Individuals at Risk
Cyber Privacy
Robocalls are out of control. But that could change after June 30: Voice providers have just days to implement the Stir/Shaken tech designed to curb annoying and costly robocalls. CNet, June 26, 2021
Cyber Defense
How to tell if a website is safe: It can be difficult to tell a legitimate website apart from an unsafe one – follow these steps to identify and protect yourself from bad websites. WeLiveSecurity, June 23, 2021
Apple publishes new user guide detailing how sideloading and third-party app stores would undermine iPhone security: Apple has just published a new user guide that details what life would be like for iOS users if Apple were forced to allow the sideloading of third-party apps. The report, which was published this morning, is called Building a Trusted Ecosystem for Millions of Apps and describes Apple’s view on the importance of having a curated and managed App Store be the only way that iOS devices can download new apps. 9to5Mac, June 23, 2021
Cyber Update
30M Dell Devices at Risk for Remote BIOS Attacks, RCE: Four separate security bugs would give attackers almost complete control and persistence over targeted devices, thanks to a faulty update mechanism. ThreatPost, June 24, 2021
Cyber Warning
“I’m totally screwed.” WD My Book Live users wake up to find their data deleted: Storage-device maker advises customers to unplug My Book Lives from the Internet ASAP. ars technica, June 24, 2021
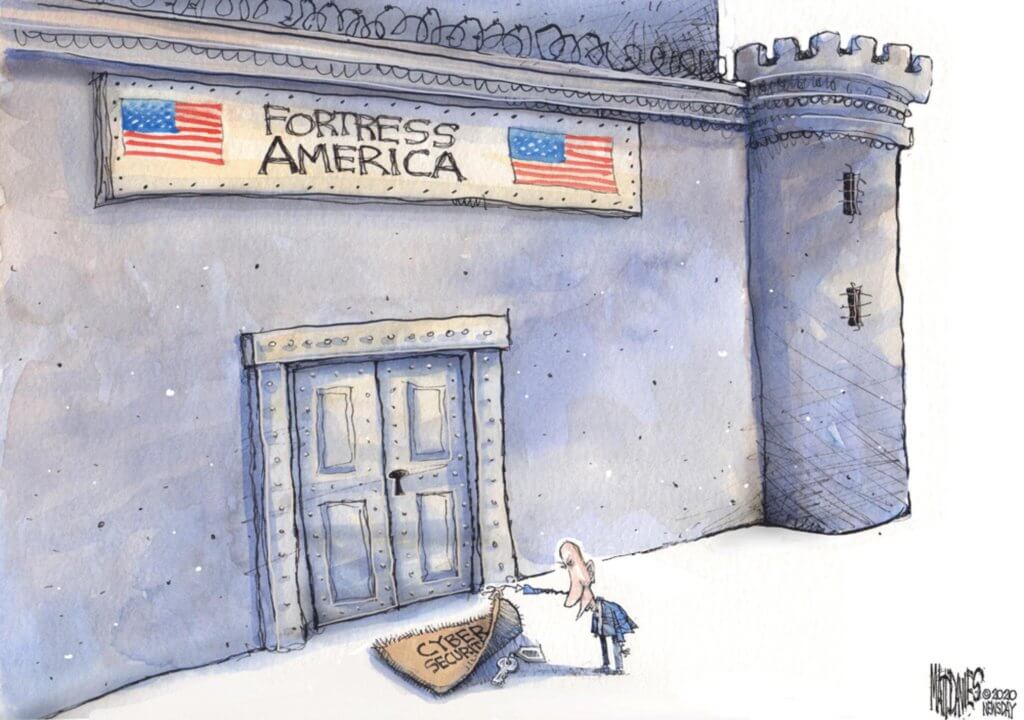
Cyber Humor
Information Security Management for the Organization
Information Security Management
7 Unconventional Pieces of Password Wisdom: Challenging common beliefs about best practices in password hygiene. DarkReading, June 25, 2021
Using VMs to hide ransomware attacks is becoming more popular: In early 2020, security researchers were baffled to discover that a ransomware gang had come up with an innovative trick that allowed it to run its payload inside virtual machines on infected hosts as a technical solution that bypassed security software. TheRecord, June 25, 2021
74% of Q1 Malware Was Undetectable Via Signature-Based Tools: Attackers have improved on tweaking old malware to continue sneaking it past traditional threat detection controls, researchers report. DarkReading, June 25, 2021
D3FEND KNOWLEDGE GRAPH GUIDES SECURITY ARCHITECTS TO DESIGN BETTER CYBER DEFENSES: MITRE is looking for help from the cybersecurity community to build out an NSA-funded framework for network defense. The goal is to help security architects quickly understand the specific capabilities of a wide variety of defensive technologies. MITRE, June 2021
Updates to the CIS Controls and Free Microsoft 365 Assessment Workbook: I know my community is already familiar with the CIS Critical Security Controls, as well as the free assessment workbook that I adapted from AuditScripts to apply to Microsoft 365 environments. This week, the Center for Internet Security released updates to the framework (we are now on v8). You can download the new controls here, and if you want to see the recent webinar covering these updates, go here. REgarding 365, May 20, 2021
Cybersecurity in Society
Cyber Crime
Malware author made $2 million after infecting 222,000 Windows systems: The operator of a malware strain known as Crackonosh has made more than 9,000 Monero coins (estimated today at around $2 million) after infecting more than 222,000 Windows computers since 2018. TheRecord, June 24, 2021
