Individuals at Risk
Cyber Defense – Log4j
A NON-TECHNICAL LOG4J / LOG4SHALL FAQ: Log4j is a computer program. It was written a couple of decades ago. It has been incorporated into zillions of other computer programs by companies all over the world. This includes Google, Apple, IBM, Facebook, browsers like Firefox, etc, etc, etc. Depending on brand and model, it also includes smart TVs, security cameras, doorbells, etc. Stan’s Corner, SecureTheVillage, December 28, 2021
Cyber Defense
Why You Should Always Enable 2-Factor Authentication: You’ve no doubt heard about two-factor authentication at some point in the relatively recent past, but if you’re like many consumers, there’s a good chance you haven’t actually used it yet. If that’s the case, it’s time to learn about what, exactly, two-factor authentication is, how it works, and why it is very important that you use it. SlashGear, December 30, 2021
This holiday season, give your children the gift of cybersecurity awareness: Don’t leave your kids to their own devices – give them a head start with staying safe online instead. WeLiveSecurity, December 22, 2021
Cyber Warning
Are Apple AirTags Being Used to Track People and Steal Cars?: On a Sunday night in September, Ashley Estrada was at a friend’s home in Los Angeles when she received a strange notification on her iPhone: “AirTag Detected Near You.” Yahoo, December 31, 2021
RedLine malware shows why passwords shouldn’t be saved in browsers: The RedLine information-stealing malware targets popular web browsers such as Chrome, Edge, and Opera, demonstrating why storing your passwords in browsers is a bad idea. BleepingComputer, December 28, 2021
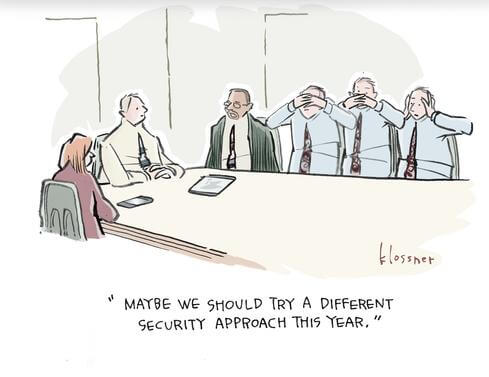
Cyber Humor
Information Security Management for the Organization
Cybersecurity in the C-Suite & Board
Why Cyber Due Diligence Is Essential to the M&A Process: That announcement may feel good, but if your prospective acquisition’s cybersecurity levels are substandard, it might be best to hold off. DarkReading, December 29, 2021
Information Security Management
Changing the Conversation with Risk Quantification: As organizations continue to leverage the latest technologies and move toward even greater interconnectivity in the pursuit of growth, business strategy and cybersecurity continue to converge. Cybersecurity concerns now extend beyond the traditional IT areas of responsibility, impacting all levels of an organization. SecurityIntelligence, December 28, 2021
Hackers Are Getting Better and Better at Defeating Your 2FA Security: Two-factor authentication is a widely used and trusted security mechanism, but criminals are increasingly using malicious toolkits that can outwit it. Gizmodo, December 28, 2021
7 Steps for Navigating a Zero-Trust Journey: Don’t think of zero trust as a product. Think of it as “how you actually practice security.” DarkReading, December 28, 2021
93% of Tested Networks Vulnerable to Breach, Pen Testers Find: Data from dozens of penetration tests and security assessments suggest nearly every organization can be infiltrated by cyberattackers. DarkReading, December 21, 2021
Cybersecurity in Society
Cyber Crime
$2.2M Worth of Bored Ape Yacht Club NFTs Stolen — Victim Says Incident Was ‘Arguably the Worst Night’ of His Life: According to reports, roughly $2.2 million worth of Bored Ape Yacht Club (BAYC) and Mutant Ape Yacht Club (MAYC) non-fungible tokens (NFTs) were stolen from a collector. The owner of the NFTs Todd Kramer said the incident was “arguably the worst night” of his life. Furthermore, there’s claims that the NFT marketplace Opensea froze the collectibles, and crypto advocates are complaining about the lack of decentralization. Bitcoin.com, December 31, 2021
T-Mobile confirms SIM swapping attacks led to breach: T-Mobile has confirmed a data breach that was caused in part by SIM swapping attacks, according to a statement from the company. ZDNet, December 30, 2021
United States Has the Most Data Breach Victims in the World: Between phishing attacks and data base breaches, your personal data is exposed to a constant barrage of unauthorized access. But American internet users have it particularly bad. PCMag, December 30, 2021
LastPass confirms credential stuffing attack against some of its users: Password manager app LastPass said today that a threat actor has launched a credential stuffing attack against its users in an attempt to gain access to their cloud-hosted password vaults. TheRecord, December 28, 2021
Iranian hackers behind Cox Media Group ransomware attack: The ransomware attack that crippled the IT systems and live streams of Cox radio and TV stations earlier this year was the work of Iranian hackers, The Record has learned. TheRecord, December 28, 2021
