This week’s essential cybersecurity and privacy news for the cyber-aware and the cyber-concerned. Designed to educate, support, and advocate.
Stan’s Corner
From the Center for Cybersecurity Policy and Law comes this warning about the implications of the Supreme Court’s overturning of Chevron. Overturning Chevron means we are going to see judicial attacks on the SEC, FTC, CISA, and other government agencies charged with cybersecurity regulations. It will be up to the next Congress and the next administration to fix the problem. In the meantime, we continue to be at significant disadvantage to our adversaries.
- Chevron Pattern Disrupted: The Impact on Cybersecurity Regulations: On June 28, the Supreme Court struck down a long-standing precedent on the power of federal agencies to interpret and clarify the laws they enforce. The ruling will likely have a sweeping effect on regulations, including cybersecurity rules, in every sector. … The Supreme Court ruling in Loper Bright Enterprises v. Raimondo reversed its seminal decision in Chevron v. Natural Resources Defense Council – the 1984 precedent that called for judges to give deference to federal agencies’ interpretation of laws passed by Congress. This was also known as “Chevron deference” or the “Chevron doctrine.” … This post outlines the implications of this new legal landscape on cybersecurity regulatory efforts, enforcement, and policymaking.
From SecureTheVillage
- Smaller business? Nonprofit? Take your security to the next level. Apply Now! If you’re a small business or nonprofit in the greater Los Angeles area, apply NOW for LA Cybersecure. Protect your organization with our innovative team-based learn-by-doing program with coaching and guidance that costs less than two cups of coffee a week.
- IT Service Provider / MSP? Take your client’s security to the next level. Apply Now! If you’re an IT service provider in the greater Los Angeles area, apply NOW for LA Cybersecure. With our innovative team-based learn-by-doing program, you’ll have both that “seat at the table” and the peace of mind that you’re providing your clients with the IT security management they need.
- The LA Cybersecure Program is funded in part by a grant from the Center for Internet Security (CIS) Alan Paller Laureate Program.
- Family Protection Newsletter: Did you know we created the Family Protection Newsletter for non-cyber experts? For your parents, friends, those who need to protect themselves in a digital world. Sign up or share with a friend! Click here to learn more and quickly add to your free subscription!
- How Hackable Are You? Think your defenses are strong. Find out as SecureTheVillage tests you on five basic controls and download our free updated 13-step guide.
- Please Support SecureTheVillage: We need your help if we’re to build a world of CyberGuardians TM. Please donate to SecureTheVillage. Thank you. It takes a village to secure the village. TM.
Security Nonprofit of the Week … CyberWyoming & CyberWyoming Alliance
Established in 2017, CyberWyoming, a 501(c)6 nonprofit, combats cyber risks for Wyoming businesses. It fosters collaboration among communities, fortifying state and national cybersecurity through tailored economic development and workforce training. Providing consultancy and education services, it integrates cyberpsychology into training for small business stakeholders. The CyberWyoming Alliance, a 501(c)3 nonprofit, headquartered in Laramie, amplifies cybersecurity awareness across local communities. Targeting diverse groups, it secures grants, tailors programs, and establishes information-sharing networks to disseminate crucial cybersecurity updates. This strategic approach reinforces cybersecurity throughout Wyoming, making a significant impact on various demographics and entities. CyberWyoming is a member of Nonprofit Cyber, a coalition of implementation-focused cybersecurity nonprofits including SecureTheVillage.
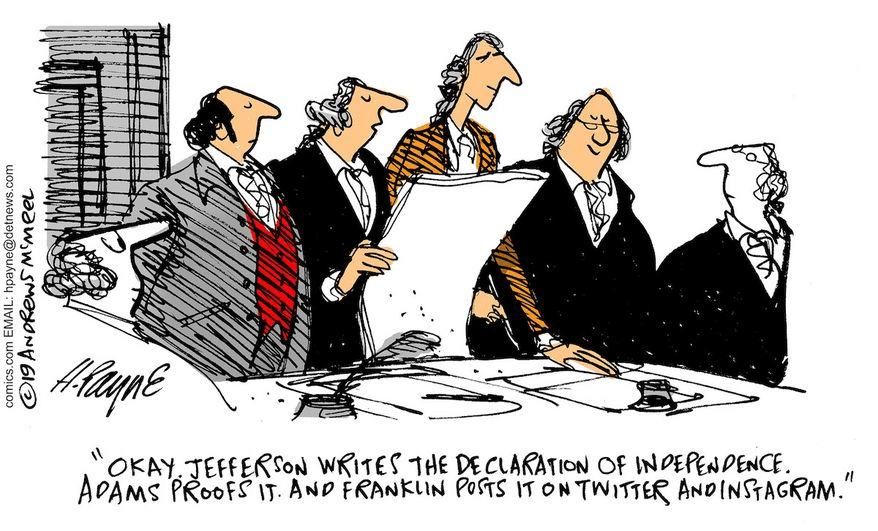
Cyber Humor
Section 2: Let’s Be Careful Out There. And Let’s Help Others Who Aren’t Yet Cyber-Aware.
