This week’s essential cybersecurity and privacy news for the cyber-aware and the cyber-concerned. Designed to educate, support, and advocate.
Stan’s Top of the News
Our Top of the News is another story on data brokers, a shadowy multibillion-dollar industry that collects, aggregates, buys, and sells data. These practices are currently legal in the US. Congress: We the people need help. Are you there?
- It’s shockingly easy to buy sensitive data about US military personnel: A new report exposes the privacy and national security concerns created by data brokers. US senators tell MIT Technology Review the industry needs to be regulated. … For as little as $0.12 per record, data brokers in the US are selling sensitive private data about active-duty military members and veterans, including their names, home addresses, geolocation, net worth, and religion, and information about their children and health conditions. … In a unsettling study published on Monday, researchers from Duke University approached 12 data brokers in the US and asked what would be necessary to buy this kind of information; they ultimately purchased thousands of records about American service members, finding that many brokers offered to sell the data with minimal vetting and were willing to deal with buyers using email domains based in both the US and Asia. … The year-long study, which was funded in part by the US Military Academy at West Point, highlights the extreme privacy and national security risks created by data brokers. These companies are part of a shadowy multibillion-dollar industry that collects, aggregates, buys, and sells data, practices that are currently legal in the US. Many brokers advertise that they have hundreds of individual data points on each person in their database, and the industry has been criticized for exacerbating the erosion of personal and consumer privacy.
Small and Midsize Organizations. Take your security to the next level. As part of our LA Cybersecure initiative, SecureTheVillage has launched a Pilot Program to enable 50 small to midsize organizations to measurably improve their cybersecurity readiness. The LA Cybersecure Pilot Program is funded by a grant from the Center for Internet Security (CIS) Alan Paller Laureate Program. Find out more and register now.
Family Protection Newsletter: Did you know we created the Family Protection Newsletter for non-cyber experts? For your parents, friends, those who need to protect themselves in a digital world. Sign up or share with a friend! Click here to learn more and quickly add to your free subscription!
How Hackable Are You? Take our test. Find out how hackable you are and download our free updated 13-step guide.
- How Hackable Are You? Think your defenses are strong. Find out as SecureTheVillage tests you on five basics. Please take our short test as your answers will help you and guide us to improve community safety.
Upcoming events. Please join us.
- Los Angeles Cybersecurity Workforce Coalition: The monthly meeting of the workforce coalition, Tue, November 7, 1:00 pm – 2:00 pm PT.
- Eighth Annual Los Angeles Cyber Security Summit. Join SecureTheVillage on November 30 at the Beverly Hilton Hotel for the Cyber Security Summit, ranked as one of the “Top 50 Must-Attend Conferences” by DigitalGuardian. Keynote speakers are friends of SecureTheVillage: LA County CISO Jeffrey Aguilar and FBI Supervisory Special Agent Michael Sohn. I’m moderating “Panel 3 Cloud Security – Leveraging Its Strengths and Overcoming Its Vulnerabilities”. Register free with code STV23. Come say hello at the SecureTheVillage booth.
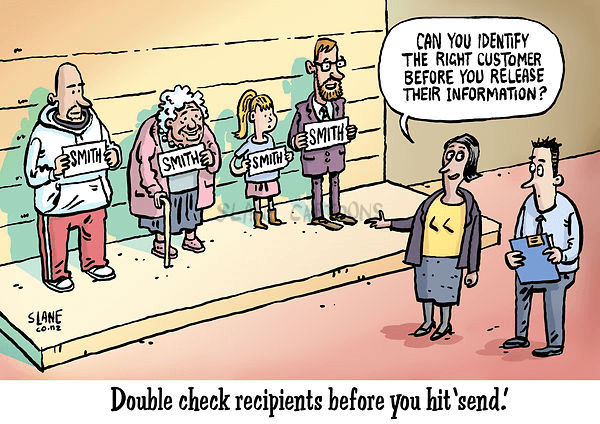
Cyber Humor
Cybersecurity Nonprofit of the Week … The Institute for Security and Technology.
Kudos this week to The Institute for Security and Technology and their Ransomware Task Force (RTF). The Task Force aims to equip businesses, organizations, and governments of all sizes to prepare for ransomware attacks, effectively respond, and quickly recover. The Task Force has published the Cyber Incident Reporting Framework and the Blueprint for Ransomware Defense representing a set of foundational and actionable safeguards derived from the Center for Internet Security’s Critical Security Controls. Like SecureTheVillage, the Institute is a member of Nonprofit Cyber, a coalition of implementation-focused cybersecurity nonprofits.
