This week’s essential cybersecurity and privacy news for the cyber-aware and the cyber-concerned. Designed to educate, support, and advocate.
Stan’s Top of the News
CISA introduces election security program to support states meet cybersecurity challenges. With all that’s happening in American society, the states need all the support they can get. Will they take it?
- Multiple threats to election systems prompt U.S. cybersecurity agency to boost cooperation with states: The nation’s cybersecurity agency on Thursday launched a program aimed at boosting election security in the states, shoring up support for local offices and hoping to provide reassurance to voters that this year’s presidential elections will be safe and accurate. … Officials with the U.S. Cybersecurity and Infrastructure Security Agency are introducing the program this week to the National Association of State Election Directors and National Association of Secretaries of State, which are meeting in the nation’s capital. … For state and local election officials, the list of security challenges keeps growing. Among them: potential cyberattacks waged by foreign governments, criminal ransomware gangs attacking computer systems and the persistence of election misinformation that has led to harassment of election officials and undermined public confidence.
Small and Midsize Organizations. Take your security to the next level. Apply Now! If you’re a small business, nonprofit, or IT / MSP in the greater Los Angeles area, apply NOW for LA Cybersecure, a pilot program with coaching and guidance that costs less than two cups of coffee a week. https://securethevillage.org/la-cybersecure-pilot/ The LA Cybersecure Pilot Program is funded by a grant from the Center for Internet Security (CIS) Alan Paller Laureate Program.
Family Protection Newsletter: Did you know we created the Family Protection Newsletter for non-cyber experts? For your parents, friends, those who need to protect themselves in a digital world. Sign up or share with a friend! Click here to learn more and quickly add to your free subscription!
How Hackable Are You? Take our test. Find out how hackable you are and download our free updated 13-step guide.
- How Hackable Are You? Think your defenses are strong. Find out as SecureTheVillage tests you on five basics. Please take our short test as your answers will help you and guide us to improve community safety.
Upcoming events. Please join us.
- Los Angeles Cybersecurity Workforce Coalition: The monthly meeting of the workforce coalition, Tue, February 6, 1:00 pm – 2:00 pm PT. The LA Cybersecurity Workforce Coalition is for employers, educators, government, nonprofits, and others with a professional interest in the cybersecurity workforce challenge.
Please Support SecureTheVillage.
- We need your help if we’re to build a world of CyberGuardians TM. Please donate to SecureTheVillage. Thank you. It takes a village to secure the village. TM.
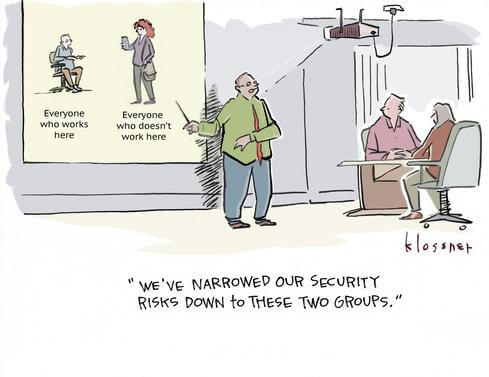
Cyber Humor
Cybersecurity Nonprofit of the Week … National Cybersecurity Alliance,
Kudos this week to the National Cybersecurity Alliance, a non-profit organization on a mission to create a more secure, interconnected world. The Alliance is an advocate for the safe use of technology, educating everyone on how we can protect ourselves, our families, and our organizations from cybercrime. They create strong partnerships between governments and corporations to amplify their message and to foster a greater “digital” good, encouraging everyone to do their part to prevent digital wrongdoing of any kind. As they say, the real solution to cybercrime isn’t technology, it’s all of us doing our part. Like SecureTheVillage, the National Cybersecurity Alliance is a member of Nonprofit Cyber, a coalition of implementation-focused cybersecurity nonprofits.
Live on Cyber with Dr. Stan Stahl – Live on LinkedIn and Your Favorite Podcast Platform

Clear. Simple. Wrong. (Video) (Podcast): H.L. Mencken famously said “For every complex problem there is an answer that is clear, simple, and wrong.” We humans are wired to want simple solutions to complex problems. It’s built into our neurology. And it makes it harder to manage cybersecurity. The computer and telecommunications revolution that we’re in the middle of is upending our world. A simple cybercrime example: In the old days, if a criminal wanted to rob a bank, the criminal had to go to the bank. No more. Now the criminal can steal money from people’s bank accounts over the Internet from anywhere in the world. Complex problems don’t get solved, they get managed. Let’s take a step back and ask what we can do to manage our security and privacy; in our homes, in our places of work, in our schools, and throughout our community. As always, Stan Stahl, PhD and Julie Michelle Morris provide actionable tips and thoughtful wisdom in a fun conversation on the complexities of #cybersecurity and #privacy.