The human cost of ransomware: Irish healthcare disruption will continue for months: The attack has been attributed to the Conti ransomware gang. The cyber criminals provided HSE with a decryption tool for free but have threatened to publish information stolen in the attack – potentially a violation of patient privacy – if they don’t receive a ransom of a reported $20 million in bitcoin, something that HSE vowed not to pay. But even with the correct decryption key, restoring the network has been a slow and arduous task for HSE. Health services across Ireland remain disrupted as hospitals attempt to treat patients, despite limited IT services and no internet access – meaning appointments are still being delayed or cancelled. Bollyinside, June 24, 2021
Have we reached peak ransomware? How the internet’s biggest security problem has grown and what happens next: A string of high-profile cyberattacks has made ransomware an impossible issue to ignore – in fact, even world leaders are talking about it. Will this be enough to make cyber criminals think twice? ZDNet, June 22, 2021
Cyber Privacy
Dutch consumer group demands TikTok pay €1.5 billion: For the second time this month, the video-sharing platform TikTok faces demands to pay more than €1 billion. The company has come under heavy scrutiny for its privacy regulations. DW, June 24, 2021
Banning Surveillance-Based Advertising: The Norwegian Consumer Council just published a fantastic new report: “Time to Ban Surveillance-Based Advertising.” Schneier on Security, June 24, 2021
Supply Chain Security
Microsoft admits to signing rootkit malware in supply-chain fiasco: Microsoft has now confirmed signing a malicious driver being distributed within gaming environments. BleepingComputer, June 26, 2021
Microsoft says its customer support tools were compromised by the SolarWinds hackers: It says the group used the tools for targeted attacks. The Verge, June 24, 2021
The Power of Anonymity in Supply Chain Security: The SolarWinds breach of 2020 was widely considered the biggest cyber-attack in history. Just three months later, the Microsoft Exchange hack took its place. Both had far-reaching consequences that affected not only SolarWinds and Microsoft, but also their customers, partners, and vendors. The shift toward large-scale hacks on software vendors should serve as a warning to businesses of all sizes: hackers do not need to hack your business directly to breach your business. Info Security Magazine, June 24, 2021
Cyber Defense
Amazon launching global competition to find and fix 1 million software bugs: Participants in AWS BugBust can win a free trip to AWS re:Invent 2021 in Las Vegas. ZDNet, June 24, 2021
Secretary Mayorkas, Mayor Garcetti Visit LA Cyber Lab: LOS ANGELES – Yesterday, Secretary of Homeland Security Alejandro N. Mayorkas and Mayor of Los Angeles Eric Garcetti visited the Los Angeles Cyber Lab and received a briefing on its operational capabilities. The Cyber Lab is a prime example of how a public-private partnership can shore up our cyber defenses across every level of government as called for by President Biden. Homeland Security, June 11, 2021
Know Your Enemy
Clop Gang Partners Laundered $500 Million in Ransomware Payments: The cybercrime ring that was apprehended last week in connection with Clop (aka Cl0p) ransomware attacks against dozens of companies in the last few months helped launder money totaling $500 million for several malicious actors through a plethora of illegal activities. The Hacker News, June 24, 2021
State‑sponsored or financially motivated: Is there any difference anymore?: What does the increasingly fuzzy line between traditional cybercrime and attacks attributed to state-backed groups mean for the future of the threat landscape? WeLiveSecurity, June 22, 2021
