A weekly aggregation of important cybersecurity and privacy news designed to educate, support, and advocate; helping you meet your data care challenges and responsibilities.
Stan’s Top of the News

October is Cybersecurity Awareness Month. The President in his proclamation “encourages all Americans to increase their cybersecurity at home, at work, and in schools by taking steps such as enabling multi-factor authentication, using a trusted password manager and strong passwords, recognizing and reporting phishing, and updating their software regularly. As the threat of malicious cyber activities grows, we must all do our part to keep our Nation safe and secure.”
- A Proclamation on Cybersecurity Awareness Month, 2022: During Cybersecurity Awareness Month, we highlight the importance of safeguarding our Nation’s critical infrastructure from malicious cyber activity and protecting citizens and businesses from ransomware and other attacks. We also raise awareness about the simple steps Americans can take to secure their sensitive data and stay safe online. The White House, September 30, 2022
- Enable multi-factor authentication
- Use a trusted password manager and strong passwords
- Recognize and report phishing
- Update software regularly.
Election Security Webinar … Watch the Recording
If you weren’t able to attend our election security webinar, you can watch the recording.
- What Every Citizen Needs to Know: 2022 Election Cybersecurity: Our democracy depends on getting the mid-term elections right. This means — first and foremost — getting cybersecurity right … Everything from protecting sensitive voter identities, registered voter lists, and voting machines; coming to grips with social media; and ensuring confidence in the outcomes. … Find out what’s really going on from three of the nation’s leading experts in election cybersecurity. How vulnerable are our election systems? How is cybersecurity managed in the 50 states? How do we navigate the coming flood of both mis-information and dis-information? How much confidence can we have in the outcome? Panelists include Brandon Wales, First Executive Director, Cybersecurity and Infrastructure Security Agency (CISA); Kathy Boockvar, Vice President of Election Operations & Support, Center for Internet Security; Adam Powell III, Executive Director, Election Cybersecurity Initiative, USC Annenberg Center on Communication Leadership and Policy, University of Southern California. Dr. Stan Stahl, SecureTheVillage President and founder moderates.
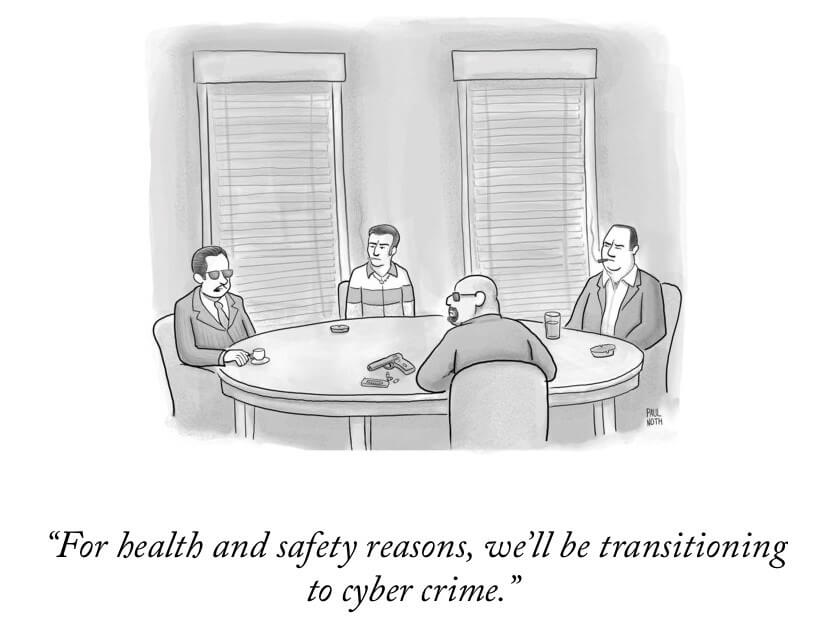
Cyber Humor
Security Nonprofit of the Week … Cyber Readiness Institute
Our kudos this week to the Cyber Readiness Institute (CRI) and the great work they do helping our medium-size and smaller organizations manage their information security challenges. CRI’s Cyber Readiness Program helps organizations protect their data, employees, vendors, and customers. This free, online program is designed to help small and medium-sized enterprises become more secure against today’s most common cyber vulnerabilities. Their free Cyber Leader Certification Program is a personal professional credential for those who have completed the Cyber Readiness Program. Both are highly recommended.
Section 2 – Personal Data Care – Security and Privacy
Important data care stories for protecting yourself and your family.
