This week’s essential cybersecurity and privacy news for the cyber-aware and the cyber-concerned. Designed to educate, support, and advocate.
Stan’s Top of the News
TransUnion’s systems contain sensitive financial (and other) information about nearly every American. Our Top of the News is a story about their abysmal performance in processing requests to freeze credit. Since freezing one’s credit is one of the most important things we can do to protect our identity, TransUnion’s failure to properly implement a credit freeze puts us all at risk. And a paltry fine of $8 million is completely inadequate for a company whose 2022 net income was $270 million. There need to be real consequences for poor security performance. Are you listening Washington?
- TransUnion Failed to Quickly Place or Remove Freezes on Credit Reports: The Consumer Financial Protection Bureau accused the credit bureau, one of three major credit reporting agencies, of “lying to consumers.”… The Consumer Financial Protection Bureau earlier this month ordered TransUnion to pay $8 million for misleading consumers who believed they were protected by freezes but were not because the company’s computer systems were overwhelmed by requests and failed to activate them, according to an administrative settlement between the bureau and TransUnion and two subsidiaries. The total includes a $5 million penalty and $3 million to compensate customers.
Small and Midsize Organizations. Take your security to the next level. As part of our LA Cybersecure initiative, SecureTheVillage has launched a Pilot Program to enable 50 small to midsize organizations to measurably improve their cybersecurity readiness. The LA Cybersecure Pilot Program is partially funded by a grant from the Center for Internet Security (CIS) Alan Paller Laureate Program. Find out more, read our Press Release, and register now.
Family Protection Newsletter: Did you know we created the Family Protection Newsletter for non-cyber experts? For your parents, friends, those who need to protect themselves in a digital world. Sign up or share with a friend! Click here to learn more and quickly add to your free subscription!
How Hackable Are You? Take our test. Find out how hackable you are and download our free updated 13-step guide.
- How Hackable Are You? Think your defenses are strong. Find out as SecureTheVillage tests you on five basics. Please take our short test as your answers will help you and guide us to improve community safety.
Upcoming events. Please join us.
- Eighth Annual Los Angeles Cyber Security Summit. Join SecureTheVillage on November 30 at the Beverly Hilton Hotel for the Cyber Security Summit, ranked as one of the “Top 50 Must-Attend Conferences” by DigitalGuardian. Keynote speakers are friends of SecureTheVillage: LA County CISO Jeffrey Aguilar and FBI Supervisory Special Agent Michael Sohn. Register free with code STV23. Come say hello at the SecureTheVillage booth.
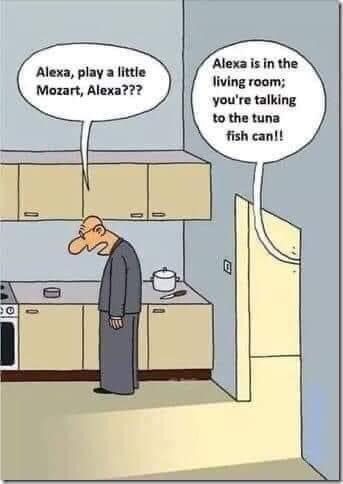
Cyber Humor
Cybersecurity Nonprofit of the Week … Cybercrime Support Network
Kudos this week to the Cybercrime Support Network, a nonprofit that helps individuals and small businesses impacted by cybercrime. As a leading voice for cybercrime victims, the Cybercrime Support Network is dedicated to serving those affected by the ever growing impact of cybercrime before, during, and after. Founded in 2017, Cybercrime Support Network (CSN) connects victims to resources, increases cybercrime and online fraud reporting, and decreases revictimization. Since November 2018, CSN has provided help to over 1,000,000 individuals and small businesses via FightCybercrime.org and ScamSpotter.org. Like SecureTheVillage, the Cybercrime Support Network is a fellow-member of Nonprofit Cyber, a coalition of implementation-focused cybersecurity nonprofits.
Live on Cyber with Dr. Stan Stahl – Live on LinkedIn and Your Favorite Podcast Platform

You’re not to small to be a target. Protect yourself: (Video) (Podcast): Think you’re too small to be a target? What happens when your admin’s email gets hacked? You don’t want to guess or waste time. #Cybersecurity for the small and micro-business is crucial. But it has to fit YOU. Let’s break down what you really need to do to keep your business safe, without overburdening you or your team. Don’t leave your business vulnerable—learn what you can do today to start your cybersecurity journey. … As always, Stan and Julie provide actionable tips and thoughtful wisdom about the steps we can take to protect our cybersecurity and privacy while we wait for our cybersecurity Nirvana. … Subscribe to Live on Cyber for your weekly 15-min update with Stan Stahl, PhD and Julie Michelle Morris on your favorite podcast platform.
