This week’s essential cybersecurity and privacy news for the cyber-aware and the cyber-concerned. Designed to educate, support, and advocate.
Stan’s Top of the News
An amazing day-by-day account of the MGM attack. And of the cybercriminal gang known simply as Com. From The Wall Street. A must read.
- The Audacious MGM Hack That Brought Chaos to Las Vegas: A gang of young criminals. A more than $30 million ransom. Casinos in disarray. Six days inside the cyberattack that put corporate America on notice. … The break-in began on an otherwise typical Las Vegas Friday night. … Step one was a phone call to MGM Resorts’ tech support. The person on the line said they were an employee, but had forgotten their password and were locked out of their account. … They gave some personal information over the phone. It all checked out. … What tech support didn’t realize was that the caller was a hacker. … A few minutes later, the real MGM employee received a notification that his password had been reset and reported this to the IT department. … By then, it was too late. The hackers were in. … Over the next five days, a brash group of cybercriminals would try to take more than $30 million from MGM. For the hackers, it was the ultimate game, and a shot at defying the oldest rule in Vegas: The house always wins. … The hack cost the company about $100 million in lost hotel and casino revenues.
Smaller Organizations. Take your security to the next level. Apply Now! If you’re a small business, nonprofit, or IT / MSP in the greater Los Angeles area, apply NOW for LA Cybersecure, a pilot program with coaching and guidance that costs less than two cups of coffee a week. https://securethevillage.org/la-cybersecure-pilot/ The LA Cybersecure Pilot Program is funded by a grant from the Center for Internet Security (CIS) Alan Paller Laureate Program.
Family Protection Newsletter: Did you know we created the Family Protection Newsletter for non-cyber experts? For your parents, friends, those who need to protect themselves in a digital world. Sign up or share with a friend! Click here to learn more and quickly add to your free subscription!
How Hackable Are You? Take our test. Find out how hackable you are and download our free updated 13-step guide.
- How Hackable Are You? Think your defenses are strong. Find out as SecureTheVillage tests you on five basics. Please take our short test as your answers will help you and guide us to improve community safety.
Upcoming events. Please join us.
- Los Angeles Cybersecurity Workforce Coalition: The monthly meeting of the workforce coalition, Tue, April 2, 1:00 pm – 2:00 pm PT. The LA Cybersecurity Workforce Coalition is for employers, educators, government, nonprofits, and others with a professional interest in the cybersecurity workforce challenge.
- Information Security Threat Briefing – A DFPI / FBI / SecureTheVillage Collaboration: SecureTheVillage in collaboration with the CA Department of Financial Protection and Innovation (DFPI) is hosting a cybersecurity threat briefing specifically designed for financial institutions, other fintech organizations, and their IT service providers, MSPs, insurance brokers, and others. FBI Supervisory Special Agent (SSA) Michael Sohn is the keynote speaker. Friday, April 19, 8:30 am – 10:00 am PT.
Please Support SecureTheVillage.
- We need your help if we’re to build a world of CyberGuardians TM. Please donate to SecureTheVillage. Thank you. It takes a village to secure the village. TM.