Section 2 – Let’s Be Careful Out There. And Let’s Help Others Who Aren’t Yet Cyber-Aware.
Another sad story of online fraud stealing the future of our senior citizens. Please warn the people you know to be careful.
- With ‘pig butchering’ scams on the rise, FBI moves to stop the bleeding: Victims of the sophisticated online con are likened to hogs, fattened up for slaughter. … She called herself Anna, and she reached out to Barry May over social media. … “It was on Facebook, was an Asian woman that supposedly lived in New York, on Fifth Avenue,” he said. “And so we just started chatting.” … Soon, he said, Anna was sending explicit photos. May, a divorced and retired insurance adjuster living in Mississippi, was smitten. She told him they could be together, but first she needed a favor.
No the sky is not falling. When “what could happen” gets mistaken for “what has happened.”
- 3 million smart toothbrushes were not used in a DDoS attack after all, but it could happen: [UPDATED] What’s next, malware-infected dental floss? But seriously: It’s a reminder that even the smallest smart home devices can be a threat. Here’s how to protect yourself. … In a note to ZDNET, a Fortinet representative said, “To clarify, the topic of toothbrushes being used for DDoS attacks was presented during an interview as an illustration of a given type of attack, and it is not based on research from Fortinet or FortiGuard Labs. It appears … the narrative on this topic has been stretched to the point where hypothetical and actual scenarios are blurred.”
Section 3 – Cybersecurity and Privacy News for the Cyber-Concerned.
Two stories on personal privacy. The first an opinion piece by Senator Kirsten Gillibrand. The second an illustration of why Gillibrand is right.
- It’s open season on personal data: We need a Data Protection Agency now: by Sen. Kirsten Gillibrand, opinion contributor. … A few months ago, a New York mom answered a call from what sounded like her 14-year-old daughter, who was screaming and crying that she’d been arrested. A “police officer” then came on the line and told the mother that she needed to deliver $15,500 to bail her daughter out. … In reality, the girl’s voice on the other end was an AI-powered voice clone — possibly generated using clips compiled from social media. … It’s just one example of the growing number of scams using AI technology to exploit a person’s online data. Across the country, Americans lose billions of dollars every year to cybercrimes. From phishing, social media and phone scams to data breaches and ransomware attacks, criminals are finding new and innovative ways to collect consumer data and exploit it. … It’s not just criminals who are using our personal data in dangerous and concerning ways. … The U.S. is one of the only democracies, and virtually the only member of the Organization for Economic Cooperation and Development, without a federal data protection agency. Instead, authorities have to rely on a patchwork of protections that make jurisdictional oversight very nebulous.
- Judge allows case against geolocation data broker Kochava to proceed: An Idaho federal judge on Saturday ruled that a Federal Trade Commission (FTC) enforcement action against the data broker Kochava — which the agency asserts sells vast amounts of non-anonymized data belonging to millions of people — may continue, a reversal of a prior ruling to dismiss the case. … Privacy advocates consider the court decision to be significant for several reasons, including that the case is the FTC’s first against a geolocation data broker to be fought in court. The decision also lays the foundation for a widely anticipated FTC rulemaking on commercial surveillance, which could further limit data brokers’ activities. … The ruling cites FTC arguments that Kochava customers can draw upon its various “data collections” to identify individuals. The ruling cites an example from the FTC alleging that Kochava combines and packages data that can identify “a woman who visits a particular building, the woman’s name, email address, and home address, and whether the woman is African-American, a parent (and if so, how many children), or has an app identifying symptoms of cancer on her phone.”
This week brings additional evidence of nefarious Chinese state-sponsored hackers together with another story of how North Korea uses the proceeds of its cyber-thefts to support its nuclear ambitions.
- Chinese hackers have lurked in some US infrastructure systems for ‘at least five years’: The Chinese hackers behind a campaign to infiltrate transportation hubs and other critical American infrastructure have had access to some of their targets’ computer networks for “at least five years,” according to a new report by US and allied security agencies obtained by CNN. … The campaign is part of a long-running effort by the hackers to position themselves for potentially crippling cyberattacks that could disrupt water and electricity, according to US officials.
- Dutch intelligence finds Chinese hackers spying on secret Defence Ministry network: Chinese state-sponsored hackers broke into an internal computer network used by the Dutch Ministry of Defence last year, the Netherlands said Tuesday. … In a rare announcement, both the country’s military (MIVD) and civilian (AIVD) security services said the ministry had been hacked for espionage purposes after the threat actor exploited a vulnerability in FortiGate devices, as first reported by Reuters.