Section 2 – Let’s Be Careful Out There. And Let’s Help Others Who Aren’t Yet Cyber-Aware.
Scams. Fake updates. And now, dangerous QR codes. Let’s be careful out there.
- New Hotel Phishing Scam — Be Careful If You’re Offered a Discounted Rate: You’ve made your flight plans and booked your hotel but are less than thrilled about how much you had to pay for your upcoming vacation. … So, when you receive an email from the hotel that offers you a discount on your stay if you follow a few simple steps, you happily oblige.
- Fake Chrome update spreads Trojan malware: An alarming surge in fraudulent Chrome update websites has raised concerns as they could grant unauthorized access to users’ devices through remote access trojans. … Researchers at the cybersecurity company Sucuri noticed an influx in websites infected with fake Google Chrome update malware, nicknamed “FakeUpdateRU.” … The bogus websites trick users into thinking they are downloading a legitimate update for their Chrome browser, while they’re actually installing a remote access trojan (RAT).
- Quishing is the new phishing: What you need to know: Cybercrime always seems to find a new way to take advantage of modern technologies and now QR codes are the next it thing. … I remember a couple of Super Bowls ago when the hosting network displayed a company ad that was nothing more than a QR code. Even back then, I said to my wife, “Oh, boy, this could get ugly.” The point was that, like all things, QR codes always seem innocuous…until they aren’t. … Folks, we’ve arrived at that point where QR codes have started being weaponized in phishing attacks. … Aka, quishing.
Facial Recognition = Ultimate Surveillance?
- How facial-recognition app poses threat to privacy, civil liberties: Tech reporter Kashmir Hill has written about the intersection of privacy and technology for more than a decade, but even she was stunned when she came across a legal memo in 2019 describing a facial recognition app that could identify anyone based on a picture. She immediately saw the potential this technology had to become the stuff of dystopian nightmare, the “ultimate surveillance tool,” posing immense risks to privacy and civil liberties.
Section 3 – Cybersecurity and Privacy News for the Cyber-Concerned.
Cybersecurity news from Washington.
- Neuberger: New global initiatives will include information sharing, ransomware payment tracking: A global coalition of government cybersecurity leaders will announce efforts to boost information sharing about digital threats and take on nefarious cryptocurrency payments when they convene in Washington next week, a senior White House official said on Tuesday. … The Biden administration is set to host officials from 50 countries next week for its International Counter Ransomware Initiative (CRI) where participants will unveil a number of “deliverables,” Anne Neuberger, the deputy national security adviser for cyber and emerging technologies, said at a Council on Foreign Relations event in Washington.
- CISA working on updated National Cyber Incident Response Plan: The Cybersecurity and Infrastructure Security Agency (CISA) is working with industry stakeholders and government agencies on a new version of the National Cyber Incident Response Plan (NCIRP) — the framework that outlines the country’s response to significant cyber incidents. … The updated plan was mandated in the 2023 National Cybersecurity Strategy, and CISA is now working with the Office of the National Cyber Director (ONCD) to coordinate input from regulators, critical infrastructure organizations and more. … Eric Goldstein, executive assistant director for Cybersecurity at CISA, said in a statement on Friday that a new version of the plan was needed since the original was first released seven years ago. … “Our approach to update the NCIRP will be grounded in transparency and collaboration, recognizing that the private sector is often the first responder to many cyber incidents and that adversary campaigns increasingly transcend national borders,” he said.
- U.S. to warn crypto firms against financing Hamas, terror groups: U.S. Deputy Treasury Secretary Wally Adeyemo on Friday will warn cryptocurrency firms against allowing their platforms to be used to finance terrorist organizations, as scrutiny mounts of how Hamas may have used digital currency to fund its attack on Israel. … In a speech at London’s Royal United Services Institute, a foreign-policy think tank, Adeyemo will make clear that U.S. officials are tracking the role crypto firms play in supporting terrorist groups as lawmakers in both parties call for a closer investigation of digital funds.
- U.S. Tries New Tack on Russian Disinformation: Pre-Empting It: The State Department’s Global Engagement Center is taking the unusual step of disclosing a covert Russian operation when it is barely off the ground. … “What we’re trying to do is expose Russia’s hidden hand,” James P. Rubin, the center’s coordinator, said in an interview in which he described the Russian effort in broad outlines.
Ukrainian hackers claim to have infiltrated a top Russian bank. Kudos!!
- Ukrainian hackers and intel officers partner up in apparent hack of a top Russian bank: Two Ukrainian hacktivist groups are claiming to have broken into Russia’s largest private bank, Alfa-Bank. … In a blog post last week, the hackers from groups called KibOrg and NLB shared screenshots of what appears to be an internal database belonging to Alfa-Bank, as well as personal details of several Russian individuals as “confirmation” of the breach. Within the database, the hackers say there are over 30 million records including names, birthdates, account numbers and phone numbers of Russian customers.