This secretive firm has powerful new hacking tools: Mollitiam Industries claims to have created hackings tools that can take control of smartphones and laptops. Wired, June 15, 2021
National Cybersecurity
The National Guard Just Simulated A Cyberattack That Brought Down Utilities Nationwide: This year’s Cyber Yankee exercises simulated the increasingly likely scenario of cyberattacks crippling huge sections of the nation’s infrastructure. The Drive, June 23, 2021
Secretive NSA opens doors to new “collaboration center” as cyberthreats mount: Fort Meade, Maryland — One of the most notoriously secretive U.S. intelligence agencies has opened a new facility that it hopes, uncharacteristically, will welcome plenty of outside visitors. CBS, June 23, 2021
Pressure Grows for Federal Data Breach Legislation: Even as cybersecurity grows in importance as a national priority, individual states continue to push ahead with their own data breach legislation, making for an increasingly complicated compliance landscape for cybersecurity managers. DataCenter Knowledge, June 22, 2021
The Cybersecurity 202: Defense contractors are yet another sector highly vulnerable to hacking, study finds: Defense contractors are highly vulnerable to ransomware and similar cyberattacks that have been roiling other critical industry sectors, a report out today finds. Washington Post, June 22, 2021
Cyber Law
Class action targets Scripps over data breach that exposed 147,000+ patients’ info: Scripps Health is being accused of failing to properly secure and protect patients’ health information stored within the San Diego-based system’s network, which a malware attack compromised April 29, according to court documents. HealthIT, June 22, 2021
Cyber Regulation
SEC Probes SolarWinds Customers on Data Breach Disclosures: The Securities and Exchange Commission is looking into whether some companies hit by the SolarWinds Orion cyberattack failed to divulge the breach as legally required, Reuters reported. MSSP, June 25, 2021
Critical Infrastructure
How Cyber Safe is Your Drinking Water Supply?: Amid multiple recent reports of hackers breaking into and tampering with drinking water treatment systems comes a new industry survey with some sobering findings: A majority of the 52,000 separate drinking water systems in the United States still haven’t inventoried some or any of their information technology systems — a basic first step in protecting networks from cyberattacks. KrebsOnSecurity, June 21, 2021
Cyber Enforcement
High-Ranking FIN7 Gang Member Receives 7-Year Prison Term: Prosecutors Say Andrii Kolpakov Was a ‘Pen Tester’ for Payment Card Theft Group. BankInfoSecurity, June 25, 2021
How Cyber Sleuths Cracked an ATM Shimmer Gang: In 2015, police departments worldwide started finding ATMs compromised with advanced new “shimming” devices made to steal data from chip card transactions. Authorities in the United States and abroad had seized many of these shimmers, but for years couldn’t decrypt the data on the devices. This is a story of ingenuity and happenstance, and how one former Secret Service agent helped crack a code that revealed the contours of a global organized crime ring. KrebsOnSecurity, June 23, 2021
Instructions Show How Cops Use GrayKey to Brute Force iPhones: Newly released documents provide new insight into the capabilities of the iPhone unlocking tech. Vice, June 22, 2021
Cyber Misc
Exclusive: Hacker reveals smart meters are spilling secrets about the Texas snowstorm: Power companies won’t disclose who was protected from blackouts—but smart meters may be leaking insights. Daily Dot, June 24, 2021