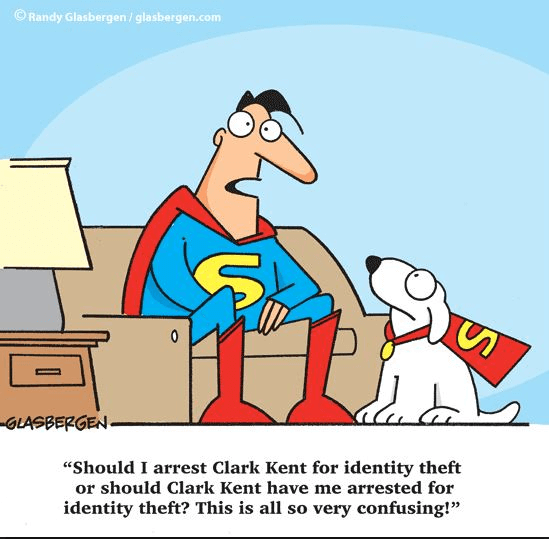
Cyber Humor
Security Nonprofit of the Week … Global Cyber Alliance (GCA)
Kudos this week to cybersecurity nonprofit Global Cyber Alliance (GCA). GCA builds practical, measurable solutions and easy to use tools, and they work with partners to accelerate adoption around the world. GCA recently partnered with the Public Interest Registry to develop an explainer video on cybersecurity risks to mission-based/non-profit organization and how to use the cybersecurity toolkit for those organizations to address those risks. The video is embedded in the mission-based organization toolkit. GCA was one of the founders of Nonprofit Cyber, the first-of-its-kind coalition of global nonprofit organizations to enhance joint action to improve cybersecurity. SecureTheVillage is a proud member of Nonprofit Cyber.
Section 2 – Let’s Be Careful Out There. And Let’s Help Others Who Aren’t Yet Cyber-Aware.
Another reminder to freeze your credit as AT&T leaks our personal information, including social security numbers.
- AT&T says personal data from 73 million current and former account holders leaked onto dark web: AT&T has launched an investigation into the source of a data leak that includes personal information of 73 million current and former customers. … In a news release Saturday morning, the telecommunications giant said the data was “released on the dark web approximately two weeks ago,” and contains information such as account holders’ Social Security numbers.
Tax time. IRS scam time.
- IRS kicks off annual Dirty Dozen with warning about phishing and smishing scams: The Internal Revenue Service today kicked off the annual Dirty Dozen list with a warning for taxpayers to be aware of evolving phishing and smishing scams designed to steal sensitive taxpayer information. … With taxpayers continuing to be bombarded by email and text scams, the IRS and the Security Summit partners warned individuals and businesses to remain vigilant against these attacks. Fraudsters and identity thieves attempt to trick the recipient into clicking a suspicious link, filling out personal and financial information or downloading a malware file onto their computer. … “Scammers are relentless in their attempts to obtain sensitive financial and personal information, and impersonating the IRS remains a favorite tactic,” said IRS Commissioner Danny Werfel. “People can be anxious to get the latest information about their refund or other tax issues, so scammers frequently try using the IRS as a way to trick people. The IRS urges people to be extra cautious about unsolicited messages and avoid clicking any links in an unsolicited email or text if they are uncertain.”
Section 3 – Cybersecurity and Privacy News for the Cyber-Concerned.
In national cybersecurity new, the US, UK and New Zealand have accused China of launching a sweeping cyber espionage campaign.
- U.S. and Britain Accuse China of Cyberespionage Campaign: The actions on both sides of the Atlantic, which included sanctions, underscored the escalation of cyberconflict between Western allies and Beijing. … The United States and Britain imposed sanctions on China’s elite hacking units on Monday, accusing Beijing’s top spy agency of a yearslong effort to place malware in America’s electrical grids, defense systems and other critical infrastructure, and of stealing the voting rolls for 40 million British citizens. … Taken together, the actions on both sides of the Atlantic underscored the escalation of cyberconflict between the Western allies and Beijing, in vastly different spheres.
- China hits back at US, UK for sanctions on espionage hacks as coordinated pressure on Beijing grows: Beijing has lashed out at the United States and the United Kingdom for imposing sanctions over alleged Chinese government-backed cyberattacks, calling the Western allies’ move an act of “political manipulation.”
- APT31: the Chinese hacking group behind global cyberespionage campaign: The United States and Britain filed charges and imposed sanctions on a company and individuals tied to a Chinese state-backed hacking group named APT31 that they allege engaged in a sweeping cyber espionage campaign. … This group was allegedly run by China’s Ministry of State Security and targeted millions of people, mostly in the U.S. and Britain, for more than a decade including officials, lawmakers, activists, academics and journalists, and firms ranging from defence contractors to a U.S. smartphone maker.
