A weekly aggregation of important cybersecurity and privacy news … helping you navigate the new world of cybersecurity and privacy.
Stan’s Top-3
Cyberwar is coming to America. Cybercriminals acting with Putin’s permission will attack our businesses, governments, and nonprofits. We are not prepared.
I’ve Dealt With Foreign Cyberattacks. America Isn’t Ready for What’s Coming.: As Russian missiles rain on Ukraine, there’s another battle brewing — in the cybersphere. Destructive malware has flooded hundreds of Ukrainian websites and computers since Vladimir Putin announced his invasion. It would be a mistake to assume such attacks will remain limited to Ukrainian targets. New York Times, March 4, 2022
Most Cybersecurity Vendors at Risk Due to Internet-Exposed IT Assets: Study shows more than 97% have exposed assets on AWS — among a wide range of other issues. … For all their domain expertise, many cybersecurity vendors are as dangerously exposed to Internet-borne threats as the customers their technologies are designed to protect. DARKReading, March 4, 2022
7 Pressing Cybersecurity Questions Boards Need to Ask: For every new technology that cybersecurity professionals invent, it’s only a matter of time until malicious actors find a way around it. We need new leadership approaches as we move into the next phase of securing our organizations. For Boards of Directors (BODs), this requires developing new ways to carry out their fiduciary responsibility to shareholders, and oversight responsibility for managing business risk. Directors can no longer abdicate oversight of cybersecurity or simply delegate it to operating managers. They must be knowledgeable leaders who prioritize cybersecurity and personally demonstrate their commitment. Many directors know this, but still seek answers on how to proceed. Harvard Business Review, March 4, 2022
Cyber Humor
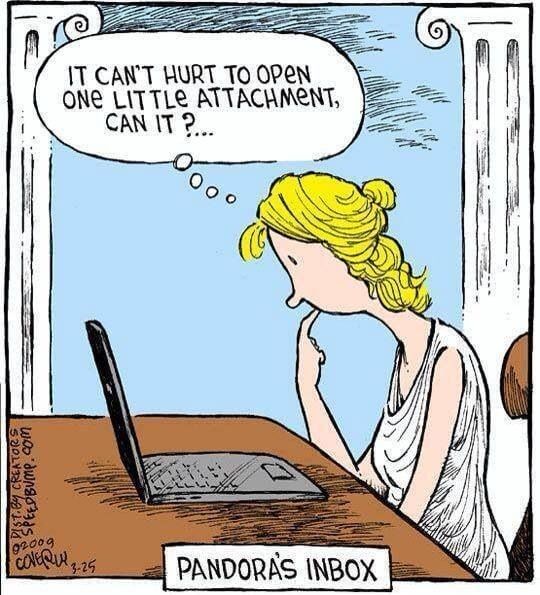
Table of Contents
- Stan’s Top-3: My pick of the 3 most important stories of the week.
- Cyber Humor: Because laughter is the best medicine.
- The Front Page: Other front page cybersecurity and privacy stories.
- Section 2 – Personal Security and Privacy: Important stories for protecting yourself and your family.
- Section 3 – General Cyber Security and Privacy: Cybersecurity and privacy stories for those wanting a deeper look.
- Section 4 – Securing the Organization: Stories to support executives and top management in securing their organizations.
The Front Page
A deeper dive on the cyber war in Ukraine.
Thousands Without Internet After Massive “Cyberattack” In Europe: The outages also knocked offline some 5,800 wind turbines in Germany and Central Europe with a combined output of 11 gigawatts. NDTV, March 5, 2022
Hacker group Anonymous declares ‘cyber war’ on Putin’s Russia: The online hacker group known as ‘Anonymous’ has declared that it is at ‘cyber war’ against Russia and the regime of President Vladimir Putin, targeting more than 1,500 Russian websites. U.S. officials confirmed they have seen evidence of the Anonymous hacks. MSNBC, March 4, 2022
Volunteer Hackers Converge on Ukraine Conflict With No One in Charge: The hackers have claimed a number of disruptions over the past week, blurring the lines between amateurs and groups linked to governments. … The hackers came from around the world. They knocked Russian and Ukrainian government websites offline, graffitied antiwar messages onto the home pages of Russian media outlets and leaked data from rival hacking operations. And they swarmed into chat rooms, awaiting new instructions and egging each other on. New York Times, March 4, 2022
European officials aiding Ukrainian refugees targeted with malware -researchers: LONDON, March 2 (Reuters) – An unidentified state actor is targeting European officials with malicious software in an apparent attempt to try and disrupt efforts to assist Ukrainian refugees, cybersecurity firm Proofpoint said on Wednesday. Reuters, March 3, 2022
Microsoft says cyberattacks targeting Ukraine ‘raise serious concerns’ under Geneva Convention: Washington (CNN Business) As hacking by nation-states has grown more pervasive in recent years, Microsoft has long called for the creation of a new Geneva Convention governing cyberspace. … But now, for the first time, the tech giant appears to be suggesting that cyberattacks tied to the war in Ukraine could potentially be considered war crimes under existing international law. CNN Business, March 1, 2022
Cyberattack on NATO could trigger collective defence clause – official: LONDON/WASHINGTON, Feb 28 (Reuters) – A cyberattack on a NATO member state could trigger Article 5, its collective defence clause, a NATO official said on Monday, amid concerns that chaos in cyberspace around Russia’s invasion of Ukraine could spill over into other territories. Reuters, February, 28, 2022
As Tanks Rolled Into Ukraine, So Did Malware. Then Microsoft Entered the War.: After years of talks about the need for public-private partnerships to combat cyberattacks, the war in Ukraine is stress-testing the system WASHINGTON — Last Wednesday, a few hours before Russian tanks began rolling into Ukraine, alarms went off inside Microsoft’s Threat Intelligence Center, warning of a never-before-seen piece of “wiper” malware that appeared aimed at the country’s government ministries and financial institutions. New York Times, February 28, 2022
The Russian disinformation war.
