This week’s essential cybersecurity and privacy news for the cyber-aware and the cyber-concerned. Designed to educate, support, and advocate.
Stan’s Top of the News
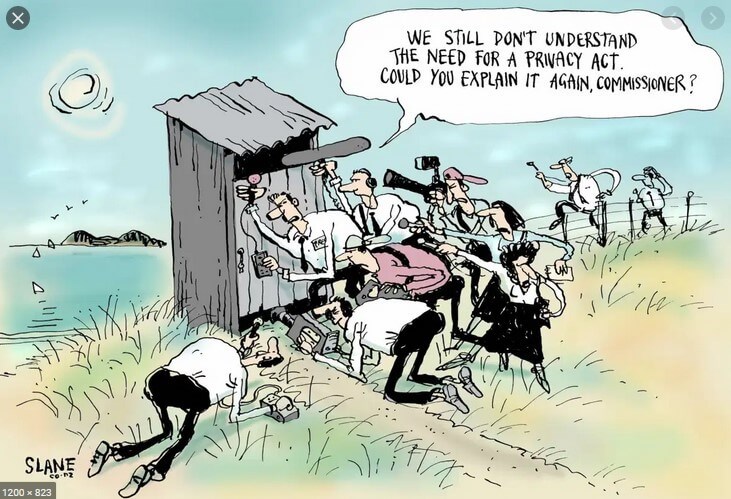
This week’s Top of the News is all about privacy … and our lack thereof.
Our lead story reports on a study by Mozilla that basically says our cars are data collection machines on wheels, gobbling up everything they can about us and our cars.
- If You’ve Got a New Car, It’s a Data Privacy Nightmare: Bad news: your car is a spy. Every major car brand’s new internet-connected models flunked privacy and security tests conducted by Mozilla. Bad news: your car is a spy. If your vehicle was made in the last few years, you’re probably driving around in a data-harvesting machine that may collect personal information as sensitive as your race, weight, and sexual activity. Volkswagen’s cars reportedly know if you’re fastening your seatbelt and how hard you hit the brakes. … That’s according to new findings from Mozilla’s *Privacy Not Included project. The nonprofit found that every major car brand fails to adhere to the most basic privacy and security standards in new internet-connected models, and all 25 of the brands Mozilla examined flunked the organization’s test. Mozilla found brands including BMW, Ford, Toyota, Tesla, and Subaru collect data about drivers including race, facial expressions, weight, health information, and where you drive. Some of the cars tested collected data you wouldn’t expect your car to know about, including details about sexual activity, race, and immigration status, according to Mozilla.
And in case you’re not yet concerned, this next story is interesting for what it portends for our privacy in the future.
- The Technology Facebook and Google Didn’t Dare Release: Engineers at the tech giants built tools years ago that could put a name to any face but, for once, Silicon Valley did not want to move fast and break things
Next up is an opportunity to strengthen consumer defenses here in California. It’s one small step for mankind, but one nevertheless. The California Senate has passed Senate Bill 362, the Delete Act. The bill would create a one-step mechanism for consumers to get every data broker to delete their personal information. The bill must be passed by the Assembly by September 14. If you live in CA, you can let your Assembly Person know your position. You can find your CA Representative here: https://findyourrep.legislature.ca.gov/.
- Opinion: The misuse of personal data is everywhere. Here’s one measure that fights back: The United States has no national privacy law. What it has instead is a laissez-faire policy that allows businesses and governments to harvest all manner of data and use it in any way they choose.
Last up on our miserable state of privacy is a LinkedIn piece by Julie Morris, my podcast co-host. Commenting on our need to emulate the EU “consent required” affirmative privacy model, Julie provides an excellent overview of how we the people would benefit from legislation similar to the EU’s Digital Markets Act. Julie and I will discuss this further on our next podcast.
- BREAKING: EU clamps down on gatekeepers (big tech) – to include “Banning tracking outside of their services without consent” and more. Why we must consider the same in the U.S.: As the digital age advances, the burden of data protection and privacy has increasingly been placed on CONSUMERS – not the tech companies that hold the power and the data. … This imbalance is not just unfair—it’s unsustainable.
In Memoriam: I lost a true friend and colleague this week, Liz Fraumann. Liz was a strong supporter of our work at SecureTheVillage “connecting the dots” in the Los Angeles cybersecurity workspace. She profoundly cared not just about cybersecurity but primarily she cared about people. She loved us as we loved her. We will miss her enthusiasm, her knowledge, her wisdom, and – most of all – her generous spirit. Our deepest condolences to her family and co-workers.
New. Family Protection Newsletter: Did you know we created the Family Protection Newsletter for non-cyber experts? For your parents, friends, those who need to protect themselves in a digital world. Sign up or share with a friend! Click here to learn more and quickly add to your free subscription!
How Hackable Are You? Take our test. Find out how hackable you are and download our free 8-step guide.
- How Hackable Are You? Think your defenses are strong. Find out as SecureTheVillage tests you on five basics. Please take our short quiz as your answers will help you and guide us to improve community safety.
Upcoming events. Please join us.
