A weekly aggregation of important cybersecurity and privacy news helping you meet your data care challenges and responsibilities.
Stan’s Top-3
Our lead stories this week are warnings about online bank fraud. First is a new FBI warning about Business Email Compromise (BEC). The second is a warning about Zelle scams. NEVER transfer money based on an email, text, or other form of non-personal request. ALWAYS confirm the legitimacy of the request and the correctness of the account information. Vultures everywhere.
- FBI warns workers to beware of BEC scams that have stolen $43 billion in five years: The FBI is warning individuals and companies of the high costs that come with falling for business email compromise (BEC) attacks. Domestic and international losses are estimated to have reached $43 billion between June 2016 to December 2021, and increased 65% between July 2019 and December 2021. Techspot, May 5, 2022
- Zelle Scams: How They Work and How to Keep Your Money Safe: Criminals are using the peer-to-peer payment service to drain bank accounts. Here’s how to protect yourself. CNET, May 4, 2022
Facebook makes the Top-3 again this week with Gizmodo’s interesting analysis of its ranking algorithms.
- We’re Publishing the Facebook Papers. Here’s What They Say About the Ranking Algorithms That Control Your News Feed: Facebook employees knew that a computer-curated feed increased the time users spent on the social network—and that it led to unhealthy behaviors. Gizmodo, May 2, 2022
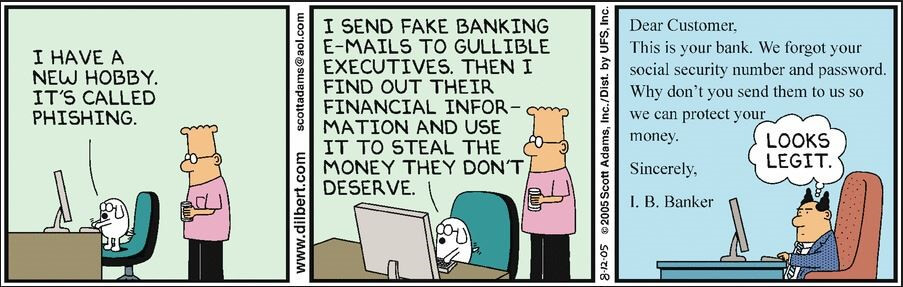
Cyber Humor
The Front Page
Other front page cybersecurity and privacy stories.
The rest of the front page is again focused on the cybersecurity impact of Russia’s invasion of Ukraine, starting with an interesting twist that might have far-reaching implications for our own cybersecurity talent shortage.
This story intrigues me. Might we train prisoners to be cybersecurity workers, offering them great careers and perhaps shortened sentences? Might this be an equity play? Intriguing.
- Russia to Rent Tech-Savvy Prisoners to Corporate IT?: Faced with a brain drain of smart people fleeing the country following its invasion of Ukraine, the Russian Federation is floating a new strategy to address a worsening shortage of qualified information technology experts: Forcing tech-savvy people within the nation’s prison population to perform low-cost IT work for domestic companies. KrebsOnSecurity, May 2, 2022
The good news is that Ukraine and its friends continue taking the battle to Russia. The dangerous news is we don’t know where this ends.
- Anonymous Claims Responsibility For Cyberattack Against Russian Rosneft: Russian energy giant Rosneft has been hit by a major cyberattack, according to various news reports in Germany. Oil Price, May 3, 3022
- Hacking Russia was off-limits. The Ukraine war made it a free-for-all: Experts anticipated a Moscow-led cyber-assault; instead, unprecedented attacks by hacktivists and criminals have wreaked havoc in Russia. … For more than a decade, U.S. cybersecurity experts have warned about Russian hacking that increasingly uses the labor power of financially motivated criminal gangs to achieve political goals, such as strategically leaking campaign emails. Washington Post, May 1, 2022
- Russians plunder $5M farm vehicles from Ukraine — to find they’ve been remotely disabled: (CNN)Russian troops in the occupied city of Melitopol have stolen all the equipment from a farm equipment dealership — and shipped it to Chechnya, according to a Ukrainian businessman in the area. CNN, May 1, 2022
- Nobody Knows Where the Red Line Is for Cyberwarfare: Is offense the best defense? Or would threats of retaliation keep an enemy in check? … A common explanation for why the Soviet Union never used nuclear weapons during the Cold War was the expectation that any attack would likely prompt a devastating nuclear response. The fear of mutually assured destruction was enough to keep both the USSR and the U.S. from launching a nuclear attack, even as they spent decades building up huge stockpiles of weapons. Bloomberg, May 2, 2022
Meanwhile millions of Russians are using VPNs to get the news Putin’s state-controlled media is blocking.