Ukrainians say hackers used local government sites to spread fake ‘capitulation’ news: WASHINGTON, March 3 (Reuters) – Ukrainian officials say hackers have broken into local government websites to spread false reports that Kyiv had capitulated and signed a peace treaty with Moscow. Reuters, March 3, 2022
Phony images masquerading as CNN coverage go viral amid war in Ukraine: Washington (CNN)As CNN works to debunk misinformation about the war in Ukraine, some social media accounts are working to spread misinformation about CNN’s own coverage of the war. CNN politics, March 5, 2022
Section 2 – Personal Security and Privacy
When will they ever learn?
We’re all still using the same passwords, even after they’ve been breached: People in 2022 are still picking garbage passwords, and reusing ones that have already been breached … Passwords are a problem that big tech is trying to fix but they are still essential for accessing pretty much anything online. And even now people aren’t changing them after a breach and then still use the same password to access multiple sites. ZD Net, March 3, 2022
Short passwords are like cheap locks.
8-Character Passwords Can Be Cracked in Less than 60 Minutes: Researchers say passwords with less than seven characters can be hacked “instantly. Brute-force hacking can crack an eight-character password in less than one hour, according to Hive Systems. DARKReading, March 3, 2022
Section 3 – General Cyber Security and Privacy Stories
Cyber crime.
Hackers leak 190GB of alleged Samsung data, source code: The Lapsus$ data extortion group leaked today a huge collection of confidential data they claim to be from Samsung Electronics, the South Korean giant consumer electronics company. … The leak comes less than a week after Lapsus$ released a 20GB document archive from 1TB of data stolen from Nvidia GPU designer. Bleeping Computer, March 4, 2022
Cybercriminals who breached Nvidia issue one of the most unusual demands ever: Data extortionists who stole up to 1 terabyte of data from Nvidia have delivered one of the most unusual ultimatums ever in the annals of cybercrime: allow Nvidia’s graphics cards to mine cryptocurrencies faster or face the imminent release of the company’s crown-jewel source code. ars technica, March 3, 2022
Car production halted by Toyota after suspected cyber-attack: Supplier to Japanese car manufacturer experienced a system failure as a result of a presumed malware attack. First reported by the Nikkei Asia news agency, the cyber-attack affected Kojima Industries which manufactures both interior and exterior car parts and is a part of Toyota’s just-in-time supply chain in Japan. … The issue resulted in 14 plants and 28 production lines being suspended. Plants outside of Japan have not been affected. Cyber Security Hub, March 3, 2022
Leading freight management company discloses breach.
Expeditors outlines severity of cyberattack, partially resumes operations: Expeditors International, a top-five freight management company by revenue, disclosed Wednesday that last month’s cyberattack will have a “material adverse impact” on finances and that it will be late filing its 2021 annual report because of difficulty accessing information on its accounting systems. … In a separate notice to the Securities and Exchange Commission, the logistics provider said it is making progress returning to normal operations but is unable to estimate when it will resume full operations. American Shipper, March 2, 2022
Cyber action in Washington as Senate and White House agree on new legislation.
Senate passes major cybersecurity legislation to force reporting of cyberattacks and ransomware: (CNN)The Senate on Tuesday passed major cybersecurity legation, moving one step closer toward forcing critical infrastructure companies to report cyberattacks and ransomware payments. CNN, March 2, 2022
White House backs bill requiring mandatory cyber reporting to CISA amid Ukraine crisis: The White House has come out in full support of a bill requiring hospitals, power plants, water utilities, airports and other critical infrastructure to report cyber attacks to the Department of Homeland Security within 72 hours. CBS News, March 4, 2022
Details of Russian ransomware gangs leaked in new cyberwar front.