- Can Smartphones Help Predict Suicide?: A unique research project is tracking hundreds of people at risk for suicide, using data from smartphones and wearable biosensors to identify periods of high danger — and intervene. The New York Times, September 30, 2022
- Malicious Apps With Millions of Downloads Found in Apple App Store, Google Play: The ongoing ad fraud campaign can be traced back to 2019, but recently expanded into the iOS ecosystem, researchers say. … The threat actors behind a newly discovered malicious advertising app operation have been active since at least 2019, but researchers tracking their evolution report the group has become more sophisticated, expanding beyond its previous Android-specific attacks into the iOS ecosystem. DARK Reading, September 23, 2022
Section 3 – A Deeper Look for the Cyber-Concerned Citizen
Data Care, cybersecurity, and privacy stories to keep you informed.
LA Unified is still in the midst of its breach. Expect things to clarify this week.
- LAUSD says it won’t pay ransom after cyberattacker threatens to release sensitive information: Amid reports that LAUSD has until 4 pm Monday to pay, district says it won’t cave to a ‘nefarious crime syndicate’ … The Los Angeles Unified School District does not plan to pay a ransom to a “criminal organization” who has threatened to release potentially confidential or sensitive information about students or employees that the organization claims it stole during a recent cyberattack on the district’s computer systems, the district said on Friday, Sept. 30. … Although the district did not specify when the ransom is supposed to be paid, one cybersecurity expert tweeted that L.A. Unified was given a deadline of 4 p.m. Monday Pacific Standard Time. Los Angeles Daily News, September 30, 2022
The next story illustrates the disinformation challenges to our mid-term elections. Even as Meta shut-down this China-based network, it can’t shut them all down in a futile whack-a-mole exercise. All the more reason to watch our election webinar What Every Citizen Needs to Know: 2022 Election Cybersecurity.
- Facebook parent dismantles China-based network targeting American users: Facebook’s parent company Meta disrupted a China-based network of accounts that was seeking to influence U.S. politics ahead of the 2022 midterms, the company reported Tuesday. The Washington Post, September 27, 2022
Two pieces on the recent Uber hack made the news this week. The first illustrates Uber’s security weaknesses that enabled the breach. The second is an opinion piece by Bruce Schneier, a leading cybersecurity guru. Schneier argues for more explicit regulations and penalties for companies who fail to implement reasonable security practices. We’ll be discussing Schneier’s recommendations on our October 20 reasonable security webinar. What Every Business Leader Needs – A Reasonable Approach to Reasonable Security.
- Uber Hack: It’s the Simple Things That Kill Your Security: In Uber’s last update about its recent hack, the ride-sharing company blamed the Lapsus$ hacking group for its security fiasco. Lapsus$, Uber added, had also breached Microsoft, Cisco, Samsung, Nvidia, and Okta. Over the last week, they’d also breached video game maker Rockstar Games. That sounds really big and scary, doesn’t it? Well, the attack’s results were ugly, but it’s the way it was done that stands out. That was the kind of simple-minded attack that a script-kiddie teenager could pull up. And, oh, what’s this? The attack had been made by an 18-year-old with the moniker “Tea Pot.” … And how did Tea Pot pull it off? By buying a contractor’s ID and password off the dark web. The real hacking tool used here? About 1/20th of a Bitcoin, or a grand in real money, for business account access. TheNewStack, September 27, 2022
- The Uber Hack Exposes More Than Failed Data Security: By Bruce Schneier. Mr. Schneier is a security technologist and the author of 14 books, including the forthcoming “A Hacker’s Mind: How the Powerful Bend Society’s Rules, and How to Bend them Back.” … We need strong regulations that force organizations to maintain good security practices. The focus must be on resilient security for the user data entrusted to the company. Government regulation should not be involved (for example) if Uber loses the source code to its phone apps or its employee Slack channel. Government regulation should be involved if Uber loses data about the rides taken by its 100 million-plus users. The New York Times, September 26, 2022
The Optus breach in Australia has taken an interesting turn, both in the unusual action by the threat actor to withdraw their ransomware demand and in the seemingly customary threat of a class action suit on behalf of those damaged by the breach.
