This week’s essential cybersecurity and privacy news for the cyber-aware and the cyber-concerned. Designed to educate, support, and advocate.
Stan’s Top of the News
With the holiday season upon us, our Top of the News is a warning about the cyber scams that accompany the holidays. Let’s be careful out there. And let’s help those who aren’t yet cyber-aware.
- New York Department of State’s Consumer Protection Division Issues Scam Prevention Tips For Consumers As Holiday Season Approaches: As Black Friday & Cyber Monday Fast Approach, the Division of Consumer Protection Wants to Make Sure Consumers heed warnings of Scammers. … Tips to Help Consumers Shop Safely Online as Holiday Season Gets an Early Start
Please Support SecureTheVillage.
- We need your help if we’re to build a world of CyberGuardians. Please donate to SecureTheVillage. Donate now in celebration of Giving Tuesday. It will only take a few minutes and it will leave you feeling happy all day. Thank you. It takes a village to secure the village. TM.
Small and Midsize Organizations. Take your security to the next level. As part of our LA Cybersecure initiative, SecureTheVillage has launched a Pilot Program to enable 50 small to midsize organizations to measurably improve their cybersecurity readiness. The LA Cybersecure Pilot Program is funded by a grant from the Center for Internet Security (CIS) Alan Paller Laureate Program. Find out more and register now.
Family Protection Newsletter: Did you know we created the Family Protection Newsletter for non-cyber experts? For your parents, friends, those who need to protect themselves in a digital world. Sign up or share with a friend! Click here to learn more and quickly add to your free subscription!
How Hackable Are You? Take our test. Find out how hackable you are and download our free updated 13-step guide.
- How Hackable Are You? Think your defenses are strong. Find out as SecureTheVillage tests you on five basics. Please take our short test as your answers will help you and guide us to improve community safety.
Upcoming events. Please join us.
- Los Angeles Cybersecurity Workforce Coalition: The monthly meeting of the workforce coalition, Tue, December 5, 1:00 pm – 2:00 pm PT.
- Eighth Annual Los Angeles Cyber Security Summit. Join SecureTheVillage on November 30 at the Beverly Hilton Hotel for the Cyber Security Summit, ranked as one of the “Top 50 Must-Attend Conferences” by DigitalGuardian. Keynote speakers are friends of SecureTheVillage: LA County CISO Jeffrey Aguilar and FBI Supervisory Special Agent Michael Sohn. I’m moderating “Panel 3 Cloud Security – Leveraging Its Strengths and Overcoming Its Vulnerabilities”. Register free with code STV23. Come say hello at the SecureTheVillage booth.
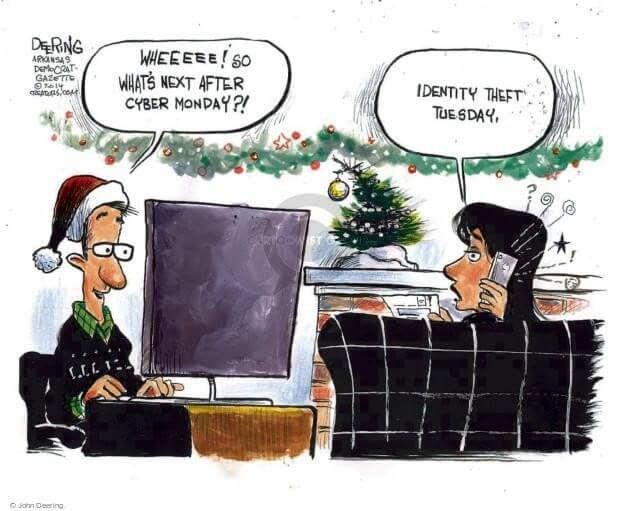
Cyber Humor
Cybersecurity Nonprofit of the Week … US Valor
Kudos this week to US Valor, a nonprofit with two intertwined objectives: (1) helping veterans transition back into civilian life and (2) helping America meet our cybersecurity workforce challenge. US Valor does this through an innovative Department of Labor approved Apprenticeship Program. The US Valor Cybersecurity Apprenticeship Program (CAP) is all about helping transitioning military personnel and U.S. Veterans experience a smooth transition from military life to the civilian world through its Department of Labor Registered Apprenticeship Program (RAP). I’m a proud member of US Valor’s Advisory Board and I encourage you to support them.
Live on Cyber with Dr. Stan Stahl – Live on LinkedIn and Your Favorite Podcast Platform

Security. Privacy. Freedom: (Video) (Podcast): Julie and Stan are taking a week off in Thanksgiving celebration with family. In its place, we revisit an essential May 2022 conversation Stan had with Nicole Perlroth, award-winning author of “This is How They Tell me the World Ends.” Listen as Nicole explains why we all need to practice good data care with a story, asking “What would Putin want from me?” Subscribe to Live on Cyber with Stan Stahl, PhD and Julie Michelle Morris, your weekly 15-min update on the latest in privacy and information security affecting our businesses and the communities we live in!