Cyberattack on one of Norway’s largest media companies shuts down presses: Amedia, the largest local news publisher in Norway, announced on Tuesday that several of its central computer systems were shut down in what it is calling an apparent “serious” cyberattack. TheRecord, December 28, 2021
Photography site Shutterfly is dealing with a ransomware attack: American photography company Shutterfly has experienced a ransomware attack on parts of its networks, the company confirmed in a statement late Sunday night. CyberScoop, December 27, 2021
Criminals have stolen nearly $100 billion in Covid relief funds, Secret Service says: Criminals have stolen close to $100 billion in pandemic relief funds, the U.S. Secret Service said Tuesday. Cnbc, December 21, 2021
Cyber Surveillance
A Digital Manhunt: How Chinese Police Track Critics on Twitter and Facebook: Authorities in China have turned to sophisticated investigative software to track and silence obscure critics on overseas social media. Their targets include college students and non-Chinese nationals. The New York Times, December 31, 2021
“Hacking of my phone is just tip of iceberg,” says Polish opposition politician: A politician whose phone was hacked by military-grade spyware when he was running the opposition’s election campaign says that his case is just “the tip of the iceberg”. He claims that the hacking helped influence the outcome of the election and has called for an official inquiry. Notes From Poland, December 28, 2021
Taking Action Against the Surveillance-For-Hire Industry: Recently, there has been an increased focus on NSO, the company behind the Pegasus spyware (software used to enable surveillance) that we enforced against and sued in 2019. However, NSO is only one piece of a much broader global cyber mercenary industry. Today, as part of a separate effort, we are sharing our findings about seven entities that we removed from our platform for engaging in surveillance activity and we will continue to take action against others as we find them. Meta, December 16, 2021
National Cybersecurity
Security done right: Celebrating infosec wins in 2021: Infosec headlines are typically dominated by data breaches, cyber-attacks, vulnerabilities, and other threats or incidents where human error often has a part to play. The Daily Swig, December 31, 2021
22 cybersecurity statistics to know for 2022: As we usher in the New Year, let’s take a look at some statistics that will help you stay up-to-date on recent cybersecurity trends. WeLiveSecurity, December 30, 2021
6 things in cybersecurity we didn’t know last year: The past 12 months in cybersecurity have been a rough ride. In cybersecurity, everything is broken — it’s just a matter of finding it — and this year felt like everything broke at once, especially toward the end of the year. But for better or worse, we end the year knowing more than we did before. TechCrunch, December 29, 2021
An inside look at how CISA is building an agency for elite cybersecurity talent: Dave Bittner: The Cybersecurity and Infrastructure Security Agency, better known as CISA, was spun up in 2018 operating under the Department of Homeland Security. In July of 2021, Jen Easterly was confirmed by the US Senate as Director of CISA, and under her leadership the organization has continued its efforts toward public-private partnerships in cybersecurity. CISA recently established the Joint Cyber Defense Collaborative, an effort by the agency to lead the development of proactive cyber defense operation plans. Kiersten Todt is Chief of Staff at the Cybersecurity and Infrastructure Security Agency, and she joins us with insights on CISA’s efforts… TheRecord, December 26, 2021
National Cyber Defense
The year the tide turned on ransomware: US authorities scored a handful of rare wins in what once seemed like an unwinnable battle against ransomware. TechCrunch, December 30, 2021
We’re starting to see a national response to ransomware, says Mandiant CEO: As the recent Log4j breach demonstrates, U.S. businesses and government organizations have been taking a pounding from cybercriminals. It’s coming in the form of ransomware, data breaches, distributed denial-of-service (DDoS), and other damaging attacks. CNBC, December 21, 2021
Cyber Misc
University loses 77TB of research data due to backup error: The Kyoto University in Japan has lost about 77TB of research data due to an error in the backup system of its Hewlett-Packard supercomputer. BleepingComputer, December 30, 2021


