This week’s essential cybersecurity and privacy news for the cyber-aware and the cyber-concerned. Designed to educate, support, and advocate.
Stan’s Top of the News
United Health is back at the Top of the News this week as the health industry continues to dig out from the cyberattack. The great concern is for the patients unable to get their prescriptions filled and the smaller independent healthcare practices struggling to pay their bills.
- UnitedHealth unit will start processing $14 billion medical claims backlog after hack: UnitedHealth Group said on Friday its Change Healthcare unit will start to process the medical claims backlog of more than $14 billion as it resumes some software services disrupted by a cyberattack last month. … The company has been scrambling to resume services at the technology unit that was hit by a cyberattack on Feb. 21, disrupting payments to U.S. doctors and healthcare facilities and forcing the U.S. government to launch a probe.
- UnitedHealth hack reveals gaps in doctors’ cyberattack insurance: Many health care providers struggling to get paid after the hack of a UnitedHealth Group subsidiary are still trying to figure out if their cyberattack insurance will help cover their losses. … Providers ranging from large health systems to small independent practices are racking up big bills and say efforts to advance payments while Change Healthcare restores medical claims systems are falling short.
- White House cyber official urges UnitedHealth to provide third-party certification of network safety: Senior White House officials are urging UnitedHealth Group to provide its customers with detailed third-party cybersecurity assessments of its systems as it recovers from a cyberattack. … The ransomware attack against UnitedHealth subsidiary Change Healthcare has caused one of the biggest healthcare crises in years. … The attack cut off a pivotal link between medical providers and insurance companies, leaving pharmacists scrambling for weeks to facilitate the distribution of much-needed drugs and medical facilities struggling to get reimbursement for care. Change Healthcare says it processes 15 billion transactions annually.
Small and Midsize Organizations. Take your security to the next level. Apply Now! If you’re a small business, nonprofit, or IT / MSP in the greater Los Angeles area, apply NOW for LA Cybersecure, a pilot program with coaching and guidance that costs less than two cups of coffee a week. https://securethevillage.org/la-cybersecure-pilot/ The LA Cybersecure Pilot Program is funded by a grant from the Center for Internet Security (CIS) Alan Paller Laureate Program.
Family Protection Newsletter: Did you know we created the Family Protection Newsletter for non-cyber experts? For your parents, friends, those who need to protect themselves in a digital world. Sign up or share with a friend! Click here to learn more and quickly add to your free subscription!
How Hackable Are You? Take our test. Find out how hackable you are and download our free updated 13-step guide.
- How Hackable Are You? Think your defenses are strong. Find out as SecureTheVillage tests you on five basics. Please take our short test as your answers will help you and guide us to improve community safety.
Upcoming events. Please join us.
- Los Angeles Cybersecurity Workforce Coalition: The monthly meeting of the workforce coalition, Tue, April – , 1:00 pm – 2:00 pm PT. The LA Cybersecurity Workforce Coalition is for employers, educators, government, nonprofits, and others with a professional interest in the cybersecurity workforce challenge.
- Information Security Threat Briefing – A DFPI / FBI / SecureTheVillage Collaboration: SecureTheVillage in collaboration with the CA Department of Financial Protection and Innovation (DFPI) is hosting a cybersecurity threat briefing specifically designed for financial institutions, other fintech organizations, and their IT service providers, MSPs, insurance brokers, and others. FBI Supervisory Special Agent (SSA) Michael Sohn is the keynote speaker. Friday, April 19, 8:30 am – 10:00 am PT.
Please Support SecureTheVillage.
- We need your help if we’re to build a world of CyberGuardians TM. Please donate to SecureTheVillage. Thank you. It takes a village to secure the village. TM.
Cybersecurity Nonprofit of the Week … The Center for Internet Security
Our kudos this week to the Center for Internet Security (CIS®). CIS® is a community-driven nonprofit responsible for the CIS Controls®, CIS Benchmarks™, and CIS Hardened Images®. Strong proponents of collaboration and innovation, CIS is also home to the Multi-State Information Sharing and Analysis Center® (MS-ISAC®) and the Elections Infrastructure Information Sharing and Analysis Center® (EI-ISAC®). SecureTheVillage is a recipient of a grant from the Center’s Allen Paller Laureate Program to support our launch of a Pilot Program to measurably improve the cybersecurity of small and midsize organizations. The Center for Internet Security is one of the founders of Nonprofit Cyber, a coalition of implementation-focused cybersecurity nonprofits including SecureTheVillage.
