A weekly aggregation of important cybersecurity and privacy news designed to educate, support, and advocate; helping you meet your data care challenges and responsibilities.
Stan’s Top of the News
Our lead stories this week are privacy stories engendered by the Supreme Court’s decision to overturn Roe v Wade.
The first two stories deal with how privacy rights will or will not be protected in the months and years ahead.
- It’s not just period trackers: The post-Roe digital data dragnet is bigger than you think: As states move to ban abortion, digital footprints could prove a new risk to people seeking to terminate pregnancies. … The fall of Roe v. Wade will let states limit or ban abortion — and one big unanswered question is what role technology will play in how those new rules are enforced. The Grid, June 24, 2022
- Big Tech silent on data privacy in post-Roe America: Period- and fertility-tracking apps have become weapons in Friday’s post-Roe America. … These seemingly innocuous trackers contain tons of data about sexual history, menstruation and pregnancy dates, all of which could now be used to prosecute women seeking abortions — or incite digital witch hunts in states that offer abortion bounties. … Under a law passed last year in Texas, any citizen who successfully sues an abortion provider, a health center worker, or anyone who helps someone access an abortion after six weeks can claim at least $10,000, and other US states are following that example. The Register, June 24, 2022
This next story looks at the other side of the coin; access to information in the post-Roe America.
- The brewing fight to keep abortion info online: Yesterday, the Supreme Court voted to uphold a Mississippi abortion ban and overturn Roe v. Wade, ending abortion access in some states and triggering impending bans in others. The decision won’t end abortion in America, but in many places it will move the procedure underground and, based on recent history, online. … Understandably, abortion advocates have focused on surveillance issues in the immediate aftermath of the ruling, concerned about states using online records for criminal prosecutions. But there’s also a fight brewing over how and where advocates will be able to share abortion information online. If a procedure is illegal, then states could claim content enabling that procedure is illegal too — raising thorny questions for platforms and activists alike. The Verge, June 25, 2022
Scientific American weighs in here as well on the subject of misinformation and disinformation
- How Abortion Misinformation and Disinformation Spread Online: How Abortion Misinformation and Disinformation Spread Online. … The Supreme Court’s decision to curtail abortion rights has come to fruition. One of the outcomes that will be less discussed is how more people in states with heavy restrictions will turn to search engines and social media to figure out how now to manage their reproductive decisions, and will find themselves reading questionable information. The information they’ll find could be questionable; the number of false and misleading statements online about abortion has grown since the draft opinion on Dobbs v. Jackson Women’s Health Organization was leaked in May, and with the decision now handed down, it will undoubtedly increase. Scientific American, June 24, 2022
And finally, the New York Times gives us a stark reminder of China’s surveillance of its people where there is little to no privacy.
- ‘An Invisible Cage’: How China Is Policing the Future: The more than 1.4 billion people living in China are constantly watched. They are recorded by police cameras that are everywhere, on street corners and subway ceilings, in hotel lobbies and apartment buildings. Their phones are tracked, their purchases are monitored, and their online chats are censored. … Now, even their future is under surveillance. The New York Times, June 25, 2022
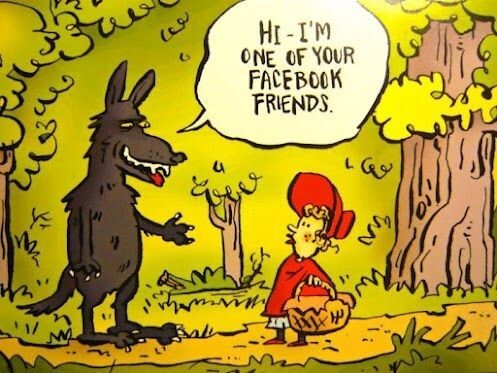
Cyber Humor
Security Nonprofit of the Week … Auto-ISAC
One of several Information Sharing and Analysis Centers (ISACs), the Auto-ISAC was formed in August 2015 by automakers to establish a global information sharing community to address vehicle cyber security risks. Auto-ISAC operates a central hub for sharing, tracking and analyzing intelligence about cyber threats, vulnerabilities and incidents related to the connected vehicle. Currently, Auto-ISAC Members account for more than 99 percent of light-duty vehicles in North America, with over 30 global OEM and supplier Members. Building upon the success of this collaboration, Auto-ISAC recently expanded membership to heavy trucking OEMs and their suppliers, as well as the commercial vehicle sector—including fleets and carriers.
Live on Cyber with Dr. Stan Stahl – Live on LinkedIn

Live on Cyber with Dr. Stan Stahl: Join Julie Morris and me as we riff on Kiersten Todt’s observation that we included in last week’s Cyber News. The cause of ransomware is that we’re not doing a better job of truly making companies more resilient. You know we’re talking about basic cyber-hygiene … multi factor authentication, backups, encryption. So we’ve got to get to where we can raise the bar in security so that industry is doing a better so that ransomware isn’t an issue. We talk basic data care hygiene. What it is. And several nonprofits that can help you achieve it. SecureTheVillage, June 23, 2022, 2022
Section 2 – Personal Data Care – Security and Privacy
Important data care stories for protecting yourself and your family.
