This week’s essential cybersecurity and privacy news for the cyber-aware and the cyber-concerned. Designed to educate, support, and advocate.
Stan’s Corner
In compiling the news this week, I was reminded of the Parable of the Boiling Frog. A frog will jump out of a pot of hot water. It won’t jump out of a pot of cold water, even if you slowly heat the water. The frog will sit there as the water slowly heats up. It won’t perceive the danger. And it will die.
Are we the frogs of the cybercrime epidemic as the temperature slowly rises? Or do we jump out of the pot while there’s still time?
As The Wall Street Journal points out in the story below, the cyberattack on CDK Global impacted as many as 50% of automobile showrooms. That’s 1 of every 2 car buyers, along with the banks and insurance companies who provide car loans and insurance, along with the dealerships paying interest on the inventory, along with the ability of sales people to pay their rent when they can’t sell cars. In other words, it’s a big deal.
And CDK is not alone in dominating its industry. We’re still living through the Change Healthcare breach that impacted the ability of 1/3 of us to get our medications.
What happens when it’s the airline reservation system? Or the banking system?
We can all be grateful for the work the Federal government is doing to push and prod the private sector to better protect its systems and our information. But government is too slow, particularly in today’s hyper-partisan Washington.
The challenge, as the recent ProPublica story on Microsoft so well illustrates: spending money to improve security too often loses out to profits. Given the inevitability of a serious cybersecurity incident, this can’t but illustrate … changing metaphors … killing the goose that laid the golden eggs. Take some of those profits and invest them in making sure you aren’t destroying tomorrow’s golden eggs. In other words, let get out of the pot while we still can.
Please. For all of us. For the greater good.
- CDK Global Hack Shows Risk of One Software Vendor Dominating an Industry: Airlines, banks and hospitals could be vulnerable to a ‘single point of failure’ attack like the one that hobbled car dealers. … The cyberattack on software firm CDK Global that forced U.S. car dealerships to break out pen and paper to do business is putting a spotlight on other sectors critically reliant on just a handful of vendors. … Airlines, banks and healthcare providers all use a handful of niche software providers—many of which have been dominant for decades—for key functions such as booking flights, processing payments and managing patient data.
From SecureTheVillage
- Smaller business? Nonprofit? Take your security to the next level. Apply Now! If you’re a small business or nonprofit in the greater Los Angeles area, apply NOW for LA Cybersecure. Protect your organization with our innovative team-based learn-by-doing program with coaching and guidance that costs less than two cups of coffee a week.
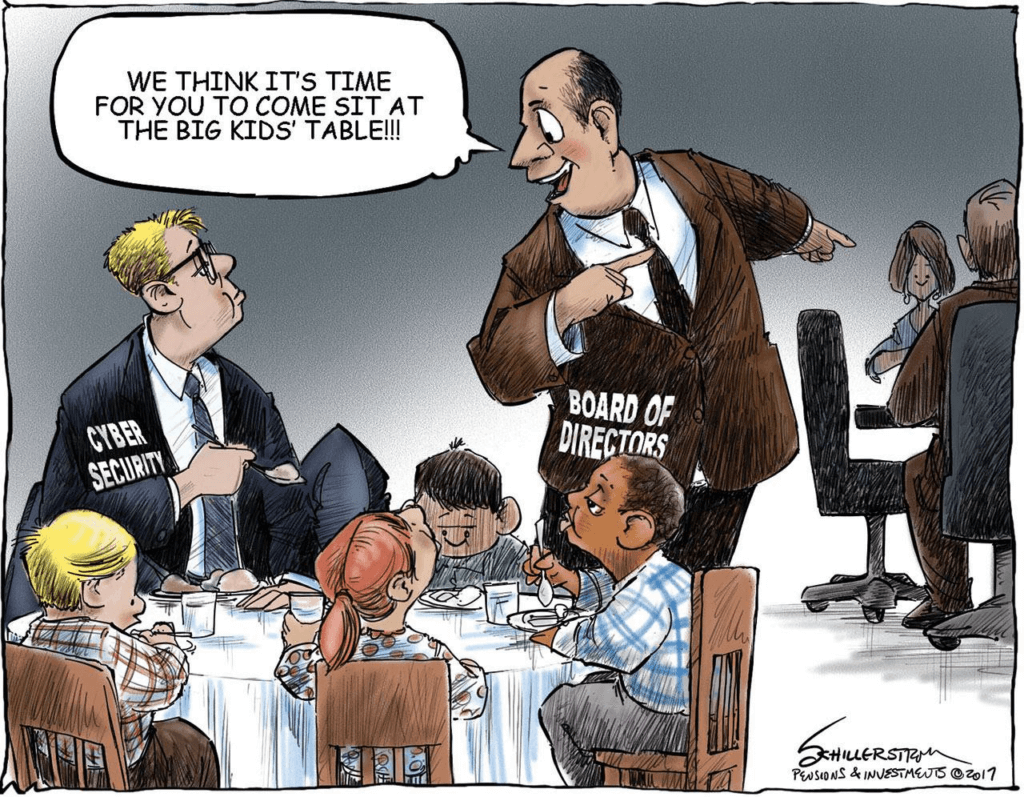
