This week’s essential cybersecurity and privacy news for the cyber-aware and the cyber-concerned. Designed to educate, support, and advocate.
Stan’s Corner
This week saw the release of a ProPublica report on Microsoft’s refusal to fix a critical security flaw at the same time as Microsoft’s President was apologizing for the company’s sorry state of security. Might this be our Unsafe at Any Speed, Ralph Nader’s book that finally brought federal regulation to auto safety?
As two quotes from the ProPublica story demonstrate, from top-to-bottom, throughout the culture, people are disincentivized to prioritize security over functionality. “You will get a promotion because you released the next new shiny thing in Azure. You are not going to get a promotion because you fixed a bunch of security bugs.” Publicly-traded tech giants “are beholden to the share price, not to doing what’s right for the customer all the time. That’s just a reality of capitalism. You’re never going to change that in a public company because at the end of the day, they want the shareholder value to go up.”
Even with Microsoft’s apology and with more companies signing up to CISAs Security by Design program, if history is any guide we are going to confront the question of creating the equivalent of the National Highway Traffic Safety Administration to set and enforce security standards in the computing products we use.
- Microsoft Chose Profit Over Security and Left U.S. Government Vulnerable to Russian Hack, Whistleblower Says: Former employee says software giant dismissed his warnings about a critical flaw because it feared losing government business. Russian hackers later used the weakness to breach the National Nuclear Security Administration, among others. … Microsoft hired Andrew Harris for his extraordinary skill in keeping hackers out of the nation’s most sensitive computer networks. In 2016, Harris was hard at work on a mystifying incident in which intruders had somehow penetrated a major U.S. tech company. … The breach troubled Harris for two reasons. First, it involved the company’s cloud — a virtual storehouse typically containing an organization’s most sensitive data. Second, the attackers had pulled it off in a way that left little trace.
- Microsoft Grilled on Capitol Hill Over Security Failures: Lawmakers asked about a series of recent breaches, the company’s business practices in China. … Microsoft President Brad Smith said the company bears responsibility for a raft of security failures that led to a hack of U.S. government systems last year, and vowed to address them in testimony before Congress on Thursday. … Smith, in an appearance before the House Committee on Homeland Security, said the company accepts the findings of an investigation into its security practices “without equivocation or hesitation.” … “We acknowledge that we can and must do better, and we apologize and express our deepest regrets to those who have been impacted,” he said.
From SecureTheVillage
- Smaller business? Nonprofit? Take your security to the next level. Apply Now! If you’re a small business or nonprofit in the greater Los Angeles area, apply NOW for LA Cybersecure. Protect your organization with our innovative team-based learn-by-doing program with coaching and guidance that costs less than two cups of coffee a week.
- IT Service Provider / MSP? Take your client’s security to the next level. Apply Now! If you’re an IT service provider in the greater Los Angeles area, apply NOW for LA Cybersecure. With our innovative team-based learn-by-doing program, you’ll have both that “seat at the table” and the peace of mind that you’re providing your clients with the IT security management they need.
- The LA Cybersecure Program is funded in part by a grant from the Center for Internet Security (CIS) Alan Paller Laureate Program.
- Family Protection Newsletter: Did you know we created the Family Protection Newsletter for non-cyber experts? For your parents, friends, those who need to protect themselves in a digital world. Sign up or share with a friend! Click here to learn more and quickly add to your free subscription!
- How Hackable Are You? Think your defenses are strong. Find out as SecureTheVillage tests you on five basic controls and download our free updated 13-step guide.
- Please Support SecureTheVillage: We need your help if we’re to build a world of CyberGuardians TM. Please donate to SecureTheVillage. Thank you. It takes a village to secure the village. TM.
Cybersecurity Nonprofit of the Week … The CyberPeace Institute
Kudos this week to the CyberPeace Institute, an independent and neutral nongovernmental organization whose mission is to ensure the rights of people to security, dignity and equity in cyberspace. The CyberPeace Institute is home to the Humanitarian Cybersecurity Center (HCC). The HCC provides expert support and practical free cyber assistance to non-governmental Organizations (NGOs), tailored to their needs and located anywhere in the world. Through its Cyber Attacks in Times of Conflict Platform #Ukraine, the CyberPeace Institute is tracking cyberattacks and operations targeting critical infrastructure and civilian objects in Ukraine. The CyberPeace Institute is a member of Nonprofit Cyber, a coalition of implementation-focused cybersecurity nonprofits including SecureTheVillage.
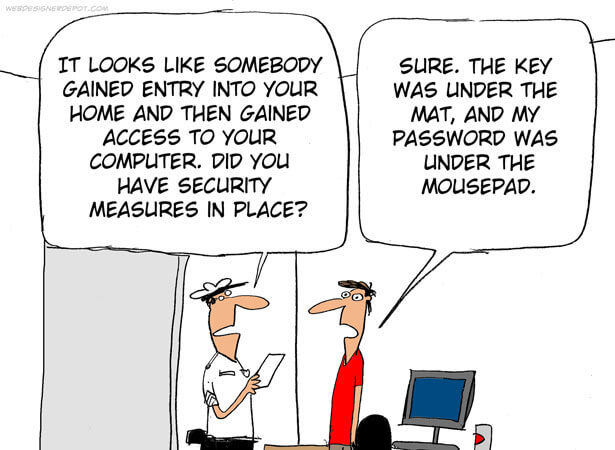
Cyber Humor
Section 2: Let’s Be Careful Out There. And Let’s Help Others Who Aren’t Yet Cyber-Aware.