#BeCarefulOutThere.
- The volume of my emails and text messages shot up dramatically after Roe v Wade was overturned. It seemed that every political organization having my contact information had something to say and wanted my money to support “the cause.” What an opportunity for fraud!!! Never trust a link in an email or text message. If the cause sounds like something you want to support, find and investigate it’s website, and even double-check that. #NeverTrust.#AlwaysVerify.
Fraud is back in the news again this week with another story of banks’ unwillingness to pay for Zelle-type fraud.
- When Customers Say Their Money Was Stolen on Zelle, Banks Often Refuse to Pay: Federal law requires banks to reimburse customers for unauthorized electronic transfers, but they often refuse, stranding victims. … Argelys Oriach was on his way home from a shopping trip one evening in March when he was robbed at gunpoint. The thief demanded his iPhone and passcode. Mr. Oriach turned them over and fled. … The next morning, Mr. Oriach … said he discovered that the thief had drained $8,294 from his bank accounts at Capital One, using multiple money transfer apps including Zelle. He contacted Capital One, fully expecting the bank to refund him the stolen cash, as required by federal law. The bank refunded only $250, saying it found no evidence that the rest of the money was stolen. Mr. Oriach was stunned. The New York Times, June 21, 2022
Section 3 – General Data Care, Cybersecurity, and Privacy Stories
Data Care, cybersecurity and privacy stories for those wanting a deeper look.
The Washington Post’s Cybersecurity 202 analyst, Joseph Marks is leaving. This is is his last column where he writes cybersecurity has “gone from a relatively back-burner issue embraced by a handful of government officials and lawmakers to a top national security concern. … that’s probably just the beginning. Things will definitely get wilder from here.” Marks leaves us with three big themes that have preoccupied his reporting the past eight years along with their likely trajectory.
- Cybersecurity’s bad and it’s getting worse: There are few analogues in history for how cybersecurity has surged in importance as a government policy issue during the past eight years. Washington Post, June 24, 2022
The following stories illustrate Marks’ point.
- How Russia’s vaunted cyber capabilities were frustrated in Ukraine: A quiet partnership of the world’s biggest technology companies, U.S. and NATO intelligence agencies, and Ukraine’s own nimble army of hackers has pulled off one of the surprises of the war with Russia, largely foiling the Kremlin’s brazen internet hacking operations. Washington Post, June 21, 2022
- Microsoft: Russian cyber spying targets 42 Ukraine allies: Coinciding with unrelenting cyberattacks against Ukraine, state-backed Russian hackers have engaged in “strategic espionage” against governments, think tanks, businesses and aid groups in 42 countries supporting Kyiv, Microsoft said in a report Wednesday. AP News, June 22, 2022
- US disrupts Russian botnet that ‘hacked millions of devices’: The US Department of Justice (DoJ) has dismantled the infrastructure of what it described as a Russian botnet consisting of millions of hacked Internet of Things (IoT) devices. ZD Net, June 20, 2022
- Russian emails appear to show ‘network’ holding $4.5bn assets linked to Putin: Palaces, yachts and vineyards reportedly provided to Vladimir Putin by friends and oligarchs can now be linked to what appears to be an informal network holding assets worth more than $4.5bn (£3.7bn). The Guardian, June 20, 2022
The following two stories perhaps serve to bookend our challenges. The first details an obscenely large crypto-crime likely brought on by users who had gotten hacked. The second tells the story of an entire city in Japan put at grave risk because of what can only be described as careless negligence. Can anyone say “DATA CARE?”
- Hacker exploits Harmony blockchain bridge, loots $100M in crypto: A hacker has exploited a vulnerability to steal $100 million from Harmony’s Horizon Bridge, which allows users to transfer their crypto assets from one blockchain to another. Tech Crunch, June 24, 2022
- Japanese man loses USB stick with entire city’s personal details: For many, after-work drinks are a common way of relaxing after a busy week. But one worker in Japan could be nursing a protracted hangover after he lost a USB memory stick following a night out with colleagues. The man reportedly spent several hours drinking in a local restaurant before he lost the memory stick. BBC, June 24, 2022
I’m sure none of us are surprised to discover that the cybercriminals continue to up their game.
- Conti ransomware hacking spree breaches over 40 orgs in a month: The Conti cybercrime syndicate runs one of the most aggressive ransomware operations and has grown highly organized, to the point that affiliates were able to hack more than 40 companies in a little over a month. Bleeping Computer, June 23, 2022
- We’re now truly in the era of ransomware as pure extortion without the encryption: Why screw around with cryptography and keys when just stealing the info is good enough. The Register, June 25, 2022
- These hackers are spreading ransomware as a distraction – to hide their cyber spying: A group of likely state-backed cyber attackers have adopted a new loader to spread five different kinds of ransomware in a bid to hide their true espionage activities. ZD Net, June 23, 2022
- Ransomware attacks: This is the data that cyber criminals really want to steal: There are certain types of data that criminals target the most, according to an analysis of attacks. ZD Net, June 20, 2022
Meanwhile the growth of cybercrime means the cyber insurance industry faces “catastrophic financial loss” unless something changes; like their business model.
