A weekly aggregation of important cybersecurity and privacy news helping you meet your data care challenges and responsibilities.
Stan’s Top of the News
Our first two stories this week are harbingers of social media change; the first with some reasonable ideas; the second with a cudgel.
In our first story, Geoffrey Fowler tells how the Instagram feed of his new baby was soon filled with all kinds of unwanted crap. After a good explanation of how social media algorithms work to maximize profit, Fowler offers several reasonable suggestions for improving these algorithms.
Our second story is anything but reasonable . It tells of an appeals court ruling last week that allows Texas residents to sue social media sites that they suspect of censoring information. The law seems so poorly written though that social media companies are at risk of being sued regardless of the actions they take to prevent what someone might believe to be censorship.
Our third story offers a summary of what’s going on in Washington as America stumbles its way into what one hopes will be reasonable data privacy.
- I gave Instagram photos of my baby. Instagram returned fear: Algorithms prey on you. What if you could reset them. … When my son was born last year, friends from all over wanted to share in my joy. So I decided to post a photo of him every day on Instagram. … Within weeks, Instagram began showing images of babies with severe and uncommon health conditions, preying on my new-parent vulnerability to the suffering of children. My baby album was becoming a nightmare machine. Washington Post, May 12, 2022
- Texas has declared open season on Facebook, Twitter and YouTube with censorship law: (CNN)Texas residents can now sue Facebook, Twitter and YouTube for allegedly censoring their content after a federal appeals court sided Wednesday with the state’s law restricting how social media sites can moderate their platforms. CNN, May 13, 2022
- The Messy Progress on Data Privacy: America still doesn’t have a federal data privacy law. But look what we have found — hope! … The latest attempt to create the first broad national data privacy law in the United States is causing the typical nonsense in Washington. But from the mess in Congress and elsewhere in the U.S., we’re finally seeing progress in defending Americans from the unrestrained information-harvesting economy. The New York Times, May 12, 2022
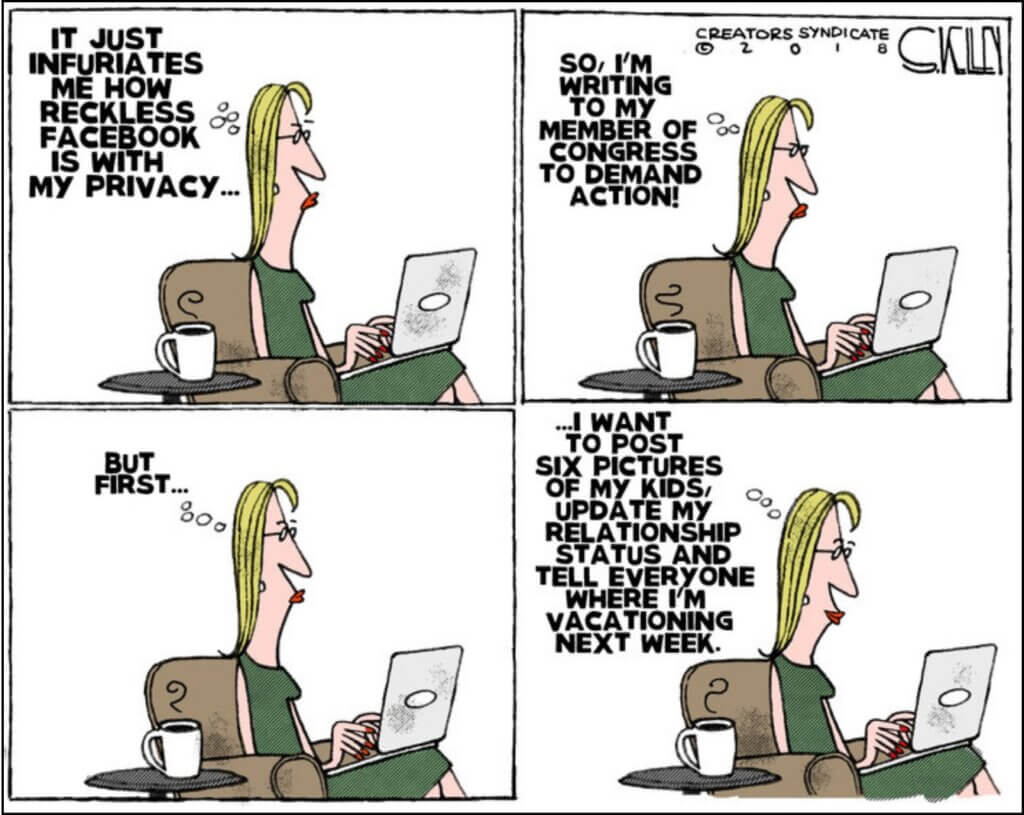
Cyber Humor
Security Nonprofit of the Week … Please Take Their MFA Survey.