Live on Cyber with Dr. Stan Stahl – Live on LinkedIn and Your Favorite Podcast Platform

SEC vs. SolarWinds: The Fallout for American Corporations: (Video) (Podcast): What are the implications when a nation-state attacks a private company? … 🟢 At the same time we see the #Biden-Harris administration, #NIST, #CISA, #DoJ and other government entities – along with non-government organizations like #CIS, #CRI, Sightline Security, #DDN, and SecureTheVillage – in a concerted, intentional effort to help equip American corporations – ❌ We see the #SEC send exactly the wrong message in its lawsuit against #SolarWinds and its Chief Information Security Officer (#CISO). … 👉 What could the #SEC do to help, rather than blame? They could start by making sure every Board has someone on it who is trained in – and knowledgeable about – cybersecurity and other kinds of systemic risk. That alone would go a long way towards both improved cybersecurity management and transparency. … If you’re a CISO, board member, or just interested in the evolving world of cybersecurity governance, join Stan and Julie in this episode of #LiveOnCyber as they riff on ways the #SEC could help our businesses achieve reasonable – and transparent – cybersecurity instead of throwing them under the bus 🚍. … Subscribe to Live on Cyber with Stan Stahl, PhD and Julie Michelle Morris, your weekly 15-min update on the latest in privacy and information security affecting your business and community!
Section 2 – Let’s Be Careful Out There. And Let’s Help Others Who Aren’t Yet Cyber-Aware.
There’s phishing, smishing and now quishing.
- Quishing Campaigns Spike 50% in September: Security researchers have detected a double-digit percentage increase in incidents involving QR code phishing (quishing), as cyber-criminals exploit employee use of personal devices lacking enterprise protection.
Here’s two new scams to be wary of. Let’s be careful out there.
- An info-stealer campaign is now targeting Facebook users with revealing photos: Cybercriminals are using Facebook ads to distribute malware and hijack users’ social media accounts, researchers have found. … In the so-called malvertising campaign, hackers exploit legitimate tools for online ad distribution and insert infected links into typical advertisements. To entice users into clicking, the campaign offers “provocative enticements” — in this case, lewd images of young women, according to cybersecurity researchers at Bitdefender.
- Microsoft Warns of Fake Skills Assessment Portals Targeting IT Job Seekers: A sub-cluster within the infamous Lazarus Group has established new infrastructure that impersonates skills assessment portals as part of its social engineering campaigns.
Section 3 – Cybersecurity and Privacy News for the Cyber-Concerned.
The Wall Street Journal reports a hack at a major Chinese bank disrupted U.S. Treasury trading. Key question is who did this and why?
- Hack at ICBC Targeted the Digital Underbelly of Financial Markets: Unit of Industrial and Commercial Bank of China remains unplugged from U.S. markets. … There is a new reason to worry about the hardiness of the market for U.S. government debt: hackers. … Cybercriminals held hostage this week a New York unit of the world’s largest bank, Industrial and Commercial Bank of China, disrupting trading in U.S. Treasurys. The impact was relatively minor, market participants said, but the fear wasn’t.
Crime bosses in Myanmar force trafficked people to scam victims through building romantic and other relationships. Now China is going after them.
- China Unleashes Crackdown on ‘Pig Butchering.’ (It Isn’t What You Think.): Beijing is going after scam mills that operate out of secretive, dystopian compounds and swindle people worldwide. … It’s called “pig butchering.” … Armies of scammers operating from lawless corners of Southeast Asia—often controlled by Chinese crime bosses—connect with people all over the world through online messages. They foster elaborate, sometimes romantic, relationships, and then coax their targets into making bogus investments. Over time, they make it appear that the investments are growing to get victims to send more money. Then, they disappear. … For decades, frontier fiefdoms such as those in Myanmar have been havens for gambling and trafficking of everything from drugs to wildlife to people. Now, they are dens for pig-butchering operations.
The Electronic Frontier Foundation issues a stark warning about the EU’s Article 45.
- Article 45 Will Roll Back Web Security by 12 Years: The EU is poised to pass a sweeping new regulation, eIDAS 2.0. Buried deep in the text is Article 45, which returns us to the dark ages of 2011, when certificate authorities (CAs) could collaborate with governments to spy on encrypted traffic—and get away with it. … Article 45 forbids browsers from enforcing modern security requirements on certain CAs without the approval of an EU member government. … Which CAs? Specifically the CAs that were appointed by the government, which in some cases will be owned or operated by that selfsame government. … That means cryptographic keys under one government’s control could be used to intercept HTTPS communication throughout the EU and beyond.
The FTC continues to strengthen the Safeguards Rule to the benefit of consumers.