- IT Service Provider / MSP? Take your client’s security to the next level. Apply Now! If you’re an IT service provider in the greater Los Angeles area, apply NOW for LA Cybersecure. With our innovative team-based learn-by-doing program, you’ll have both that “seat at the table” and the peace of mind that you’re providing your clients with the IT security management they need.
- The LA Cybersecure Program is funded in part by a grant from the Center for Internet Security (CIS) Alan Paller Laureate Program.
- Family Protection Newsletter: Did you know we created the Family Protection Newsletter for non-cyber experts? For your parents, friends, those who need to protect themselves in a digital world. Sign up or share with a friend! Click here to learn more and quickly add to your free subscription!
- How Hackable Are You? Think your defenses are strong. Find out as SecureTheVillage tests you on five basic controls and download our free updated 13-step guide.
- Please Support SecureTheVillage: We need your help if we’re to build a world of CyberGuardians TM. Please donate to SecureTheVillage. Thank you. It takes a village to secure the village. TM.
Security Nonprofit of the Week … Global Cyber Alliance (GCA)
Kudos this week to cybersecurity nonprofit Global Cyber Alliance (GCA). GCA builds practical, measurable solutions and easy to use tools, and they work with partners to accelerate adoption around the world. GCA was one of the founders of Nonprofit Cyber, the first-of-its-kind coalition of global nonprofit organizations to enhance joint action to improve cybersecurity. SecureTheVillage is a proud member of Nonprofit Cyber.
Cyber Humor
Section 2: Let’s Be Careful Out There. And Let’s Help Others Who Aren’t Yet Cyber-Aware.
Be suspicious. Always be suspicious. Don’t trust. Cybercriminals are out there. Like crocodiles in the river, they’re waiting for you to cross.
- Mac users served info-stealer malware through Google ads: Full-service Poseidon info stealer pushed by “advertiser identity verified by Google.” … Mac malware that steals passwords, cryptocurrency wallets, and other sensitive data has been spotted circulating through Google ads, making it at least the second time in as many months the widely used ad platform has been abused to infect web surfers. … The latest ads, found by security firm Malwarebytes on Monday, promote Mac versions of Arc, an unconventional browser that became generally available for the macOS platform last July. The listing promises users a “calmer, more personal” experience that includes less clutter and distractions, a marketing message that mimics the one communicated by The Browser Company, the startup maker of Arc.
Patch your AirPods. Patch all your computers, and your laptops, and your smartphones and everything else that connects to cyberspace.
- Apple Patches AirPods Bluetooth Vulnerability That Could Allow Eavesdropping: Apple has released a firmware update for AirPods that could allow a malicious actor to gain access to the headphones in an unauthorized manner.
And from The Washington Post comes some good advice on checking the privacy policies of that app you’re about to download.
