Secure The Village
Let’s Build Community: Forty years ago I was part of a team at MITRE with the audacious dream that we might mathematically prove a complex algorithm was secure. … We couldn’t. Stan Stahl, PhD, SecureTheVillage, January 2022
Individuals at Risk
Identity Theft
Scary Fraud Ensues When ID Theft & Usury Collide: What’s worse than finding out that identity thieves took out a 546 percent interest payday loan in your name? How about a 900 percent interest loan? Or how about not learning of the fraudulent loan until it gets handed off to collection agents? One reader’s nightmare experience spotlights what can happen when ID thieves and hackers start targeting online payday lenders. KrebsOnSecurity, January 25, 2022
Your Credit Card is Worth $5.80 on the Dark Web: According to a study by NordVPN of more than 1.5 million American cards for sale on the dark web. Yahoo!Finance, January 28, 2022
Cyber Privacy
Apple publishes new information about AirTags as tracking controversy continues: Apple has updated a “Personal Safety User Guide” amid an ongoing controversy about its AirTags tracking devices. Yahoo!News, January 26, 2022
Cyber Warning
Shipment-Delivery Scams Become the Favored Way to Spread Malware: Attackers increasingly are spoofing the courier DHL and using socially engineered messages related to packages to trick users into downloading Trickbot and other malicious payloads. Threatpost, January 27, 2022
Cyber Defense
Happy Data Privacy Day – and we really do mean “happy”: Loosely speaking, we’re happy to trade information about our own lives in return for insights into, and engagement with, the lives of other people. … And why shouldn’t we? … So here are a few simple tips to help you indulge more safely… Naked Security, January 28, 2022
A Former Hacker’s Guide to Boosting Your Online Security: More stolen personal data is available online than ever before. A man who once ran a website that prosecutors called the Amazon of stolen identity information offers his tips on the best ways to protect your data. ProPublica, January 27, 2022
Cyber Sunshine
73-Year-Old Grandmother Helps Police Catch Scammer: After being contacted by a man claiming to be her grandson who “stated that he was in jail and that she needed to contact his lawyer,” a 73-year-old woman on Long Island aided New York police in arresting the man who allegedly tried to scam her. Newsweek, January 22, 2022
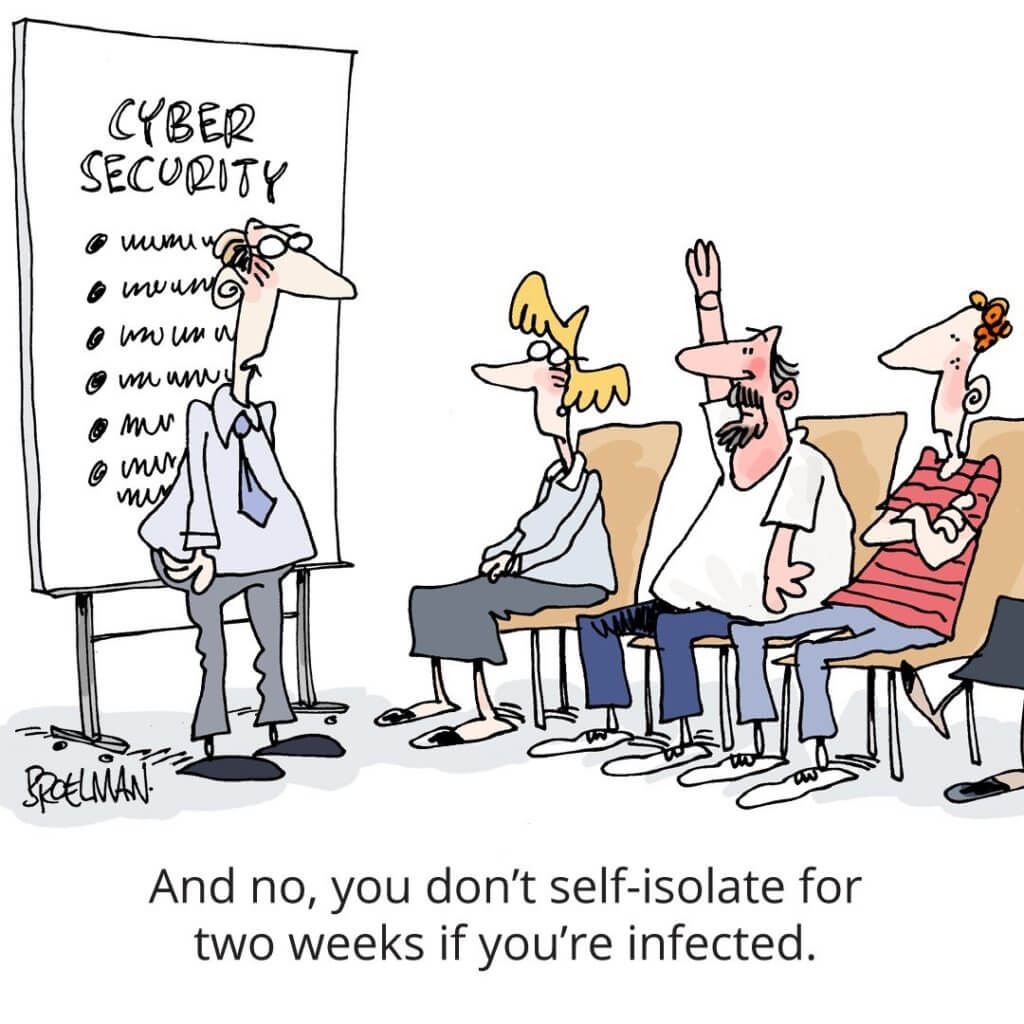
Cyber Humor
Cybersecurity in Society
Cyber Crime
Hackers have stolen $80 million in cryptocurrency from the Qubit DeFi platform: Qubit Finance, a decentralized finance (DeFi) platform, has become the latest victim of a high-value theft, with hackers stealing around $80 million in cryptocurrency on Thursday. The value of cryptocurrency stolen makes this the largest hack of 2022 so far. The Verge, January 28, 2022
‘We’re losing control of our data’ as breaches reach an all-time high: According to the 2021 Annual Data Breach Report published by the Identity Theft Resource Center (ITRC) on Monday, the overall number of data compromises (1,862) is up more than 68% compared to 2020 (1,108). Out of the 1,862 compromises, 1,600 of those were cyberattacks. ZDNet, January 25, 2022
Cyber Attack
Report: DHS Fears Russian Cyberattack If US Acts on Ukraine: Officials Believe Russia Would Consider ‘Cyberattack on Homeland’ If Provoked, BankInfoSecurity, January 24, 2022
Cyber Surveillance
The Battle for the World’s Most Powerful Cyberweapon: A Times investigation reveals how Israel reaped diplomatic gains around the world from NSO’s Pegasus spyware — a tool America itself purchased but is now trying to ban. New York Times, January 28, 2022
F.B.I. Secretly Bought Israeli Spyware and Explored Hacking U.S. Phones: Israel used the NSO Group’s software as a tool of diplomacy. The F.B.I. wanted it for domestic surveillance. Then everything soured. Here are highlights of a New York Times Magazine investigation. New York Times, January 28, 2022
Top Human Rights Watch investigator allegedly hacked with Pegasus spyware: Allegation marks latest example of how NSO clients have used powerful surveillance tool to target campaigners and journalists, The Guardian, January 26, 2022
Cyber Freedom
Myanmar Junta’s New Cyber Law to Jail Anyone Using VPN: The regime is taking steps to permanently undermine internet freedom in the country. The Irrawaddy, January 24, 2022
National Cybersecurity / Cyber Defense