Section 2 – Let’s Be Careful Out There. And Let’s Help Others Who Aren’t Yet Cyber-Aware.
Watch as Philadelphia attorney Gary Schildhorn tells a Senate panel of an attempted scam as his son’s voice was spoofed by A.I.
- Senate Special Aging Hearing on Artificial Intelligence and Fraud: Philadelphia Attorney Tells Lawmakers How He Nearly Fell Victim to AI Scam. … Philadelphia attorney Gary Schildhorn tells a Senate panel about his story of an attempted scam against him where his son’s voice was spoofed by artificial intelligence.
Reuters has a special report on the ‘pig-butchering’ industry where scammers build relationships with their online victims to “invest” their money in fraudulent crypto-investment schemes.
- Crypto scam: Inside the billion-dollar ‘pig-butchering’ industry: Fraudulent crypto investment schemes directed from Asia known as “pig butchering” have become a global billion-dollar industry. But little is known about those who benefit. Reuters traced at least $9 million linked to such scams to an account registered to a well-connected representative of a Chinese trade group in Thailand.
On the side of the good guys, California students will soon be taught social media literacy skills to help them identify fake news.
- California students will soon be taught how to spot fake news: Public school students in California will soon learn media literacy skills to help them identify fake news online and distinguish ads from legitimate news stories, thanks to a new law. … A growing number of states are including media literacy skills in public education to help teens consume news more discerningly.
Section 3 – Cybersecurity and Privacy News for the Cyber-Concerned.
Kudos to the Justice Department for seizing nearly $9M stolen through ‘pig butchering.
- Cyber Scam Organization Disrupted Through Seizure of Nearly $9M in Crypto: The Justice Department announced today the seizure of nearly $9 million worth of Tether, a cryptocurrency pegged to the U.S. dollar. These seized funds were traced to cryptocurrency addresses allegedly associated with an organization that exploited over 70 victims through romance scams and cryptocurrency confidence scams, which are widely known as “pig butchering.”
After several major cyber-incidents, Australia has launched a “whole of country” defense.
- Australia beefs up cyber defences after major breaches: Australia will give cyber health checks for small businesses, increase cyber law enforcement funding and introduce mandatory reporting of ransomware attacks under a security overhaul announced on Wednesday after a spate of attacks. … The federal government said it will also subject telecommunications firms to tougher cyber reporting rules which apply to critical infrastructure, seek migrants to build up the cyber security workforce and set limits on inter-agency data sharing to encourage people to report incidents.
Analogous to the SolarWinds supply chain attack, Microsoft has alerted CyberLink that North Korean hackers have modified its software to infect victims in Japan, Taiwan, Canada, and the US.
- Microsoft alerts CyberLink to North Korean threat: Microsoft has alerted software company CyberLink to the misuse of its software by North Korean group Diamond Sleet. The cyber gang is believed to have injected malicious code into the program, infecting more than 100 targets. … Microsoft says it has been used to attack targets in Japan, Taiwan, Canada, and the US. … “This malicious file is a legitimate CyberLink application installer that has been modified to include malicious code that downloads, decrypts, and loads a second-stage payload,” it added.
Hacking a company to sell them information security services is wrong. Full stop!! The ISC2 code of ethics for Certified Information System Security Professionals (CISSP) is clear and unambiguous. (1) Protect society, the common good, necessary public trust and confidence, and the infrastructure. (2) Act honorably, honestly, justly, responsibly, and legally. (3) Provide diligent and competent service to principals. (4) Advance and protect the profession.
- Former infosec COO pleads guilty to attacking hospitals to drum up business: Admits to taking phones used for ‘code blue’ emergencies offline and more. … An Atlanta tech company’s former COO has pleaded guilty to a 2018 incident in which he deliberately launched online attacks on two hospitals, later citing the incidents in sales pitches. … Under a plea deal he signed last week, Vikas Singla, a former business leader at network security vendor Securolytics – a provider to healthcare institutions, among others – admitted that in September 2018 he rendered the Ascom phone system of Gwinnett Medical Center inoperable.
Three class-action lawsuits follow the recent breach at mortgage lender Mr. Cooper.
- Lawsuits pile up after data breach at mortgage lender Mr. Cooper: The cyberattack on Dallas-based mortgage lender Mr. Cooper is over–and here come the lawyers. … Three class-action lawsuits filed Nov. 14 allege Mr. Cooper did not adequately safeguard the confidential personal information of its approximately 4.3 million customers. The suits contend that the company’s negligence allowed the data breach. They also claim the company did not notify customers of the breach in a timely manner.
This week’s cybercrime news includes a breach announcement that likely would not have happened without the SEC’s recent regulatory moves. two more MOVEit victims.