This week’s security nonprofit is again the Cyber Readiness Institute. CRI is conducting a global survey to gauge the awareness and implementation of multifactor authentication (MFA) among small and medium-sized businesses. The survey is supported by CRI Members: Mastercard, Apple, GM, Principal Financial Group CGE, and Microsoft. You can view the survey here through 11:59 EST on May 16. We urge you to take this survey as it will provide valuable information to the community as we defend ourselves against cybercrime. Thanks in advance for your help.
Live on Cyber with Dr. Stan Stahl – Live on LinkedIn

Live on Cyber with Dr. Stan Stahl: Join Julie Morris and me as we discuss the latest in cybersecurity. This week we tell the story of an 82 year old woman hung out to dry by her credit card companies after scammers stole more that $70,000 from her. SecureTheVillage, May 11, 2022
Section 2 – Personal Data Care – Security and Privacy
Important data care stories for protecting yourself and your family.
#UpdateNow
- Microsoft Patch Tuesday, May 2022 Edition: Microsoft today released updates to fix at least 74 separate security problems in its Windows operating systems and related software. This month’s patch batch includes fixes for seven “critical” flaws, as well as a zero-day vulnerability that affects all supported versions of Windows. KrebsOnSecurity, May 10, 2022
#BeCarefulOutThere. #Don’tTrust.Verify.
- Common LinkedIn scams: Beware of phishing attacks and fake job offers: LinkedIn scammers attack when we may be at our most vulnerable – here’s what to look out for and how to avoid falling victim to fraud when using the platform. WeLiveSecurity, May 9, 2022
#AnonymizeYourself
- How to delete yourself from internet search results and hide your identity online: Here is a step-by-step guide to reducing your digital footprint online, whether you want to lock down data or vanish entirely. ZD Net May 11, 2022
Section 3 – General Cybersecurity and Privacy Stories
Cybersecurity and privacy stories for those wanting a deeper look.
#RussianAggressionUkraine
- Russian TV, online platforms hacked with antiwar message on Victory Day: RIGA, Latvia — Russians using smart TVs reported seeing something atypical: A message appeared instead of the usual listing of channels. “The blood of thousands of Ukrainians and hundreds of murdered children is on your hands,” read the message that took over their screens. “TV and the authorities are lying. No to war.” The Washington Post, May 9, 2022
- US and its allies say Russia waged cyberattack that took out satellite network: February outage came an hour before Russia began its invasion of Ukraine. … The US and European Union on Tuesday said Russia was responsible for a cyberattack in February that crippled a satellite network in Ukraine and neighboring countries, disrupting communications and a wind farm used to generate electricity. ars technica, May 10, 2022
#CyberCrime
- DEA Investigating Breach of Law Enforcement Data Portal: The U.S. Drug Enforcement Administration (DEA) says it is investigating reports that hackers gained unauthorized access to an agency portal that taps into 16 different federal law enforcement databases. KrebsOnSecurity has learned the alleged compromise is tied to a cybercrime and online harassment community that routinely impersonates police and government officials to harvest personal information on their targets. KrebsOnSecurity, May 12, 2022
- Conti Ransomware Declared a “National Emergency” in Costa Rica; $15 Million in Rewards Offered by US Government: The Conti ransomware that has been plaguing Windows systems around the world has ripped through the Costa Rican government since April, and has become such a persistent and damaging issue that the country has declared it a national emergency. This has prompted the US State Department to turn up the pressure on the group by offering a total of $15 million in reward money for information that leads to identification or arrest of the group’s organizers. CPO Magazine, May 11, 2022
- A US college is shutting down for good following a ransomware attack: Lincoln College says it will close this week in the wake of a ransomware attack that took months to resolve. While the impact of COVID-19 severely impacted activities such as recruitment and fundraising, the cyberattack seems to have been the tipping point for the Illinois institution. Yahoo!Finance, May 9, 2022
#KnowYourEnemy: You can read about the prospective Colonial Pipeline fine in a zillion places. The story is a relatively easy-to-understand overview of how Colonial Pipeline was breached. Kudos to Sophos for writing.
- Colonial Pipeline facing $1,000,000 fine for poor recovery plans: If you were in the US this time last year, you won’t have forgotten, and you may even have been affected by, the ransomware attack on fuel-pumping company Colonial Pipeline. … The organisation was hit by ransomware injected into its network by so-called affiliates of a cybercrime crew known as DarkSide. Naked security by sophos, May 10, 2022
#CyberSurveillance: Continued Pegasus fallout.