- Los Angeles Cybersecurity Workforce Coalition: The monthly meeting of the workforce coalition, Tue, October 5, 1:00 pm – 2:00 pm PT.
- What Every Business Leader Needs – A Reasonable Approach to Reasonable Security. Don’t miss our 4th Annual Reasonable Cybersecurity Webinar, October 12, 11:00 am – 12:30 pm PT. Register Now.
Cyber Humor
Cybersecurity Nonprofit of the Week … The CyberPeace Institute
Kudos this week to the CyberPeace Institute, an independent and neutral nongovernmental organization whose mission is to ensure the rights of people to security, dignity and equity in cyberspace. The CyberPeace Institute is home to the Humanitarian Cybersecurity Center (HCC). The HCC provides expert support and practical free cyber assistance to non-governmental Organizations (NGOs), tailored to their needs and located anywhere in the world. Through its Cyber Attacks in Times of Conflict Platform #Ukraine, the CyberPeace Institute is tracking cyberattacks and operations targeting critical infrastructure and civilian objects in Ukraine. The CyberPeace Institute is a member of Nonprofit Cyber, a coalition of implementation-focused cybersecurity nonprofits including SecureTheVillage.
Live on Cyber with Dr. Stan Stahl – Live on LinkedIn and Your Favorite Podcast Platform

Botnet Takedown: Decoding a Major Cyber Win: (Video) (Podcast): In a landmark collaboration, the F.B.I. and international partners have dismantled a formidable #botnet responsible for a staggering 30% of cybercrime, affecting businesses worldwide, from financial sectors to critical infrastructures. … Special kudos to the Los Angeles office of the F.B.I. and Supervisory Special Agent Mike Sohn. Beyond their exemplary work on #Qakbot, members of the LA office have supported SecureTheVillage’s educational initiatives since our founding. … Tune into this episode of #LiveonCyber with Stan and Julie for commentary on the latest in #cybersecurity and insights for business leaders navigating this complex landscape. … Hear about Dr. Stan’s ‘urgent HELP!’ text message from family, illustrating our collective need for cyber vigilance.
Section 2 – Let’s Be Careful Out There. And Let’s Help Others Who Aren’t Yet Cyber-Aware.
Apple User? Update now!! Including your Watch and Mac. See our story in the next section for context of this emergency app. Bottom line: It’s the NSO Group’s Pegasus software again.
- Update your iPhone: Apple just pushed out a significant security update: Apple released a significant security updatefor iPhones and iPads Thursday to patch newly discovered security vulnerabilities in the devices’ system software.
If you’re not using multifactor authentication, you should be. And if you have a friend or colleague who isn’t using multifactor authentication, please help them understand it’s importance.
- CEO, ex-NSA hacker says ‘people hate’ this advice—but it’s your ‘single biggest’ protection from scams: You might be ignoring your best tool to protect you against scams because it’s too annoying — even though it only takes a minute or two out of your day. … “Everybody hates multi-factor authentication,” cybersecurity expert and former government hacker Kyle Hanslovan tells CNBC Make
The election is still more than a year away. But misinformation, malinformation, and disinformation is already in full bloom. Always check sources. Don’t fall victim to believing what you want to believe. We all have confirmation bias. Let’s guard against it.
- China suspected of using AI on social media to sway US voters, Microsoft says: Microsoft researchers said on Thursday they found what they believe is a network of fake, Chinese-controlled social media accounts seeking to influence U.S. voters by using artificial intelligence.
Section 3 – Cybersecurity and Privacy News for the Cyber-Concerned.
Here’s the story on why you have to patch your Apple devices.
- Apple discloses zero-days linked to NSO Group spyware: Apple released software updates on Thursday to address two zero-day vulnerabilities that researchers said were used to deliver NSO Group’s Pegasus spyware to at least one victim. … Cybersecurity researchers at the Citizen Lab at The University of Toronto said that all users of Apple devices should update their operating systems immediately to fix the bugs.
A couple of pieces on AI security made the news this week. The first is truly creepy. The second is a well put together overview of the emerging field.
- Criminal enterprise flaunts AI in creepy ‘fraud-for-hire’ commercial meant for dark web: A criminologist recently unearthed a video of a multibillion-dollar, transnational criminal organization that has been stealing from the U.S. government since the pandemic and selling generative artificial intelligence tools to other criminals, an expert says. … The 58-second clip, which was meant for the dark web, opens with a person – who goes by “Sanchez” – covered head to toe in black clothing and speaking behind a black skeleton mask with someone else who appears to be digging a grave behind him. … “Yes, I sell Chase bank accounts. Yes, I am one of the first people to sell fake bank accounts four years ago,” the man who calls himself “Sanchez” said. “We started with my partner four years ago. Now we are about 30 people in one office.”