- Businesses risk ‘catastrophic financial loss’ from cyberattacks, US watchdog warns: Private insurance companies increasingly limit coverage against major cyber threats, per a report from the GAO. … A government watchdog has warned that private insurance companies are increasingly backing out of covering damages from major cyberattacks — leaving American businesses facing “catastrophic financial loss” unless another insurance model can be found. The Verge, June 23, 2022
Back on the surveillance front, we have two stories this week. NSO Group is as bad as we thought. And they’re not alone.
- Pegasus used by at least 5 EU countries, NSO Group tells lawmakers: NSO Group ‘made mistakes,’ its chief lawyer says. … The Israeli spyware firm NSO Group on Tuesday told European lawmakers at least five EU countries have used its software and the firm has terminated at least one contract with an EU member country following abuse of its Pegasus surveillance software. Politico, June 21, 2022
- Apple and Android phones hacked by Italian spyware, Google says: An Italian company’s hacking tools were used to spy on Apple and Android smartphones in Italy and Kazakhstan, Alphabet’s Google said in a report on Thursday. … Milan-based RCS Lab, whose website claims European law enforcement agencies as clients, developed tools to spy on private messages and contacts of the targeted devices, the report said. CNN Business, June 23, 2022
Meanwhile, back in Washington, while the Administration, NIST, CISA, Justice and other Agencies are all aggressively moving forward to defend the nation, the Legislative wheels continue to move slower than maple sap in Vermont in December. At least we got two important bills through the system this week.
- Biden signs cyber bills into law: President Biden on Tuesday signed two bipartisan bills into law aimed at enhancing federal, state and local governments’ cybersecurity measures. The Hill, June 21, 2022
Section 4 – Data Care in the Organization
Stories to support executives and top management in securing their organizations.
We highlight four stories that top security management will want to review. In the first, the experts at Gartner offer strategic recommendation for navigating the expected evolving information security and privacy landscape.
- Gartner Unveils the Top Eight Cybersecurity Predictions for 2022-23: Analysts Explore the Future of Cybersecurity at the Gartner Security & Risk Management Summit, June 21-22 in Sydney. Executive performance evaluations will be increasingly linked to ability to manage cyber risk; almost one-third of nations will regulate ransomware response within the next three years; and security platform consolidation will help organizations thrive in hostile environments, according to the top cybersecurity predictions revealed by Gartner, Inc. today. Gartner, June 21, 2022
Our second story is of concern to every risk manager who owns a cyber-insurance policy. Over the years I’ve had the dubious pleasure of reading a lot of the fine print in a number of security policies in an attempt to help clients sort out exactly what’s covered and what isn’t. I’m very qualified to do this analysis, by virtue both of my in-the-trenches 40+-years experience in information security management and my mathematics PhD in the field of logic. That said, the fine print often makes getting a logically coherent understanding of the specifics of what’s covered and what’s not is impossible. And when I’ve asked brokers what this or that means, all I commonly get are ‘deer in the headlight” stares and a lot of blah-blah-blah. So don’t take it for granted that you’re getting the coverage you need. This problem will only get worse as insurance companies are tightening the qualifications for insurance, as we discussed in our story above.)
- Do You Have Ransomware Insurance? Look at the Fine Print: Insurance exists to protect the insured party against catastrophe, but the insurer needs protection so that its policies are not abused – and that’s where the fine print comes in. However, in the case of ransomware insurance, the fine print is becoming contentious and arguably undermining the usefulness of ransomware insurance. The Hacker News, June 20, 2022
Our next story, from the World Economic Forum, gives high-level guidance on testing your incident response plans. It offers excellent recommendations and should be read by senior information security managers (CISOs and equivalent) and the executives to whom the senior information security manager reports (CFOs. COOs, Chief Legal Officers, Chief Risk Officers, CEOs etc). We can’t emphasize enough the importance of training, testing, and table-top exercises in ensuring your plan will work as needed when it’s needed. Take it with the seriousness given to active-shooter drills.
- 6 steps to validate cyber incident response plans in times of conflict: Should the worst occur, cyber incident response plans can help mobilize resources, contain the attack, mitigate damages and expedite recovery. … Cyber attacks have become a widespread risk to governments and businesses. … During times of conflict, such as Russia’s invasion of Ukraine, these risks become amplified. … Here are key things to consider when evaluating cyber incident response capabilities. World Economic Forum, June 22, 22
Deeper in the trenches is guidance from CISA on how to safely use Windows Power Shell.
- Keeping PowerShell: Measures to Use and Embrace: Cybersecurity authorities from the United States, New Zealand, and the United Kingdom have released a joint Cybersecurity Information Sheet (CIS) on PowerShell. The CIS provides recommendations for proper configuration and monitoring of PowerShell, as opposed to removing or disabling it entirely due to its use by malicious actors after gaining access into victim networks. These recommendations will help defenders detect and prevent abuse by malicious cyber actors, while enabling legitimate use by administrators and defenders. … CISA urges organizations to review Keeping PowerShell: Measures to Use and Embrace and take actions to strengthen their defenses against malicious cyber activity. CISA, June 22, 2022