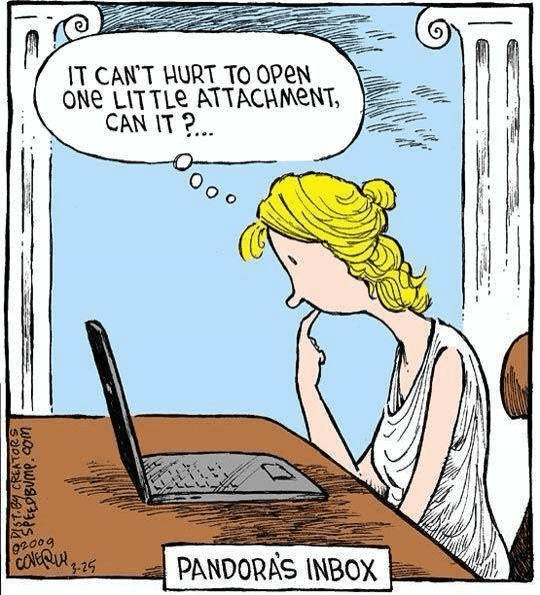
Cyber Humor
Section 2 – Let’s Be Careful Out There. And Let’s Help Others Who Aren’t Yet Cyber-Aware.
Tip of the Week: Teach the people you love to be suspicious. Help them understand that the Internet is a dangerous place. Warn them. Be a CyberGuardian TM.
- From Ransomware to Pig Butchering, Visa Report Shows Top Scams Impacting Consumers and Businesses Globally: Today, Visa released the Spring 2024 Edition of its Biannual Threats Report, which outlines the top payment threats impacting consumers and businesses around the world. The report points to increasingly organized, sophisticated threat actors targeting the most vulnerable point in the payments’ ecosystem: humans. … “With the use of Generative AI and other emerging technologies, scams are more convincing than ever, leading to unprecedented losses for consumers,” said Paul Fabara, Chief Risk and Client Services Officer, Visa. “
- Why AI Obituary Scams Are a Cyber-Risk for Businesses: Scammers now use AI to instantly whip up SEO-friendly bereavement scams, and it’s never been easier to swindle mourners or use them to get to their employers. … Two-bit scammers are generating near-instant obituaries for recently deceased strangers, taking advantage of vulnerable loved ones and potentially infecting their devices with malware.
- Romance Scam Statistics – Common Types & How To Stay Safe: Online dating is the most common way to meet people, which unfortunately paves the way for scams and frauds, as the latest romance scam statistics show. The devastating figures and trends are a testament to how far malicious actors will go to get rich. … When we dove into these statistics, we were stunned to see how much money millions of people lost in the last few years as a result of romance fraud.
- A Mexican Drug Cartel’s New Target? Seniors and Their Timeshares: One of Mexico’s most violent criminal groups, Jalisco New Generation, runs call centers that offer to buy retirees’ vacation properties. Then, it empties its victims’ bank accounts.
Good news. Airbnb has banned surveillance cameras.
- Hidden Cameras: What Travelers Need to Know: We talked to security and privacy experts about Airbnb’s new ban on surveillance cameras, your privacy rights and how to find a hidden camera. … This month, Airbnb announced that, starting April 30, the company would ban the use of surveillance cameras in its rentals. The news was welcomed by those concerned about privacy. … “Cameras are both creepy and a threat,” said Albert Fox Cahn, the executive director of the Surveillance Technology Oversight Project, which has campaigned for a ban on cameras in Airbnbs since 2022. “People are terrified about having their intimate moments photographed without their consent and having owners able to monitor their activities within a rental.”
From our friends at the Cybercrime Support Network. An excellent analysis of Credit Freeze vs Credit Alert. SecureTheVillage recommends everyone freeze their credit.
- Credit Freeze vs. Fraud Alert: Which One to Choose?: In the ever-evolving landscape of financial security, it’s crucial to stay informed about tools and measures to protect your identity and assets. Two commonly discussed options for safeguarding your credit information are credit freezes and fraud alerts. While both serve the purpose of preventing unauthorized access to your credit report, they operate in slightly different ways and may be appropriate in different circumstances. Let’s delve into the nuances of each and when it’s best to employ them.
Section 3 – Cybersecurity and Privacy News for the Cyber-Concerned.
In a story with national security implications, the Government continues to warn water districts.
- US warns hackers are carrying out attacks on water systems: The U.S. government is warning state governors that foreign hackers are carrying out disruptive cyberattacks against water and sewage systems throughout the country. … In a letter released Tuesday, National Security Advisor Jake Sullivan and Environmental Protection Agency Administrator Michael Regan warned that “disabling cyberattacks are striking water and wastewater systems throughout the United States.” … The letter singled out alleged Iranian and Chinese cyber saboteurs. Sullivan and Regan cited a recent case in which hackers accused of acting in concert with Iran’s Revolutionary Guards had disabled a controller at a water facility in Pennsylvania. They also called out a Chinese hacking group dubbed “Volt Typhoon” which they said had “compromised information technology of multiple critical infrastructure systems, including drinking water, in the United States and its territories.” … “These attacks have the potential to disrupt the critical lifeline of clean and safe drinking water, as well as impose significant costs on affected communities,” the letter said.