- Exclusive: UN experts investigate 58 cyberattacks worth $3 bln by North Korea: United Nations sanctions monitors are investigating dozens of suspected cyberattacks by North Korea that raked in $3 billion to help it further develop its nuclear weapons program, according to excerpts of an unpublished U.N. report reviewed by Reuters.
This week in cybercrime. The first tells the story of a deepfake video conference leading to a $25 million fraud.
- Finance worker pays out $25 million after video call with deepfake ‘chief financial officer’: Authorities are increasingly concerned at the damaging potential posed by artificial intelligence technology. … A finance worker at a multinational firm was tricked into paying out $25 million to fraudsters using deepfake technology to pose as the company’s chief financial officer in a video conference call, according to Hong Kong police. … The elaborate scam saw the worker duped into attending a video call with what he thought were several other members of staff, but all of whom were in fact deepfake recreations, Hong Kong police said at a briefing on Friday.
- The Lurie Children’s outage is having ripple effects across the pediatric medical community: Some community providers who rely on Lurie’s network say they can’t bill patients or access online records and are sending patients elsewhere. … The cybersecurity issue at Lurie Children’s Hospital that has spanned more than a week is having ripple effects across the pediatric medical community — from slow-downs in billing to young patients being sent to other hospitals to community physicians who rely on Lurie’s system struggling to communicate with families. … Lurie, which is nationally renowned and is the biggest children’s hospital in the Chicago area, has been dealing with a “criminal threat” to its network, which forced Lurie to shut down the system since Jan. 31. … As the cybersecurity issue cripples communication at Lurie and beyond, some pediatricians are sending their young patients to other hospitals if they need urgent medical care. … But without a window into children’s previous treatment at Lurie, since their online medical records have gone dark, these patients are often showing up without access to their medical history, lab results or medications — crucial details a doctor might need to help make decisions about their medical care.
- Health insurance data breach affects nearly half of France’s population, privacy regulator warns: Data on more than 33 million people in France, approximately half the population, was compromised in a cyberattack at the end of January, according to the country’s privacy watchdog. … The Commission Nationale Informatique et Libertés (CNIL) announced this week it had been informed by two health insurance companies, Viamedis and Elmer’s, about the incident. … It warned that the data affects policyholders and their families and includes “marital status, date of birth and social security number, the name of the health insurer as well as the guarantees of the contract taken out.” Medical histories and treatment data was not compromised.
- Clorox says cyberattack caused $49 million in expenses: Clorox has confirmed that a September 2023 cyberattack has so far cost the company $49 million in expenses related to the response to the incident. … Clorox is an American manufacturer of consumer and professional cleaning products with 8,700 employees and almost $7.5 billion in revenue for 2023. … On August 11th, Clorox suffered a cyberattack that caused significant disruption in the company’s operation, leading to lowered production and decreased availability of consumer products.
- Ransomware victim numbers rose by 50% in 2023: The number of victims that ransomware groups posted on their data leak sites increased by 50% last year according to an analysis by researchers from Palo Alto Networks. Twenty-five new groups also appeared last year but some of them had a short life until they disbanded or rebranded. … “2023 presented a thriving and evolving ransomware landscape as reflected in posts from ransomware leak sites,” the Palo Alto researchers said in their report.
- Ransomware hackers raked in a record $1 billion from victims last year: Despite efforts to contain the ransomware criminal ecosystem, the promise of wealth and the relative lack of consequences have spurred more ransomware hackers than ever before. … Victims of ransomware paid their attackers more than $1 billion last year, a new report has found, a record high that shows that many cybercriminals are raking in money by extorting people and institutions with near impunity. … The figure comes from a study of 2023 ransomware payments conducted by Chainalysis, a company that tracks cryptocurrency payments around the world.
Section 4 – Managing Information Security and Privacy in Your Organization.
Warning to executives. Don’t trust those QR codes.
- QR Code ‘Quishing’ Attacks on Execs Surge, Evading Email Security: The use of QR codes jumped in Q4 2023, especially against executives, who saw 42 times more QR code phishing than the average employee. … Email attacks using QR codes to deliver malicious payloads surged in the last quarter. Attackers are specifically targeting corporate executives and managers.
For the IT Team
- Critical Patches Released for New Flaws in Cisco, Fortinet, VMware Products: Cisco, Fortinet, and VMware have released security fixes for multiple security vulnerabilities, including critical weaknesses that could be exploited to perform arbitrary actions on affected devices.
- Ivanti publishes urgent warning about new vulnerability: The software company Ivanti has identified yet another new vulnerability in one of its products requiring an immediate patch from users. … In an advisory on Thursday afternoon, the company spotlighted CVE-2024-22024 — a vulnerability affecting Ivanti Connect Secure, Ivanti Policy Secure and ZTA gateways. … The vulnerability carries a severity score of 8.3 and “allows an attacker to access certain restricted resources without authentication.”