- FTC Amends Safeguards Rule to Require Non-Banking Financial Institutions to Report Data Security Breaches: Amendment will require non-bank financial institutions to report when they discover that information affecting 500 or more people has been acquired without authorization. … The Federal Trade Commission has approved an amendment to the Safeguards Rule that would require non-banking institutions to report certain data breaches and other security events to the agency.
Be careful what you text from your car. In a loss for consumer privacy advocates, a court has ruled that automakers can intercept and record text messages that flow through a car’s infotainment systems.
- Court rules automakers can record and intercept owner text messages: A federal judge on Tuesday refused to bring back a class action lawsuit alleging four auto manufacturers had violated Washington state’s privacy laws by using vehicles’ on-board infotainment systems to record and intercept customers’ private text messages and mobile phone call logs.
A ransomware criminal exposes their operations to a “job applicant.”
- Ransomware Mastermind Uncovered After Oversharing on Dark Web: Meet “farnetwork,” one of the most prolific RaaS operators around, who spilled too many details during an affiliate “job interview.” … When researchers responded to an ad to join up with a ransomware-as-a-service (RaaS) operation, they wound up in a cybercriminal job interview with one of the most active threat actors in the affiliate business, who turns out to be behind at least five different strains of ransomware.
This week in cybercrime. Includes more fallout from the MOVEit breach.
- Cyberattack Disrupts Mortgage Payments for Millions of Mr. Cooper Customers: The company, one of the largest U.S. mortgage servicers, said it was trying to determine if the attackers obtained personal information about its four million customers. … Mr. Cooper, one of America’s largest nonbank mortgage loan servicers, suffered a cyberattack last week that disrupted loan payments and other transactions for millions of customers.
- MOVEit Data breach affected 1.3M people, say Maine officials: The state of Maine has begun notifying people whose personal information was included in a data breach impacting as many as 1.3 million individuals, state officials announced Thursday.
- Hackers Claim They’ve Leaked Dallas County Data: A ransomware group called Play claims it hacked Dallas County and that it has released five gigabytes of county data. The group threatens to release more soon. … The county first became aware of a “cybersecurity incident” on Oct. 19The group behind the ransomware attack against the county claims it has released five gigabytes of Dallas County data and that it will release more if the county fails to respond. Play, the ransomware group that claimed responsibility for the attack last month, initially said it would be releasing data by Nov. 3 if the county didn’t pay an unspecified ransom.
- Cloudflare website downed by DDoS attack claimed by Anonymous Sudan: Update November 09, 17:19 EST: A threat group known as Anonymous Sudan claimed that they were the ones who took down Cloudflare’s website in a distributed denial-of-service (DDoS) attack. … Cloudflare confirmed that the outage resulted from a DDoS attack that only affected the www.cloudflare.com website without impacting other products or services. The company didn’t attribute the attack to a specific threat actor.
Section 4 – Managing Information Security and Privacy in Your Organization.
An aware, trained, and motivated workforce is vital to warding off cyber-attacks. That makes the following story most important as it illustrates how NOT to motivate your workforce.
- When Good Security Awareness Programs Go Wrong: Avoid making these mistakes when crafting a security awareness strategy at your organization. … A company once sent an email to all of its employees (about 500 of them), telling them about a holiday bonus of $650. When prompted to click on a link and fill out a form with their personal details to claim the bonus, the employees were surprised to be informed that the email was part of a phishing simulation, and by filling out the form, they had failed the test. Instead of receiving a bonus, employees were required to take mandatory security awareness training. … This is an example of how not to train people.
As the cost of cybercrime rises, the insurance industry is adding to the momentum for stronger cybersecurity.
- Meet Your New Cybersecurity Auditor: Your Insurer: As cyber insurance gets more expensive and competitive, security decision-makers have actionable opportunities to strengthen their cyber defenses. … As businesses deal with the fallout of massive ransomware waves, from Lapsus$ to Cl0p/MOVEit, an unlikely new entity is joining the regulatory bodies to raise the bar for cybersecurity: the cyber insurer. These experts do more than just process claims in the aftermath of an attack. Their coverage requirements and metrics-driven approach to risk put organizations not meeting cyber-hygiene basics on notice. How can chief information security officers (CISOs) prepare to work with this important power player?
On the technical front, this move by Microsoft will help organizations implement stronger technical controls to protect the IT network.
- Microsoft will roll out MFA-enforcing policies for admin portal access: Microsoft will soon start rolling out Conditional Access policies requiring multifactor authentication (MFA) from administrators when signing into Microsoft admin portals such as Microsoft Entra, Microsoft 365, Exchange, and Azure.