Update now.
- ASUS warns of critical remote authentication bypass on 7 routers: ASUS has released a new firmware update that addresses a vulnerability impacting seven router models that allow remote attackers to log in to devices. … The flaw, tracked as CVE-2024-3080 (CVSS v3.1 score: 9.8 “critical”), is an authentication bypass vulnerability allowing unauthenticated, remote attackers to take control of the device.
- Apps that steal bank info among 90+ malicious downloads in Google Play store: study: Have an Android device? It might be time for a wellness check. … Security experts at Zscaler announced recently that they have found more than 90 malicious apps in the Google Play store. All told, the apps have been installed more than 5.5 million times, according to Zscaler ThreatLabz. … For Android users who may have unknowingly downloaded the apps, ThreatLabz mentioned one rising danger in particular, the Anatsa malware, also called TeaBot. Anatsa is built to access people’s banking information from hundreds of financial applications around the world.
- Google just gave Pixel owners 50 reasons to update their smartphone — don’t sleep on these patches: If you own a Pixel smartphone, you’re going to want to install the latest updates as soon as possible because Google has just fixed 50 security flaws—including one that’s being used by hackers in their attacks as a zero-day.
Another reason to be careful shopping online. The store you’re visiting may be a clone of the store you want.
- Scammers’ New Way of Targeting Small Businesses: Impersonating Them: Copycats are using videos and photos to pose as real small-business owners and dupe their customers. … Copycats are stepping up their attacks on small businesses. … Sellers of products including merino socks and hummingbird feeders say they have lost customers to online scammers who use the legitimate business owners’ videos, logos and social-media posts to assume their identities and steer customers to cheap knockoffs or simply take their money.
Section 3: Cybersecurity and Privacy News for the Cyber-Concerned.
AI is in the news in support of attackers and defenders
- GPT-4 autonomously hacks zero-day security flaws with 53% success rate: Researchers were able to successfully hack into more than half their test websites using autonomous teams of GPT-4 bots, co-ordinating their efforts and spawning new bots at will. And this was using previously-unknown, real-world ‘zero day’ exploits.
- AI Chatbot Fools Scammers & Scores Money-Laundering Intel: Experiment demonstrates how AI can turn the tables on cybercriminals, capturing bank account details of how scammers move stolen funds around the world.
Vermont’s proposed privacy bill was vetoed by the Governor.
- Despite broad support in the Legislature, Gov Phil Scott vetoes Vermont data privacy legislation: Supporters of the bill suggested that tech industry lobbyists had spread misinformation to scuttle it.
This week in cybercrime. Governments fighting ransomware. A $20 million crypto-hack. And an allegation which, if confirmed, could be the largest single loss of sensitive private information.
- Cleveland City Hall confirms it was hit with ransomware attack: After a week with sparse details, and cryptic references to a “cyber incident” at City Hall, Cleveland officials on Friday admitted that city government systems were hit with a ransomware attack.
- Grand Traverse County law enforcement adjusts to loss of systems during cyber attack: Grand Traverse County and the city of Traverse City are continuing their investigations into Wednesday’s ransomware attack, with help from the FBI and Michigan State Police. … The county said it detected “network irregularities” at 6:06 a.m. on Wednesday. … The county’s IT department and leadership then took county and Traverse City offices offline out of precaution.
- City of Newburgh offices at City Hall and on Grand Street will reopen Monday: City Hall and city offices at 123 Grand St. will reopen at 9 a.m. Monday. … The offices have been closed since this past Monday due to what the city said was a network security incident.
- Crypto platform UwU Lend dealing with $20 million theft: The UwU Lend crypto platform says it has made an offer to a hacker behind the theft of nearly $20 million worth of ETH. … Early on Monday, several blockchain security companies reported an issue with the platform, warning that someone appeared to be siphoning what amounted to $19.3 million worth of ETH.
- The mystery of an alleged data broker’s data breach: Since April, a hacker with a history of selling stolen data has claimed a data breach of billions of records — impacting at least 300 million people — from a U.S. data broker, which would make it one of the largest alleged data breaches of the year.
Section 4: Helping Executives Understand Why and Know How.
Change Healthcare’s breach has several lessons of interest.
- 8 critical lessons from the Change Healthcare ransomware catastrophe: From fundamental security mistakes and strategic shortcuts, to emerging industry trends, Change Healthcare’s security meltdown provides ample fodder for thought on how not to be the next high-profile victim.
Section 5: For Information Security Managers
The Snowflake story provides several critical security suggestions for information security managers, including IT Service Providers / MSPs who manage the security of their clients. The story outlines Mandiant’s report documenting numerous weaknesses by Snowflake and its customers. The following from Mandiant’s report is of particular interest to MSPs, “In several Snowflake related investigations, Mandiant observed that the initial compromise of infostealer malware occurred on contractor systems that were also used for personal activities, including gaming and downloads of pirated software. ” The computers you and your people use to access client systems must be properly secured and protected!
- Hackers steal “significant volume” of data from hundreds of Snowflake customers: Given shortcomings of Snowflake and its customers, there’s plenty of blame to go around. … As many as 165 customers of cloud storage provider Snowflake have been compromised by a group that obtained login credentials through information-stealing malware, researchers said Monday. … On Friday, Lending Tree subsidiary QuoteWizard confirmed it was among the customers notified by Snowflake that it was affected in the incident. Lending Tree spokesperson Megan Greuling said the company is in the process of determining whether data stored on Snowflake has been stolen.