- F.B.I. Told Israel It Wanted Pegasus Hacking Tool for Investigations: A 2018 letter from the bureau to the Israeli government is the clearest documentary evidence to date that the agency weighed using the spyware for law enforcement operations. The New York Times, May 12, 2022
- Spain’s spy chief sacked after Pegasus spyware revelations: The Spanish government has sacked the country’s spy chief, Paz Esteban, as it tries to contain the fallout from a cyber-espionage scandal that has engulfed the ruling coalition and raised further questions about the use of controversial Pegasus spyware in Spain and beyond. The Guardian, May 10, 2022
#CyberSurveillance: We want it to be as easy as possible to identify abusers. And we want total assurance that our private messages stay private. Encryption for me, but not for thee.
- New EU rules would require chat apps to scan private messages for child abuse: The proposal has been called unworkable and invasive by privacy experts … The European Commission has proposed controversial new regulation that would require chat apps like WhatsApp and Facebook Messenger to selectively scan users’ private messages for child sexual abuse material (CSAM) and “grooming” behavior. The proposal is similar to plans mooted by Apple last year but, say critics, much more invasive. The Verge, May 14, 2022
#CyberLawsuit: Capital One has settled its class action suit for less than $2 per customer. Had the CA Consumer Privacy law been in effect, the cost could have been between $100 – $750 for each CA resident affected.
- Capital One Data Breach $190M Class Action Settlement: Capital One will pay $190 million to resolve claims it jeopardized customer information in a 2019 data breach. … The settlement benefits around 98 million Capital One customers whose information was compromised as part of the 2019 data breach. Top Class Actions, May 11, 2022
#SecureIT: These next two stories point towards a future with more secure software. Let’s hope.
- Tech giants pledge multimillion down payment to secure open source: Top technology companies offered $30 million toward a two-year goal to bolster software supply chain security. Cybersecurity Dive, May 13, 2022
- Software patching must work like car safety recalls, says US cyber boss: Adds infosec regulation coming to more industries but with a light touch, more collaboration … Software made unsafe by dependencies should be fixed without users needing to interact with the source of the problem, according to US National Cyber Director Chris Inglis, who serves in the Executive Office of the President. The register, May 13, 2022
#CybersecuritySkillsCrisis: Here’s a story of hope that’s dear to my heart. I grew up what was a middle-class town in western Pennsylvania. It’s since been carved out as businesses left. It would be great if towns like the one I grew up in could provide the cyber talent we so desperately need.
- Cybersecurity has a desperate skills crisis. Rural America could have the answer: A tiny town of 3,000 people has grown into a flourishing cybersecurity hotspot, and a case study on how the US could fix its growing tech skills shortage. ZD Net, May 11, 2022
#CyberLawEnforcement: The government continues its excellent work building cyber-alliances.
- United States Signs Protocol to Strengthen International Law Enforcement Cooperation to Combat Cybercrime: At the Council of Europe (COE) headquarters in Strasbourg, France, on May 12, Deputy Assistant Attorney General (DAAG) Richard Downing of the U.S. Department of Justice’s Criminal Division signed the Second Additional Protocol to the Convention on Cybercrime on enhanced cooperation and disclosure of electronic evidence on behalf of the U.S. government. The United States Department of Justice, May 12, 2022
Section 4 – Data Care in the Organization
Stories to support executives and top management in securing their organizations.
#Don’tTrust.Verify: In the face of increased attacks brought on in part by Russia’s aggression, organizations are strongly advised to make doubly certain that their MSP / IT vendor’s are effectively managing their own security. Ask your MSP to report on their information security practices. Are they following the NIST Cybersecurity Framework? The Center for Internet Security, version 8? CISA’s Shields Up Program?
- Beware of state actors stepping up attacks on managed service providers: Cyber agencies advise users to check contracts to ensure providers have sufficient security controls in place. … The agencies responsible for cybersecurity from the United States, United Kingdom, Australia, and Canada have issued a second alert this week, stating that attacks on managed service providers (MSP) are expected to increase. ZD Net, May 11, 2022
#UpdateNow: Every organization needs to double check that IT is doing a thorough job of patching and updating critical vulnerabilities.
Critical F5 BIG-IP vulnerability exploited to wipe devices: A recently disclosed F5 BIG-IP vulnerability has been used in destructive attacks, attempting to erase a device’s file system and make the server unusable. Bleeping Computer, May 11, 2022
#CMMC. For companies in the defense supply chain.
- Tabletop exercises to put CMMC 2.0 through the paces: Keep an eye on the Defense Department this summer to see just how well designers of version 2.0 of the Cybersecurity Maturity Model Certification (CMMC) did. … The first real test of the revamped effort comes in the form of tabletop exercises in mid-to-late June or early July. Federal News Network, May 9, 2022