- Is that app sketchy? Here are 3 easy ways to check: You could spend your remaining days reading privacy policies. Or take just a few minutes to do these checks for red flags. … Downloading an unfamiliar app is like inviting a stranger into your home. It will probably be okay, but it’s smart to do some checking first. … Companies have every incentive to gobble personal information from your phone or nag you to pay for a crummy app. It’s unfair, but you’re mostly on your own to preserve your privacy, security and safety from scams. … You don’t need to be Sherlock Holmes to sleuth out potentially suspect apps. Just spend a few minutes doing these three spot checks to look for red flags:
Section 3: Cybersecurity and Privacy News for the Cyber-Concerned.
In national cybersecurity news, the danger level continues to heighten.
- Stopping Chinese cyberattacks is officially now the biggest priority for US security forces: The US Department of Homeland Security (DHS) has shuffled its priorities to place battling the “cyber and other threats posed by the People’s Republic of China” at the top of the list, at least until the end of 2025. … China has been conducting numerous cyber attacks against US infrastructure, particularly focussing on internet-facing endpoints within water facilities. … In a statement, DHS Secretary Alejandro Mayorkas said, “From the banking system to the electric grid, from health care to our nation’s water systems and more, we depend on the reliable functioning of our critical infrastructure as a matter of national security, economic security, and public safety.” … “The threats facing our critical infrastructure demand a whole of society response and the priorities set forth in this memo will guide that work. I look forward to continuing our work with partners at all levels of government and the private sector to better ensure the safety of all Americans,” Mayorkas continued.
- China ‘actively’ targeting US industrial base, warns CYBERCOM chief: “The People’s Republic of China’s efforts to steal intellectual property, gain critical infrastructure footholds and disrupt supply chains pose significant risk to DoD’s ability to defend the nation,” CYBERCOM Commander Gen. Haugh said. … TECHNET CYBER 2024 — US Cyber Command officials this week painted a grim picture of what Chinese cyber attacks could do to the US defense industrial base, including destroying critical infrastructure, intellectual property theft and supply chain disruption. … “The defense industrial base is being actively targeted by our adversaries and competitors, particularly by the People’s Republic of China. They are acting with increasing agility and sophistication, which we must continue to outpace,” Commander of CYBERCOM, Gen. Timothy Haugh said Tuesday during his keynote address at the TechNet Cyber conference in Baltimore. … “The People’s Republic of China’s efforts to steal intellectual property, gain critical infrastructure footholds and disrupt supply chains pose significant risk to DoD’s ability to defend the nation.”
- Microsoft informs customers that Russian hackers spied on emails: Russian hackers who broke into Microsoft’s systems and spied on staff inboxes earlier this year also stole emails from its customers, the tech giant said on Thursday, around six months after it first disclosed the intrusion. … The disclosure underscores the breadth of the breach as Microsoft faces increasing regulatory scrutiny over the security of its software and systems against foreign threats. An allegedly Chinese hacking group that separately breached Microsoft last year stole thousands of U.S. government emails. … The Russian government has never responded to the Microsoft hacking allegations, but Microsoft has said the hackers targeted cybersecurity researchers who had been investigating the Russian hacking group’s actions. …”This week we are continuing notifications to customers who corresponded with Microsoft corporate email accounts that were exfiltrated by the Midnight Blizzard threat actor,” a Microsoft spokesperson said in an emailed statement. Bloomberg first reported on the action earlier in the day. … Microsoft said it was also sharing the compromised emails with its customers, but did not say how many customers had been impacted, nor how many emails may have been stolen.
- CISA confirms hackers may have accessed data from chemical facilities during January incident: Hackers may have accessed sensitive information about the nation’s chemical facilities during a cyberattack in January, the Cybersecurity and Infrastructure Security Agency (CISA) confirmed on Monday.
Cybercrime continues to be the growth industry of the 21st century.