Telecom regulator blocks China Unicom from US market over espionage concerns: The Federal Communications Commission on Thursday voted to ban China Unicom(CHU), a state-owned Chinese telecommunications carrier, from offering telecom services in the United States. CNN Business, January 28, 2022
White House, EPA release 100-day cybersecurity plan for water utility operators: In response to several cyber threats targeting water systems over the past year, the White House, Environmental Protection Agency (EPA) and Cybersecurity and Infrastructure Security Agency (CISA) are rolling out a 100-day plan to improve the cybersecurity of the country’s water systems. ZDNet, January 27, 2022
White House tells agencies to adopt the ‘Zero Trust’ security model: Agencies have 60 days to come up with an implementation plan. Engadget, January 26, 2022
SBA Announces $3 Million in Grants for Small Business Cyber Security: The Small Business Administration (SBA) has announced $3 million in new funding for state governments to assist emerging small businesses develop their cyber security infrastructure. Small Business Trends, January 25, 2022
Know the Enemy
How a Cyber Criminal Justice System Resolves Disputes: The darknet community uses its own underground justice system to solve disputes that arise between one cyber criminal and another. Secvurity Intelligence, January 26, 2022
Cyber Enforcement
$300,000 in fines issued as Canadian officials take down dark web marketplace: Officials said they shut down CanadianHQ, which they claimed was one of the largest Dark Web marketplaces in the world. ZDNet, January 26, 2022
Information Security Management in the Organization
Cybersecurity in the C-Suite & Board
Bosses think that security is taken care of: CISOs aren’t so sure: The World Economic Forum warns about a significant gap in understanding between C-suites and information security staff – but it’s possible to close the gap. ZDNet, January 18, 2022
Information Security Management
NIST releases automation-friendly security and privacy assessment procedures: The National Institute of Standards and Technology (NIST) published Special Publication (SP) 800-53A Revision 5 to correspond with updated information system security and privacy controls, in its latest special publication revision released Tuesday. FEDSCOOP, January 27, 2022
How CISOs are preparing to tackle 2022: To continually understand the priorities and concerns of our community, we run research with security leaders every six months. … The top five challenges shown below, as reported by survey takers, are very consistent with what I’m hearing in my regular interactions with customers and partners. Microsoft, January 25, 2022
Using the NIST Cybersecurity Framework to address organizational risk: NIST’s CSF, used with other guidance, can help map risk to actual threats and better comply with security mandates such as the U.S.’s cybersecurity executive order. CSO, January 25, 2022
22 cybersecurity myths organizations need to stop believing in 2022: Security teams trying to defend their organizations need to adapt quickly to new challenges. Yesterday’s buzzwords and best practices have become today’s myths. CSO, January 24, 2022
2022 Ponemon Cost of Insider Threats Global Report: External attackers aren’t the only threats modern organizations need to consider in their cybersecurity planning. Malicious, negligent and compromised users are a serious and growing risk. As the 2022 Cost of Insider Threats: Global Report reveals, insider threat incidents have risen 44% over the past two years, with costs per incident up more than a third to $15.38 million. Proofpoint, January 25, 2022
CISA Publishes Infographic on Layering Network Security Through Segmentation: CISA has published an infographic to emphasize the importance of implementing network segmentation—a physical or virtual architectural approach that divides a network into multiple segments, each acting as its own subnetwork, to provide additional security and control that can help prevent or minimize the impact of a cyberattack. CISA, January 24, 2022
Cyber Warning
North Korean Hackers Using Windows Update Service to Infect PCs with Malware: The notorious Lazarus Group actor has been observed mounting a new campaign that makes use of the Windows Update service to execute its malicious payload, expanding the arsenal of living-off-the-land (LotL) techniques leveraged by the APT group to further its objectives. The Hacker News, January 28, 2022