More warnings. More reminders to help those more vulnerable.
- Romance scams cost consumers $1.14 billion last year. It’s a ‘more insidious’ fraud, expert says: Consumers lost a whopping $1.14 billion to romance scams in 2023, according to the Federal Trade Commission. … “Romance scams tend to be some of the more insidious because they prey on emotions,” said a fraud expert. “These things happen in real life, these aren’t just shows that we see on Netflix.”
- How criminals are exploiting personal information to target vulnerable seniors in elder fraud: Scammers are preying on society’s most vulnerable members. … Scammers are using leaked personal information to rob older Americans of their hard-earned money. … In 2023, people over 60 lost a whopping $3.4 billion to scams, a 10.6% increase from 2022, according to the FBI’s IC3 reports. … Tech support scams are the most common, affecting the most people and causing the biggest financial losses. Other common scams include investment fraud, romance fraud and identity theft.
Another stark reminder to have different passwords for different websites and to use MFA whenever it’s offered.
- RockYou2024: 10 billion passwords leaked in the largest compilation of all time: The largest password compilation with nearly ten billion unique passwords was leaked on a popular hacking forum. The Cybernews research team believes the leak poses severe dangers to users prone to reusing passwords. … “In its essence, the RockYou2024 leak is a compilation of real-world passwords used by individuals all over the world. Revealing that many passwords for threat actors substantially heightens the risk of credential stuffing attacks,” researchers said.
Section 3: Cybersecurity and Privacy News for the Cyber-Concerned.
An important story in The New York Times on attacks on the satellite system that keeps planes in the air and let’s Google Maps guide us to our destination.
- Why GPS Is Under Attack: The Global Positioning System runs the modern world. … But it is under daily attack. …This year alone, researchers say, more than 60,000 commercial flights have been hit by bogus GPS signals, which can confuse pilots. … The American GPS network that was once the gold standard is at risk of becoming a relic as Chinese, Russian and European systems modernize. … Without GPS, much of modern life would falter. Delayed ambulances. Extended power cuts. No cellphone signals. … Yet the U.S. has no civilian backup system.
And this from The Wall Street Journal on tips for staying safe in the world of deepfakes.
- In an Era of Fakes, How to Know When Someone Online Is Real: Some of the old tricks to vet people no longer apply. What to do now. … You’re on Facebook, LinkedIn or X and get a message. Maybe it’s from a stranger in your industry, maybe someone from your hometown claiming to know you from way back when. The person wants to reconnect or get your advice. … This could all be wonderful. Or it could be the start of a scam. … Unfortunately, security experts say, the latter is more likely, because personalized schemes to dupe internet users are on the rise. Trouble is, it is harder than ever to know whether that person showing up in your messages is real or not.
Two stories on the never-ending battle by law enforcement to shut down the cybercriminal gangs that prey on us.
- Europol coordinates global action against criminal abuse of Cobalt Strike: Law enforcement has teamed up with the private sector to fight against the abuse of a legitimate security tool by criminals who were using it to infiltrate victims’ IT systems. Older, unlicensed versions of the Cobalt Strike red teaming tool were targeted during a week of action coordinated from Europol’s headquarters between 24 and 28 June. … Throughout the week, law enforcement flagged known IP addresses associated with criminal activity, along with a range of domain names used by criminal groups, for online service providers to disable unlicensed versions of the tool. A total of 690 IP addresses were flagged to online service providers in 27 countries. By the end of the week, 593 of these addresses had been taken down. … Known as Operation MORPHEUS, this investigation was led by the UK National Crime Agency and involved law enforcement authorities from Australia, Canada, Germany, the Netherlands, Poland and the United States. Europol coordinated the international activity, and liaised with the private partners. This disruptive action marks the culmination of a complex investigation initiated in 2021.
- FBI Offers $10 Million Reward for Capture of Russian Hacker: The FBI have placed a multi-million dollar bounty on the head of a Russian hacker who allegedly targeted the Ukrainian government’s cyber infrastructure in the lead up to the 2022 invasion. … Amin Timovich Stigal is a 22-year old hacker from Grozny in the Chechen Republic. … Between August 2021 and February 2022, Stigal is alleged to have committed “computer intrusions targeting critical Ukrainian critical infrastructure.”
Russia continues to drive disinformation. This story focuses on France. But it’s happening everywhere as Russia continues to interfere wherever it can.
- Russian-linked cybercampaigns put a bull’s-eye on France. Their focus? The Olympics and elections: PARIS (AP) — Photos of blood-red hands on a Holocaust memorial. Caskets at the Eiffel Tower. A fake French military recruitment drive calling for soldiers in Ukraine, and major French news sites improbably registered in an obscure Pacific territory, population 15,000. … All are part of disinformation campaigns orchestrated out of Russia and targeting France, according to French officials and cybersecurity experts in Europe and the United States. France’s legislative elections and the Paris Olympics sent them into overdrive. … More than a dozen reports issued in the past year point to an intensifying effort from Russia to undermine France, particularly the upcoming Games, and President Emmanuel Macron, who is one of Ukraine’s most vocal supporters in Europe. … This story, supported by the Pulitzer Center for Crisis Reporting, is part of an Associated Press series covering threats to democracy in Europe.