In a move with significant implications for our smaller businesses, The Wall Street Journal takes a deep dive on the shift underway in how organizations are managing cybersecurity risks in their supply chain.
- Companies Take a Closer Look at Supply Chains After Recent Cyberattacks: Corporate security executives beef up supplier oversight following extensive supply-chain attacks. … Companies are ramping up oversight of suppliers after major supply-chain cyberattacks have affected thousands of businesses and breached data on millions of customers. … Previously content with periodic questionnaires about supplier controls, corporate security chiefs are demanding stricter contractual terms around when and how their suppliers must notify them that they have experienced a cyberattack. Many now require third-party providers to adhere more closely to best practices from the U.S. Commerce Department’s National Institute of Standards and Technology, and others. … “The way in which third-party dependencies are managed is probably insufficient for today’s market, given the threat outlook and the sophistication of the actors that are engaged in either social engineering tactics or in ransomware operations,” said Pat Opet, global chief information security officer at banking giant JPMorgan Chase.
This is a great story of cyber security collaboration between colleges and smaller organizations. Smaller businesses get information security support while the students get valuable training. SecureTheVillage is working to implement these programs in LA.
- Small Businesses Look to College Students to Help Guard Against Hackers: Universities set up free clinics to assist small organizations with their cybersecurity needs. … It isn’t easy to be a David against Goliath hackers. Small organizations—nonprofits, local public services, mom-and-pop businesses—don’t have the cybersecurity resources to put up much of a defense. … But thanks to a new initiative, help for such groups is increasingly available—from college students. … Similar to clinics in which law and medical students perform pro bono services, university-based clinics around the country staffed by students now give cybersecurity assessments, training and other help to groups with little in the way of such resources.
After last week’s bad publicity, GM announces they’re no longer sharing driving data with insurance companies. And the Transportation Department announces a review of how airlines use and secure customer information. Amazing what a little transparency can do.
- Federal officials want to know how airlines handle — and share — passengers’ personal information: Federal officials said Thursday they will review how airlines protect personal information about their passengers and whether they are making money by sharing that information with other parties. … The U.S. Department of Transportation said its review will focus on the 10 biggest U.S. airlines and cover their collection, handling and use of information about customers. … “Airline passengers should have confidence that their personal information is not being shared improperly with third parties or mishandled by employees,” Transportation Secretary Pete Buttigieg said.
- General Motors Quits Sharing Driving Behavior With Data Brokers: G.M. had provided information about braking, acceleration and speed to LexisNexis Risk Solution and Verisk, firms that generated driver risk profiles for insurers.
Kudos to the British Library as it continues rebuilding its online presence.
- British Library hailed by UK cyber agency for its response to ransomware attack: The interim head of Britain’s National Cyber Security Centre (NCSC) said the British Library “should be applauded” for refusing to pay an extortion fee to the criminals behind a ransomware attack last year. … The British Library — the national library of the United Kingdom and an archive of millions of books and manuscripts — was hit by an initially unspecified attack last October, although internally the cause was known to be ransomware. … A wide range of services across the library were shuttered by the incident, including access to its online catalog — described as “one of the most important datasets for researchers around the world” by the library’s chief executive, Sir Roly Keating. … Although there are secure copies of all of the items in this catalog, the attack left the majority of the library’s digital infrastructure unusable. Recovery is still ongoing five months later, with the infrastructure rebuild expected to be complete by mid-April, at which point the library will begin restoring its systems in a phased manner. … The library detailed its recovery process in an 18-page incident review earlier this month. The move to publish the review — in stark contrast to the secrecy which most organizations respond to ransomware attacks with — was widely acclaimed.
In the Vancouver 2024 Pwn2Own competition, security researchers unearthed several previously undiscovered vulnerabilities in critical systems, including Windows. several browsers, and a Tesla Model 3.
- White-Hat hackers earn $1,132,500 for 29 zero-days at Pwn2Own Vancouver: Pwn2Own Vancouver 2024 has ended with security researchers collecting $1,132,500 after demoing 29 zero-days (and some bug collisions). … The total prize pool was over $1,300,000 in cash prizes and a Tesla Model 3, which Team Synacktiv won on the first day. … Competitors successfully gained code execution and escalated privileges on fully patched systems after hacking Windows 11, Ubuntu Desktop, VMware Workstation, Oracle VirtualBox, three web browsers (Apple Safari, Google Chrome, and Microsoft Edge), and the Tesla Model 3. … Vendors have 90 days to release security fixes for zero-day vulnerabilities reported during Pwn2Own contests before TrendMicro’s Zero Day Initiative discloses them publicly.
Section 4 – Managing Information Security and Privacy in Your Organization.
Using Fortinet firewalls? Time to patch.
- Exploit released for Fortinet RCE bug used in attacks, patch now: Security researchers have released a proof-of-concept (PoC) exploit for a critical vulnerability in Fortinet’s FortiClient Enterprise Management Server (EMS) software, which is now actively exploited in attacks.