- Fidelity National Financial shuts down network in wake of cybersecurity incident: Fidelity National Financial, or FNF, a Fortune 500 company that provides title insurance and settlement services for the mortgage and real estate industries, announced on Tuesday that it was the victim of a “cybersecurity incident that impacted certain FNF systems.” … The company filed a report with the Securities and Exchange Commission (SEC) saying that it has launched an investigation, hired “leading experts” to help, alerted law enforcement and “implemented certain measures to assess and contain the incident.”
- Cyberattack on Kansas Courts Leaves Lawyers Filing ‘Everything by Fax’: The state’s court system has been offline for more than a month. … Kansas courts have been running on paper forms and in-person visits to the courthouse since mid-October, when officials discovered there was a “security incident” and disconnected the online court system. … This week, state officials said that cybercriminals were behind the “sophisticated foreign” attack and had stolen data and threatened to post it on a site on the dark web. … “It will likely take several weeks to return safely to normal operations, including electronic filing, but we will do so,” the state’s seven Supreme Court justices said in a joint statement. … The Kansas court system is the latest institution to be crippled by cyberattacks that have hamstrung K-12 schools, hospitals and federal and local agencies in recent years. Court systems in Florida, Georgia, Louisiana, Minnesota, Texas and Wisconsin have also been targeted. In Alaska, officials took the state court system offline for several weeks after a 2021 cyberattack.
- Chinese hackers steal chip designs from major Dutch semiconductor company — perps lurked for over two years to steal NXP’s chipmaking IP: Chimera, a Chinese-linked hacker group, infiltrated the network of the Dutch semiconductor giant NXP and had access for over two years from late 2017 to the beginning of 2020, reports NRC. During this period, the notorious hackers reportedly stole intellectual property, including chip designs. The full extent of the theft is still unknown. NXP is the largest chipmaker in Europe, and the scale and extent of the reported attack is shocking.
- Potentially hundreds of UK law firms affected by cyberattack on IT provider CTS: CTS, a managed service provider (MSP) for law firms in the United Kingdom, is “urgently investigating” a cyberattack that has disrupted its services — potentially leaving hundreds of British law firms unable to access their case management systems. … The company announced Friday that it was “experiencing a service outage which has impacted a portion of the services we deliver to some of our clients,” and confirmed “the outage was caused by a cyber-incident.” The UK government is “closely monitoring the company’s situation,” according to a government spokesperson.
- Hackers Leak Thousands of Idaho National Lab Employees’ PII Data: The Idaho National Laboratory (INL) has been hacked by a group of hackers called Sieged Security (aka SiegedSec). INL, a leading US nuclear research facility, confirmed the breach on Tuesday. … The INL explained that on 20 November, a cybersecurity data breach occurred in a federally approved external vendor system, which the lab uses for supporting INL cloud Human Resources service.
- Personal info of Canadian Armed Forces, RCMP stolen in cyberattack: The data of some Canadian government employees — including current and former members of the Canadian Armed Forces and Royal Canadian Mounted Police personnel — was leaked during a cyberattack on the systems of a government contractor used for relocation services.
- Welltok data breach exposes data of 8.5 million US patients: Healthcare SaaS provider Welltok is warning that a data breach resulting from the MOVEit exploit exposed the personal data of nearly 8.5 million patients in the U.S. after a file transfer program used by the company was hacked in a data theft attack.
- More than 330,000 Medicare recipients affected by MOVEit breach: In the latest disclosures related to a Russian ransomware gang’s exploitation of the popular MOVEit file transfer service, a federal government agency revealed that more than 330,000 Medicare recipients were affected in a leak of sensitive data. … The U.S. Center for Medicare & Medicaid Services (CMS) said it is sending letters to those who may have been impacted by a breach of the corporate network of Maximus Federal Services — a CMS contractor that used Progress Software’s MOVEit Transfer.
Section 4 – Managing Information Security and Privacy in Your Organization.
Want your awareness training program to be effective? Make sure you’re not replicating these ‘7 Deadly Sins.’
- The 7 Deadly Sins of Security Awareness Training: Stay away from using these tactics when trying to educate employees about risk. … Effective security awareness programs educate staff about risks and — if done well — dramatically reduce data breaches and attacks within an organization. While there are many tactics that work, there are also plenty of clunkers. … What are some of the more “sinful” ways companies try to dispense awareness education, only to find out their efforts are not working? Here’s a look at the seven deadly sins of security awareness so you can avoid these missteps when crafting your own program.
IT organizations need to pay attention to Windows fingerprint authentication as researchers have uncovered multiple vulnerabilities in the way fingerprint authentication is managed in multiple laptops.
- Microsoft’s Windows Hello fingerprint authentication has been bypassed: Security researchers have found flaws in the way laptop manufacturers are implementing fingerprint authentication. … Microsoft’s Windows Hello fingerprint authentication has been bypassed on laptops from Dell, Lenovo, and even Microsoft. Security researchers at Blackwing Intelligence have discovered multiple vulnerabilities in the top three fingerprint sensors that are embedded into laptops and used widely by businesses to secure laptops with Windows Hello fingerprint authentication.