- Everything You Wanted to Know About AI Security but Were Afraid to Ask: There’s been a great deal of AI hype recently, but that doesn’t mean the robots are here to replace us. This article sets the record straight and explains how businesses should approach AI. … From musing about self-driving cars to fearing AI bots that could destroy the world, there has been a great deal of AI hype in the past few years. AI has captured our imaginations, dreams, and occasionally, our nightmares. However, the reality is that AI is currently much less advanced than we anticipated it would be by now. Autonomous cars, for example, often considered the poster child of AI’s limitless future, represent a narrow use case and are not yet a common application across all transportation sectors. … In this article, we de-hype AI, provide tools for businesses approaching AI and share information to help stakeholders educate themselves.
The LastPass breach continues to find victims. It’s absolutely incredible to me how people with their crypto wallets protected by LastPass failed to change their passwords following the LastPass breach. This is 1st-grade stuff like looking both ways before crossing the street. It is not rocket science.
- Experts Fear Crooks are Cracking Keys Stolen in LastPass Breach: In November 2022, the password manager service LastPass disclosed a breach in which hackers stole password vaults containing both encrypted and plaintext data for more than 25 million users. Since then, a steady trickle of six-figure cryptocurrency heists targeting security-conscious people throughout the tech industry has led some security experts to conclude that crooks likely have succeeded at cracking open some of the stolen LastPass vaults. … Taylor Monahan is lead product manager of MetaMask, a popular software cryptocurrency wallet used to interact with the Ethereum blockchain. Since late December 2022, Monahan and other researchers have identified a highly reliable set of clues that they say connect recent thefts targeting more than 150 people, Collectively, these individuals have been robbed of more than $35 million worth of crypto.
And it’s not going to get any easier, not with countries like North Korea putting their best and brightest to the task of stealing our money. And – like the LastPass story shows – it’s like taking candy from a baby.
- Inside North Korea’s Crypto Heists: $200M in Crypto Stolen in 2023; Over $2B in the Last Five Years: Over the past five years, North Korean hackers have stolen over USD 2 billion in cryptocurrencies in over 30 attacks, according to TRM Labs. While reports have indicated the amount of crypto stolen by North Korea since 2018 to be as high as $3 billion, our research indicates that this figure likely includes multiple large hacks misattributed to North Korea. … In 2023, although the total amount stolen in cryptocurrency attacks is down from a record-setting 2022, North Korea has maintained its focus on the crypto ecosystem. Year-to-date, North Korea has stolen USD 200 million in cryptocurrency, accounting for over 20% of all stolen crypto this year.
Meanwhile we’re also under attack from China and Russia. And don’t get your hopes up that we charged 9 Russians. Good for us. Great for us with last week’s Qakbot takedown. But all the great work of the government goes for naught when we leave our doors and windows open.
- Chinese-Speaking Cybercriminals Launch Large-Scale iMessage Smishing Campaign in U.S.: A new large-scale smishing campaign is targeting the U.S. by sending iMessages from compromised Apple iCloud accounts with an aim to conduct identity theft and financial fraud. … A stand-out aspect of the activity is the use of breached Apple iCloud accounts as a delivery vector to send package delivery failure messages, urging recipients to click on a link to reschedule the delivery and enter their credit card information in a fake form.
- 9 Russians charged with cyberattacks targeting US companies: The men allegedly infected victims’ computers with Trickbot malware. … The Justice Department earlier this week charged nine Russian nationals who they say used Russian-based malware in cyberattacks to steal money from U.S. companies, governments and school districts.
Here’s what happens when we leave our doors and windows open. Here’s what happens when we fail to change our passwords following a major breach. Here’s what happens when we fail to keep our computers updated. Here’s what happens when we fail to prepare for an attack.
- Hinds County computer system remains under ransomware attack: HINDS COUNTY, Miss. — Hinds County government offices remain closed because of a ransomware attack on its computer system. … Friday was the second straight day the Hinds County Tax Collector’s office and other state offices were forced to close. … People coming to renew their license plates were greeted by a closed sign outside the building.
- Minneapolis school district says data breach affected more than 100,000 people: Minneapolis Public Schools has begun notifying more than 100,000 people that their personal information may have been leaked after a cyberattack early this year.
- Ransomware gang claims credit for Sabre data breach: Travel booking giant Sabre said it was investigating claims of a cyberattack after a tranche of files purportedly stolen from the company appeared on an extortion group’s leak site.
- Johnson & Johnson discloses IBM data breach impacting patients: Johnson & Johnson Health Care Systems (“Janssen”) has informed its CarePath customers that their sensitive information has been compromised in a third-party data breach involving IBM.
Section 4 – Managing Information Security and Privacy in Your Organization.
Warn your people to be extra vigilant with emails. Teach them to be especially careful for unexpected emails with links or attachments or that ask for money to be sent.
- New phishing tool hijacked thousands of Microsoft business email accounts: Researchers have uncovered a hidden “phishing empire” targeting businesses in Europe, Australia and the U.S. with a sophisticated new tool. … A hacking group called W3LL, which has been active since at least 2017, has created an English-language underground marketplace to sell a phishing kit that can bypass multi-factor authentication, according to a report by cybersecurity firm Group-IB. … Their targeted buyers are “criminals of all skill levels” who want to engage in business email compromise (BEC) attacks, which involve defrauding a company through messages that appear to be official.