- FBI Helping Australian Authorities Investigate Massive Optus Data Breach: Initial reports suggest a basic security error allowed the attacker to access the company’s live customer database via an unauthenticated API. … Australian telecommunication giant Optus is reportedly receiving help from the FBI in investigating what appears to have been an easily preventable breach that ended up exposing sensitive data on nearly 10 million customers. … Meanwhile, the apparent hacker or hackers behind the breach on Tuesday withdrew their demand for a $1 million ransom along with a threat to release batches of the stolen data till the ransom was paid. The threat actor also claimed he or she deleted all the data stolen from Optus. The apparent change of heart, however, came after the attacker already earlier had released a sample of some 10,200 customer records, seemingly as proof of intent. DARK Reading, September 27, 2022
- ‘Teach Optus a lesson’: class actions over cyber hack grow: Optus is staring down a second class action over its mammoth data breach last week, with plaintiff law firm Maurice Blackburn announcing on Wednesday that it was investigating filing a claim against the telco. … It would add to the claim already proposed by Slater + Gordon on Monday, for which the firm has had “unprecedented” response from possible class members, with tens of thousands of current and former Optus customers already registering an interest. Financial Review, September 28, 2022
Meanwhile, Fast Company got serious egg on its face when a hacker breached Fast Company’s site and posted obscene racist comments.
- Hacker shares how they allegedly breached Fast Company’s site: Fast Company took its website offline after it was hacked to display stories and push out Apple News notifications containing obscene and racist comments. Today, the hacker shared how they allegedly breached the site. Bleeping Computer, September 28, 2022
The next story takes a deep look at the ransomware industry. The story is adapted from the forthcoming book The Ransomware Hunting Team: A Band of Misfits’ Improbable Crusade to Save the World From Cybercrime, by Renee Dudley and Daniel Golden.
- Inside the Ransomware Gangs That Extort Hospitals They shut down patient care and put lives at risk. Would the pandemic finally slow them down?: On a bleak St. Patrick’s Day in 2020, with holiday festivities canceled as COVID-19 swept across the U.S., Lawrence Abrams sent messages to ten of the largest ransomware gangs in the world. Stop attacking hospitals and other medical facilities for the duration of the pandemic, he pleaded. Too many lives were at stake. Intelligencer, September 28, 2022
These next stories reflect how we have to raise our game in the “spy vs spy” reality of cybercrime.
- Fake CISO Profiles on LinkedIn Target Fortune 500s: Someone has recently created a large number of fake LinkedIn profiles for Chief Information Security Officer (CISO) roles at some of the world’s largest corporations. It’s not clear who’s behind this network of fake CISOs or what their intentions may be. But the fabricated LinkedIn identities are confusing search engine results for CISO roles at major companies, and they are being indexed as gospel by various downstream data-scraping sources. KrebsOnSecurity, September 29, 2022
- Microsoft: Hackers are using open source software and fake jobs in phishing attacks: Microsoft details how hackers are using easily available tools and non-existent job offers to trick developers and IT workers. … A phishing-happy hacking crew linked to North Korea’s armed forces has been using trojanized open-source apps and LinkedIn recruitment bait to hit tech industry employees, according to threat analysts from Microsoft’s advanced persistent threat (APT) research group. ZD Net, September 30, 2022
- Sophisticated Covert Cyberattack Campaign Targets Military Contractors: Malware used in the STEEP#MAVERICK campaign features rarely seen obfuscation, anti-analysis, and evasion capabilities. … A cyberattack campaign, potentially bent on cyber espionage, is highlighting the increasingly sophisticated nature of cyberthreats targeting defense contractors in the US and elsewhere. DARK Reading, September 28, 2022
- NSA and CISA: Here’s how hackers are going after critical systems, and what you need to do about it: NSA and CISA offer some advice for critical infrastructure operators on how to protect their industrial control systems. … The National Security Agency (NSA) and the Cybersecurity and Infrastructure Security Agency (CISA) have issued an advisory explaining how to thwart cyberattacks on operational technology (OT) and industrial control system (ICS) assets. … The new joint advisory outlines what critical infrastructure operators should know about their opponents, citing recent cyberattacks on Ukraine’s energy grid and the ransomware attack against a fuel distribution pipeline. ZD Net, September 23, 2022
- Pentagon launches effort to assess crypto’s threat to national security: The military’s innovation office is launching a sweeping review of cryptocurrencies to assess threats to national security and law enforcement posed by the rise of digital assets. … The Defense Advanced Research Projects Agency – better known as DARPA, the office that developed the earliest technology undergirding the internet – has hired crypto intelligence firm Inca Digital to conduct the year-long project. The company will develop tools that give the Pentagon a granular view of crypto markets’ inner workings, in part to help authorities crack down on illicit uses of digital assets. Stars and Stripes, September 23, 2022
Rounding out this week’s news are three stories. The first is a new EU bill giving consumers more rights against harmful AI. The second story suggests that China is harvesting zero-days for possible use in their cyber-espionage and cyber-crime activities. The third is an analysis of the impact $2 billion in stolen digital currency on the crypto world.