- How millions of Russians are tearing holes in the Digital Iron Curtain: A surge in virtual private network downloads is a challenge to Vladimir Putin and his version of the war. Washington Post, May 6, 2022
Security Nonprofit of the Week … Please Take Their MFA Survey.
This week’s security nonprofit, the Cyber Readiness Institute, is conducting a global survey to gauge the awareness and implementation of multifactor authentication (MFA) among small and medium-sized businesses. The survey is supported by CRI Members: Mastercard, Apple, GM, and Principal Financial Group. You can view the survey here through 11:59 EST on May 16. We urge you to take this survey as it will provide valuable information to the community as we defend ourselves against cybercrime. Thanks in advance for your help.
Live on Cyber with Dr. Stan Stahl – Live on LinkedIn

Live on Cyber with Dr. Stan Stahl: Join Julie Morris and me as we discuss the latest in cybersecurity. Interpol says “We can’t arrest our way out of cybercrime.” So what do we do to manage to manage our security and privacy? This leads to a discussion of data care, and the things we can all do to keep ourselves and our community safe from cybercrime. SecureTheVillage, May 4, 2022
Section 2 – Personal Data Care – Security and Privacy
Important data care stories for protecting yourself and your family.
#UpdateNow. Keeping your devices updated is a critical component of data care. The following is a reminder that this principle even applies to security software.
- Decade-old bugs discovered in Avast, AVG antivirus software: Researchers say exploitation could have had “far-reaching and significant” consequences. ZD Net, May 5, 2022
At the same time, users have to be careful that the updates they apply are legitimate.
- These fake Windows 10 updates will land you with a ransomware infection: Cybercriminals are smuggling malware inside fake Windows 10 updates. Techradar, May 3, 3022
What you put in your mental health app should stay in your mental health app. Not so.
- Mental health apps have terrible privacy protections, report finds: As a category, mental health apps have worse privacy protections for users than most other types of apps, according to a new analysis from researchers at Mozilla. Prayer apps also had poor privacy standards, the team found. The Verge, May 2, 2022
While we all hate passwords, they’re still a necessary element of sound data care. Make sure yours are long, complex, and unique.
- It’s World Password Day – and the perfect time to tighten up your password security habits: It’s OK if you didn’t know there was a World Password Day – which takes place on the first Thursday of every May – but you should know how to manage your passwords. USA Today, May 5, 2022
What secrets does your digital footprint hold?
- A security researcher easily found my passwords and more: How my digital footprints left me surprisingly over-exposed: The internet never forgets information that we post online – and, as I discovered, old information can come back to haunt you. ZD Net, May 5, 2022
Section 3 – General Cybersecurity and Privacy Stories
Cybersecurity and privacy stories for those wanting a deeper look.
These stories tell us more about the capabilities of the cybercriminal underground. Do not underestimate them. They’re smart, they’re committed, and they’re organized.
- Botnet that hid for 18 months boasted some of the coolest tradecraft ever: It’s not the kind of security discovery that happens often. A previously unknown hacker group used a novel backdoor, top-notch tradecraft, and software engineering to create an espionage botnet that was largely invisible in many victim networks. Ars technica, May 3, 2022
- Experts Analyze Conti and Hive Ransomware Gangs’ Chats With Their Victims: An analysis of four months of chat logs spanning more than 40 conversations between the operators of Conti and Hive ransomware and their victims has offered an insight into the groups’ inner workings and their negotiation techniques. The Hacker News, May 3, 2022
- Security researchers: Here’s how the Lazarus hackers start their attacks: Here’s how North Korea’s Lazarus hackers use LinkedIn to reach targets and Office macros to compromise hosts. ZD Net, May 6, 2022
- Hackers Have Found a Way to Spoof Any Gmail Address: Right email, wrong message … Just because that email has the right name and a correct email address doesn’t mean it’s legitimate. Lifewire, May 4, 2022
Lest you need convincing, these next stories demonstrate the point.
- AGCO ransomware attack disrupts tractor sales during U.S. planting season: U.S. agricultural equipment maker AGCO Corp (AGCO.N) said on Friday a ransomware attack was affecting operations at some of its production facilities, and dealers said tractor sales had been stalled during the crucial planting season. Reuters, May 6, 2022
- Health startup myNurse to shut down after data breach exposed health records: myNurse, a healthcare startup that provides chronic care management and remote patient monitoring services, said it will shut down at the end of the month after reporting a data breach that exposed personal health information of its users. Tech Crunch, May, 2, 2022
- Chinese hackers took trillions in intellectual property from about 30 multinational companies: A years long malicious cyber operation spearheaded by the notorious Chinese state actor, APT 41, has siphoned off an estimated trillions in intellectual property theft from approximately 30 multinational companies within the manufacturing, energy and pharmaceutical sectors. CBS News, May 4, 2022
- Crypto Hackers Stole More Than $370 Million In April Alone: The total amount of crypto stolen since the beginning of the year is more than $1.6 billion. … In April alone, hackers stole more than $370 million in crypto from several web3 projects, according to a cybersecurity firm, with nearly $100 million being stolen over the weekend. Vice, May 2, 2022
Even as we can’t arrest our way to cybersecurity, our Department of Justice is hard at work doing what it can.