- Rise in cyberattacks is alarming folks: A new study has revealed a startling rise in cyberattacks from 2022 to 2023 across the US. Throughout 2023, the United States experienced an alarming 3,205 data breaches, marking a dramatic 78% surge from the 1,801 incidents reported in 2022. The tech sector saw a 92% rise in breaches with 65 million victims impacted within the technology sector.… .… The study conducted by data collection experts SOAX utilized data from the Identity Theft Resource Center on the number of data violation cases from 2020 to 2023 by industry.
Even as we give kudos to Interpol for their excellent work, let’s not delude ourselves into thinking that law enforcement can control cybercrime.
- Nearly 4,000 arrested in global police crackdown on online scam networks: International law enforcement said on Thursday that it dismantled online scam networks in several countries, arresting over 3,900 suspects and seizing $257 million in illegally obtained assets. … The operation, dubbed First Light, was conducted by police officers from 61 countries and targeted phishing, investment fraud, fake online shopping sites, romance scams, and impersonation scams, according to a statement by Interpol. … In addition to arresting thousands of potential cybercriminals, the police also identified over 14,600 other possible suspects across all continents. … During the searches, law enforcement seized suspects’ real estate, high-end vehicles, expensive jewelry, and many other high-value items and collections. They also froze 6,745 bank accounts used for transferring money obtained through illegal operations.
This week in cybercrime.
- Phishing attack hits L.A. County public health agency, jeopardizing 200,000-plus residents’ personal info: The personal information of more than 200,000 people in Los Angeles County was potentially exposed after a hacker used a phishing email to steal the login credentials of 53 public health employees, the county announced Friday. … Details that were possibly accessed in the February data breach include the first and last names, dates of birth, diagnoses, prescription information, medical record numbers, health insurance information, Social Security numbers and other financial information of Department of Public Health clients, employees and other individuals.
- Levi Strauss notifies customers of cyberattack: Personal information, including partial payment details, may have been obtained by bad actors during an automated credential-stuffing attack on Levi’s online store. … The maker of the famous Levi’s denim jeans reported that over 72,000 accounts were affected during a “security incident” that was detected on July 13th.
- Neiman Marcus says 64,000 affected by breach of Snowflake customer account: The luxury retailer Neiman Marcus said a recent breach that exposed the information of more than 64,000 people was traced back to the company’s account with data storage provider Snowflake.
- Indonesia’s national data center encrypted with LockBit ransomware variant: Hackers have encrypted systems at Indonesia’s national data center with ransomware, disrupting immigration checks at airports and a variety of other public services, according to the country’s communications ministry.
- Seattle Libraries Network Outage Nears a Month: A ransomware attack that has impacted the Seattle Public Library and its 27 branches continues to be felt nearly a month after its discovery May 25. E-book access has been restored, but computer networks remain down…. The Seattle Public Library would like you, please, to not return your books. … The library and its 27 branches continue to struggle through a ransomware attack that has disabled its networks, rendered its hundreds of public computers useless and turned its normal operations upside down. … Book checkouts are being done by spreadsheet. Column A: the library user’s account number. Column B: the book’s bar code number. The low-tech inventory will be integrated with the library’s normal account system at some future, unknown date. … With its computer networks down, the library has no way to check books back into its system, making it more convenient for everyone if you just hold onto your books for a little while. In normal times, the library says it loans out and other items each month. … The shutdown, which library officials have attributed to a ransomware attack, has now lingered for four weeks, with no solid estimate on when full library services may return.
- Crypto scammers circle back, pose as lawyers, steal an extra $10M in truly devious plan: The FBI says in just 12 months, scumbags stole circa $10 million from victims of crypto scams after posing as helpful lawyers offering to recover their lost tokens. … Between February 2023-2024, scammers were kicking US victims while they were already down, preying on their financial vulnerability to defraud them for a second time in what must be seen as a new low, even for that particular breed of dirtball. … It’s the latest update from the FBI’s Internet Crime Complaint Center (IC3) on the ongoing issue which was first publicized in August last year. … The Reg heard there was a rise in these fake companies cropping up, which claim to help recover stolen crypto in exchange for fees that would never be returned, but this is the first time IC3 has put a monetary value to the crime. … These “law firms” contact victims on social media and messaging platforms, IC3 said, all claiming to have the proper authority to carry out successful fraud investigations, when in fact they have no business serving seizure orders to the likes of cryptocurrency companies.