This week in cybercrime. More bad news for the automobile industry in the wake of the CDK attack.
- Car dealership losses from CDK software outage could soon reach $1 billion, study finds: Dealerships across the US have seen operations hindered for weeks, with losses mounting. … Direct losses to the auto dealerships impacted by outages at major software provider CDK Global in recent weeks could reach a collective $1 billion if the problems are not fixed soon, according to new data.
- CDK Global faces multiple lawsuits from dealerships crippled by cyberattack: CDK Global faces at least eight lawsuits from auto dealerships over cyberattacks that took down the software provider’s dealer management system, crippling car sellers’ operations. … The plaintiffs, who are employees or customers of car dealerships that use CDK tools, allege CDK did not adequately protect customer data and that the personal information of tens of thousands of people was likely exposed in the hack.
- TeamViewer: Hackers copied employee directory and encrypted passwords: Software company TeamViewer says that a compromised employee account is what enabled hackers to breach its internal corporate IT environment and steal encrypted passwords in an incident attributed to the Russian government.
- Prudential Financial now says 2.5 million impacted by data breach: Prudential Financial, a global financial services company, has revealed that over 2.5 million people had their personal information compromised in a February data breach.
- Patelco Credit Union makes minor restorations but no end near for crippling credit union cyber attack: Patelco Credit Union, after a week of customer lockdowns, made minor restorations in online functions as it reels from an ongoing cyber attack targeting its systems and databases. … This follows the initial June 29 notice from Patelco detailing a lockdown of customers’ accounts, barring anyone from accessing any information about their statement balances, online payments, direct deposits, transfers or other daily functions.
- Hacker group claims it breached Florida Department of Health system, demands payment: A hacker group claims it has breached the Florida Department of Health and gained access to a large amount of potentially sensitive data on Floridians. The RansomHub ransomware group said in a post on the dark web that it will release 100 gigabytes of department data unless the state pays an undisclosed amount of money. A database of all of the state’s payments to contractors in a year takes up about 0.1 gigabytes.
Section 4: Helping Executives Understand Why and Know How.
Here’s an excellent analysis by Sophos showing the value of having information security and IT at the table where business decisions are made. Including information security and IT in discussions about cyber-insurance results in lower insurance costs and improved cybersecurity. That’s a win-win-win.
- Cyber Insurance and Cyber Defenses 2024: Lessons from IT and Cybersecurity Leaders: Investing in cyber defenses to optimize your insurance position is a win-win: organizations report easier, cheaper access to cyber coverage as well as improved protection and a reduction in IT workload. … Cyber risk is inevitable. In today’s business environment, the goal should not be to eradicate risk, but rather to manage it as efficiently as possible. Two primary approaches are treatment by deploying cyber controls and changing user behaviors, and transfer through cyber insurance. These approaches are interconnected: strong controls lower risk which facilitates access to coverage, while weak controls increase risk, making affordable policies harder to obtain. … In the face of inevitable cyberattacks, adopting a holistic approach to cyber risk management that takes advantage of the interplay between cyber defenses and cyber insurance will enable organizations to lower their overall total cost of ownership (TCO) of cyber risk management while reducing their likelihood of experiencing a major incident. … The research also reveals that investing in cyber defenses not only makes getting insurance easier and cheaper but also improves protection and reduces IT workload. This finding further emphasizes the importance of considering cyber risk investments holistically, rather than as individual components.
Section 5: Securing the Technology.
- SaaS Cybersecurity: Threats And Mitigation Strategies: With SaaS solutions, businesses can use scalable and cost-effective software for all kinds of operations, from communication to data analytics, without heavy investment in custom IT infrastructure. Yet turning to third-party service providers always comes with data security risks, and SaaS apps are no exception. According to Statista, in 2023, 43% of respondents mentioned identity and access governance as their main security concern while adopting SaaS. … So, what are the most urgent threats in SaaS, and how can we deal with them? I talked to security experts at Brights, a company specializing in SaaS development, to find out and share with you.
- Juniper releases out-of-cycle fix for max severity auth bypass flaw: Juniper Networks has released an emergency update to address a maximum severity vulnerability that leads to authentication bypass in Session Smart Router (SSR), Session Smart Conductor, and WAN Assurance Router products. … The security issue is tracked as CVE-2024-2973 and an attacker could exploit it to take full control of the device. … “An Authentication Bypass Using an Alternate Path or Channel vulnerability in Juniper Networks Session Smart Router or Conductor running with a redundant peer allows a network-based attacker to bypass authentication and take full control of the device,” reads the description of the vulnerability. … “Only Routers or Conductors that are running in high-availability redundant configurations are affected by this vulnerability,” Juniper notes in the security advisory.