The continuing UnitedHealth breach. This hasn’t had the coverage of a ship hitting the Francis Scott Key bridge. It should. It’s an ongoing disaster that we first covered in our News of February 25.
- UnitedHealth Group has paid more than $3 billion to providers following cyberattack: UnitedHealth Group has paid out more than $3.3 billion to providers affected by the cyberattack on its subsidiary Change Healthcare. … UnitedHealth, which owns Change Healthcare, discovered in February that a cyber threat actor had breached part of the unit’s information technology network. Change Healthcare processes more than 15 billion billing transactions annually, and 1 in every 3 patient records passes through its systems, according to its website.
- UnitedHealth Tackles $14 Billion Claims Backlog From Cyberattack : Change Healthcare will begin processing more than $14 billion in claims following last month’s cyberattack. … UnitedHealth Group (UHG), Change’s parent company, said on its website Friday (March 22) that it expected its biggest clearinghouses to be back online during the weekend, “and we expect more than $14 billion in claims referenced to start flowing soon after.”
- Federal Scrutiny Growing Over Change Healthcare Breach: In addition to the investigation by the Department of Health and Human Services, CISA reportedly expressed concerns about UnitedHealth Group’s transparency and a top lawmaker is seeking answers about the issues raised by the cybersecurity agency. … The U.S. Cybersecurity and Infrastructure Security Agency recently expressed concerns about UnitedHealth Group’s transparency over the widely felt Change Healthcare ransomware attack and a top U.S. lawmaker is seeking answers about the issues raised by the cybersecurity agency, according to a letter from U.S. Rep. Jamie Raskin.
- US offers $10 million bounty for info on ‘Blackcat’ hackers who hit UnitedHealth: The U.S. State Department on Wednesday offered up to $10 million for information on the “Blackcat” ransomware gang who hit the UnitedHealth Group’s tech unit and snarled insurance payments across America.
- 4 Things You Need to Know About Health Care Cyberattacks: Despite the explosion in ransomware hacks like the one against Change Healthcare, regulation is spotty and few new safeguards have been proposed to protect patient data, vulnerable hospitals and medical groups. … The recent cyberattack on the billing and payment colossus Change Healthcare revealed just how serious the vulnerabilities are throughout the U.S. health care system, and alerted industry leaders and policymakers to the urgent need for better digital security. … Cybersecurity consultants and government officials have consistently identified health care as the sector of the U.S. economy most susceptible to attacks, and as much a part of the nation’s critical infrastructure as energy and water.
This is the kind of story we should never see. Why are we making it harder for people to get on the Information Superhighway?
- Millions of Low-Income Families Set to Lose Internet Subsidies: The Affordable Connectivity Program, a $14.2 billion federal effort to make internet service more affordable, is expected to run out of funding this spring. … The Affordable Connectivity Program, which was tucked into the 2021 infrastructure law, was part of the Biden administration’s initiative to connect every American to affordable, high-speed internet. … Phyllis Jackson, a retired administrative assistant in Monroeville, Pa., signed up for home internet service for the first time in about two decades early last year. She now regularly uses the internet to pay her bills online, buy clothes, find new recipes and learn about her medication. … Ms. Jackson said she signed up for internet service after enrolling in a federal program that provided a monthly discount for low-income households. That program is set to run out of funding this spring, however, which will make it harder for Ms. Jackson and millions of other households to afford to stay connected to the internet. … “I really can’t do without it,” said Ms. Jackson, 79. “The way things are today, everyone needs to be able to use the computer.”
- Thousands of West Virginians can afford internet access thanks to a federal program. It’s running out of money: Unless Congress acts, the Affordable Connectivity Program will end this spring, affecting the 125,000 West Virginians who rely on it. … For more than two years, a key federal broadband program has been a lifeline that helped people afford the internet by pouring billions of dollars into efforts to close the digital divide. … That could all change in the next few weeks when the Affordable Connectivity Program (ACP) runs out of money, leaving around 125,000 West Virginians — and millions more Americans — without a benefit that has improved internet access across the country.