Section 4: Helping Executives Understand Why and Know How.
Why “reasonable security” is so important. Businesses not only face direct cybercrime losses and the cost of restoring their systems. They continue to face lawsuits from others they may have damaged. Being able to successfully argue that your security practices are reasonable is a reasonable defense.
- Panera class action alleges restaurant data breach impacts tens of thousands: A former employee of Panera Bread is suing the bakery chain, alleging her personally identifiable information — including Social Security number — was exposed in a cyberattack on the company. … Plaintiff Gracelyn Donovan filed the class action lawsuit against Panera LLC on June 21 in a Missouri federal court, alleging negligence. … Donovan says Panera stored sensitive information about current and former employees that was stolen in a March cyberattack on its systems. She says she believes the information, which includes passport numbers, driver’s license numbers and financial account numbers, is now in the hands of cybercriminals and will be marketed and sold. … Panera could have prevented the March 23 data breach by adequately securing and encrypting its servers, Donovan says. … Instead, she says Panera disregarded the rights of her and others by “willfully, recklessly, or negligently” failing to implement adequate measures to ensure their personally identifiable information was safeguarded.
Section 5: Securing the Technology.
Use MOVEit? Patch it. TeamViewer? Consider removing it until the dust settles. And take a look at how well you’re managing the security of your SaaS applications.
- Fresh MOVEit Bug Under Attack Mere Hours After Disclosure: The high-severity CVE-2024-5806 allows cyberattackers to authenticate to the file-transfer platform as any valid user, with accompanying privileges. … A high-severity security vulnerability in Progress Software’s MOVEit Transfer software could allow cyberattackers to get around the platform’s authentication mechanisms — and it’s being actively exploited in the wild just hours after it was made public. … Admins should patch the issue immediately — not only is MOVEit on cybercriminals’ radar screens after the events of last year, but the ability to access internal files at Fortune 1000 companies is a juicy plum for any espionage-minded advanced persistent threat (APT).
- TeamViewer Detects Security Breach in Corporate IT Environment: TeamViewer on Thursday disclosed it detected an “irregularity” in its internal corporate IT environment on June 26, 2024. … “We immediately activated our response team and procedures, started investigations together with a team of globally renowned cyber security experts and implemented necessary remediation measures,” the company said in a statement. … It further noted that its corporate IT environment is completely cut off from the product environment and that there is no evidence to indicate that any customer data has been impacted as a result of the incident. … It did not disclose any details as to who may have been behind the intrusion and how they were able to pull it off, but said an investigation is underway and that it would provide status updates as and when new information becomes available. … TeamViewer, based in Germany, is the maker of remote monitoring and management (RMM) software that allows managed service providers (MSPs) and IT departments to manage servers, workstations, network devices, and endpoints. It’s used by over 600,000 customers.
- Combatting the Evolving SaaS Kill Chain: How to Stay Ahead of Threat Actors: The modern kill chain is eluding enterprises because they aren’t protecting the infrastructure of modern business. SaaS continues to dominate software adoption, and it accounts for the greatest share of public cloud spending. But enterprises and SMBs alike haven’t revised their security programs or adopted security tooling built for SaaS. … The mature security controls CISOs and their teams depended on in the age of on-prem dominance have vanished. Firewalls now protect a small perimeter, visibility is limited, and even if SaaS vendors offer logs, security teams need homegrown middleware to digest them and push into their SIEM. … SaaS vendors do have well-defined security scopes for their products, but their customers must manage SaaS compliance and data governance, identity and access management (IAM), and application controls — the areas where most incidents occur. While this SaaS shared responsibility model is universal among SaaS apps, no two SaaS applications have identical security settings.


