SecureTheVillage Calendar
Dr. Steve Krantz Webinar: Personal Cybersecurity January 12, 2021 @ 1:00 pm – 3:00 pm PST
Caltech/Fullstack Cyber Bootcamp Virtual/Online Hiring Day. January 12, 2021 @ 2:00 pm – 4:30 pm PST
Dr. Steve Krantz Webinar: Become A CyberGuardian January 14, 2021 @ 12:30 pm – 2:00 pm PST
Information Security Management Webinar: Ask the Lawyer: Updates on the Evolving Security and Privacy Legal Landscape with Jordan Fischer. January 14, 2021 @ 10:00 am – 11:00 am PST
Financial Services Cybersecurity Roundtable: Protecting Yourself and Your Business Against the Latest Cyber Threats with Mark Rhodes-Ousley. January 22, 2021 @ 8:30 am – 10:00 am PST
Digital Directors Network: Global Case Studies In Innovation Governance: An Australian And US Perspective January 27, 2021 @ 4:00 pm – 5:15 pm PST
Dr. Steve Krantz Webinar: Doing It … Online. TUE, February 9, 2021, 2:30 PM PST
Individuals at Risk
Cyber Privacy
Hey Alexa, Who Am I Messaging?: Research shows that microphones on digital assistants are sensitive enough to record what someone is typing on a smartphone to steal PINs and other sensitive info. ThreatPost, December 23, 2020
Cyber Defense
Delivering Santa from Third-Party Risk: 2020 has made even St. Nick susceptible to the risks associated with the coronavirus pandemic. Fortunately, cybersecurity experts are ready to help the merry old elf with advice on reducing risks to his global operations. DarkReading, December 24, 2020
Android security: The last piece of advice you’ll need for 2020: Jack Wallen takes one more opportunity to remind Android device owners to use those phones with a great deal of caution; otherwise, they could become victims of malware. TechRepublic, December 23, 2020
How to Not Fall for a Charity Scam This Holiday Season: This holiday season, many people will turn to charities to give back. The last thing they want to do is give money to scammers instead of a cause they truly support. According to the FBI’s website, charity fraud rises during the holidays, when people choose to make end-of-year tax deductible gifts. Security Intelligence, December 18, 2020
Cyber Warning
Fake Amazon gift card emails deliver the Dridex malware: The Dridex malware gang is delivering a nasty gift for the holidays using a spam campaign pretending to be Amazon Gift Cards. BleepingComputer, December 25, 2020
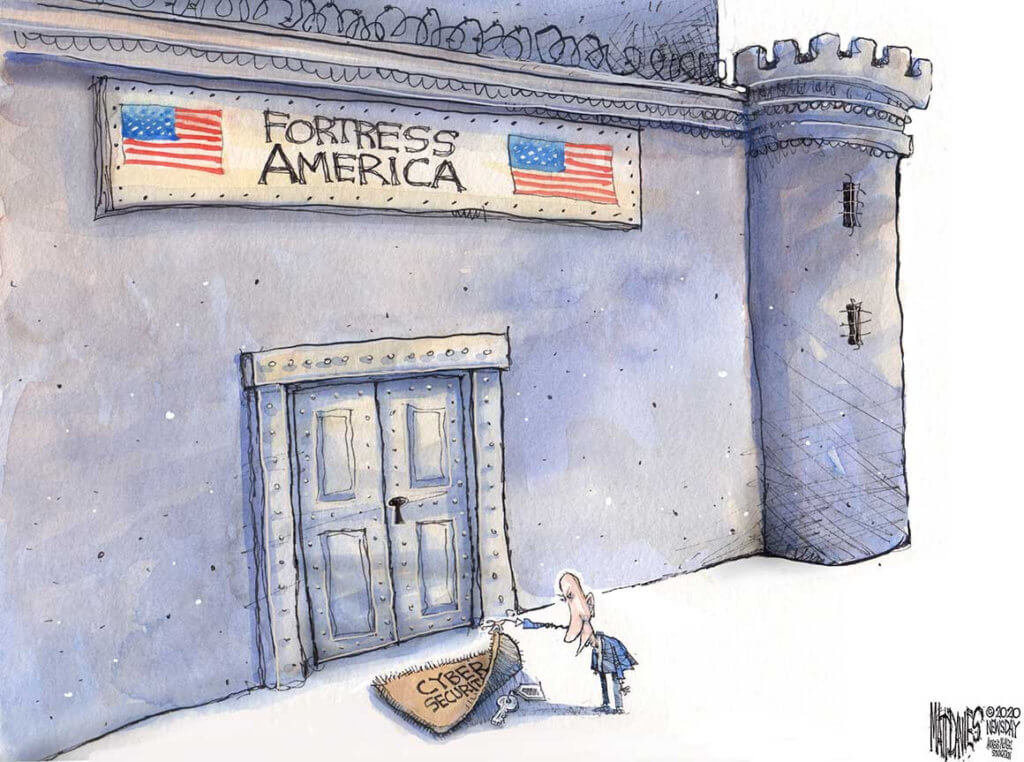
Cyber HUmor
Information Security Management for the Organization
Information Security Management
NIST Releases Draft Guidance for IoT Cybersecurity: The National Institute of Standards and Technology (NIST) released a draft version of Special Publication (SP) 800-213 and several supporting documents aimed at manufacturers, with the goal of establishing a baseline for securely integrating Internet of Things (IoT) devices into Federal networks. MeriaTalk, December 24, 2020
7 Cybersecurity Tools On Our Holiday Wish List: The holiday season is upon us. After a difficult year, and facing an even more challenging year ahead, digital defense experts don’t have visions of sugar plums dancing in their heads. Instead, they dream of cybersecurity tools and other resources to help them cope with a wild threat landscape. SecurityIntelligence, December 22, 2020
Cybersecurity Trends: Keeping Up With 2020’s ‘New Normal’: This year has seen major changes in cybersecurity trends. At times, 2020 seems to have come and gone in a flash. For many, it has dragged on for what seems to be years and years. Data breaches, new threats to education, the new normal of working from home (WFH), new malware styles and pandemic-related attacks are all cybersecurity threats specifically created or accelerated by COVID-19 and 2020’s other big news events. They are all part of a permanent and dramatic shift in society. Security Intelligence, December 22, 2020
Cyber Privacy
CCPA vs GDPR – Spot the Difference: For more than two years, the GDPR has been one of the most pressing pieces of data protection legislation that organisations handling data on EU residents had to get to grips with. Its strict regulations meant that companies compliant with the GDPR would also be likely to comply with the data protection standards in any territory outside of the EU as well. The status quo changed in July however, when the California Consumer Protection Act (CCPA) began to be enforced. CPO, December 22, 2020