In major privacy news, Facebook is alleged to have launched a secret project designed to intercept and decrypt the network traffic between people using Snapchat’s app and its servers.
- Facebook snooped on users’ Snapchat traffic in secret project, documents reveal: In 2016, Facebook launched a secret project designed to intercept and decrypt the network traffic between people using Snapchat’s app and its servers. The goal was to understand users’ behavior and help Facebook compete with Snapchat, according to newly unsealed court documents. Facebook called this “Project Ghostbusters,” in a clear reference to Snapchat’s ghost-like logo. … On Tuesday, a federal court in California released new documents discovered as part of the class action lawsuit between consumers and Meta, Facebook’s parent company. … The newly released documents reveal how Meta tried to gain a competitive advantage over its competitors, including Snapchat and later Amazon and YouTube, by analyzing the network traffic of how its users were interacting with Meta’s competitors. Given these apps’ use of encryption, Facebook needed to develop special technology to get around it.
The SEC has launched a probe of technology and telecom companies. The objective appears to be the companies’ disclosures related to the SolarWinds attacks.
- SEC Ramps Up Massive-Hack Probe With Focus on Tech, Telecom Companies: SEC Ramps Up Massive-Hack Probe With Focus on Tech, Telecom Companies . … The US Securities and Exchange Commission is asking tech and telecom companies how they handled the sprawling 2020 SolarWinds cyberattack, and drawing fire from the cybersecurity industry and big business for what they call overreach. … The SEC, which sought the information from a broader swath of victim companies in the wake of the massive hack, has been refining its inquiries, according to people familiar with it, who didn’t identify the companies. The regulator has asked for internal communications about the cyber-assault’s impact, probing for gaps in corporate security and for other cyber incidents, according to the people, who asked not to be named discussing a private matter.
CISA publishes draft incident reporting rules for critical infrastructure companies.
- U.S. Publishes Draft Federal Rules for Cyber Incident Reporting: New rules from the U.S. Cybersecurity and Infrastructure Security Agency, part of the Department of Homeland Security, mark the first time the federal government has proposed comprehensive cybersecurity regulations across critical-infrastructure sectors. … The U.S. Cybersecurity and Infrastructure Security Agency on Wednesday published long-awaited draft rules on how critical-infrastructure companies must report cyberattacks to the government. … CISA developed the rules after President Biden signed the Cyber Incident Reporting for Critical Infrastructure Act into law on March 15, 2022. Officials hope reports from companies in a range of industries will allow them to better spot attack patterns and determine tactics used by cybercriminals and nation-states to help improve defenses. … Under the rules, companies that own and operate critical infrastructure would need to report significant cyberattacks within 72 hours and report ransom payments within 24 hours.
In cybercrime this week, a cyberattack on a UK trade union.
- Tech trade union confirms cyberattack behind IT, email outage: Systems have been pulled offline as a precaution. … The Communications Workers Union (CWU), which represents hundreds of thousands of employees in sectors across the UK economy including tech and telecoms, is currently working to mitigate a cyberattack. … In what was originally being called a serious IT outage at the end of last week, the union confirmed to The Register today that the incident is now being treated as an attack, the full extent of which is still being assessed.
Section 4 – Managing Information Security and Privacy in Your Organization.
Patch these vulnerabilities now. Hackers are actively exploiting them.
- CISA Adds Three Known Exploited Vulnerabilities to Catalog: CISA has added three new vulnerabilities to its Known Exploited Vulnerabilities Catalog, based on evidence of active exploitation.
- CVE-2023-48788 Fortinet FortiClient EMS SQL Injection Vulnerability
- CVE-2021-44529 Ivanti Endpoint Manager Cloud Service Appliance (EPM CSA) Code Injection Vulnerability
- CVE-2019-7256 Nice Linear eMerge E3-Series OS Command Injection Vulnerability