Details of another big ransomware group ‘Trickbot’ leak online, experts say: WASHINGTON, March 4 (Reuters) – A week after the notorious Russia-based extortionist gang Conti was humbled when reams of data on its internal chats were published online, a second group – Trickbot – appears to have been hit by a leak as well. Reuters, March 4, 2022
Conti Ransomware Group Diaries, Part I: Evasion: A Ukrainian security researcher this week leaked several years of internal chat logs and other sensitive data tied to Conti, an aggressive and ruthless Russian cybercrime group that focuses on deploying its ransomware to companies with more than $100 million in annual revenue. The chat logs offer a fascinating glimpse into the challenges of running a sprawling criminal enterprise with more than 100 salaried employees. The records also provide insight into how Conti has dealt with its own internal breaches and attacks from private security firms and foreign governments. KrebsOnSecurity, March 1, 2022
Conti Ransomware Group Diaries, Part II: The Office: Earlier this week, a Ukrainian security researcher leaked almost two years’ worth of internal chat logs from Conti, one of the more rapacious and ruthless ransomware gangs in operation today. Tuesday’s story examined how Conti dealt with its own internal breaches and attacks from private security firms and governments. In Part II of this series we’ll explore what it’s like to work for Conti, as described by the Conti employees themselves. KrebsOnSecurity, March 2, 2022
Conti Ransomware Group Diaries, Part III: Weaponry: Part I of this series examined newly-leaked internal chats from the Conti ransomware group, and how the crime gang dealt with its own internal breaches. Part II explored what it’s like to be an employee of Conti’s sprawling organization. Today’s Part III looks at how Conti abused a panoply of popular commercial security services to undermine the security of their targets, as well as how the team’s leaders strategized for the upper hand in ransom negotiations with victims. KrebsOnSecurity, March 4, 2022
Cybersecurity company finds five-year old Chinese hacking operation
New Chinese hacking tool found, spurring U.S. warning to allies: (Reuters) – Security researchers with U.S. cybersecurity firm Symantec said they have discovered a “highly sophisticated” Chinese hacking tool that has been able to escape public attention for more than a decade. Yahoo!Finance, February 28, 2022
California bar leaks extremely sensitive private information.
Calif. Bar Leak Reveals Wider Exposure Of Court Records: Thousands of confidential or restricted records leaked from courts across the nation appear to have been published online, Law360 has found, with several affected courts confirming they use popular case management software recently alleged to have a security flaw. Law360, March 1, 2022
As if we needed another story of small software bugs with huge consequences.
How a simple security bug became a university campus ‘master key’: When Erik Johnson couldn’t get his university’s mobile student ID app to reliably work, he sought to find a workaround. Tech Crunch, March 3, 2022
Cyber Warning … Is your company being courted or is this a cyber attack?
Malware campaign impersonates VC firm looking to buy sites: BleepingComputer was recently contacted by an alleged “venture capitalist” firm that wanted to invest or purchase our site. However, as we later discovered, this was a malicious campaign designed to install malware that provides remote access to our devices. Bleeping Computer, March 3, 2022
Missouri Governor doubles down on shooting the messenger in apparent display of cyber ignorance.
Parson digs in against evidence absolving reporter he accused of being a ‘hacker’: Gov. Mike Parson on Thursday once again refused to accept the conclusions of an investigation by the highway patrol and Cole County prosecutor surrounding a reporter who uncovered a security flaw in a state website. Missouri Independent, March 3, 2022
The Surveillance Economy: Advertisers finding new ways to track us online.
The Quiet Way Advertisers Are Tracking Your Browsing: Cookies are on the way out—but not enough is being done about browser fingerprinting. So what is it? … Creepy cookies that track all your online activity are (slowly) being eradicated. In recent years major web browsers, including Safari and Firefox, have restricted the practice. Even Chrome has realized that cookies present a privacy nightmare. But stopping them ends only one kind of online tracking—others are arguably worse. Wired, February 26, 2022
Section 4 – Securing the Organization
Stories to support executives and top management in securing their organizations.
The “C” in CISO stands for “communication.
The CISO role needs rethinking, says Gartner: The role of the cybersecurity leader needs to be reframed, as accountability for risk and security shifts, according to Gartner research. Digital Nation, March 3, 2022
7 mistakes CISOs make when presenting to the board: Corporate boards are asking their CISOs to inform them more often about cybersecurity risks. This gives security leaders an opportunity to help senior business stakeholders better understand security’s value and makes them more likely to support and strengthen security strategies. CSO, March 1, 2022
New government advice on securely managing the IT network.
NSA report: This is how you should be securing your network: US spy agency NSA has given its most up-to-date guidance for protecting networks against attacks. … The National Security Agency (NSA) has released a new report that gives all organizations the most current advice on how to protect their IT network infrastructures from cyberattacks. … NSA’s report ‘Cybersecurity Technical Report (CTR): Network Infrastructure Security Guidance’ is available freely for all network admins and CIOs to bolster their networks from state-sponsored and criminal cyberattacks. ZD Net, March 4, 2022
Get patching now: CISA adds another 95 flaws to its known exploited vulnerabilities list: The US Cybersecurity and Infrastructure Security Agency (CISA) just added a whopping 95 new bugs to its catalogue of known exploited vulnerabilities, including multiple critical Cisco router flaws, Windows flaws new and old, and bugs in Adobe Flash Player, and more. ZD Net, March 4, 2022