- DoJ convicts cybercriminal who tricked DoD into paying $23.5 million via phishing attack: The U.S. Department of Justice (DoJ) has announced the conviction of Sercan Oyuntur, 40, resident of California, for multiple counts relating to a phishing operation that caused $23.5 million in damages to the U.S. Department of Defense (DoD). Bleeping Computer, May 2, 2022
- U.S. offers $15 million reward for information on Conti ransomware group: The United States on Friday offered a reward of up to $15 million for information on the Russia-based Conti ransomware group, which has been blamed for cyber extortion attacks worldwide, State Department spokesman Ned Price said. Reuters, May 6, 2022
Meanwhile a security researcher has discovered vulnerabilities in cybercriminal malware that might be exploitable to prevent a ransomware attack from successfully encrypting a victim’s files. Stay tuned.
- Vulnerabilities Allow Hijacking of Most Ransomware to Prevent File Encryption: A researcher has shown how a type of vulnerability affecting many ransomware families can be exploited to control the malware and terminate it before it can encrypt files on compromised systems. Security Week, May 4, 2022
This pair of stories from Motherboard is interesting. The first would qualify as an egregious violation of privacy; the second is SafeGraph’s response to the publicity. In the absence of strong GDPR-style privacy laws, it would seem to take strong negative publicity to counteract the profit opportunities in data collection.
- Data Broker Is Selling Location Data of People Who Visit Abortion Clinics: It costs just over $160 to get a week’s worth of data on where people who visited Planned Parenthood came from, and where they went afterwards. Motherboard, May 3, 2022
- Data Broker SafeGraph Stops Selling Location Data of People Who Visit Planned Parenthood: The move comes after Motherboard found it was possible to buy data showing how many people visited Planned Parenthood locations, where they came from, and where they went afterwards. Motherboard, May 4, 2022
Connecticut has become the 5th state to pass a data privacy law. The law moves in the direction of GDPR where users must affirmatively agree to their information being collected and sold. This is unlike most of the U.S. where it’s the responsibilities of users to “just say no,” if the law in their state even gives them this opportunity. And, as in the SafeGraph stories above, without stories like Motherboard’s users don’t even know to say no.
- Connecticut becomes fifth state with data privacy law: Connecticut’s recently passed data privacy bill became law on Wednesday, making it the fifth state in the U.S. with some form of data privacy protections for its residents. The Record, May 4, 2022
Beyond privacy is surveillance. More fallout from the NSO Group Pegasus scandal as Spain acknowledges its cyber-surveillance of Catalan independence leaders.
- Catalans demand answers after Spanish spy chief confirms phone hacking: The Catalan government is calling for answers “from the highest level” after the head of Spain’s National Intelligence Centre (CNI) reportedly confirmed that 18 members of the regional independence movement were spied on with judicial approval. The Guardian, May 5, 2022
Section 4 – Data Care in the Organization
Stories to support executives and top management in securing their organizations.
Another warning. This one targeting people engaged in Mergers and Acquisitions.
- New Hacker Group Pursuing Corporate Employees Focused on Mergers and Acquisitions: A newly discovered suspected espionage threat actor has been targeting employees focusing on mergers and acquisitions as well as large corporate transactions to facilitate bulk email collection from victim environments. May 2, 2022
More corporate upgrades for your IT team.
- F5 Releases Security Advisories Addressing Multiple Vulnerabilities: F5 has released security advisories on vulnerabilities affecting multiple products, including various versions of BIG-IP. Included in the release is an advisory for CVE-2022-1388, which allows undisclosed requests to bypass the iControl REST authentication in BIG-IP. An attacker could exploit CVE-2022-1388 to take control of an affected system. CISA, May 4, 2022
On the defensive side, the National Institute of Standards and Technology (NIST) has released updated guidance on managing supply chain risk. Vital reading for the CIO, CTO, CISO.
- NIST Releases Updated Cybersecurity Guidance for Managing Supply Chain Risks: The National Institute of Standards and Technology (NIST) on Thursday released an updated cybersecurity guidance for managing risks in the supply chain, as it increasingly emerges as a lucrative attack vector. The Hacker News, May 5, 2022


