSA encryption and elliptic-curve cryptography (ECC).
This week in cybercrime. Another report on the magnitude of the MOVEit breach. I expect lawsuits to be filed against both T-Mobile and Kroll for the cyberattack that seems to have compromised claimant information in several crypto bankruptcies. A Kroll lawsuit could test the boundaries of “reasonable” security.
- MOVEit, the biggest hack of the year, by the numbers: At least 1,000 companies compromised. At least 60 million individuals affected. Estimated losses exceed $9,000,000,000. And the bleeding continues.
- Hosting firm says it lost all customer data after ransomware attack: Danish hosting firms CloudNordic and AzeroCloud have suffered ransomware attacks, causing the loss of the majority of customer data and forcing the hosting providers to shut down all systems, including websites, email, and customer sites.
- Rackspace’s costs to deal with ransomware attack top $10 million: Rackspace Technology Inc. spent $10.8 million on expenses related to a ransomware attack in December that blocked thousands of customers from accessing their emails and related data, according to regulatory filings.
- Cyberattack shutters major NSF-funded telescopes for more than 2 weeks: As astronomers lose valuable windows for observations in Hawaii and Chile, cybersecurity experts wonder why hackers would target such facilities.
- Claimant Data Breached in Genesis, FTX and BlockFi Bankruptcy Cases: Kroll, the claims agent in bankruptcy cases for Genesis Global Holdco, FTX and BlockFi, said it was the victim of a cyberattack, and that data belonging to hundreds of claimants could have been accessed. Kroll said Thursday that a phone number belonging to the company’s restructuring administration business was compromised by hackers in a SIM-swapping attack on carrier T-Mobile US around Aug. 19.
Section 4 – Managing Information Security and Privacy in Your Organization.
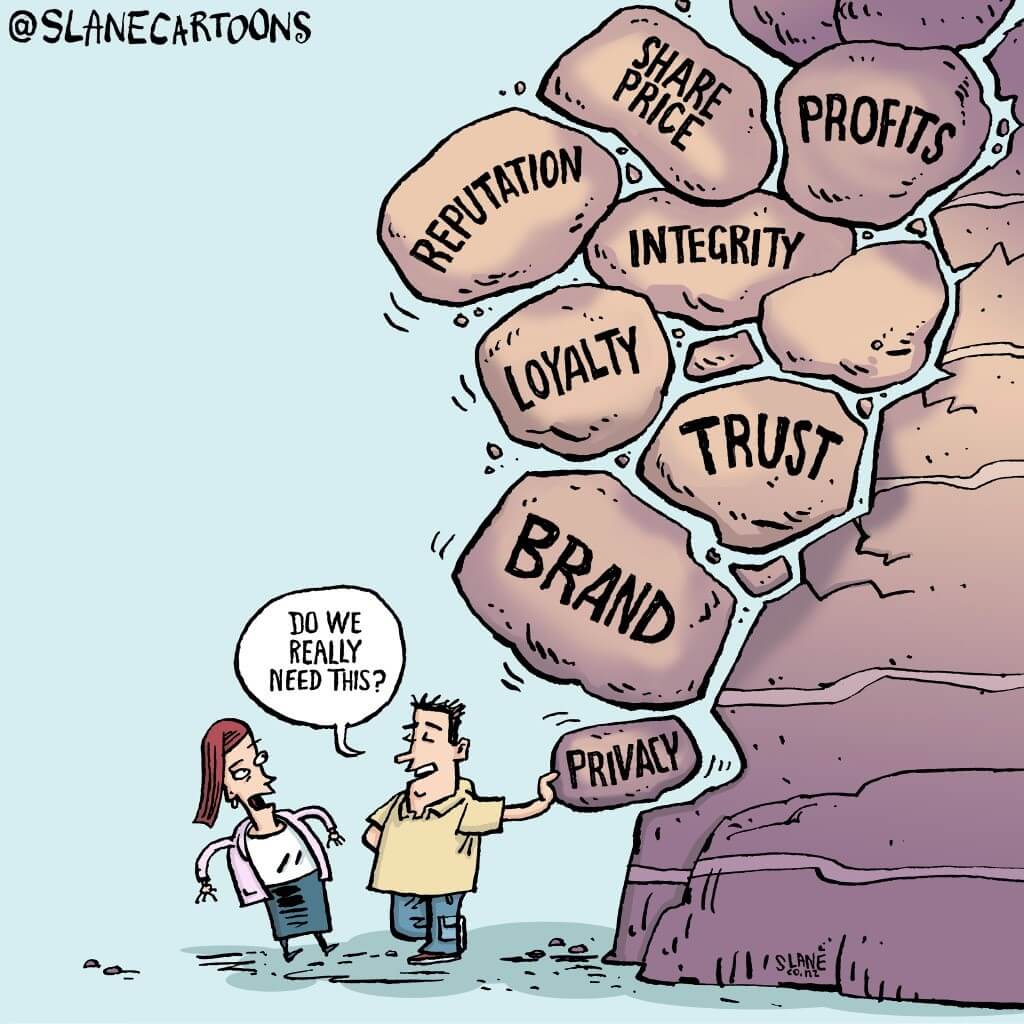
We regularly talk about the improtance of leadership — tone at the top — in managing cybersecurity. As the next story illustrates, leadership needs to come from throughout the organization.
- When Leadership Style Is a Security Risk: Risk-aware leaders can be a cybersecurity advantage. Their flexible leadership style and emphasis on security first help set the tone and demonstrate a commitment to avoiding risk. … Effective leaders have the power to motivate, inspire, encourage, and guide their teams. While C-suite leadership may receive the most accolades, it is leaders at all levels who hold the keys to the culture of a company. Leadership style is of the utmost importance when it comes to improving widespread cybersecurity readiness.
If you have to negotiate with hackers, it’s good to know the boundaries.
- Haggling With Hackers: Surprising Lessons From 50 Negotiations With Ransomware Gangs: Ransomware negotiations are usually shrouded in secrecy, but some security experts think that we should make them public and analyze them to glean insights. So that’s exactly what we did. … The prevailing wisdom from cybersecurity experts is that trying to negotiate with ransomware hackers is a bad idea, but on December 30, 2020, one victim broke the rules and gave it a shot.