- The EU wants to put companies on the hook for harmful AI: A new bill will allow consumers to sue companies for damages—if they can prove that a company’s AI harmed them. … The EU is creating new rules to make it easier to sue AI companies for harm. A bill unveiled this week, which is likely to become law in a couple of years, is part of Europe’s push to prevent AI developers from releasing dangerous systems. And while tech companies complain it could have a chilling effect on innovation, consumer activists say it doesn’t go far enough. MIT Technology Review, October 1, 2022
- China’s infosec researchers obeyed Beijing and stopped reporting vulns … or did they?: The number of vulnerability reports provided by Chinese information security researchers has fallen sharply, according to research by think tank The Atlantic Council, which also found a strangely commensurate increase in bug reports from unknown sources. … The Council explored the state of Chinese infosec research in the context of the 2021 introduction of “Regulations on the Management of Security Vulnerabilities of Network Products” (RMSV) that require local researchers to report any vulns they find to local authorities. As The Register has reported, the purpose of the regulations may be to allow China’s government to stockpile vulnerabilities that could be used for strategic or offensive operations. A ban on Chinese researchers participating in international infosec competitions is thought to have been imposed for similar reasons. The Register, September 27, 2022
- The Crypto World Is on Edge After a String of Hacks: More than $2 billion in digital currency has been stolen in hacks this year, shaking faith in the experimental field of decentralized finance, known as DeFi. The New York Times, September 28, 2022
Section 4 – Information Security and Privacy Management in the Organization
Stories to support executives and top management in securing their organizations and protecting privacy.
Reasonable Security Webinar: As part of Cybersecurity Awareness Month, SecureTheVillage is hosting its 3rd-annual webinar on the topic of reasonable security. … Ask ten cybersecurity professionals what “reasonable security” is and you’ll likely get ten different answers. That’s because – truth be told – what counts as “reasonable security” is a work in progress.
- What Every Business Leader Needs – A Reasonable Approach to Reasonable Security: Join SecureTheVillage and our expert panel of information security professionals on Thursday, October 20, 11:00 am – 2:00 pm PDT for a workshop-style conversation on how to think through reasonable security. Leave with a framework for ensuring your information security practices are reasonable.
- Your information risk exposure
- Your information risk tolerance
- Your information risk management practices
The following stories illustrate the importance of implementing reasonable security practices.
- Hackers are testing a destructive new way to make ransomware attacks more effective: Cyber criminals are testing a new method of cyber extortion. It could be very worrying. … Ransomware hackers are experimenting with a new kind of attack that, instead of encrypting data, outright destroys it. The aim is to make it impossible for victims to retrieve their data if they don’t pay the ransom. ZD Net, September 27, 2022
- More Than 60% Of Hackers Can Exfiltrate Data In Less Than Five Hours, Finds Inaugural Hacking Report: New research from Bishop Fox and SANS provides unique adversarial perspective, and offers “best worst-case” scenario of what defenders will likely face. … The specific findings include:
- Nearly 40% indicated that they can break into an environment more often than not, if not always
- When they do break into an environment, nearly 60% report they are able to do so in 5 hours or less
- More than one third of respondents can escalate or move laterally within 3-5 hours, with one fifth doing so in 2 hours or less
- Nearly two thirds of respondents need 5 hours or less to collect and potentially exfiltrate data once they have gained access, with more than 40% requiring 2 hours or less
Zero Trust has emerged as a powerful technology cyber defense strategy. The following WSJ story provides an executive level overview.
- Why Even Big Tech Companies Keep Getting Hacked—and What They Plan to Do About It: Hackers keep tricking employees to gain access to corporate networks, so companies are changing their approach to make it harder to wreak havoc once they’re in. … The companies that should know best how to fight hackers, tech firms, have reached an arresting conclusion: The weakest link in security, as it’s been since the Trojan War, is humans. … Increasingly, they are taking a new approach: Trust no one. The Wall Street Journal, September 24, 2022
Vulnerability Alert: If you still run your Exchange Servers in-house, you need to protect them against newly discovered 0-day vulnerabilities.
- Microsoft: Two New 0-Day Flaws in Exchange Server: Microsoft Corp. is investigating reports that attackers are exploiting two previously unknown vulnerabilities in Exchange Server, a technology many organizations rely on to send and receive email. Microsoft says it is expediting work on software patches to plug the security holes. In the meantime, it is urging a subset of Exchange customers to enable a setting that could help mitigate ongoing attacks. KrebsOnSecurity, September 30, 2022