Secure The Human
6 persuasion tactics used in social engineering attacks: IT security teams need to educate employees about the psychological techniques cybercriminals often use in social engineering attacks. TechRepublic, December 23, 2020
The Many Ways Disinformation And Cybercrime Can Infiltrate Your Business: Disinformation is having a profound impact on our lives. The same social engineering techniques that make advertising effective or that lure people into engaging with scams are even being wielded for political aims by organized groups with lots of resources. Deliberate disinformation, amplified by the exploitation of technology platforms, is manipulating public opinion and businesses on an alarming scale. Forbes, December 23, 2020
Cybersecurity in Society
Cyber Attack
Citrix devices are being abused as DDoS attack vectors … Citrix says it’s working on a fix, expected next year: Threat actors have discovered a way to bounce and amplify junk web traffic against Citrix ADC networking equipment to launch DDoS attacks. ZDNet, December 24, 2020
Cyber Espionage
Lazarus Group Targeted COVID-19 Research: Kaspersky: North Korean APT Group Used Malware in Attempt to Steal Information. BankInfoSecurity, December 24, 2020
Cyber Privacy
How to monitor the vaccinated while addressing privacy concerns: There is a great deal that public health authorities can learn if proper data are collected about the effects of the first anti COVID-19 vaccinations. Unfortunately, the data needed are quite extensive and personal. Privacy advocates are sure to raise objections. The solution is not to curb the necessary collection of health information but to institute effective oversight measures. TheHill, December 26, 2020
Cyber Freedom
Zero-click iMessage zero-day used to hack the iPhones of 36 journalists: Malicious messages installed spyware that recorded audio and pics and stole passwords. ars technica, December 21, 2020
National Cybersecurity – Solar Winds
Microsoft Discovers A Second Hacking Team Exploiting SolarWinds Orion Software: Microsoft’s security research blog says that a second hacking team distinct from the Russian SolarWinds hacking group also targeted the Texas-based software company since the beginning of the year. CPO, December 25, 2020
CrowdStrike Fends Off Attack Attempted By SolarWinds Hackers: The suspected Russian hackers behind the massive SolarWinds attack attempted to hack CrowdStrike through a Microsoft reseller’s Azure account but were ultimately unsuccessful, CrowdStrike says. CRN, December 24, 2020
CISA Releases Free Detection Tool for Azure/M365 Environment: CISA has created a free tool for detecting unusual and potentially malicious activity that threatens users and applications in an Azure/Microsoft O365 environment. The tool is intended for use by incident responders and is narrowly focused on activity that is endemic to the recent identity- and authentication-based attacks seen in multiple sectors. US Cert, December 24, 2020
NIST’s Ron Ross: ‘The Adversary Lives in the Cracks’: In the wake of the SolarWinds breach, Ron Ross of the National Institute of Standards and Technology has turned his attention to systems security engineering – and the reality that the adversaries are exploiting it to their advantage better than the defenders are. This disparity, Ross says, has to change. GovInfoSecurity, December 23, 2020
Five Solution Providers Breached By SolarWinds Hackers: Researchers: The SolarWinds hackers called for proceeding with the second stage of their attack on Stratus Networks, Digital Sense, ITPS and Netdecisions, and had an unknown response to compromising Deloitte, Truesec says. CRN, December 23, 2020
How the SolarWinds hackers are targeting cloud services in unprecedented cyberattack: Analysis: To understand where the SolarWinds attackers are going next, and how to defend against them, look to the clouds. GeekWire, December 23, 2020