Russian hackers target French.
- France accuses Russian state hackers of targeting government systems, universities, think tanks: A hacking group associated with Russia’s military intelligence agency has been spying on French universities, businesses, think tanks, and government agencies, according to a new report from France’s top cybersecurity agency.
The frequency and cost of cybercrime continues to rise with major economic implications.
- September was a record month for ransomware attacks in 2023: Ransomware activity in September reached unprecedented levels following a relative lull in August that was still way above regular standards for summer months. … According to NCC Group data, ransomware groups launched 514 attacks in September. This surpasses March 2023 activity, which counted 459 attacks, and was heavily skewed by Clop’s Fortra GoAnywhere data theft attacks.
- U.S. Health Systems Have Cost The Economy Nearly $80 Billion: A new report from cybersecurity research firm Comparitech has found that since 2016, there have been 539 confirmed ransomware attacks on healthcare organizations in the United States, which hit nearly 10,000 separate healthcare sites and potentially impacted over 52 million patient records. The firm estimates that such attacks have cost the U.S. economy over $77 billion just from the downtime alone. The average amount of downtime lost to a ransomware attack was 14 days but in some cases the damage took months to repair. The average ransom demand in the 66 attacks that have occurred in 2023 so far was for over $2 million. “It’s clear that hackers aren’t just succeeding in data theft but are managing to cause unprecedented disruption with their malware,” the report’s authors write.
This week in cybercrime includes two stories where the point of entry was via third parties.
- Orange County DA’s Office hit by computer breach; communications system taken down. The agency said it isolated the system portion that was hacked to limit the damage. … The Orange County District Attorney’s Office information technology system was hacked over the weekend, prompting the agency to shut down portions of the system while it investigates the extent of the damage, a spokesperson said Monday, Oct. 23.
- Stanford University investigating cyberattack after ransomware claims: Stanford University is investigating a cybersecurity incident within its Department of Public Safety after a ransomware gang claimed it attacked the school on Friday. … On Friday morning, the Akira ransomware gang claimed it attacked Stanford University and stole 430 gigabytes of data.
- University of Michigan employee, student data stolen in cyberattack: The University of Michigan says in a statement today that they suffered a data breach after hackers broke into its network in August and accessed systems with information belonging to students, applicants, alumni, donors, employees, patients, and research study participants. … Unauthorized access to the servers lasted between August 23-27, the university says, and the data exposed included personal, financial, and medical details.
- Philadelphia: Hackers spent three months accessing city gov’t email accounts: The government of Philadelphia said hackers spent at least three months inside city email systems, giving them wide access to health information stored in email accounts. … The city did not respond to requests for comment about how many people were affected by the situation, but in a notice released on Friday officials said an unauthorized actor had access to some city email accounts from May 26 to July 28.
- Nearly $550K stolen: City of East Lansing victim of cybercrime: East Lansing is partnering with multiple law enforcement agencies to recover nearly $550,000 that was stolen from the city in an elaborate email scam. … According to the city of East Lansing, someone took the money in a scam that used a compromised vendor’s email account to reroute the payment for a legitimate bill to a different account. The engineers of the cybercrime were able to overcome East Lansing’s financial validation processes, resulting in almost $550,000 stolen.
- CCleaner confirms data breach via MOVEit attack: CCleaner, a popular software for cleaning files and Windows Registry entries, has confirmed that attackers accessed some of its customer data. … Users on Windows and CCleaner forums started sharing emails that they received from the software maker informing them about a recent breach. … CCleaner said it was impacted by the MOVEit Transfer bug, which allowed attackers to exfiltrate some of its customers’ data.
Section 4 – Managing Information Security and Privacy in Your Organization.
Dialogue between the CISO and the Board is vital for creating the “Tone at the Top” required for success.
- How to ask the board and C-suite for security funding: Cybersecurity funding is inextricably coupled with enterprise risk management as boards of directors take on more responsibility for purchasing decisions. … Recent guidance published by the National Association of Corporate Directors (NACD) and the Internet Security Alliance instructs board members to drive “a culture of corporate cyber responsibility” by empowering CISOs with the influence and resources they need to drive decisions where cybersecurity is effectively prioritized and not subordinated to cost, performance, and speed to market.
A case study that’s excellent reading for defenders. Once again, the point of entry was a third-party contractor.
- US energy firm shares how Akira ransomware hacked its systems: In a rare display of transparency, US energy services firm BHI Energy details how the Akira ransomware operation breached their networks and stole the data during the attack. … The attack first started by the Akira threat actor using the stolen VPN credentials for a third-party contractor to access BGI Energy’s internal network.