Joe Biden Blames Russia For Huge SolarWinds Hack: President Donald Trump has cast doubt on Moscow’s involvement, despite even his own secretary of state and attorney general saying the intelligence points to Russia. Huffington Post, December 22, 2020
How SolarWinds could’ve been prevented … An interview with National Institute of Standards and Technology Fellow Ron Ross: As the government deals with what might be the worst cybersecurity breach ever, one federal expert says agency cyber planning misses an important practice. National Institute of Standards and Technology Fellow Ron Ross joined the Federal Drive with Tom Temin to discuss what should happen next. FederalNewsNetwork, December 22, 2020
SolarWinds Hack: Is NSA Doing the Same to Russia?: Espionage Operations Demand a Different Policy Response to Damaging Cyberattacks. BankInfoSecurity, December 21, 2020
How A Cybersecurity Firm Uncovered The Massive Computer Hack: The first word that hackers had carried out a highly sophisticated intrusion into U.S. computer networks came on Dec. 8, when the cybersecurity firm FireEye announced it had been breached and some of its most valuable tools had been stolen. NPR, December 21, 2020
SolarWinds incident should be a catalyst to rethink federal cybersecurity: Federal chief information officers and chief information security officers didn’t get a lot of sleep last week, and may not for the foreseeable future. FederalNewsNetwork, December 21, 2020
Christopher Krebs, Former Government Cybersecurity Head Blames Russian Intelligence For Massive Hack: Christopher Krebs, the former top cybersecurity official in the U.S., says Russia is to blame for a massive breach that’s affected the State Department, the Pentagon, the Treasury Department, the Department of Homeland Security and other departments and agencies. NPR, December 21, 2020
National Cybersecurity
How China Uses Stolen US Personnel Data: Interesting analysis of China’s efforts to identify US spies: By about 2010, two former CIA officials recalled, the Chinese security services had instituted a sophisticated travel intelligence program, developing databases that tracked flights and passenger lists for espionage purposes. “We looked at it very carefully,” said the former senior CIA official. China’s spies “were actively using that for counterintelligence and offensive intelligence. The capability was there and was being utilized.” China had also stepped up its hacking efforts targeting biometric and passenger data from transit hubs… Schneier on Security, December 24, 2020
Building resilience to the North Korean cyber threat: Asia Transnational Threats Forum, the Center for East Asia Policy Studies at Brookings: On October 15, as part of the Asia Transnational Threats Forum, the Center for East Asia Policy Studies at Brookings convened a virtual roundtable on cybersecurity and resilience, focused on North Korean cyber threats and the impact of digital technologies on the region’s security, economy, and political dynamics. The event builds on a series of forums started in 2018, including discussions on cyber issues, counterterrorism, and climate security. Brookings, December 23, 2020
Cyber Operations Tracker … Database of publicly known state-sponsored incidents that have occurred since 2005. Council on Foreign Relations: Since 2005, thirty-four countries are suspected of sponsoring cyber operations. China, Russia, Iran, and North Korea sponsored 77 percent of all suspected operations. In 2019, there were a total of seventy-six operations, most being acts of espionage. Council on Foriegn Relations, 2020
Cyber Enforcement
FBI and European law enforcement shut down VPN used by ransomware groups: The action cuts off access to a useful cybercrime tool, the agencies say. CNet, December 23, 2020
Disinformation
‘Deepfake’ Queen delivers alternative Christmas speech, in warning about misinformation: London (CNN)A fake Queen Elizabeth danced across TV screens on Christmas as part of a “deepfake” speech aired by a British broadcaster. CNN, December 25, 2020
Cyber Defense
Microsoft, McAfee, Rapid7, and Others Form New Ransomware Task Force: Industry group wants to get a framework in the hands of the new administration’s cybersecurity officials by early spring 2021. DarkReading, December 23, 2020


